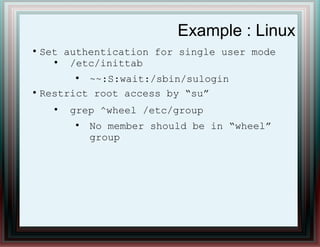
This document provides an overview of operating system and server security. It discusses key functions of an operating system including resource management, user interface, running programs, and security enforcement. It then covers possible attacks like password cracking, unauthorized access to resources, and placement of rootkits. The document gives examples of hardening techniques for user management, password policies, limiting services and access, and setting permissions on Linux and Windows systems. It stresses the importance of both OS and physical security, and provides hardware security best practices like firmware updates, unique credentials, and secure SNMP configuration.