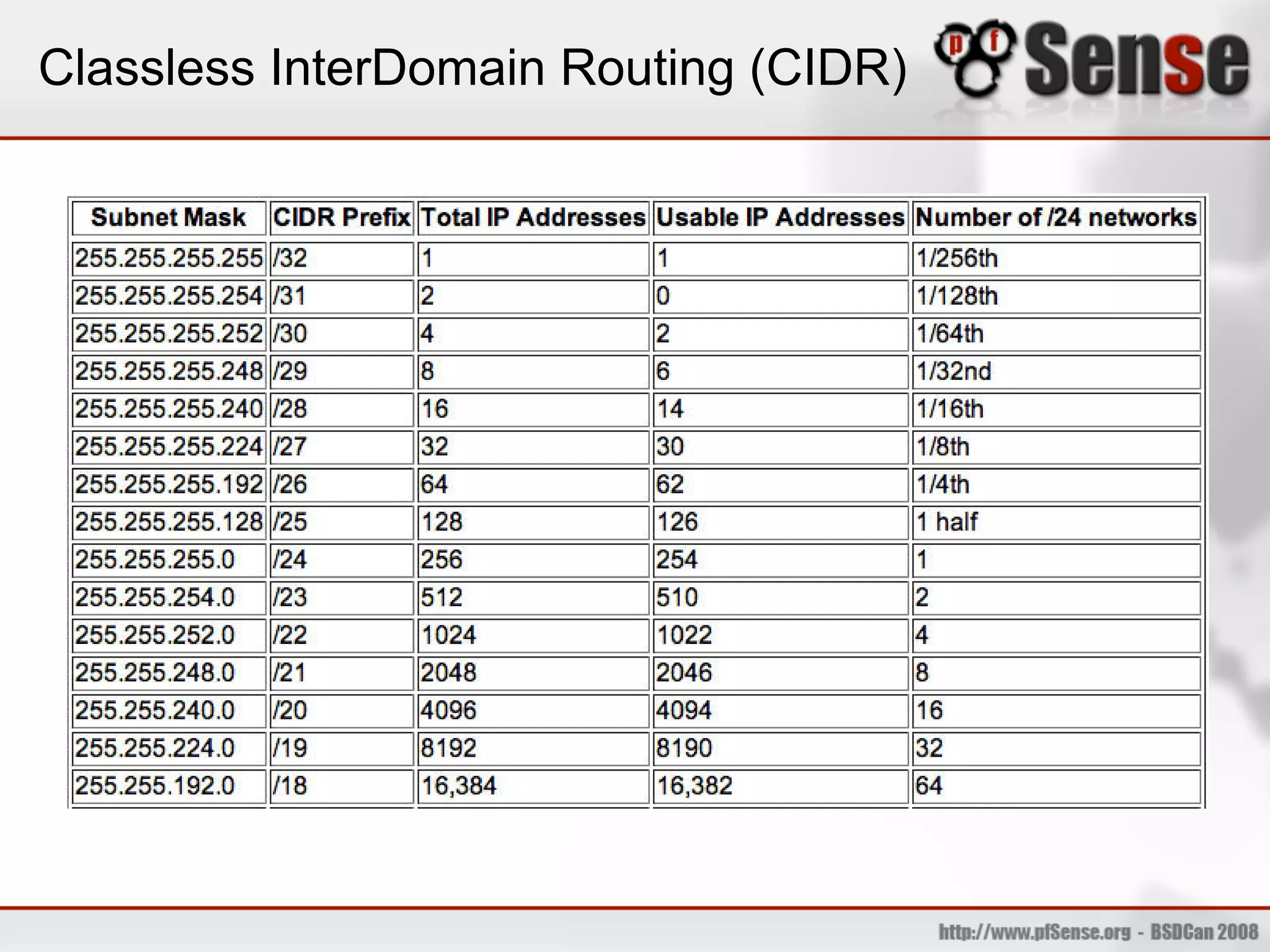
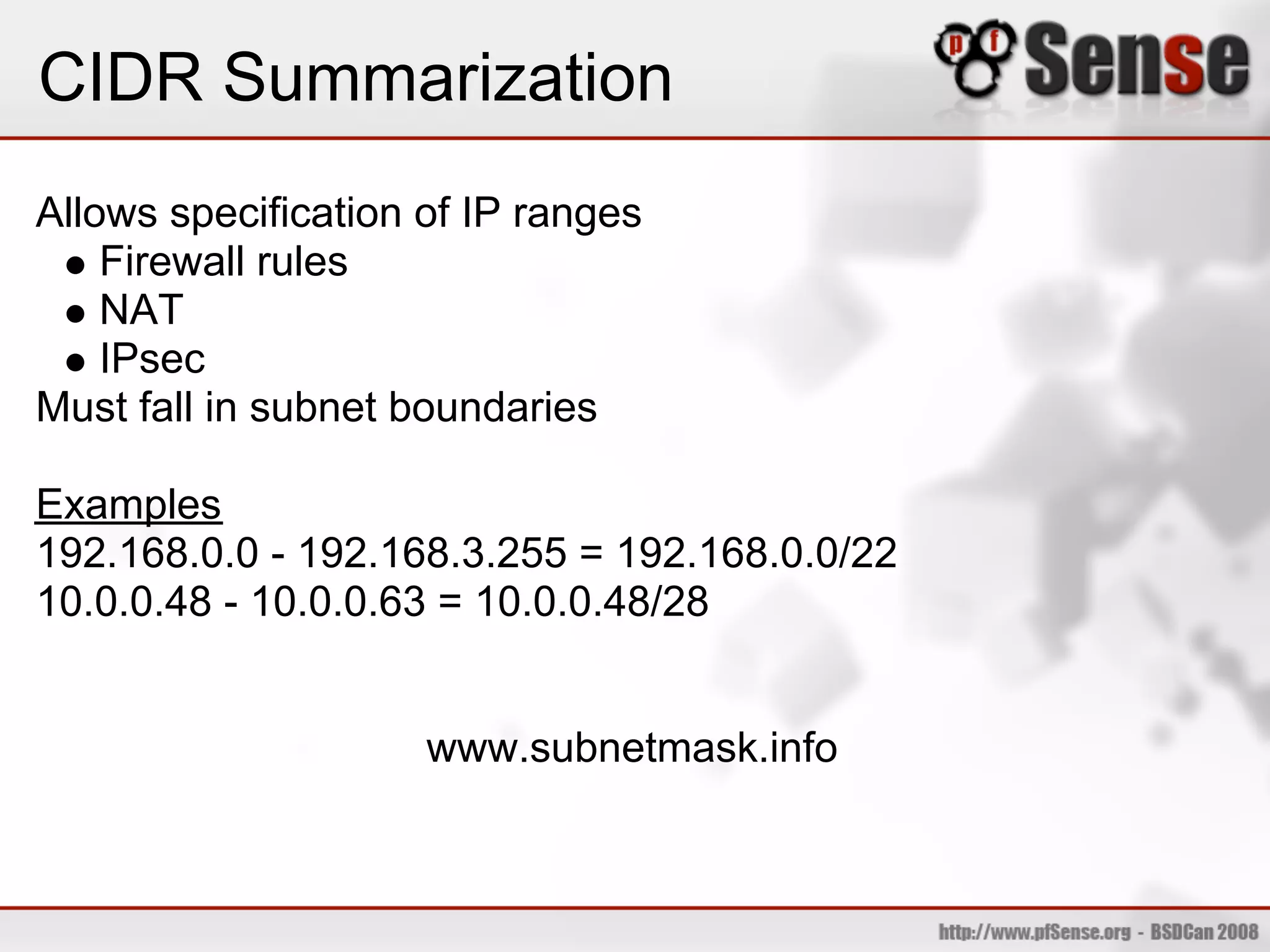
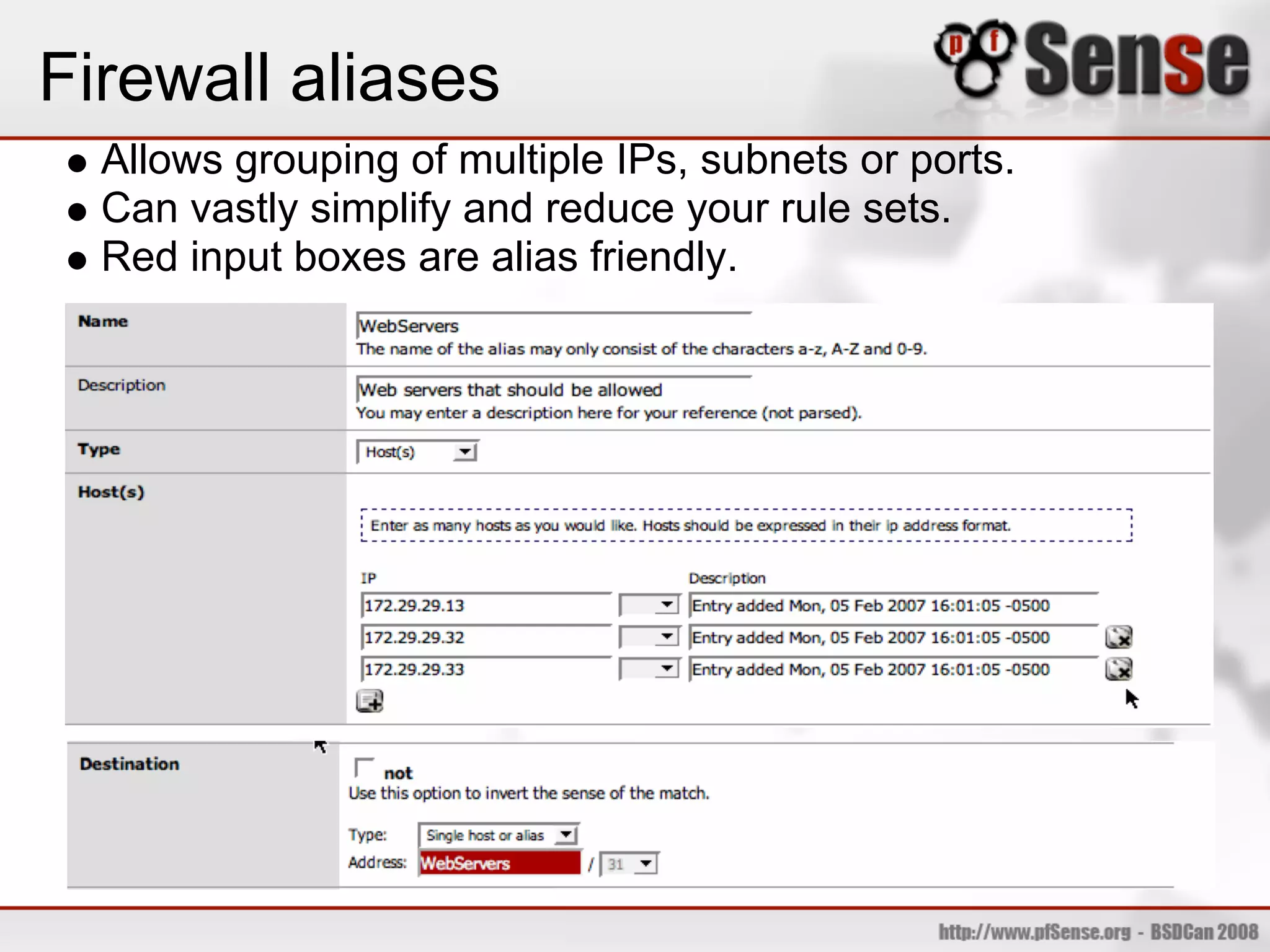
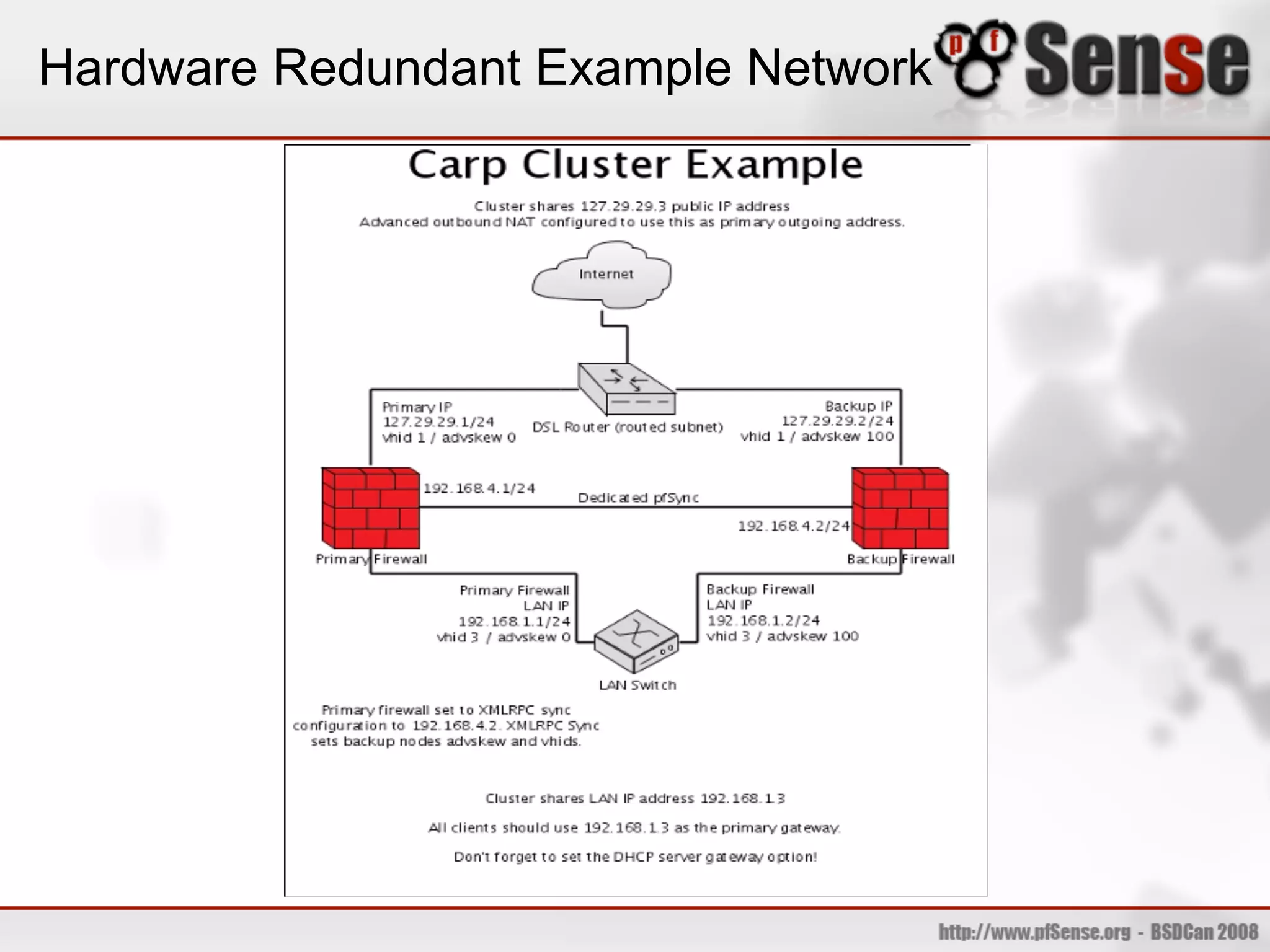
The document provides an overview of pfSense, an open source firewall and routing platform based on FreeBSD. It discusses the history and evolution of pfSense, hardware requirements, common deployment scenarios, and key features such as firewall rules, NAT, VPNs, traffic shaping, wireless access points, and high availability using CARP. The document also advertises a live demo of pfSense installation and configuration.