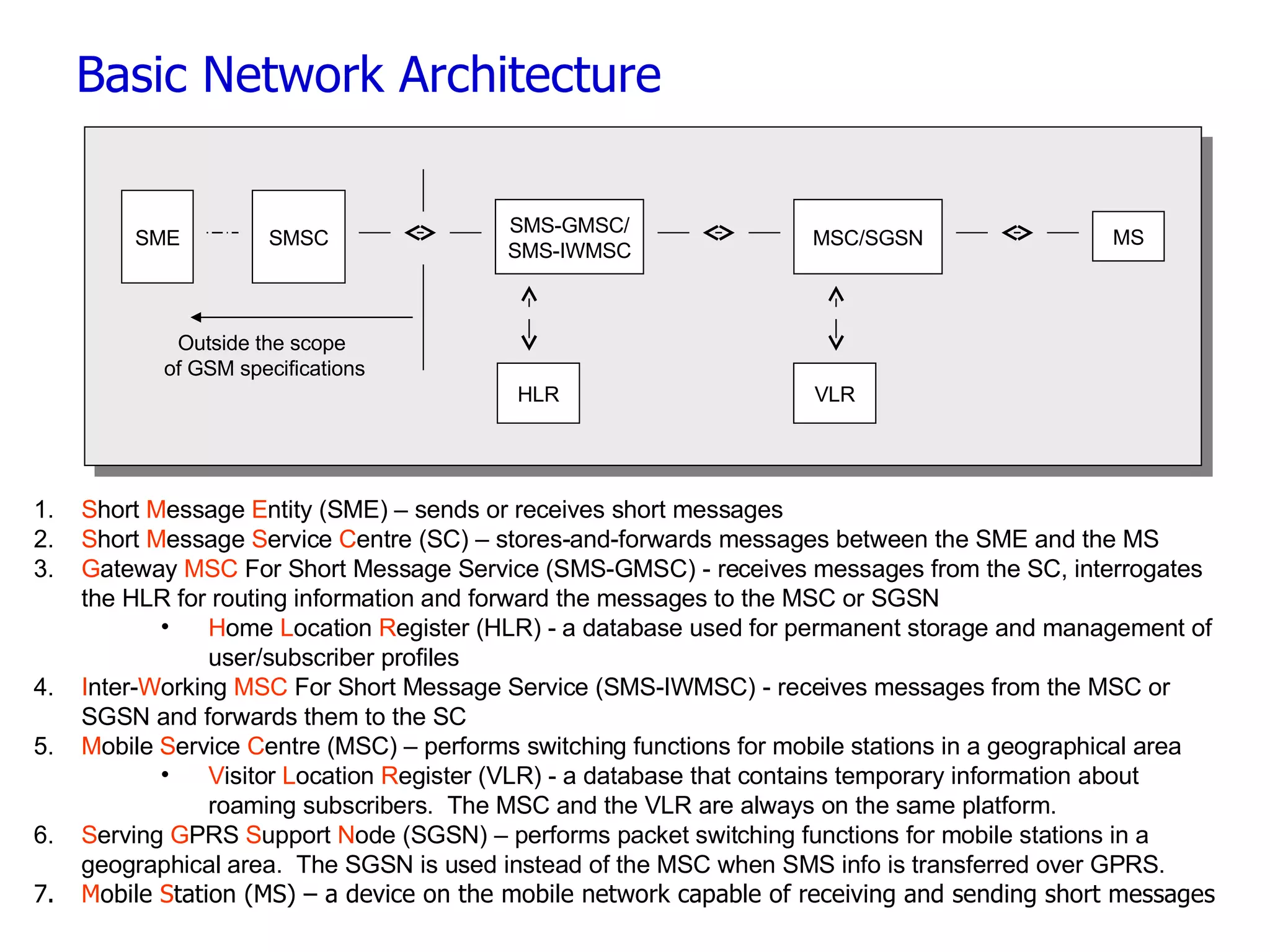
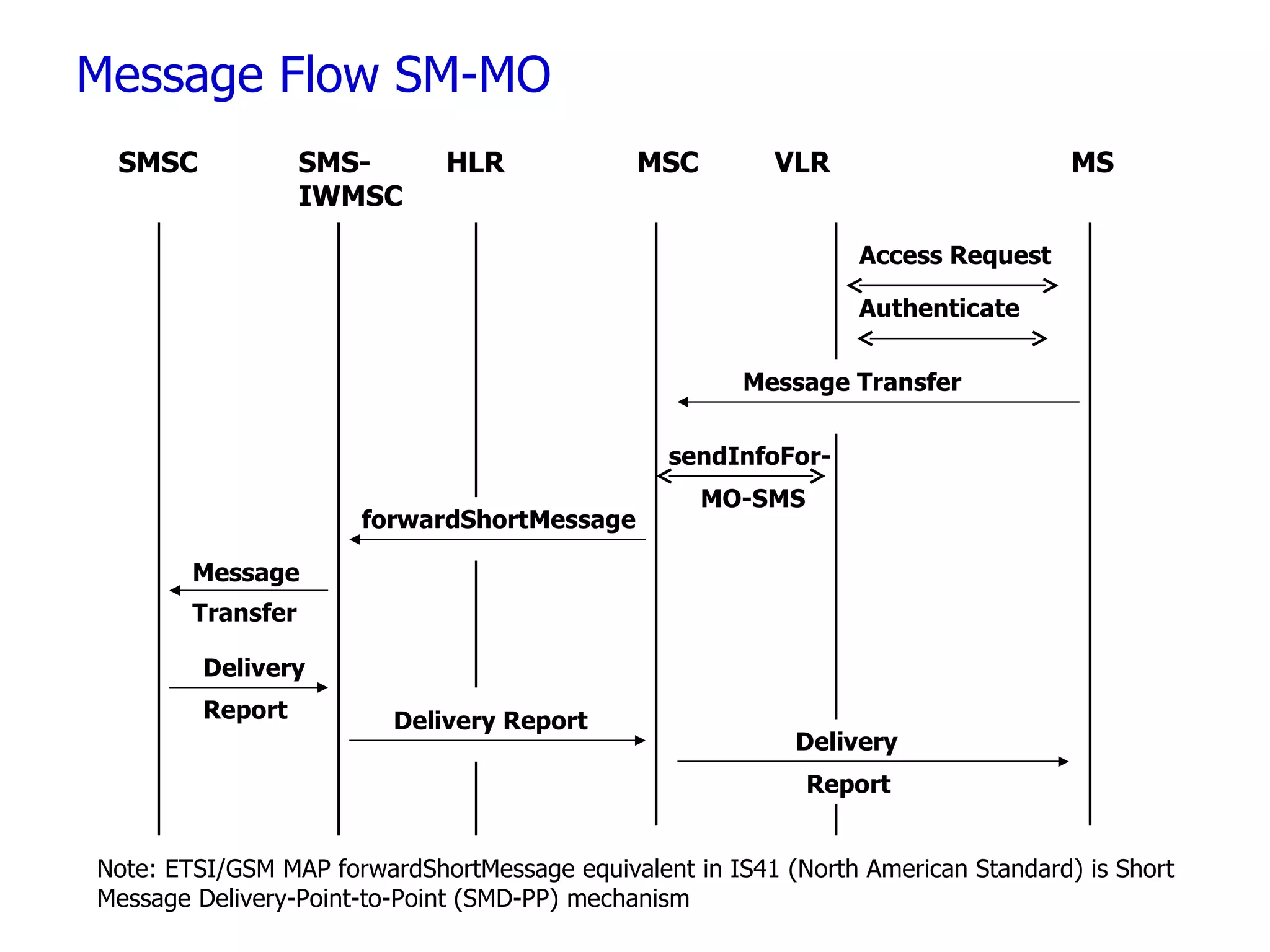
SMS (Short Message Service) allows users to send and receive text messages to and from mobile devices. SMS was introduced in 1991 in Europe and is supported on major mobile networks like GSM, GPRS, and CDMA. SMS messages can contain up to 160 Latin characters or 70 Unicode characters and are sent and received via Short Message Entities and a Short Message Service Center, which stores and forwards messages between mobile stations and networks.
![The Telecom Source www.thetelecomsource.com [email_address]](https://image.slidesharecdn.com/10-slides-to-sms-22607/75/10-Slides-to-SMS-12-2048.jpg)