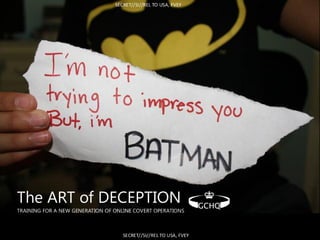
The Art of Deception - Training for a new generation of online covert operations GCHQ of UK+USA joint.
- 1. SECRET//SI//REL TO USA, FVEY 'i;m ‘wprÿss *>f; iWi W you 2ÿMAN The ART of DECEPTION ”GCHQ"TRAINING FOR A NEW GENERATION OF ONLINE COVERT OPERATIONS SECRET//SI//RELTO USA, FVEY
- 2. SECRET//SI//REL TO USA, FVEY HSOCHUMANSCIENCE OPERATIONS CELL SECRET//SI//RELTO USA, FVEY
- 3. SECRET//SI//RELTO USA, FVEY Online HUMINT Strategic Influence JTRIG Disruption and CNA SECRET//SI//RELTO USA, FVEY
- 4. SECRET//SI//RELTO USA, FVEY ANTHROPOLOGY PSYCHOLOGY SOCIOLOGY *** b V < ) .i>- i *s ECONOMICS/ V4 / HISTORY BIOLOGY POLITICAL SCIENCE SECRET//SI//RELTO USA, FVEY
- 5. SECRET//SI//RELTO USA, FVEY Culture Deception Ethnography Influence ANTHROPOLOGY Ethnography Magic PSYCHOLOGY SOCIOLOGY * f A. Personality 'ÿ' » • Compliance Trust i Elicitationt s>/ t t Obedience s s ECONOMICS/ fk / / J Social Networks i / Belief x HISTORY Religion BIOLOGY POLITICAL SCIENCE Key Leader Engagement Neuroscience Global Trends Evolutionary Biology SECRET//SI//RELTO USA, FVEY
- 6. SECRET//SI//RELTO USA, FVEY SCIENCE SIGINT SKILLS SYSTEMS SECRET//SI//RELTO USA, FVEY
- 7. SECRET//SI//RELTO USA, FVEY Online HUMINT Strategic Influence JTRIG Disruption and CNA SECRET//SI//RELTO USA, FVEY
- 8. SECRET//SI//RELTO USA, FVEY ti - ' 1 v *i %i > s We want to build Cyber Magicians. SECRET//SI//RELTO USA, FVEY
- 9. SECRET//SI//RELTO USA, FVEY ocaa Online Covert Action Accreditation SECRET//SI//RELTO USA, FVEY
- 10. SECRET//SI//RELTO USA, FVEY ACNO Key Skill Strands Online HUMINT Influence & Info Ops Disruption & CNA Magic Techniques & Experiment lIndividual Psychology Professionalism Deception Elegance Group Performance Creativity Global IntuitionMedia SECRET//SI//RELTO USA, FVEY
- 11. SECRET//SI//RELTO USA, FVEY ACNO Key Skill Strands Online HUMINT Influence & Info Ops Disruption & CNA Magic Techniques & Experiment I Decisions [Emotional not rational) Individual Psychology Professionalism TrustBELIEF TrustPersonality (OCEAN) |1How to apply x these DeceptionRemote Assessment in Digital Cues Persuasive TechBehaviour Self 10 PRINCIPLES OF SCAMS HINDSIGHT& [whoI am? Motives & exploiting them] BIAS Influence Influence EleganceI nCONFIRMATIONPERSUASION Hofstede Dimensions BIAS i Optimising Deception Channels Building Relationships Hofstede Dimensions i Group i ANCHORING Interaction across cultures Prates of Reflection to assess if weare doing op elÿantly Mirroring / Mimicry iCONSPIRACY STORIES CONFORMITY / QBEDIANCE PRIMING iSocial Penetration Motives Roles Influence/Cascade DIFFUSION OF INNOVATION/Theory Virtual Communities IPerformance CreativitySocial Identity Theory i f Brainstorming Constructing experience in mind of target which should be accepted so they don't realise It How to act / behave Social Proof/ Herding etc NARRATIVE -FtlSelf Presentation in Cyber context ;idtr alternate AGENTICITV Becoming / Targeting GroupReducing PATTERNICI ( Intel /Analysis/ IntuitionMedia How to do some of this in real time so need to understand what you are doing in this psychology Reading from digital tells but going with performance to reduce my risk but satisfy tnquisition Financial Ecosystem of Media Thin Slicing Design, Retention & Trust PROPAGANDA TAA ADVERTISING Sell -own - Earn BRANDING MARKETING TO USA, FVEYSE&
- 12. SECRET//SI//RELTO USA, FVEY ACNO Key Skill Strands Online HUMINT Influence & Info Ops Disruption & Comp Net Attack Mental Health a Psychopathy * 71- 5 USv S3 Decision Making —RationaleChoice Crime & punishment mm [•] % [ÿTag r*iriTi4 Decisions [Emotional not rational! [ÿXI Individual Psychology s ( BELIEF Trust FLAMMED INTERVENTION Personality (OCEAN) 1 DeceptionHow to apply K these Remote Assessment in Digital Cues Persuasive Behaviour Self 10 PRINCIPLES OF SCAMS HINDSIGHT& [whoI am? Motives & exploiting them] BIAS Influence Influence EleganceI CONFIRMATIONPERSUASION Hofstede Dimensions BIAS r Optimising Deception Channels Building Relationships Hofstede Dimensions ! Group i ANCHORING /Interaction across cultures Praces of Reflection to assess if weare doing op eiÿantly Mirroring / MimicryCONSPIRACY STORIES CONFORMITY / QBEDIANCE PRIMING i !Social Penetration i Motives Roles Influence/Cascade DIFFUSION OF INNOVATION Theory /Virtual Communities j Performance CreativityMorality & Ethics Social Identity Theory Brainstorming Constructing experience in mind of target which should be accepted so they don't realise it How to act / behave ! Social Proof/ Herding etc NARRATIVE 1 l 4 Self Presentation in Cyber context :>Cyber Cultures across Organisations CCJ/REidtr alternate AGENTICITV Becoming / Targeting P !S Group Dynamics Reducing |-p| Group Effectiveness PATTERN1C Intel /Analysis j GlobalLegitimisation of Violence IntuitionSOCIAL NETWORKS ) MediaConstructing News System Howto do some of this in real time so need to understand what you are doing In this psychology Reading from digital tells but going with performance to reduce my risk but satisfy Target's Inquisition Financial Ecosystem of Media Thin Slicing Design, Retention & Trust PROPAGANDA TAA fias Management & Legend Building (decided not to include in training) r±ii ADVERTISING Sell -own - Earn BRANDING MARKETING *TO USA, FVEYSE&
- 13. SECRET//SI//RELTO USA, FVEY Human Science Learning Path i A A Strategic Influence (1day) A i A rA Scams And fA f i r JHk r Wj uenceit ! I I i Psychology And Cyber - psychology “ Tells*i Online HUMINTACore Disruption {1hour) i 1 Engineering Fur CNA (e-learning) u rCNA and Disruption •I HSOC m i* IVW( Vitwifinwlnuftlllt ocoo SECRET//SI//RELTO USA, FVEY
- 14. SECRET//SI//REL TO USA, FVEY *ÿ V I IIIf V 1 & *I * 1 C, - *W* I - . i1 V ** > w* * L * * « •1* EI 41 B*v* k, r 4r: •Ifli *< .v*T. Md/ JCK j . _ SECRET//SI//RELTO USA, FVEY
- 15. SECRET//SI//RELTO USA, FVEY •If? * V1 .« # i-4 * ’I i A SECRET//SI//RELTO USA, FVEY
- 16. SECRET//SI//RELTO USA, FVEY Magicians, the military and intelligence 3 fe *rl Vr 4* I # * & L 4. w a f ri* rr f. Vr /A-c //Hr 4 § (gJt1 w *- 1 *ÿf 1 • Hi** ji y 4 ums Iff Jean Robert-Houdin 1856 mission on behalf of Napoleon III to help quell the Marabout-led uprising in Algeria. Jasper Maskelyne 1940s Camouflage work during the Second World War. John Mulholland 1950s CIA work on the application of conjuring to ‘clandestine activities'. SECRET//SI//RELTO USA, FVEY
- 17. P— -1- X Jjn . X X r-. ps . p **’ rt Dissimulation - Hide the real Repackaging DazzlingMasking ~ ttv r_- - PH H B.i IP™” r-n 1-- X SE* 1 i*j , j ipi Jmi w] - ~ u d J W & i|f f**,iflV|jlV .m j * t * * . V* L/Vij ivÿ. x->B / ' J LKPIJ » .» . '3 t r -l t (V r i..*' y: Lt* / 'i .w. -J pJ ™ _|ÿ Th “ SWr"' i 1 it. ._. # “ IV--Jt ' 'ÿ £ ’,1 V * » rp _! PuA "Lÿf jiW- _ rS!H- . *7i -‘ , - laW ,fc J Mimicking Simulation Inventing Decoying Show the false SECRET//SI//RELTO USA, FVEY
- 18. SECRET//SI//RELTO USA, FVEY The psychological building blocks of deception Ex net / Attention SensemakingPerception Behaviour 1 */ V / Affect SECRET//SI//RELTO USA, FVEY
