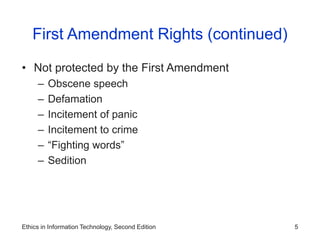
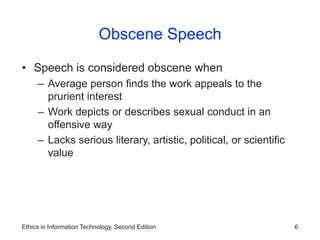
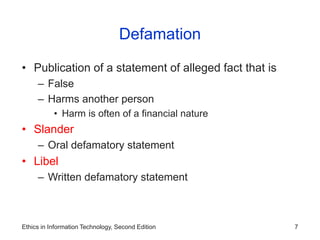
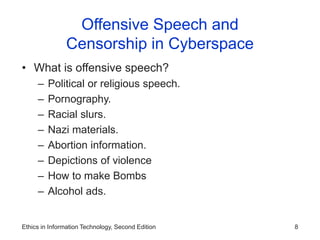
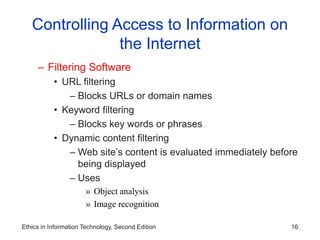
The document discusses key issues relating to freedom of expression and the use of information technology. It covers the legal basis for free speech protections in the US and exceptions like obscenity, defamation, and incitement. The document also examines challenges posed by the internet regarding controlling access to information, anonymity, censorship, defamation, hate speech, and pornography.