Problem 7PurposeBreak apart a complicated system.ConstantsC7C13.docx
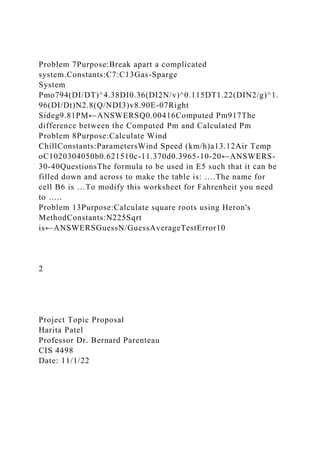
- 1. Problem 7Purpose:Break apart a complicated system.Constants:C7:C13Gas-Sparge System Pmo794(DI/DT)^4.38DI0.36(DI2N/v)^0.115DT1.22(DIN2/g)^1. 96(DI/Dt)N2.8(Q/NDI3)v8.90E-07Right Sideg9.81PM←ANSWERSQ0.00416Computed Pm917The difference between the Computed Pm and Calculated Pm Problem 8Purpose:Calculate Wind ChillConstants:ParametersWind Speed (km/h)a13.12Air Temp oC1020304050b0.621510c-11.370d0.3965-10-20←ANSWERS- 30-40QuestionsThe formula to be used in E5 such that it can be filled down and across to make the table is: ….The name for cell B6 is …To modify this worksheet for Fahrenheit you need to ….. Problem 13Purpose:Calculate square roots using Heron's MethodConstants:N225Sqrt is←ANSWERSGuessN/GuessAverageTestError10 2 Project Topic Proposal Harita Patel Professor Dr. Bernard Parenteau CIS 4498 Date: 11/1/22
- 2. Project Topic Proposal The proposed topic is cyber security. My proposal in this software development project of this class is to develop cyber security software to be a tool that protects systems against malicious attacks and online threats. The software should b able to detect and block threats that can not be detected by antivirus. The technology to be used will be defensive Artificial intelligence. Cybersecurity professional experts can utilize guarded man-made consciousness (simulated intelligence) to distinguish or stop cyberattacks. Sagacious cybercriminals use innovations like hostile computer-based intelligence and ill- disposed AI since they are harder for conventional network protection instruments to identify. Offensive AI incorporates
- 3. profound fakes, bogus pictures, personas, and recordings that convincingly portray individuals or things that never occurred or don't exist. Noxious entertainers can utilize ill-disposed AI to fool machines into breaking down by giving them mistaken information. Cybersecurity professionals can utilize cautious computer-based intelligence to recognize and prevent hostile man-made intelligence from estimating, testing, and figuring out how the framework or organization's capabilities. Defensive AI can reinforce calculations, making them more challenging to break. Network protection analysts can direct more extreme weakness tests on AI models. Artificial intelligence cautious apparatuses can precisely anticipate assault vectors, pinpoint the delicate region of the organization and frameworks, and even set it up groups for approaching occasions(Graham, Olson,& Howard, 2016). The progression of computerized data is developing a regular schedule making it progressively challenging to oversee and structure it or even to isolate what is significantly based on what is pointless. Confronted with this test, new encouraging advancement innovations are being created to bring 'information examination's to the following developmental level. Man-made consciousness (man-made intelligence), specifically, is supposed to become huge in many fields. A few types of computer-based intelligence empower AI like profound learning can be utilized to perform prescient investigation. Their true capacity for the guard space is enormous as simulated intelligence arrangements are supposed to arise in basic fields, for example, digital protection, choice of emotionally supportive networks, risk the executives, design acknowledgment, digital circumstance mindfulness, projection, malware location, and information relationship to give some examples. We have proactively seen huge technological progress in self- driving vehicles where an examination of the general climate is made continuously and computer-based intelligence frameworks steer vehicles independently under unambiguous conditions.
- 4. One of the expected utilization of man-made intelligence in digital safeguards might be to empower the setting up of self- designing organizations. It would imply that computer-based intelligence frameworks could recognize weaknesses (programming bugs) and perform reaction activities like self- fixing. This opens better approaches to fortifying interchanges and data frameworks' security by giving organization flexibility, counteraction, and assurance against digital dangers. Digital specialists concur that the human framework joining is a key component that should be available in a simulated intelligence network safety framework. Assuming we consider the fast expected to play out any digital activity just machines are fit for responding proficiently in the beginning phases of serious digital assaults. Man-made intelligence can hence conquer the shortages of conventional digital protection instruments(Austin, 2020). . It is likewise a strong component ready to improve malware discovery rates utilizing a gauge of digital insight information. Computer-based intelligence online protection frameworks can gain from signs of give and take and might have the option to match the attributes of little hints regardless of whether they are dispersed all through the organization. References Austin, G. (2020). Cyber security education: Principles and policies. Routledge Studies in Conflict, Security and Technology. Graham, J., Olson, R., & Howard, R. (2016). Cyber security essentials. CRC Press.
- 5. Assignment: Project Plan Details Your assignment this week includes the following: · A detailed list and description of each feature and function your project will contain. This will likely correspond to each page or screen in your application · A detailed list of all the data that your project will use: each table/file and all the columns/fields within each · A detailed plan of what functions you’ll be working on and expect to complete each week you'll develop detailed plans as to what functionality your project will include, and your schedule. In addition to the assignment, there is a discussion in which you'll informally describe your project for your classmates. That should be quite interesting to see what everyone is doing. There were several very interesting ideas expressed in the first assignment and I'm looking forward to seeing the detailed plans. Note: Keep the topic the same as in the project topic proposal assignment. 6. Electrical engineers use a color-coded system to identify the value of a resistor. Thus, a resistor with the banding colors green, blue,
- 6. yellow, and gold has a value of 560 kΩ�5%. Construct a worksheet similar to Figure 4.18. The user enters the digit 1 next to the appropriate color for each band and the resistance is computed in C19 with the help of table G3:I13. The multiplier is 10 raised to the power in column A. Check your results on the Internet. Cell C19 as the custom format [<0.001]##0E+0;[<1000]#0.00;##0E+0, which gives exponents in multiples of three. We shall expand on this problem in later chapters. Clearly, we really should arrange things so that there is only a single 1 in each of the Bar columns. 7. Create a worksheet to solve the following system of equations using matrix algebra: 3x1�4x2 + 5x3 + 6x4 + 2x5 ¼ 62:5 x1 + 2x2 + 3x3 + 4x4 + 5x5 ¼ 19:5 6x1 + 7x2�4x3 + 2x4�x5 ¼ 15 5x1�5x2 + 2x3 + 5x4 + 7x5 ¼ 32
- 7. �3x1 + 5x2 + 6x3 + 2x4 + x5 ¼ 16 72 CHAPTER 4 Using Functions PROBLEMS - CHAPTER 4 2. *To measure the index of refraction μ of a liquid with an Abbe refractometer, a drop is placed between two prisms and a mirror is rotated until the boundary of the light and dark zones align with the crosshairs in a microscope. The index of refraction of the liquid is given by the following equation in which the angle of rotation is θ and μg is the refractive index of glass (1.51). For liquid A, the value of θ was found to be 150°, and for B, it was 75°. Using a worksheet, find μ for each liquid: μ¼p1ffiffiffi 2 μ2g� sin2 θ � 1=2� + sin θ � �
- 8. 7. The possibility of a typo increases as the formula to be entered getsmore complex. Sometimes, it is advisable to break the problem into steps and obtain answers in which you have confidence. Then, you can attempt to code the problem in a simple formula. We will look at an example. An engineer working with a gas-sparging system needs to compute Pm from the equation: log10 Pm Pmo � � ¼ 192 Dl DT � �4:38 D2 l
- 9. N v !0:115 DlN 2 g � �1:96 Dl DT � � Q ND3 l � � Make a worksheet similar to Figure 2.28 by computing the four variable terms on the right-hand side of the equation separately in 1 2 3 4 5 6 7 8
- 10. 9 A B C D E Gas-Sparge System Pmo 794 (Dl/DT)^4.38 0.004768 Dl 0.36 (Dl²N/v)^0.115 4.415957 DT 1.22 (DlN²/g)^1.96(Dl/Dt) 0.486494 N 2.8 (Q/NDl³) 0.031844 v 8.93E-07 Right side 0.06263 g 9.81 Pm 917 Q 0.00416 Computed Pm 917 n FIGURE 2.28 34 CHAPTER 2 Basic Operations Chapter 2 Problems E2:E5. They are combined with the 192 constant in E6 and Pm is computed in E7. You should check each term with a hand calculator. Then, in B9, enter a single formula to compute Pm. In a real-life situation, once agreement has been reached between B9 and E7, the range D2:E7 could be deleted. 8. *When a person stands in the wind, the air feels colder than when the air is still. The apparent temperature is called the wind chill (Twc) and
- 11. is computed from the formula shown in Figure 2.29 where Ta is the air temperature. The values shown for parameters a through d are for degrees Celsius computations. Ta is the air temperature and V the wind velocity. For Fahrenheit computations, use 35.74, 0.6215, �35.75, and 0.4275 for the parameters and express V in mph. The cells B4:B7 have been named by the letters to the right.What formula can be used in E5 such that it can be filled down and across to make the table? Be careful with the name for the cell B6. Can you easily modify your worksheet for Fahrenheit work? 13. Recursion may be used to solve certain mathematical problems. The Babylonian (also called Heron’s) method to find square roots is summarized by the recursive equation: xi+ 1 ¼ 1 2
- 12. xi + N xi � � : Or in words, (1) make a guess, (2) divide your original number by your guess, (3) find the average of these two numbers, and (4) use this average as your next guess. Make a worksheet similar to that in Figure 2.33 and test it for various values of N. Later, we shall meet the SQRT function. 37Play It Again, Sam