3D Password for Secure Authentication
•Download as PPTX, PDF•
0 likes•5 views
3D Password for Secure Authentication
Report
Share
Report
Share
Recommended
Recommended
More Related Content
Similar to 3D Password for Secure Authentication
Similar to 3D Password for Secure Authentication (20)
Data hiding in graphical password authentication using combination

Data hiding in graphical password authentication using combination
ipas implicit password authentication system ieee 2011

ipas implicit password authentication system ieee 2011
Authentication Schemes for Session Passwords using Color and Images

Authentication Schemes for Session Passwords using Color and Images
Graphical Based Password for Android Phones using Keystroke Dynamics - A Survey

Graphical Based Password for Android Phones using Keystroke Dynamics - A Survey
Graphical Based Password for Android Phones using Keystroke Dynamics - A Survey

Graphical Based Password for Android Phones using Keystroke Dynamics - A Survey
Effectiveness of various user authentication techniques

Effectiveness of various user authentication techniques
Database Security Two Way Authentication Using Graphical Password

Database Security Two Way Authentication Using Graphical Password
Keystroke Dynamics Authentication with Project Management System

Keystroke Dynamics Authentication with Project Management System
Keystroke Dynamics Authentication with Project Management System

Keystroke Dynamics Authentication with Project Management System
Recently uploaded
Recently uploaded (20)
Crafting the Perfect Measurement Sheet with PLM Integration

Crafting the Perfect Measurement Sheet with PLM Integration
Microsoft 365 Copilot; An AI tool changing the world of work _PDF.pdf

Microsoft 365 Copilot; An AI tool changing the world of work _PDF.pdf
AI/ML Infra Meetup | Reducing Prefill for LLM Serving in RAG

AI/ML Infra Meetup | Reducing Prefill for LLM Serving in RAG
APVP,apvp apvp High quality supplier safe spot transport, 98% purity

APVP,apvp apvp High quality supplier safe spot transport, 98% purity
AI/ML Infra Meetup | Improve Speed and GPU Utilization for Model Training & S...

AI/ML Infra Meetup | Improve Speed and GPU Utilization for Model Training & S...
Tree in the Forest - Managing Details in BDD Scenarios (live2test 2024)

Tree in the Forest - Managing Details in BDD Scenarios (live2test 2024)
Mastering Windows 7 A Comprehensive Guide for Power Users .pdf

Mastering Windows 7 A Comprehensive Guide for Power Users .pdf
5 Reasons Driving Warehouse Management Systems Demand

5 Reasons Driving Warehouse Management Systems Demand
Implementing KPIs and Right Metrics for Agile Delivery Teams.pdf

Implementing KPIs and Right Metrics for Agile Delivery Teams.pdf
AI/ML Infra Meetup | Perspective on Deep Learning Framework

AI/ML Infra Meetup | Perspective on Deep Learning Framework
how-to-download-files-safely-from-the-internet.pdf

how-to-download-files-safely-from-the-internet.pdf
AI/ML Infra Meetup | ML explainability in Michelangelo

AI/ML Infra Meetup | ML explainability in Michelangelo
3D Password for Secure Authentication
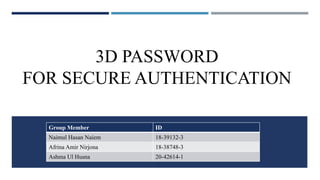
- 1. 3D PASSWORD FOR SECURE AUTHENTICATION Group Member ID Naimul Hasan Naiem 18-39132-3 Afrina Amir Nirjona 18-38748-3 Ashma Ul Husna 20-42614-1
- 2. CONTENTS Abstract Introduction Literature Review Proposed System Architectural Diagram 3D Virtual Environment Applications Conclusion
- 3. ABSTRACT Multifactor authentication scheme 3D password Authentication Biometric Virtual environment
- 4. INTRODUCTION Various systems to provide security using various authentication schemes . It can be either an identification system or a authentication system. Example:- face, fingerprints, iris etc. More secure against different attacks such as timing attacks, well-studied attacks etc.
- 5. LITERATURE REVIEW Dhatri Raval, in her paper explains about the various already available password authentication schemes such as knowledge based, token based, recognition based, biometrics based.[1] Parul, Neetu Verma, in their paper discuss about the drawbacks of the already available authentication schemes. They explained that people use textual passwords which are easy to remember and they can be cracked easily using Brute force attacks. [2] Nayana S, Dr. Niranjanamurthy, Dr. Dharmendra Chahar, in their paper explains about the advantages and disadvantages of the 3D password. They explained that the 3D password is better than the other existing authentication systems but on the other hand it is expensive.[3] Tejal M. Kognule, Monica G. Gole, Priyanka T. Dabade, Sagar B. Gawade, in their paper explains about the objects inside the 3D virtual environment. They found that the objects must be clearly visible and identical to each other. [4]
- 6. PROPOSED SYSTEM • combination of both the authentication schemes together • combines both recall-based (for example: textual passwords) and recognition-based (for example: graphical passwords) • multi password and multi factor authentication scheme
- 9. 3D VIRTUAL ENVIRONMENT 1.Implemented by 3D virtual environment 3D password solved in mathematical problems. This is: a.Time Complexity b.Space Complexity
- 10. APPLICATIONS ATM Personal Digital Assistance Desktop Computers & laptop logins Web Authentication Security Analysis Networking Nuclear & Military Areas Airplanes & Jet fighters
- 11. CONCLUSION multi-factor and multi-password authentication combine the available authentication schemes upcoming authentication schemes by adding it as a response to actions performed on an object the resulting password space becomes very large compared to any existing authentication schemes
- 12. REFERENCE [1] A.B.Gadicha, V.B.Gadicha-"Virtual Realization using 3D Password" International Journal of Electronics and Computer Science Engineering, ISSN: 2277-1956, pp216-223, 2016. [2] A.B.Gadicha, V.B.Gadicha-"Virtual Realization using 3D Password" International Journal of Electronics and Computer Science Engineering, ISSN: 2277-1956, pp216-223, 2016. [3] V.Sindhuja, S.Shiyamaladevi, S.Vinitha-“A Review of 3D Protected Password” International Journal of Innovative Research in Computer and Communication Engineering, ISSN: 2320-9801, pp3995-4001, 2016. [4] Pooja M. Shelke, F. M. Shelke, Mr. B. G. Pund-“Advance Authentication Technique: 3D Password” International Journal on Recent and Innovation Trends in Computing and Communication, ISSN: 2321- 8169, pp632-635, 2016.
- 13. THANK YOU PLEASE ASK IF YOU HAVE ANY QUESTIONS REGARDING THIS SESSION?