More Related Content
Similar to Oit2010 model extranet_topologies
Similar to Oit2010 model extranet_topologies (20)
More from Ard van Someren
More from Ard van Someren (20)
Recently uploaded
Industrial Policy - 1948, 1956, 1973, 1977, 1980, 1991Industrial Policy - 1948, 1956, 1973, 1977, 1980, 1991RKavithamani
Oit2010 model extranet_topologies
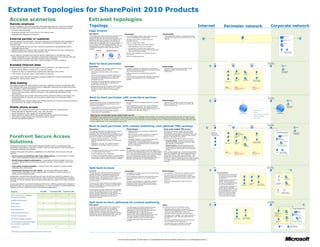
- 1. Extranet Topologies for SharePoint 2010 Products
Access scenarios Extranet topologies
Remote employee
Remote employees can access corporate information and electronic resources anywhere, Topology Internet Perimeter network Corporate network
anytime, without requiring a virtual private network (VPN). Remote employees include:
§ Traveling sales employees.
§ Employees working from home offices or at customer sites.
Edge firewall
§ Geographically dispersed virtual teams. Description Advantages Disadvantage
This configuration uses a reverse proxy server on the § This is the simplest solution that requires the least § This configuration results in a single firewall that Web servers
border between the Internet and the corporate amount of hardware and configuration. separates the corporate internal network from the
External partner or customer network to intercept and then forward requests to the
appropriate Web server located in the intranet. By
§ The entire server farm is located within the Internet. UAG
Application server
External partners can participate in business processes and collaborate with employees of corporate network.
using a set of configurable rules, the proxy server
your organization. You can use an extranet to help enhance the security of data in the verifies that the requested URLs are allowed based on § There is a single point of data:
SQL Server
following ways: the zone from which the request originated. The § Data is located within the trusted network.
requested URLs are then translated into internal URLs.
§ Apply appropriate security and user-interface components to isolate partners and to The following illustration shows an edge firewall
§ Data maintenance occurs in one place.
segregate internal data. topology. § A single farm is used for both internal and
§ Authorize partners to use only sites and data that are necessary for their contributions. Internet
external requests; this ensures that all authorized
Corporate network
§ Restrict partners from viewing other partners’ data. users view the same content. DNS Active Directory
§ Internal user requests are not passed through a domain controller
You can optimize processes and sites for partner collaboration in the following ways: proxy server.
§ Enable employees of your organization and partner employees to view, change, add, and Remote UAG Internal § UAG pre-authenticates users.
delete content to promote successful results for both companies. users Server farm users
§ Configure alerts to notify users when content changes or to start a workflow.
Back-to-back perimeter
TMG or other
firewall product
Branded Internet sites
UAG Router A Router B
Users
Description Advantages Disadvantage
Publish branded, targeted content to partners and customers in the following ways:
A back-to-back perimeter topology isolates the server § Content is isolated to a single farm on the extranet, § The back-to-back perimeter topology requires
§ Target content based on product line or customer profile. farm in a separate perimeter network. simplifying sharing and maintenance of content across additional network infrastructure and
§ Segment content by implementing separate site collections within a farm. § All hardware and data reside in the perimeter the intranet and the extranet. configuration. Administrator
workstation
network. § External user access is isolated to the perimeter Application
§ Limit content access and search results based on audience. server SQL Server DNS
§ The server farm roles and network infrastructure network.
This scenario works well with an extranet topology designed for content publishing and servers can be separated across multiple layers. § If the extranet is compromised, damage is potentially
optimized for hosting static content. Combining the network layers can reduce the limited to the affected layer or to the perimeter
complexity and cost. network. Application
SQL Server Active Directory
server
§ Each layer can be separated by additional routers Web servers domain controller
Web hosting or firewalls to ensure that only requests from
specific layers are allowed.
Microsoft® SharePoint® 2010 Products include the capability to isolate and separate data
§ Requests from the internal network can be directed
from different Web sites while sharing service application resources across these same sites. through the internal-facing ISA server or routed
Layer 1 Layer 2 Layer 3
Web servers Application servers and DNS and domain
This capability is called multi-tenancy. through the public interface of the perimeter database servers controller
· Multi-tenancy of services creates a true hosting environment and makes it possible to share network.
service resources across customers (tenants), while partitioning data based on site
subscriptions.
· Site subscriptions group tenant data across all site collections owned by the tenant, and
provide the ability to separate and group each tenant's data in an otherwise shared Back-to-back perimeter with cross-farm services TMG or other
environment. UAG firewall product
· Administrators can centrally deploy and manage features and services, while giving tenants Description Advantages Disadvantages Users
full control over the usage and experience. In some scenarios, services are better optimized by § Services are centrally managed inside the corporate § Some service applications require two-way trust
sharing service applications across farms, even in network. between domains, for example, User Profile and
extranet environments. § Service applications that involve many contributors, Secure Store Service.
Mobile phone access
Administrator
§ A farm inside the corporate network hosts service such as Managed Metadata, are located where the workstation
applications that can be shared across farms. contributor accounts are located. Special access is not
SharePoint 2010 Products include access to SharePoint sites from mobile phones: required for the perimeter network. ·
§ One or more farms in the perimeter network User Profile
· Manipulate data on SharePoint sites: view, edit, add items consumes service applications. · Search
· Search (documents, lists, people, line-of-business data) Consuming farm Services farm
· Business Data Connectivity
· Mobile document viewers (Word, Microsoft® Excel®, Microsoft® PowerPoint®) Planning for services that access external data sources
· Managed Metadata
· Alerts sent to mobile phones from SharePoint 2010 Products Important: Service applications that access external data sources by using a delegated Windows identity (Excel Services, PerformancePoint Services, and Visio Services)
put additional requirements on the environment. External data sources must reside within the same domain as the SharePoint farm that hosts the service. If farm servers · Secure Store
· Solution development platform
are split between two domains, the application servers must reside in the same domain as the external data sources. If external data sources do not reside within the same
domain, authentication to the external data sources will fail.
TMG or other
Back-to-back perimeter with content publishing (and optional TMG caching) UAG Router A Router B firewall product
Users
Description Disadvantages Using cache-enabled TMG servers
This topology adds content publishing to the back-to- § Additional hardware is required to maintain two In environments where content does not require
Optional:
back perimeter topology. By adding content separate farms. authentication, you can optimize performance by Central Content staging farm Administrator
cache-enabled
publishing, sites and content that are developed inside implementing caching features of Forefront TMG. TMG
Forefront Secure Access
§ Data overhead is greater. Content is maintained TMG servers Administration workstation
the corporate network can be published to the server and coordinated in two different farms and caching can be configured in addition to the caching (instead of UAG)
Application DNS Web servers
farm that is located in the perimeter network. networks. features in SharePoint Server 2010. server
Central
§ Requires two separate farms — one in the § Changes to content in the perimeter network are TMG provide the following two types of caching:
Solutions
SQL Server Administration
corporate network and the other in the perimeter not reflected in the corporate network. § Forward caching Forward caching provides
network. Consequently, content publishing to the perimeter cached Web objects to internal users who make Active Directory SQL Server
Application domain controller
§ Publishing is one-way. Any content created or domain is not a workable choice for extranet sites Web requests to the Internet. Web servers
server
modified in the perimeter network is unique. that are collaborative. § Reverse caching Reverse caching provides
One-way data stream
Microsoft® Forefront® Unified Access Gateway (Forefront UAG) provides secure Web SQL Server for content publishing
cached content to external Internet clients who
publishing of applications, using SSL. Forefront UAG provides access to internal resources Notes
Advantages make requests to internal Web servers published
for remote employees and partners. by TMG.
§ Customer-facing and partner-facing content is isolated The illustration shows the path of content deployment
Forefront UAG adds the following capabilities to the SharePoint 2010 Products extranet in a separate perimeter network. from the Central Administration site in the content staging TMG caching enables you to scale out beyond the Layer 1 Layer 2 Layer 3 DNS Active Directory
solution: § Content publishing can be automated. farm to the Central Administration site in the destination limits of a single farm by improving performance Web servers Application servers and DNS and domain domain controller
farm. The Central Administration site is typically installed database servers controller
§ If content in the perimeter network is compromised or where Web servers might be a bottleneck. This
· Secure access to SharePoint sites from mobile devices - Authentication of mobile on one of the application servers. The illustration
enables you to improve performance when the
corrupted as a result of Internet access, the integrity separately calls out the Central Administration site to
users using a dedicated interface for mobile devices. of the content in the corporate network is retained. maximum number of Web servers has been reached
show the role of this site in content deployment.
· Health-based endpoint authorization - Access policies that are based not only on or to reduce the number of Web servers that are
the user's identity and the information exposed, but also on the condition of the client required.
endpoint.
· Information leakage mitigation - Cleanup of the client endpoint, including cache,
Split back-to-back
TMG or other
temporary files, and cookies. UAG firewall product
· Authenticate directly from rich clients – Use Microsoft Office Forms Based Description Advantages Disadvantages
Authentication (MSOFBA) or basic authentication to enable rich client programs to This topology splits the farm between the perimeter and About this diagram:
§ Computers running SQL Server are not hosted inside § The complexity of the solution is greatly increased.
directly access SharePoint sites. corporate networks. The computers running Microsoft
the perimeter network. · Application servers are hosted inside
SQL Server® database software are hosted inside the § Intruders who compromise perimeter network
the perimeter network. This option
Additionally, Forefront UAG DirectAccess provides remote users with the experience of a corporate network. Web servers are located in the § Farm components within both the corporate network resources might gain access to farm content stored is illustrated by blue servers inside
seamless connection to the internal network. When Forefront UAG DirectAccess is enabled, perimeter network. The application server computers can and the perimeter network can share the same in the corporate network by using the server farm the dashed line.
DNS SQL Server
requests for internal network resources are directed securely, without the need to connect be hosted in either the perimeter network or the databases. accounts. · Application servers can optionally be
corporate network. Inter-farm communication is split across two deployed inside the corporate
to a VPN. § Content can be isolated to a single farm inside the §
network, with the database servers.
If the server farm is split between the perimeter network corporate network, which simplifies sharing and domains. Application
This option is illustrated by the gray Application
If your organization has previously deployed ISA Server 2006 to publish earlier releases of and the corporate network, a domain trust relationship is maintaining content across the corporate network servers inside the dashed line. servers Active Directory servers
Web servers domain controller SQL Server
SharePoint, you can continue to use this product or move to Forefront Threat Management required. In this scenario, the perimeter domain must and the perimeter network. · To optimize search performance and
Gateway (TMG) to publish SharePoint 2010 Products applications. trust the corporate domain. crawling, place the application
servers inside the corporate network
The only scenario in which a domain trust is not required with the database servers. You can
is if the Web and application servers are in the perimeter also add the Web server role to the
Feature ISA 2006 Forefront TMG Forefront UAG network, the database servers are in the corporate index server inside the corporate DNS Active Directory
network, and SQL authentication is used. However, if the network and configure this Web domain controller
Web and application servers are split between the server for dedicated use by the
Built-in features for configuring networks and SQL authentication is used, a trust index server for content crawling.
SharePoint publishing relationship is required.
Network load balancing
Split back-to-back optimized for content publishing
TMG or other
UAG firewall product
Array support
Description Notes
Mobile access If you plan to publish content from a staging farm § The data stream for content publishing travels The illustration shows the following choices:
inside the corporate network to the database from the Central Administration site in the § Application servers reside in the corporate Content Staging Farm
Rich authentication servers that host content for the extranet (also staging farm to the Central Administration site in network with the database servers. This requires
located inside the corporate network), you can the destination farm. If the Central a one-way trust relationship in which the
Web
Endpoint health detection optimize the farm by hosting the application servers, Administration site is inside the corporate perimeter domain trusts the corporate domain.
DNS Crawl server,
SQL
servers
including the Central Administration site, inside the Web server, and Central
network, the content publishing data stream does Central
Server
corporate network for the following reasons: § The query role is installed in the same network as Administration
Granular access policies not travel through the firewall between the
the databases, which optimizes performance of
Administration
perimeter network and the corporate network. SQL
Active Directory
this role. Server
Information leakage mitigation § Crawling takes place inside the corporate
Web servers domain controller
SQL
§ The Central Administration site for the production
network. Server One-way data stream
Unified portal for publishing multiple farm is installed on the index server. Application
for content publishing
server
§ The Web server role is installed on the crawl
line-of-business applications server for dedicated use by the crawl role.
DNS Active Directory
DirectAccess * domain controller
* DirectAccess is partially supported for Forefront TMG 2010
© 2010 Microsoft Corporation. All rights reserved. To send feedback about this documentation, please write to us at ITSPdocs@microsoft.com.