Computer Laboratory Rules and Guidelines
•
2 likes•844 views
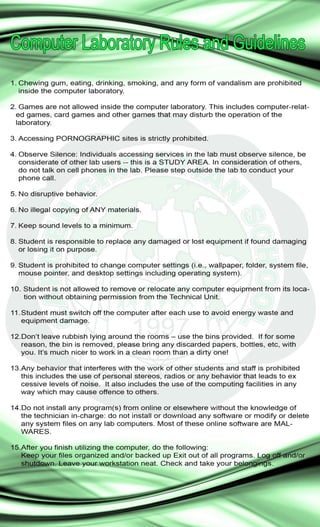
Computer Laboratory Rules and Guidelines
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
More from Mark John Lado, MIT
More from Mark John Lado, MIT (20)
Exploring Parts of Speech, Creating Strong Objectives, and Choosing the Right...

Exploring Parts of Speech, Creating Strong Objectives, and Choosing the Right...
Optimizing Embedded System Device Communication with Network Topology Design

Optimizing Embedded System Device Communication with Network Topology Design
Embedded Systems IO Peripherals Wireless Communication.pdf

Embedded Systems IO Peripherals Wireless Communication.pdf
Implementing the 6S Lean Methodology for Streamlined Computer System Maintena...

Implementing the 6S Lean Methodology for Streamlined Computer System Maintena...
ISO IEC 25010 2011 Systems and Software Quality Requirements and Evaluation S...

ISO IEC 25010 2011 Systems and Software Quality Requirements and Evaluation S...
4 Module - Operating Systems Configuration and Use by Mark John Lado

4 Module - Operating Systems Configuration and Use by Mark John Lado
3 Module - Operating Systems Configuration and Use by Mark John Lado

3 Module - Operating Systems Configuration and Use by Mark John Lado
1 Module - Operating Systems Configuration and Use by Mark John Lado

1 Module - Operating Systems Configuration and Use by Mark John Lado
2 Module - Operating Systems Configuration and Use by Mark John Lado

2 Module - Operating Systems Configuration and Use by Mark John Lado
PART 1 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...

PART 1 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...
PART 2 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...

PART 2 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...
PART 3 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...

PART 3 CT-318-Microprocessor-Systems Lesson 3 - LED Display by Mark John Lado...
Computer hacking and security - Social Responsibility of IT Professional by M...

Computer hacking and security - Social Responsibility of IT Professional by M...
A WIRELESS DIGITAL PUBLIC ADDRESS WITH VOICE ALARM AND TEXT-TO-SPEECH FEATURE...

A WIRELESS DIGITAL PUBLIC ADDRESS WITH VOICE ALARM AND TEXT-TO-SPEECH FEATURE...
IT Security and Management - Semi Finals by Mark John Lado

IT Security and Management - Semi Finals by Mark John Lado
IT Security and Management - Prelim Lessons by Mark John Lado

IT Security and Management - Prelim Lessons by Mark John Lado
Recently uploaded
APM Welcome
Tuesday 30 April 2024
APM North West Network Conference, Synergies Across Sectors
Presented by:
Professor Adam Boddison OBE, Chief Executive Officer, APM
Conference overview:
https://www.apm.org.uk/community/apm-north-west-branch-conference/
Content description:
APM welcome from CEO
The main conference objective was to promote the Project Management profession with interaction between project practitioners, APM Corporate members, current project management students, academia and all who have an interest in projects.APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across SectorsAssociation for Project Management
This presentation was provided by William Mattingly of the Smithsonian Institution, during the fourth segment of the NISO training series "AI & Prompt Design." Session Four: Structured Data and Assistants, was held on April 25, 2024.Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"National Information Standards Organization (NISO)
Recently uploaded (20)
Measures of Central Tendency: Mean, Median and Mode

Measures of Central Tendency: Mean, Median and Mode
APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across Sectors
Beyond the EU: DORA and NIS 2 Directive's Global Impact

Beyond the EU: DORA and NIS 2 Directive's Global Impact
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
Z Score,T Score, Percential Rank and Box Plot Graph

Z Score,T Score, Percential Rank and Box Plot Graph
Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
SECOND SEMESTER TOPIC COVERAGE SY 2023-2024 Trends, Networks, and Critical Th...

SECOND SEMESTER TOPIC COVERAGE SY 2023-2024 Trends, Networks, and Critical Th...
Unit-V; Pricing (Pharma Marketing Management).pptx

Unit-V; Pricing (Pharma Marketing Management).pptx
