Points 125Case Study 2 HIPAA and IT AuditsCriteriaUnaccept.docx
•Download as DOCX, PDF•
0 likes•8 views
This document outlines the criteria for a case study assignment on HIPAA and IT audits. It provides weighting and evaluation criteria for multiple sections involving analyzing HIPAA regulations, describing necessary network architecture and controls, and creating a network diagram. Students would be evaluated on creating an overview of HIPAA rules, analyzing common incident types, describing technical and non-technical controls, comparing hospital to non-medical compliance, listing IT audit steps, including references, and drawing a network diagram demonstrating a compliant architecture.
Report
Share
Report
Share
Recommended
Recommended
More Related Content
Similar to Points 125Case Study 2 HIPAA and IT AuditsCriteriaUnaccept.docx
Similar to Points 125Case Study 2 HIPAA and IT AuditsCriteriaUnaccept.docx (20)
Points 50Project Deliverable 1 Project Plan InceptionCriteri.docx

Points 50Project Deliverable 1 Project Plan InceptionCriteri.docx
What Covered Entities Need to Know about OCR HIPAA Audits

What Covered Entities Need to Know about OCR HIPAA Audits
Prepare a workplace brief (8-10 double-spaced pages) to address a .docx

Prepare a workplace brief (8-10 double-spaced pages) to address a .docx
HIPAA Compliance Testing In Software Applications.pdf

HIPAA Compliance Testing In Software Applications.pdf
Rubic_Print_FormatCourse CodeClass CodeNRS-451VNNRS-451VN-O502Heal.docx

Rubic_Print_FormatCourse CodeClass CodeNRS-451VNNRS-451VN-O502Heal.docx
Redspin & Phyllis and Associates Webinar- HIPAA,HITECH,Meaninful Use,IT Security

Redspin & Phyllis and Associates Webinar- HIPAA,HITECH,Meaninful Use,IT Security
Barbara Silva is the CIO for Peachtree Community Hospital in Atlanta.docx

Barbara Silva is the CIO for Peachtree Community Hospital in Atlanta.docx
Understanding HIPAA / HITECH as a Mail Service Provider

Understanding HIPAA / HITECH as a Mail Service Provider
Points 120Case Study 1 Cyber Security in Business Organization.docx

Points 120Case Study 1 Cyber Security in Business Organization.docx
More from harrisonhoward80223
More from harrisonhoward80223 (20)
© 2006 Thomson-Wadsworth© 2006 Thomson-Wadsworth.docx

© 2006 Thomson-Wadsworth© 2006 Thomson-Wadsworth.docx
§ 6.01 IntroductionBackground checks are an important component .docx

§ 6.01 IntroductionBackground checks are an important component .docx
© 2013 The McGraw-Hill Companies, Inc. All rights reserved. .docx

© 2013 The McGraw-Hill Companies, Inc. All rights reserved. .docx
© 2013 Laureate Education, Inc. 1 Adolescence” Program .docx

© 2013 Laureate Education, Inc. 1 Adolescence” Program .docx
© 2013 Laureate Education, Inc. 1 Young Adulthood” Prog.docx

© 2013 Laureate Education, Inc. 1 Young Adulthood” Prog.docx
© 2013 Laureate Education, Inc. 1 NURS 6441 Indivi.docx

© 2013 Laureate Education, Inc. 1 NURS 6441 Indivi.docx
© 2013 Laureate Education, Inc. 1 NURS 6441 Work .docx

© 2013 Laureate Education, Inc. 1 NURS 6441 Work .docx
© 2013 Laureate Education, Inc. 1 Comprehensive Write-u.docx

© 2013 Laureate Education, Inc. 1 Comprehensive Write-u.docx
© 2011 The McGraw-Hill Companies, Inc. All rights reserved.Mc.docx

© 2011 The McGraw-Hill Companies, Inc. All rights reserved.Mc.docx
© 2011 The McGraw-Hill Companies, Inc. All rights reserved..docx

© 2011 The McGraw-Hill Companies, Inc. All rights reserved..docx
© 2010 by The Johns Hopkins University PressConflicting Va.docx

© 2010 by The Johns Hopkins University PressConflicting Va.docx
© 2009 • Journal of Sport Administration & Supervision • Vol. .docx

© 2009 • Journal of Sport Administration & Supervision • Vol. .docx
© 2009 John Wiley and Sons AustraliaDistribution (place).docx

© 2009 John Wiley and Sons AustraliaDistribution (place).docx
© 2003 Applied Scholastics International. All Rights Reser.docx

© 2003 Applied Scholastics International. All Rights Reser.docx
© 2005 Chris Thompson and Katarina Weslien PAJ 82 (2006), pp. .docx

© 2005 Chris Thompson and Katarina Weslien PAJ 82 (2006), pp. .docx
© 2002, The Ripple Effect 1 permission granted to use for.docx

© 2002, The Ripple Effect 1 permission granted to use for.docx
© 2005 Society for the Study of Addiction doi10.1111j.1360-.docx

© 2005 Society for the Study of Addiction doi10.1111j.1360-.docx
¡A Presentar en Español!Prepare To prepare for this activit.docx

¡A Presentar en Español!Prepare To prepare for this activit.docx
You are the Human Resource Director for a 500-.docx

You are the Human Resource Director for a 500-.docx
Recently uploaded
Recently uploaded (20)
Measures of Dispersion and Variability: Range, QD, AD and SD

Measures of Dispersion and Variability: Range, QD, AD and SD
Energy Resources. ( B. Pharmacy, 1st Year, Sem-II) Natural Resources

Energy Resources. ( B. Pharmacy, 1st Year, Sem-II) Natural Resources
On National Teacher Day, meet the 2024-25 Kenan Fellows

On National Teacher Day, meet the 2024-25 Kenan Fellows
Role Of Transgenic Animal In Target Validation-1.pptx

Role Of Transgenic Animal In Target Validation-1.pptx
ICT Role in 21st Century Education & its Challenges.pptx

ICT Role in 21st Century Education & its Challenges.pptx
Beyond the EU: DORA and NIS 2 Directive's Global Impact

Beyond the EU: DORA and NIS 2 Directive's Global Impact
Presentation by Andreas Schleicher Tackling the School Absenteeism Crisis 30 ...

Presentation by Andreas Schleicher Tackling the School Absenteeism Crisis 30 ...
Python Notes for mca i year students osmania university.docx

Python Notes for mca i year students osmania university.docx
This PowerPoint helps students to consider the concept of infinity.

This PowerPoint helps students to consider the concept of infinity.
General Principles of Intellectual Property: Concepts of Intellectual Proper...

General Principles of Intellectual Property: Concepts of Intellectual Proper...
Measures of Central Tendency: Mean, Median and Mode

Measures of Central Tendency: Mean, Median and Mode
Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi

Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
Points 125Case Study 2 HIPAA and IT AuditsCriteriaUnaccept.docx
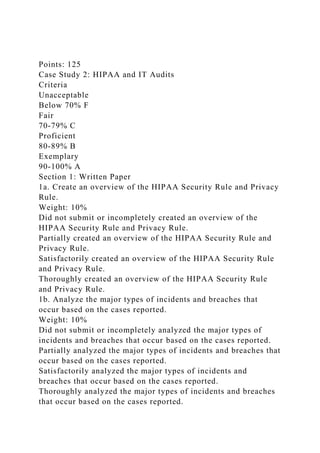
- 1. Points: 125 Case Study 2: HIPAA and IT Audits Criteria Unacceptable Below 70% F Fair 70-79% C Proficient 80-89% B Exemplary 90-100% A Section 1: Written Paper 1a. Create an overview of the HIPAA Security Rule and Privacy Rule. Weight: 10% Did not submit or incompletely created an overview of the HIPAA Security Rule and Privacy Rule. Partially created an overview of the HIPAA Security Rule and Privacy Rule. Satisfactorily created an overview of the HIPAA Security Rule and Privacy Rule. Thoroughly created an overview of the HIPAA Security Rule and Privacy Rule. 1b. Analyze the major types of incidents and breaches that occur based on the cases reported. Weight: 10% Did not submit or incompletely analyzed the major types of incidents and breaches that occur based on the cases reported. Partially analyzed the major types of incidents and breaches that occur based on the cases reported. Satisfactorily analyzed the major types of incidents and breaches that occur based on the cases reported. Thoroughly analyzed the major types of incidents and breaches that occur based on the cases reported.
- 2. 1c. Analyze the technical controls and the non-technical controls that are needed to mitigate the identified risks and vulnerabilities. Weight: 10% Did not submit or incompletely analyzed the technical controls and the non-technical controls that are needed to mitigate the identified risks and vulnerabilities. Partially analyzed the technical controls and the non-technical controls that are needed to mitigate the identified risks and vulnerabilities. Satisfactorily analyzed the technical controls and the non- technical controls that are needed to mitigate the identified risks and vulnerabilities. Thoroughly analyzed the technical controls and the non- technical controls that are needed to mitigate the identified risks and vulnerabilities. 1d. Analyze and describe the network architecture that is needed within an organization, including a medium-sized hospital, in order to be compliant with HIPAA regulations. Weight: 10% Did not submit or incompletely analyzed and described the network architecture that is needed within an organization, including a medium-sized hospital, in order to be compliant with HIPAA regulations. Partially analyzed and described the network architecture that is needed within an organization, including a medium-sized hospital, in order to be compliant with HIPAA regulations. Satisfactorily analyzed and described the network architecture that is needed within an organization, including a medium-sized hospital, in order to be compliant with HIPAA regulations. Thoroughly analyzed and described the network architecture that is needed within an organization, including a medium-sized hospital, in order to be compliant with HIPAA regulations. 1e. Analyze how a hospital is similar to and different from other non-medical organizations in regards to HIPAA compliance. Weight: 10%
- 3. Did not submit or incompletely analyzed how a hospital is similar to and different from other non-medical organizations in regards to HIPAA compliance. Partially analyzed how a hospital is similar to and different from other non-medical organizations in regards to HIPAA compliance. Satisfactorily analyzed how a hospital is similar to and different from other non-medical organizations in regards to HIPAA compliance. Thoroughly analyzed how a hospital is similar to and different from other non-medical organizations in regards to HIPAA compliance. 1f. List the IT audit steps that need to be included in the organization’s overall IT audit plan to ensure compliance with HIPAA rules and regulations. Weight: 10% Did not submit or incompletely listed the IT audit steps that need to be included in the organization’s overall IT audit plan to ensure compliance with HIPAA rules and regulations. Partially listed the IT audit steps that need to be included in the organization’s overall IT audit plan to ensure compliance with HIPAA rules and regulations. Satisfactorily listed the IT audit steps that need to be included in the organization’s overall IT audit plan to ensure compliance with HIPAA rules and regulations. Thoroughly listed the IT audit steps that need to be included in the organization’s overall IT audit plan to ensure compliance with HIPAA rules and regulations. 1g. 3 references Weight: 5% No references provided Does not meet the required number of references; some or all references poor quality choices. Meets number of required references; all references high quality choices. Exceeds number of required references; all references high
- 4. quality choices. 1h. Clarity, writing mechanics, and formatting requirements Weight: 10% More than 6 errors present 5-6 errors present 3-4 errors present 0-2 errors present Section 2: Network Architecture 2a. Create a network architecture diagram based on the description of the network architecture that you defined above for the organization to be compliant with HIPAA regulations. Weight: 15% Did not submit or incompletely created a network architecture diagram based on the description of the network architecture that you defined above for the organization to be compliant with HIPAA regulations. Partially created a network architecture diagram based on the description of the network architecture that you defined above for the organization to be compliant with HIPAA regulations. Satisfactorily created a network architecture diagram based on the description of the network architecture that you defined above for the organization to be compliant with HIPAA regulations. Thoroughly created a network architecture diagram based on the description of the network architecture that you defined above for the organization to be compliant with HIPAA regulations. 2b. Include in the diagram the switches, routers, firewalls, IDS/IPS, and any other devices needed for a compliant network architecture. Weight: 10% Did not submit or incompletely included in the diagram the switches, routers, firewalls, IDS/IPS, and any other devices needed for a compliant network architecture. Partially included in the diagram the switches, routers, firewalls, IDS/IPS, and any other devices needed for a compliant network architecture.
- 5. Satisfactorily included in the diagram the switches, routers, firewalls, IDS/IPS, and any other devices needed for a compliant network architecture. Thoroughly included in the diagram the switches, routers, firewalls, IDS/IPS, and any other devices needed for a compliant network architecture.