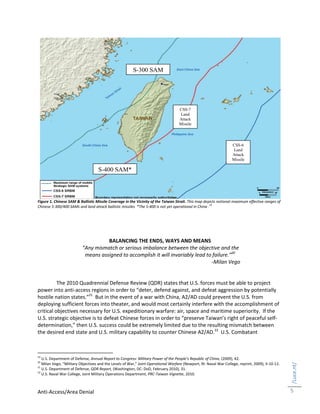
The document discusses China's development of anti-access/area denial (A2/AD) capabilities designed to disrupt U.S. power projection in the western Pacific. It analyzes the operational implications of Chinese A2/AD, including ballistic missiles threatening air bases, anti-ship missiles restricting carriers, and integrated air defenses challenging air superiority. It argues the U.S. must address any imbalance between the military objective to defend Taiwan and its ability to achieve that objective against China's A2/AD systems, such as by developing joint concepts like Air-Sea Battle to ensure freedom of movement in contested areas.