1 Homework #5. (Due Nov 30) Name .docx
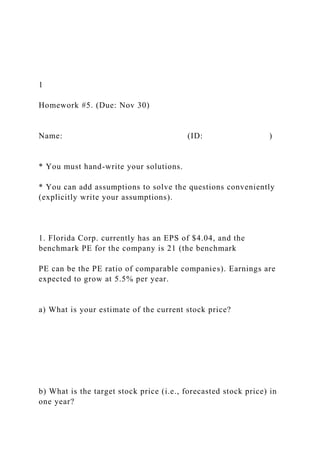
- 1. 1 Homework #5. (Due: Nov 30) Name: (ID: ) * You must hand-write your solutions. * You can add assumptions to solve the questions conveniently (explicitly write your assumptions). 1. Florida Corp. currently has an EPS of $4.04, and the benchmark PE for the company is 21 (the benchmark PE can be the PE ratio of comparable companies). Earnings are expected to grow at 5.5% per year. a) What is your estimate of the current stock price? b) What is the target stock price (i.e., forecasted stock price) in one year?
- 2. c) Assuming the company pays no dividend, what is the implied return on the company’s stock over the next year? What does this tell you about the implicit stock return using PE valuation? 2 2. Most corporations pay quarterly dividends on their common stock rather than annual dividends. Barring any unusual circumstances during the year, the board raises, lowers, or maintains the current dividend
- 3. once a year and then pays this dividend out in equal quarterly installments to its shareholders. a) Suppose a company currently pays an annual dividend of $3.60 on its common stock in a single annual installment, and management plans on raising this dividend by 3.8% per year indefinitely. If the required return on this stock is 10.5%, what is the current share price? b) Now suppose the company in (a) actually pays its annual dividend in equal quarterly installments; thus, the company has just paid a dividend of $ 0.90 per share, as it has for the previous three quarters. What is your value for the current share price now? (Hint: find the equivalent annual end-of-year dividend for each year.) Comment on whether you think this model of stock valuation appropriate. Assume that the quarterly dividends are reinvested at the required return.
- 4. 3 3. Panther Corp. has a bond issue with a face value of $1,000 that is coming due in one year. The value of Panther’s assets is currently $1,090. Rick Grimes, the CEO, believes that the assets in the firm will be worth either $920 or $1,380 in a year. T-bill rate is 4.8%. a) What is the value of Panther’s equity? The value of the debt? Use no arbitrage concept. (Hint: you can consider equity as call option.) b) Suppose Panther can reconfigure its existing assets in such a way that the value in a year will be $800 or $1,600. If the current value of assets is unchanged, will the stock holders favor such a move? Why or
- 5. why not? 4. A call option with an exercise price of $45 and four months to expiration has a price of $3.80. The stock is currently priced at $42.75, and the risk free rate is 5% per year. What is the price of a put option with the same exercise price? 4 5. Devise a portfolio using only call options and shares of stock with following value (payoff) at option expiration date. You need to specify the strike prices of call options that you employ.
- 6. 6. You are considering purchasing a put option on a stock with a current price of $33. The exercise price is $35, and the price of the corresponding call option is $2.25. According to the put-call parity theorem, if the risk-free rate of interest is 4% and there are 90 days until expiration, the value of the put should be ____________.
- 7. 0 50 payoff S(T) 60 50 110 5 7. Suppose that today is January 1 of the first year. Miami Corp. expects that the EBIT in this year will be $300. During the same period, depreciation costs will be $14 and amortization will be $6. Capital expenditures are $60, and the planned increase in net working capital is $30. The tax rate is 0.35. The debts of Miami Corp. are $250. The weighted average cost of capitals is 10%. (a) What is the free cash flow to the firm (FCFF)? (b) If the firm pays $20 as interest expense and there is no
- 8. change in the debts, what is the free cash flow to the equity (FCFE)? (c) Suppose that the FCFF of the firm will increase at 10% during year 2 and 8% during year 3. After year 3, the growth rate will be 5%. What is the value of the equity? Use FCFF for (c). (d) Suppose that the FCFE of the firm increases at 7% per year. What is the cost of equity of Miami Corp.? © Dmitriy Shironosov/ShutterStock, Inc.
- 9. LABORATORY ■■ Study■how■networks■route■packets■to■various■destination■h osts. ■■ Learn■how■networks■ensure■reliable■delivery. ■Software■needed: ■ 1)■ Apps■from■the■Lab■Manual■website: a)■ TCP/IP■(TCP■IP.jar) b)■ Network■Routing■(Network■Routing.jar) 19 OBJECTIVES REFERENCES Networking © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION 208 | Laboratory 19 BACKGROUND This lab explores the basic concepts of networking, elaborating on two specific aspects of computer networking. Review these topics from your textbook, lecture notes, or online resources: ■ Computer networks, packet switching, routers, network topologies: ring, star
- 10. ■ Network protocols, TCP/IP, IP addresses ACTIVITY ❯ Part 1 Though we tend to take networks for granted (except when they’re down!), they are surprisingly complicated. Setting one up involves much more than just running a wire between two computers. Not only must the machines agree on a whole series of protocols and identifying conventions before any communication can happen, but the wire itself is subject to seemingly malevolent forces working to corrupt the fragile data traveling through it! The TCP/IP protocol suite is a whole system of software, protocols, and management decisions. At its heart are several protocols that break messages into packets and send them from source computers to destination computers. In this activity, we will see a simplified form of TCP (Transmission Control Protocol) as it reliably sends a message to a destination computer. Start the TCP/IP app. This app simulates a reliable connection, which means that a big message is correctly sent in its entirety from source to destination. If anything goes wrong, the software makes heroic attempts to recover the information. While it is impossible to absolutely guarantee that the message will arrive intact, the networking software can make it very likely that it will be delivered
- 11. correctly. In this app, there are only two hosts, or nodes, numbered 0 and 1. Host 0 is a computer that is trying to send your message to host 1. You will play the role of one of those malevolent forces of nature, damaging and even destroying data packets. Will the software recover the data properly and save the day? Let’s hope so! © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION Networking | 209 Click on the Example button, which inserts a message into the Your message text area. Click Run, and then Send a message. Host 0 moves the message to the To be sent area and proceeds to “packetize” it into 10-character packets. Here you can see the first 10 characters—A very lon (the two spaces are part of the count)—moving slowly in a packet across the wire. What exactly does the DAT 1 0 144 in the packet mean? This is the packet’s header and contains crucial information. First, DAT identifies the type of packet being sent. There are three types of packets: DAT for “data,” ACK for “acknowledgment,” and NAK for “negative acknowledgment.” We will talk more about these in a minute.
- 12. Next in the header comes the destination address, which is 1. Though this seems a bit silly in a two-node network, bigger networks obviously require a destination address. The number 0, which appears next, is the sequence number. As messages are broken into packets, each packet is assigned a number: 0 in the first packet, 1 in the second packet, and so forth. If any packet were to arrive out of order, the destination computer could examine these sequence numbers and reassemble the message in the correct order. After all, if part of the message were scrambled, the meaning could change completely. (“You owe us $1000” means something quite different than “You owe us 000$1.”) Finally, 144 is the checksum, which alerts the destination computer that the packet was damaged. This app uses an extremely simple checksum algorithm, merely taking the ASCII value of each character in the packet, adding these together, and performing modulo 256 (keep the remainder after dividing by 256) so that the checksum is always between 0 and 255, inclusive. This checksum algorithm was actually used in some early protocols, but it is prone to serious problems. Today more advanced ones are used, most notably the cyclic redundancy code. We’d tell you how it works, but that would change our lab into an advanced mathematics class! © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION
- 13. 210 | Laboratory 19 After the first packet arrives at host 1, it sends back an ACK packet to acknowledge that the data arrived successfully. The type of the packet is ACK; the destination is 0 (host 0), and the sequence number that it sends back is 1, meaning that it expects host 0 to send it a packet with the sequence number 1 next. Finally, there is no real data in an ACK packet, so the checksum is 0. This explains why the header is ACK 0 1 0. Networks are always contending with the forces of chaos that can corrupt the data being sent: noise on the line, equipment failures, and other sorts of mayhem. So let’s wreak havoc on our poor little network and see what happens. Select Damage packets that are touched from the pull-down menu. You can do this while the app is sending packets. As a packet comes sliding along the wire, click on it. This should somehow corrupt the data. For example, the s below turned into the Japanese yen symbol! What does host 1 do when this packet arrives? How does it even know that the packet is damaged? It recomputes the checksum using the data it receives, and it matches the checksum in the header with the recomputed one. They don’t match this time, so host
- 14. 1 sends host 0 a NAK packet with the same sequence number. This tells host 0 that the packet was corrupted and needs to be resent. When host 0 gets the NAK, it resends the packet. Various status messages appear in the large text area at the bottom of the app, explaining what is going on. © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION Networking | 211 Now let’s experiment with more ways to make life difficult. Select Delete packets that are touched from the pull-down menu. When another packet comes along, click on it with your mouse and it should disappear. Packets that do not even arrive pose a bigger challenge than ones that are damaged. How does host 1 ever know that a packet is missing? Actually, it doesn’t, but host 0 is looking for an ACK or NAK packet in response to each DAT packet that it sends. So if one never arrives, host 0 assumes the packet is lost, and it sends the packet again. The host won’t wait forever to receive the ACK or NAK packet. It sets a timer on each packet and if nothing arrives before the timer counts down to 0, it times out and resends the packet.
- 15. Of course, all of this assumes that everything, including the hosts and the software, is working correctly to catch any errors that may occur. As you can imagine, there are about a million things that can happen to foul up this pretty picture, and we will explore some of them in the exercise. But suppose the packets are temporarily held up somehow. They aren’t lost, but the timer goes off anyway. What does host 1 do when it gets a duplicate packet? And does it send another ACK? Yikes! This networking is rapidly spinning out of control! Scientists who designed the Internet had to think about all these possibilities and decide how to handle them. Fortunately, they found reliable solutions so today we can sit in the comfort of our homes and travel the entire world with our fingertips. © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION 212 | Laboratory 19 ❯ Part 2 The second app simulates how computers route packets to their final destinations. Routing is enormously complicated because there are so many variables. We will see some of this unexpected complexity as we watch this app. Start the Network Routing app. Let’s go for the most complex example right away. Select Example 5 from the pull-down menu.
- 16. Each blue disk represents a node, or a computer in the network. The lines between nodes are telecommunication lines, perhaps telephone wires or Ethernet cables. Each node has its own IP address, a 32-bit number that is always represented as four octets separated by dots. In this app, the lines are “full duplex,” which means that packets can flow in either direction between the two connected hosts. This isn’t always the case in the real world, but many lines are full duplex. You can move the nodes around on the screen by dragging them. Their attached lines move with them. You can even add new nodes. To make a new node, double-click on any open space and the app places a blue dot there with the unusable address of 0.0.0.0. You are expected to change that right away! To change the characteristics of a node, double-click on the node and a new window appears: © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION Networking | 213 This window displays status information in the right column, showing packets that this
- 17. node has received and some statistics. At the top are three fields that you can change, the first being the IP address of the node. You can also customize the message you want to send, and you can add the address of the recipient. If the Destination node field is blank, no messages will be sent by this node. More than one node can send and receive messages at the same time when this app runs. The connection and routing tables below these fields are the focus of this app’s study. The connection table lists the IP addresses of nodes that directly connect to this node. Most networks assume, quite logically, that two nodes can find each other and send packets if they are directly connected. It is when nodes are not directly connected to their destinations that things get interesting! The purpose of the routing table is to tell the node what to do when it is not directly connected to the destination node. For example, if node X wants to send a packet to node Y, which is not directly connected, it must send the packet to node Z instead, and node Z then assumes the responsibility of getting it to node Y. Hopefully, Z will not mistakenly send it back to X! If so, a routing loop would occur and the packet would travel the wires endlessly, like the Flying Dutchman. This prospect so worried early developers of TCP/IP that they put a timer on each packet so that it would just evaporate after going through too many nodes.
- 18. The routing table has two columns. The first column lists the destination, and the second lists the next hop. The next hop must be a directly connected node. There are also a number of special cases that can shorten routing tables. If the word “DEFAULT” appears in the routing table, then the node merely sends packets to the first node in the directly connected table. This works nicely for leaf nodes, which connect to only one other node, but won’t work for a complex topology, or the configuration of the network. Most of the time, nodes with two or more connections need to explicitly list all distant nodes, along with the next hop. However, this quickly gets tedious and requires too much work to update, as many new nodes are added. One possible alternative is to list some of the destination/next hop pairs, and leave the others unspecified. The Network Routing app lets you do this by putting an asterisk in the destination column, as shown below for the ring network (Example 3): © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION 214 | Laboratory 19 Finally, what can we do if the network is under attack and the routing table is now obsolete due to out-of-commission routers? Early TCP/IP developers worried about this,
- 19. too, and came up with the “hot potato algorithm.” This app allows you to type “HOT POTATO” in the routing table. Nothing else is needed. Hot potato works this way: When a packet comes in, the node makes a random guess as to which directly connected node will get the packet to its final destination, and it sends it to that next hop. This may not work and it may result in routing loops, but it just might do the trick, too. Imagine a bunch of people on the beach around a campfire passing around a hot sweet potato wrapped in aluminum foil. As they energetically toss it to one another, there is a good chance that it will end up in the hands (or lap) of someone who wants to eat it! There are many other routing algorithms that were designed with various emergencies or unusual conditions in mind. One such algorithm is called “flooding,” in which every packet is copied to every outgoing wire, not just to one random one, as in hot potato. What happens in the Internet, which is built on TCP/IP? What routing algorithms are used? The local area networks that attach to the Internet often use specialized routing algorithms. For example, Ethernet is like a telephone where everyone can hear everyone else’s calls. So when the phone rings, or a new packet comes in, each computer listens to the beginning of the packet to see if it is meant for them. The backbone network that manages the long-distance, high-
- 20. volume traffic on the Internet uses several dynamic routing protocols. In such systems, nodes change their routing tables from time to time as they are forwarding packets. Unlike the “Network Routing” app, in which you, the network administrator, decide once and for all what the routing table for node X is, dynamic routing systems measure the characteristics of the traffic and the attached lines, and adjust their routing tables so that packets will flow most efficiently through the entire system. This sounds daunting, and it is, kind of like continuously adjusting the timing on all traffic lights so that cars on the streets get to their destinations in the least amount of time. While the system isn’t perfect, it’s worked on the Internet for over 40 years. © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION CS1150 Introduction to Computer Science Lab #9 – Networking, 40 points Objective: To study how networks route packets to various destination hosts. Learn how networks ensure reliable delivery. Instructions: Make sure to do the Activity as outlined in the LabCH19.pdf file. The activity is actually a tutorial that will help you to solve the problems in the exercises. It is expected that you will complete the Activity before you begin the exercises. When you are finished, save and rename the completed
- 21. document as “firstname_lastname_lab9.docx”. Then, submit the saved document to Pilot. EXERCISE 1 1) Start the “TCP/IP” applet. 2) Copy and paste the following text into the “Your Message” box: Computer networking is essential in our world today. Note that this message is exactly 52 ASCII characters long, counting spaces and the period at the end. It should look like this: Then, press the button “Send a message” and watch. 3) Count how many DAT and ACK packets were sent. (Don’t rely on the “Status” box, actually count the packets yourself.)
- 22. Write your answers here: DEFINE DAT AND GIVE NUMBER OF DAT PACKETS: DEFINE ACK AND GIVE NUMBER OF ACK PACKETS: 4) Determine the steps for calculating how many characters were sent during the entire exchange. Assuming that: · Every DAT or ACK packet has a packet header (example: DAT 1 0 221) · Besides the packet header, every DAT packet carries AT MOST 10 characters of data. · The last packet carried less than 10 characters of data. (52 data characters in the message, remember? 52 doesn’t divide nicely into 10) · ACK packets have no data, just a packet header. · Every blank space, even in a packet header, counts as a character. · Assume that every packet header is 9 characters long We calculated that exactly 171 characters were sent back and forth in total during the entire process. How did we get that number? Show the mathematical steps to calculate the number 171 here, below this line.: 5) Calculate the overhead, expressed as a percentage. Here is the process: · There are 52 characters of actual data in the message,
- 23. including blanks and punctuation. · Subtract the number of characters of actual data (52 characters) from the total number of characters sent in both directions in all the packets (from earlier in the lab). This gives you the number of characters sent that were not actually data, just part of the cost/overhead of sending the actual data. · Divide the number of overhead characters by the total number of characters to calculate the overhead expressed as a percentage of the total. Write the overhead percentage here, below this line: 6) Imagine you have a million-character message to send. Calculate how many packets will be needed and how many characters will be sent in total for the entire process to move the message from node 0 to node 1: Write your answers here: HOW MANY PACKETS TOTAL: HOW MANY CHARACTERS TOTAL: 7) What would be an obvious way to decrease the overhead percentage? Why might this solution backfire? Under what conditions would that occur? Write your answers here: OBVIOUS WAY TO DECREASE OVERHEAD PERCENTAGE: HOW THAT COULD BACKFIRE: UNDER WHAT CONDITIONS:
- 24. 8) What is the purpose of IP address? What is the purpose of Routers? Write your answers here: EXERCISE 2 1) Start or restart the “TCP/IP” applet again. Once again, copy and paste the following text into the “Your Message” box: Computer networking is essential in our world today. 2) This time, change the selection away from Leave packets undamaged to Delete packets that are touched.
- 25. 3) Delete some data packets by clicking on them as they move along the wire, and watch the re-transmission after timeout. 4) What happens if you delete the re-transmitted packet? Does the TCP/IP applet need to take any special action? Write what happens here, below this line: Is special action needed if re-transmitted packet is deleted? Write your answer here, below this line: 5) What happens if you delete ACK or NAK packets? Write your answer here, below this line: EXERCISE 3 1) Start the “Network router” applet. Select Example 3, the ring network.
- 26. 2) Double-click on the node 37.61.25.46. List the nodes it is directly connected to (the nodes in its connection table). Write your list of nodes here, below this line: 3) If 37.61.25.46 wants to send packets to a node that is not directly connected, to which node will it first send the packets? (Check the routing table by double clicking on the node.) Write the address of the next node here, below this line: 4) Run the applet for a while, letting it generate packets continuously. Double-click on 37.61.25.46 again and look at its statistics. How many packets were sent? Received? Forwarded? Write your answers here: PACKETS SENT: PACKETS RECEIVED: PACKETS FORWARDED: 5) Which nodes are sending packets out, and to whom? Write your answers here: NODES THAT ARE SENDING PACKETS: NODES THAT ARE RECEIVING PACKETS: 6) Click on 138.92.6.17. Write down its statistics. PACKETS SENT: PACKETS RECEIVED: PACKETS FORWARDED:
- 27. EXERCISE 4 1) Start the “Network router” applet. Select Example 4, the star network. 2) Look at the routing and connection tables for the center node and several other nodes. Describe any pattern you can see in these tables. Write your description here, below this line: 3) How is the connection table for the center node different from the other nodes? Write your answer here, below this line: 4) Select Generate when I click on a node from the pull-down menu. 5) If you double-click on 159.121.2.13, you will see that its destination node is 126.14.5.46. Run the applet, click on 159.121.2.13, and watch the packets go. What color does the sending computer turn briefly? What color does the destination computer turn? What does it mean if a node flashes green? Write your answers here: WHAT COLOR (SENDING COMPUTER): WHAT COLOR (DESTINATION COMPUTER):
- 28. WHAT DOES IT MEAN IF A NODE FLASHES GREEN: Try it again with 8.10.20.25 to confirm. 6) Many early computer networks used a star topology like this example. What would happen if the center node in this type of network dies? Write your answer here, below this line:
- 29. Exercise 5 Create a new topology using 4 nodes. 1) Create 4 nodes with following IP addresses Node 1 = 130.108.7.11 Node 2 = 130.108.7.22 Node 3 = 130.108.7.33 Node 4 = 130.108.7.44 2) Make Node 3 as a forwarding node and connect it with all the other remaining nodes. 3) Let the sender receiver pair be as following: Sender Receiver Node 1 Node 2 Node 2 Node 4 Node 4 Node 1 4) Your topology should look like as given below: 5) Paste your screenshot below this line: Rubric (40 pts possible):
- 30. Exercise Points 1 Question 1 0 Question 2 0 Question 3 1 Question 4 1 Question 5 2 Question 6 1 Question 7 1 Question 8 2 2 Question 1 0 Question 2 1 Question 3 1
- 31. Question 4 3 Question 5 3 3 Question 1 1 Question 2 1 Question 3 1 Question 4 1 Question 5 2 Question 6 2 4 Question 1 1 Question 2 1 Question 3 1 Question 4 1
- 32. Question 5 2 Question 6 2 5 Question 1 2 Question 2 2 Question 3 2 Question 5 2 Total 40 Lab_9_Applets/Network Routing.jar META-INF/MANIFEST.MF Manifest-Version: 1.0 Created-By: 1.6.0_38 (Sun Microsystems Inc.) Main-Class: Network
- 33. Network$1.classsynchronizedclass Network$1 extends java.awt.event.WindowAdapter { void Network$1(Network); public void windowClosing(java.awt.event.WindowEvent); } Network$2.classsynchronizedclass Network$2 extends Thread { void Network$2(Network); public void run(); } Network.classpublicsynchronizedclass Network extends java.awt.Frame implements java.awt.event.ActionListener, java.awt.event.ComponentListener, java.awt.event.MouseListener, java.awt.event.MouseMotionListener, java.awt.event.ItemListener { java.awt.Button runB; java.awt.Button stopB; java.awt.Button helpB; java.awt.Button newB; java.awt.Button editB; java.awt.Choice exampleCH; java.awt.Choice methodCH; java.awt.Color acolor; Node[] nodes; staticfinal int MAXNODES = 25; boolean mustStop; boolean running; int x; int y; int buttonHeight; int topnode;
- 34. int nextNodeNumber; java.awt.Image buffer; java.awt.Graphics gg; int current; boolean dragging; boolean genContinuously; publicstatic void main(String[]); public void Network(); public void actionPerformed(java.awt.event.ActionEvent); public void itemStateChanged(java.awt.event.ItemEvent); public void runme(); public void stop(); public void componentResized(java.awt.event.ComponentEvent); public void componentHidden(java.awt.event.ComponentEvent); public void componentMoved(java.awt.event.ComponentEvent); public void componentShown(java.awt.event.ComponentEvent); public void mouseMoved(java.awt.event.MouseEvent); public void mouseDragged(java.awt.event.MouseEvent); public void mouseEntered(java.awt.event.MouseEvent); public void mouseExited(java.awt.event.MouseEvent); public void mousePressed(java.awt.event.MouseEvent); public void mouseReleased(java.awt.event.MouseEvent); public void mouseClicked(java.awt.event.MouseEvent); public void doubleClick(java.awt.event.MouseEvent); public void newNode(int, int); public void grow(); public void singleClick(java.awt.event.MouseEvent); public void paint(java.awt.Graphics); public void update(java.awt.Graphics); public void runaux(); private void delay(int); private void help();
- 35. private void loadExample(); public Node find(String); publicstatic int convert(String); publicstatic String convert(int); } Node.classpublicsynchronizedclass Node { String id; Network parent; public int x; public int y; String messageToSend; StringList connectionTable; StringList routingTable; StringList packetsReceived; StringList info; String dest; Queue outgoing; java.awt.Color mycolor; int numericalID; boolean mustGenerate; staticfinal int SLEEPTIME = 250; int numpacketsSent; int numpacketsRecd; int numpacketsDropt; int numpacketsForwarded; staticfinal int diameter = 25; public void Node(Network, String, int, int); public void paint(java.awt.Graphics); public void connect(String); public void clearRoutes(); public void addRoute(String, String); public boolean within(int, int); publicstatic String getDest(String); publicstatic String getSource(String);
- 36. publicstatic String getMessage(String); public void send(String, String); public void deliver(String); public void route(); public String findNextHop(String); public void generatePacket(String); public float xgetRandom(); public int getRandom(); public int getRandom(int); public String status(); } NodeWindow$1.classsynchronizedclass NodeWindow$1 extends java.awt.event.WindowAdapter { void NodeWindow$1(NodeWindow); public void windowClosing(java.awt.event.WindowEvent); } NodeWindow.classpublicsynchronizedclass NodeWindow extends java.awt.Frame implements java.awt.event.ActionListener, java.awt.event.ComponentListener, java.awt.event.MouseListener, java.awt.event.ItemListener { java.awt.Choice freqCH; java.awt.TextArea conTA; java.awt.TextArea routeTA; java.awt.TextArea recvdTA; java.awt.TextArea infoTA; java.awt.TextField ipTF; java.awt.TextField sendTF; java.awt.TextField destTF; java.awt.Label Label1; java.awt.Label Label2; java.awt.Label Label3;
- 37. java.awt.Label Label4; java.awt.Label label5; java.awt.Button okB; java.awt.Button cancelB; java.awt.Image buffer; java.awt.Graphics gg; java.awt.Color acolor; staticfinal int X = 0; staticfinal int Y = 0; Node node; Network parent; public void NodeWindow(Node, Network); public void actionPerformed(java.awt.event.ActionEvent); public void itemStateChanged(java.awt.event.ItemEvent); public void componentResized(java.awt.event.ComponentEvent); public void componentHidden(java.awt.event.ComponentEvent); public void componentMoved(java.awt.event.ComponentEvent); public void componentShown(java.awt.event.ComponentEvent); public void mouseEntered(java.awt.event.MouseEvent); public void mouseExited(java.awt.event.MouseEvent); public void mousePressed(java.awt.event.MouseEvent); public void mouseReleased(java.awt.event.MouseEvent); public void mouseClicked(java.awt.event.MouseEvent); public void doubleClick(java.awt.event.MouseEvent); public void paint(java.awt.Graphics); public void update(java.awt.Graphics); } Popup$1.classsynchronizedclass Popup$1 extends java.awt.event.WindowAdapter { void Popup$1(Popup);
- 38. public void windowClosing(java.awt.event.WindowEvent); } Popup.classsynchronizedclass Popup extends java.awt.Frame { java.awt.TextArea ta; public void Popup(String); public void Popup(String, java.awt.Color); public void Popup(String, int, int); public void Popup(String, int, int, java.awt.Color); public void Popup(String, int, int, int, int, java.awt.Color); public void add(String); public void setFont(java.awt.Font); } Queue.classpublicsynchronizedclass Queue implements java.io.Serializable, Cloneable { java.util.Vector theQueue; public void Queue(); public boolean isEmpty(); public void enqueue(Object); public Object dequeue(); public Object top(); public int length(); public Object clone(); publicstatic void main(String[]); } StringList.classpublicsynchronizedclass StringList { String[] contents; int size; public void StringList(); public void StringList(String, String); public void StringList(String);
- 39. public int length(); public StringList shift(int); public StringList copy(); public int find(String); public String get(int); public void put(String, int); public void add(String); public String toString(); public String toString(char); public void substitute(String[], String[]); private void grow(); private void grow(int); publicstatic void main(String[]); } U.classpublicsynchronizedclass U { public void U(); publicstatic int atoi(String); publicstatic long atol(String); publicstatic double atod(String); publicstatic String[] copy(String[]); publicstatic String[] tokenize(String); publicstatic String[] tokenize(String, String); publicstatic String detokenize(String[]); publicstatic boolean equals(String[], String[]); publicstatic void sleep(long); publicstatic int power(int, int); publicstatic String convert(int, int); publicstatic boolean isint(String); publicstatic String dec2bin(int); publicstatic int bin2dec(String); publicstatic String twoscomplement(String); publicstatic String padout(String, char, int); publicstatic String squish(String, char); publicstatic java.awt.Color translateColor(String);
- 40. publicstatic String getField(String, int); publicstatic String getField(String, int, char); publicstatic void main(String[]); } Lab_9_Applets/TCP IP.jar META-INF/MANIFEST.MF Manifest-Version: 1.0 Created-By: 1.6.0_38 (Sun Microsystems Inc.) Main-Class: Tcpip Input.classsynchronizedclass Input extends java.awt.Frame implements java.awt.event.ActionListener { java.awt.TextArea ta; boolean iamready; java.awt.Button okB; java.awt.Button cancelB; public void Input(String); public void Input(String, int, int, int, int, java.awt.Color); public void actionPerformed(java.awt.event.ActionEvent); public boolean ready(); public String get(); } Node$1.classsynchronizedclass Node$1 extends Thread { void Node$1(Node); public void run();
- 41. } Node$2.classsynchronizedclass Node$2 extends Thread { void Node$2(Node); public void run(); } Node.classsynchronizedclass Node { int nextSeqNum; int nextAckExpected; String messageToSend; String remainingMessage; String outgoingData; int id; Tcpip parent; int x; int y; int diameter; Packet currentPkt; Packet inbox; int direction; int timer; publicstaticfinal int TRANSITDELAY = 90; Packet p; boolean waitingAck; public void Node(int, int, Tcpip, int, int, int); public boolean inject(String); public void deliver(Packet); public void start(); private void processAck(); private void processData(); public void draw(java.awt.Graphics); public void clear(); }
- 42. Packet.classsynchronizedclass Packet { String data; String type; int dest; int seq; int chksum; int x; int y; int width; int height; publicstaticfinal int XINCREMENT = 10; Tcpip parent; boolean delivered; public void Packet(String, String, int, int, Tcpip, int, int); public String toString(); public void advance(int); public void draw(java.awt.Graphics); publicstatic int computeChecksum(String); public boolean within(int, int); public void damage(); } Popup$1.classsynchronizedclass Popup$1 extends java.awt.event.WindowAdapter { void Popup$1(Popup); public void windowClosing(java.awt.event.WindowEvent); } Popup.classsynchronizedclass Popup extends java.awt.Frame { java.awt.TextArea ta; public void Popup(String); public void Popup(String, java.awt.Color);
- 43. public void Popup(String, int, int); public void Popup(String, int, int, java.awt.Color); public void Popup(String, int, int, int, int, java.awt.Color, String); public void add(String); public void setFont(java.awt.Font); } Tcpip$1.classsynchronizedclass Tcpip$1 extends java.awt.event.WindowAdapter { void Tcpip$1(Tcpip); public void windowClosing(java.awt.event.WindowEvent); } Tcpip.classpublicsynchronizedclass Tcpip extends java.awt.Frame implements java.awt.event.ActionListener, java.awt.event.ComponentListener, java.awt.event.ItemListener, java.awt.event.MouseListener { java.awt.TextArea status; java.awt.TextField inputTF; java.awt.TextField tf1; java.awt.TextField tf2; java.awt.Label lab; java.awt.Button runB; java.awt.Button sendB; java.awt.Button stopB; java.awt.Button helpB; java.awt.Button exampleB; java.awt.Color acolor; Node[] nodes; boolean mustStop; int x; int y; int buttonHeight;
- 44. java.awt.Image buffer; java.awt.Graphics gg; java.awt.Choice damageCH; boolean doDamage; publicstatic void main(String[]); public void Tcpip(); public void actionPerformed(java.awt.event.ActionEvent); public void run(); public void stop(); public void componentResized(java.awt.event.ComponentEvent); public void componentHidden(java.awt.event.ComponentEvent); public void componentMoved(java.awt.event.ComponentEvent); public void componentShown(java.awt.event.ComponentEvent); public void mouseEntered(java.awt.event.MouseEvent); public void mouseExited(java.awt.event.MouseEvent); public void mousePressed(java.awt.event.MouseEvent); public void mouseReleased(java.awt.event.MouseEvent); public void mouseClicked(java.awt.event.MouseEvent); public void doubleClick(java.awt.event.MouseEvent); public void singleClick(java.awt.event.MouseEvent); public void itemStateChanged(java.awt.event.ItemEvent); public void paint(java.awt.Graphics); public void update(java.awt.Graphics); public void msg(String); private void delay(int); private void help(); private void loadExample(); } U.classpublicsynchronizedclass U { public void U();
- 45. publicstatic int atoi(String); publicstatic long atol(String); publicstatic double atod(String); publicstatic String[] copy(String[]); publicstatic String[] tokenize(String); publicstatic String[] tokenize(String, String); publicstatic String detokenize(String[]); publicstatic boolean equals(String[], String[]); publicstatic void sleep(long); publicstatic int power(int, int); publicstatic String convert(int, int); publicstatic boolean isint(String); publicstatic String dec2bin(int); publicstatic int bin2dec(String); publicstatic String twoscomplement(String); publicstatic String padout(String, char, int); publicstatic String squish(String, char); publicstatic java.awt.Color translateColor(String); }