IRIS SOLUTIONS- IEEE 2011 PROJECT TITLES FOR ME,M.TECH,M.SC, MCA, BE,B.TECH
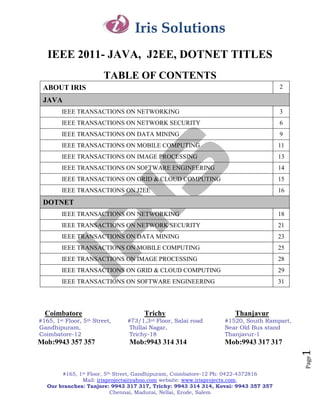
- 1. Iris Solutions IEEE 2011- JAVA, J2EE, DOTNET TITLES TABLE OF CONTENTS ABOUT IRIS 2 JAVA IEEE TRANSACTIONS ON NETWORKING 3 IEEE TRANSACTIONS ON NETWORK SECURITY 6 IEEE TRANSACTIONS ON DATA MINING 9 IEEE TRANSACTIONS ON MOBILE COMPUTING 11 IEEE TRANSACTIONS ON IMAGE PROCESSING 13 IEEE TRANSACTIONS ON SOFTWARE ENGINEERING 14 IEEE TRANSACTIONS ON GRID & CLOUD COMPUTING 15 IEEE TRANSACTIONS ON J2EE 16 DOTNET IEEE TRANSACTIONS ON NETWORKING 18 IEEE TRANSACTIONS ON NETWORK SECURITY 21 IEEE TRANSACTIONS ON DATA MINING 23 IEEE TRANSACTIONS ON MOBILE COMPUTING 25 IEEE TRANSACTIONS ON IMAGE PROCESSING 28 IEEE TRANSACTIONS ON GRID & CLOUD COMPUTING 29 IEEE TRANSACTIONS ON SOFTWARE ENGINEERING 31 Coimbatore Trichy Thanjavur #165,1stFloor, 5th Street, #73/1,3rd Floor, Salai road #1520, South Rampart, Gandhipuram, Thillai Nagar, Near Old Bus stand Coimbatore-12 Trichy-18 Thanjavur-1 Mob:9943 357 357 Mob:9943 314 314 Mob:9943 317 317 1 Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 2. Iris Solutions About Iris "Iris Solutions - A Boon for Young Technocrats" Global presence of technocrats is no more a dream in this world. We make it possible by ensuring all the quality standards within an individual which has to be the identity of a successful technocrat. Irrespective of the technologies and the domain in which a particular project gets shaped, we support all kind of student needs in terms of monetary values as well as the time factor. Students apart from doing a particular project should know how the project is getting shaped. We are aware in making this thing to happen. Research and Development plays a vital role in enhancing one‘s self development in terms of up gradation and moving forward. When you are searching for a good channel to inhibit yourself with such a platform, IRIS comes handy. Apart from providing simulation based training, we also provide industrial experts in sharing their valuable suggestions and even Industry oriented training at required cases. In short we strive hard to fulfill the student requirements in terms of each and every department of the developing their skills. 2 Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 3. Iris Solutions JAVA TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORKING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJNW01 Self-Reconfigurable Wireless In this project, ARS outperforms existing 2011 Mesh Networks failure-recovery schemes in improving channel-efficiency by more than 90% and in the ability of meeting the application bandwidth demands. Multihop wireless mesh networks experience frequent link failures caused by channel interference. 2 ISJNW02 Delay-Optimal Opportunistic In this project, the design of multiuser 2011 Scheduling and Approximations opportunistic packet schedulers for users sharing a time-varying wireless channel from performance and robustness points of view. Markov decision process framework used to compute and characterize mean- delay-optimal scheduling policies. 3 ISJNW03 Adaptive Fault-Tolerant QoS Use of fault tolerance mechanisms through 2011 Control Algorithms for redundancy improves query reliability in the Maximizing System Lifetime of presence of unreliable wireless Query-Based Wireless Sensor communication and sensor faults; it cause Networks the energy of the system to be quickly depleted. 4 ISJNW04 Optimizing Resource Conflicts in The two factors are formulated in a matrix 2011 Workflow Management Systems form and the optimal solution is found by applying concepts of the generalized eigenvalue analysis. A rough outline of an agent-based architecture is proposed to achieve runtime integration of our algorithm into a functional WfMS. 5 ISJNW05 Predictable high performance In this project we present a design and 2011 Computing using Feedback and implementation of a predictable HPC admission control system using feedback control and admission control. By creating a virtualized application layer and opportunistically 3 multiplexing is the concurrent application. Page 6 ISJNW06 Attribute-Based Access Control A cryptographic approach to enforce a fine- 2011 #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 4. Iris Solutions with Efficient Revocation in Data grained access control on the outsourced Outsourcing Systems data that is dual encryption protocol exploiting the combined features of the cipher text policy attribute-based encryption and group key management algorithm. 7 ISJNW07 Load Balance with Imperfect A novel load balancing algorithm that is 2011 Information in Structured Peer-to- unique in that each participating peer is Peer Systems based on the partial knowledge of the system to estimate the probability distributions of the capacities of peers and the loads of virtual servers, resulting in imperfect knowledge of the system state. 8 ISJNW08 A Distributed Algorithm for A distributed algorithm used for computing 2011 Finding All Best Swap Edges of a all best swap edges for a minimum-diameter Minimum-Diameter Spanning spanning tree. The best possible way of Tree reconnecting the network is to replace the failed link by a single other link called a swap link. A swap that minimizes the diameter of the resulting swap tree. 9 ISJNW09 Decomposing Workload Bursts We present a new framework for runtime 2011 for Efficient Storage Resource scheduling of a client‘s workload based on Management decomposition and recombination of the request stream. Finally, we show how the framework can be used to improve estimates of the aggregate resource requirements of multiple concurrent clients. 10 ISJNW10 Monitoring The Impact Of P2P We present an classification for broadband 2011 Users On A Broadband users into a P2P and non-P2P group based Operator‘s Network Over time on the amount of communication partners (―peers‖) they in a dedicated timeframe. We derive their impact on network characteristics like the number of active users and their aggregate bandwidth. 11 ISJNW11 Metadata Distribution and This paper makes two contributions. First, 2011 Consistency Techniques for we present a dynamic metadata distribution Large-Scale Cluster File Systems policy (DDG) to improve the metadata throughput by using a triple-defined distribution. Second, S2PC-MP reduces the overhead of failure-free execution and ensures quick recovery in the presence of metadata server failures or client failures. 4 12 ISJNW12 Flexible Robust Group Key A novel 2-round GKA protocol that offers a 2011 Page Agreement natural trade-off between message size and #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 5. Iris Solutions the desired level of fault tolerance. The new protocol is also the disruption attack by the malicious insider. 13 ISJNW13 Site-Based Partitioning And The pagerank algorithm is an important 2011 Repartitioning Techniques For component. The pagerank computation Parallel Page Rank Computation which is frequently repeated must be performed in parallel with high-efficiency and low-preprocessing overhead while considering the initial distributed nature of the web matrices. 14 ISJNW14 Stabilization of Flood Sequencing In this project we discuss a family of four 2010 Protocols in Sensor Networks flood sequencing protocols that use sequence numbers to distinguish between fresh and redundant flood messages. 15 ISJNW15 A Near-Optimal Algorithm In this project, we propose a novel topology 2010 Attacking the Topology Mismatch matching algorithm based on the Problem in Unstructured Peer-to- Metropolis-Hastings method. Our proposal Peer Networks. is guided by our insight analytical model and is close to the optimal design. 16 ISJNW16 A Dynamic Performance-Based A protocol, Performance Adaptive UDP 2010 Flow Control Method for High- which aims to dynamically and Speed Data Transfer autonomously maximize performance under different systems. A mathematical model and related algorithms are proposed to describe the theoretical basis behind effective buffer and CPU management. 17 ISJNW17 Priority of packet inference with We present an end-to-end approach for PFP 2010 back up path inference and its associated tool, POPI which enables users to discover such network policies through measurements of packet losses of different packet types. 18 ISJNW18 On the Benefits of Cooperative Cooperative Cache can improve the system 2010 Proxy Caching for Peer-to-Peer performance in wireless P2P networks. We Traffic propose a novel asymmetric cooperative cache approach, where the data requests are transmitted to the cache layer on every node. 5 Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 6. Iris Solutions TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORK SECURITY SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJNS01 SAT: A Security Architecture In this project, we propose SAT, a security 2011 Achieving Anonymity and architecture mainly consisting resolves the Traceability in Wireless Mesh conflicting security requirements of Networks unconditional anonymity for honest users and traceability of misbehaving users. 2 ISJNS02 Peering Equilibrium Multipath Our scheme relies on a game theory 2011 Routing: A Game Theory modeling, with a non-cooperative potential Framework for Internet Peering game considering both routing and Settlements congestions costs. We compare different PEMP policies to BGP Multipath schemes by emulating a realistic peering scenario. Our results show that the routing cost can be decreased by roughly 10% with PEMP. The stability of routes can be significantly improved and that congestion can be practically avoided on the peering links. 3 ISJNS03 An Obfuscation-Based Approach We address this problem and present a 2011 for Protecting Location Privacy solution based on different obfuscation operators introduce an adversary model and provide an analysis of the proposed obfuscation operators to evaluate their robustness against adversaries aiming to reverse the obfuscation effects to retrieve a location that better approximates the location of the users 4 ISJNS04 Providing Transaction Guarantees Aims to demonstrate that randomization can 2011 in Asynchronous Systems with be a very competitive approach even in No Assumptions on the Accuracy hostile environments where arbitrary faults of Failure Detection can occur. A stack of randomized intrusion- tolerant protocols is described and its performance evaluated under several settings in both local-area-network and wide-area- network environments. The stack provides a set of relevant services ranging from basic. 5 ISJNS05 Modeling and Detection of Our scheme uses the Power Spectral 2011 6 Camouflaging Worm Density (PSD) distribution of the scan Page traffic volume and its corresponding #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 7. Iris Solutions Spectral Flatness Measure (SFM) to distinguish the C-Worm traffic from background traffic. The performance data clearly demonstrates that our scheme can effectively detect the C-Worm propagation. 6 ISJNS06 Analysis of a Botnet Takeover We present the design of an advanced 2011 hybrid peer-to-peer botnet. Compared with current botnets, the proposed botnet is harder to be shut down, monitored, and hijacked. It provides individualized encryption and control traffic dispersion. 7 ISJNS07 Efficient Network Modification to As real-time traffic such as video or voice 2011 Improve QoS Stability at Failures increases on the Internet, ISPs are required to provide stable quality as well as connectivity at failures. For ISPs, how to effectively improve the stability of these qualities at failures with the minimum investment cost is an important issue, and they need to effectively select a limited number of locations to add link facilities. 8 ISJNS08 Comparative Evaluation of 1) Formalizing the problem of spoofed 2011 Spoofing Defenses traffic filtering and defining novel effectiveness measures, 2) observing each defense as selfish or altruistic and differentiating their performance goals, 3) defining optimal core deployment points for defenses that need core support, and 4) evaluating all defenses in a common and realistic setting. 9 ISJNS09 Traceback of DDoS Attacks We categorize packets that are passing 2011 Using Entropy Variations through a router into flows, which are defined by the upstream router where a packet came from, and the destination address of the packet. In this project, we use flow entropy variation or entropy variation interchangeably. 10 ISJNS10 Weak State Routing for Large- Weak State Routing (WSR) is a novel 2010 Scale Dynamic Networks routing protocol that uses weak state along with random directional walks for forwarding packets. When a packet reaches a node that contains a weak state about the destination with higher confidence than that 7 held by the packet, the walk direction is Page biased. The packet reaches the destination #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 8. Iris Solutions via a sequence of directional walks, punctuated by biasing decisions. 11 ISJNS11 On the Quality of Service of Estimating the parameters of the failure 2010 Crash-Recovery Failure Detectors detector to achieve a required QoS to configuring the crash-recovery failure detector. We investigate the impact of the dependability of the monitored process on the QoS of our failure detector 12 ISJNS12 An Advanced Hybrid Peer-to- Compared with current botnets, the 2010 Peer Botnet proposed botnet is harder to be shut down, monitored, and hijacked. It provides robust network connectivity, individualized encryption and control traffic dispersion, limited botnet exposure by each bot, and easy monitoring and recovery by its botmaster. 13 ISJNS13 Authenticated Group Key Key transfer protocols rely on a mutually 2010 Transfer Protocol Based on Secret trusted key generation center (KGC) to Sharing select session keys and transport session keys to all communication entities secretly. In this paper, we propose an authenticated key transfer protocol based on secret sharing scheme that KC can broadcast group key information to all group members at once and only authorized group members can recover the group key. 14 ISJNS14 Secure Data Replication in Data Secret sharing with cryptography 2010 Grid approaches have been used in distributed storage systems to ensure the confidentiality, integrity, and availability of critical information. specifically, we investigate the problem of optimal allocation of sensitive data objects that are partitioned by using secret sharing scheme or erasure coding scheme and/or replicated. We develop two heuristic algorithms for the two sub problems. 15 ISJNS15 Providing Witness Anonymity We introduce the concept of witness 2010 Under Peer-to-Peer Settings anonymity for peer-to-peer systems, as well as other systems with the peer-to-peer nature. We propose the Secure Deep Throat (SDT) protocol to provide anonymity for the 8 witnesses of malicious or selfish behavior to Page enable such peers to report on this behavior #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 9. Iris Solutions without fear of retaliation. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON DATA MINING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJDM01 Effective Navigation of Query Ranking and categorization, which can also 2011 Results Based on Concept be combined, have been proposed to Hierarchies alleviate this information overload problem. Results categorization for biomedical databases is the focus of this work. A natural way to organize biomedical citations is according to their MeSH annotations. 2 ISJDM02 Automatic Discovery of Personal We propose a novel, automatically extracted 2011 Name Aliases from the Web lexical pattern-based approach to efficiently extract a large set of candidate aliases from snippets retrieved from a web search engine. We define numerous ranking scores to evaluate candidate aliases using three approaches: lexical pattern frequency, word co-occurrences in an anchor text graph, and page counts on the web. 3 ISJDM03 An Efficient Index for Geographic Given a geographic query that is composed 2011 of query keywords and a location, a geographic search engine retrieves documents that are the most textually and spatially relevant to the query keywords and the location, respectively, and ranks the retrieved documents according to their joint textual and spatial relevances to the query. 4 ISJDM04 Anonymous Publication of The problem of anonymizing sparse, high 2011 Sensitive Transactional Data dimensional transactional data is solved through methods based on 1) local NN- search and 2) global data reorganization. 5 ISJDM05 Efficient Periodicity Mining in A time series is a collection of data values 2011 Time Series Databases Using gathered generally at uniform interval of Suffix Trees time to reflect certain behavior of an entity. Real life has several examples of time series such as stock growth, transactions in a superstore. A time series is mostly 9 characterized by being composed of Page repeating cycles. #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 10. Iris Solutions 6 ISJDM06 Mining Iterative Generators and The iterative pattern mining which outputs 2011 Representative Rules for Software patterns that are repeated frequently within a Specification Discovery program trace, or across multiple traces, or both. Frequent iterative patterns reflect frequent program behaviors that likely correspond to software specifications. 7 ISJDM07 Mining Web Graphs for The recommender systems are based on 2011 Recommendations Collaborative Filtering which is a technique that automatically predicts the interest of an active user by collecting rating information from other similar users or items 8 ISJDM08 Managing Multidimensional A P2P-based framework supporting the 2010 Historical Aggregate Data in extraction of aggregates from historical Unstructured P2P Networks multidimensional data is proposed, which provides efficient and robust query evaluation 9 ISJDM09 Multimodal Fusion for Video In this project, we present a flexible and 2010 Search Reranking effective reranking method, called CR- Reranking, to improve the retrieval effectiveness. Specifically, multimodal features are first utilized separately to rerank the initial returned results at the cluster level, and then all the ranked clusters from different modalities are cooperatively used to infer the shots with high relevance. 10 ISJDM10 Prospective Infectious Disease We considered the problem of identifying 2010 Outbreak Detection Using outbreak patterns in a syndrome count time Markov Switching Models series using Markov switching models. The disease outbreak states are modeled as hidden state variables which control the observed time series. 11 ISJDM11 LIGHT: A Query-Efficient yet LIGHT weight Hash Tree (LIGHT)—a 2010 Low-Maintenance Indexing query-efficient yet low-maintenance Scheme over DHTs indexing scheme. LIGHT employs a novel naming mechanism and a tree summarization strategy for graceful distribution of its index structure. We show through analysis that it can support various complex queries with near-optimal performance. 12 ISJDM12 Deriving Concept-Based User User profiling is a fundamental component 2010 Profiles from Search Engine Logs of any personalization applications. We evaluate the proposed methods against our 10 previously proposed personalized query Page clustering method. Experimental results #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 11. Iris Solutions show that profiles which capture and utilize both of the user‘s positive and negative preferences perform the best. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON MOBILE COMPUTING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJMC01 Design and Performance Analysis Here we develop two per-user-based 2011 of Mobility Management mobility management schemes for WMNs, Schemes Based on Pointer namely, the static anchor scheme and Forwarding for Wireless Mesh dynamic anchor scheme. Both schemes are Networks based on pointer forwarding. The optimal threshold of the forwarding chain length is determined for each individual mesh client dynamically based on the mesh client‘s specific mobility and service patterns. 2 ISJMC02 Dynamic Conflict-Free DCQS, a novel transmission scheduling 2011 Transmission Scheduling for technique specifically designed for query Sensor Network Queries services in wireless sensor networks. DCQS features a planner and a scheduler. The planner reduces query latency by constructing transmission plans based on the precedence constraints in in-network aggregation. The scheduler improves throughput by overlapping the transmissions of multiple query instances concurrently while enforcing a conflict-free schedule. 3 ISJMC03 Multipath Routing and Max-Min Ensure QoS, an interference-aware max-min 2011 Fair QoS Provisioning under fair bandwidth allocation algorithm, Interference Constraints in proposed where multiple paths (determined Wireless Multihop Networks by using the routing metric) coexist for each user to the base station succeed in improving network performance in terms of delay, packet loss ratio, and bandwidth usage. 4 ISJMC04 Detection of Selfish Manipulation CCA tuning can be exploited by selfish 2011 of Carrier Sensing in 802.11 nodes to obtain an unfair share of the Networks available bandwidth. Specifically, a selfish entity can manipulate the CCA threshold to ignore ongoing transmissions; this increases 11 the probability of accessing the medium and provides the entity a higher, unfair share of Page the bandwidth. #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 12. Iris Solutions 5 ISJMC05 Message-Efficient Location A better prediction model can significantly 2011 Prediction for Mobile Objects in reduce power consumption in a wireless Wireless Sensor Networks Using a sensor network because fewer redundant Maximum Likelihood Technique sensors will be activated to keep monitoring the object. The Gauss-Markov mobility model is best mobility models to describe object trajectory because it can capture the correlation of object velocity in time. 6 ISJMC06 Throughput-Lifetime Trade-Offs Operating a multi hop wireless network 2011 in Multi hop Wireless Networks while achieving both high throughput and under an SINR-Based high lifetime is a highly desirable design Interference Model goal. 7 ISJMC07 Efficient Load-Aware Routing A cluster head estimates traffic load in its 2010 Scheme For Wireless Mesh cluster. As the estimated load gets higher, networks the cluster head increases the routing metrics of the routes passing through the cluster. Based on the routing metrics, user traffic takes a detour to avoid overloaded areas and, as a result, the WMN achieves global load balancing 8 ISJMC08 Secure Data Collection in We generate randomized multipath routes, 2010 Wireless Sensor Networks Using the routes taken by the ―shares‖ of different Randomized Dispersive Routes packets change over time. The routing algorithm becomes known to the adversary, the adversary still cannot pinpoint the routes traversed by each packet. Besides randomness, the generated routes are also highly dispersive and energy efficient, making them quite capable of circumventing black holes. 9 ISJMC09 VEBEK: Virtual Energy-Based We introduce an energy-efficient VEBEK 2010 Encryption and Keying for scheme for WSNs that significantly reduces Wireless Sensor Networks the number of transmissions needed for rekeying to avoid stale keys. In addition to the goal of saving energy, minimal transmission is imperative for some military applications of WSNs where an adversary could be monitoring the wireless spectrum 10 ISDMC10 MABS: Multicast Authentication MABS, includes two schemes. The basic 2010 Based on Batch Signature scheme (MABS-B) eliminates the correlation among packets and thus 12 provides the perfect resilience to packet loss, and it is also efficient in terms of Page latency, computation, and communication #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 13. Iris Solutions overhead due to an efficient cryptographic primitive called batch signature, which supports the authentication of any number of packets simultaneously. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON IMAGE PROCESSING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJIP01 Efficient Relevance Feedback Content-based image retrieval (CBIR) is the 2011 mainstay of image retrieval systems. Relevance feedback techniques were incorporated into CBIR such that more precise results can be obtained by taking user‘s Feedbacks into account. 2 ISJIP02 High-quality Reflection Deal with a problem of separating the effect 2011 Separation using Polarized Images of reflection from images captured behind glass. The input consists of multiple polarized images captured from the same view point but with different polarizer angles. The output is the high quality separation of the reflection layer and the background layer from the images. 3 ISJIP03 Active Learning for Solving the The result on the face recognition database 2011 Incomplete Data Problem in and palm print palm vein database showed Facial Age Classification by the that our approach can handle problems with Furthest Nearest-Neighbor large number of classes. Our contributions Criterion are twofold. 1. We proposed the FNN being our novel idea, as a generic on-line or active learning paradigm. 2. We showed that it can be another viable tool for active learning of facial age range classification. 4 ISJIP04 Practical Bounds on Image The bound was computed directly from the 2011 Denoising: From Estimation to noise-free image that was assumed to be Information available. We analyze the bounds formulation to show that these two parameters are interdependent and they, along with the bounds formulation as a whole, have a nice information-theoretic interpretation as well. 13 5 ISJIP05 An Affine Symmetric Image The affine symmetry is exploited between 2010 Model and Its Applications structural textures at a local level, the Page objective being to find the minimum #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 14. Iris Solutions residual error by estimating the affine transform relating two patches of texture. Having developed a local model, the methodology is extended to the whole image to estimate the global affine relation. TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON SOFTWARE ENGINEERING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJSE01 An Attack Surface Metric Formalize the notion of a system‘s attack 2011 surface and introduce an attack surface metric to measure the attack surface in a systematic manner. Our measurement method is agnostic to a software system‘s implementation language and is applicable to systems of all sizes. 2 ISJSE02 Genetic Algorithms for A system which uses a genetic algorithm to 2011 Randomized Unit Testing find parameters for randomized unit testing that optimize test coverage. Designing GAs is somewhat of a black art. We therefore use a feature subset selection tool to assess the size and content of the representations within the GA. 3 ISJSE03 Efficient Consistency We use behavioral profiles for the definition 2011 Measurement Based on of a formal notion of consistency which is Behavioral Profiles of Process less sensitive to model projections than Models common criteria of behavioral equivalence and allows for quantifying deviation in a metric way. The derivation of behavioral profiles and the calculation of a degree of consistency have been implemented. 4 ISJSE04 Web development Navigational We presents a general vision of NDT, 2010 Development Techniques which is an approach to deal with requirements in Web systems. It is based on conclusions obtained in several comparative studies and it tries to fill some gaps detected by the research community. 14 Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 15. Iris Solutions TECHNOLOGY: JAVA DOMAIN : IEEE TRANSACTIONS ON GRID & CLOUD COMPUTING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISJGC01 Adaptive grid risk-sensitive filter Based on point-mass approximation, is 2011 for non-linear problems called the adaptive grid risk-sensitive filter. Although risk-sensitive estimators have been known to be robust compared to their risk-neutral counterparts, the implementation of risk-sensitive filters (RSFs) is almost impossible except for very trivial systems like linear Gaussian systems. 2 ISJGC02 Multicloud Deployment of We deploy a computing cluster on the top of 2011 Computing Clusters for Loosely a multicloud infrastructure, for solving Coupled MTC Applications loosely coupled Many-Task Computing applications. In this way, the cluster nodes can be provisioned with resources from different clouds to improve the cost effectiveness of the deployment, or to implement high-availability strategies. 3 ISJCC03 Enabling Public Auditability and To achieve efficient data dynamics, we 2011 Data Dynamics for Storage improve the existing proof of storage Security in Cloud Computing models by manipulating the classic Merkle Hash Tree construction for block tag authentication. To support efficient handling of multiple auditing tasks, the technique of bilinear aggregate signature to extend our main result into a multiuser setting, where TPA can perform multiple auditing tasks simultaneously. 4 ISJGC04 SOAP Processing Performance SOAP communications produce considerable 2011 and Enhancement network traffic, making them unfit for distributed, loosely coupled and heterogeneous computing environments such as the open Internet. Also, they introduce higher latency and processing delays than 15 other technologies, like Java RMI and CORBA. WS research has recently focused Page on SOAP performance enhancement. #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 16. Iris Solutions 5 ISJGC05 An Improved Ant Algorithm for Finding optimal schedules for such an 2011 Grid Scheduling Problem Using environment is an NP-hard problem, and so Biased Initial Ants heuristic approaches must be used. The goal of grid task scheduling is to achieve high system throughput and to allocate various computing resources to applications. Many different methods have been proposed to solve this problem 6 ISJGC06 Weather data sharing system: an Intelligent agents can play an important role 2011 agent-based distributed data in helping achieve the ‗data grid‘ vision. In management this study, the authors present a multi-agent- based framework to implement manage, share and query weather data in a geographical distributed environment, named weather data sharing system 7 ISJGC07 Bi-Criteria Scheduling Of Bi-criteria scheduling approaches for 2010 Scientific Grid Workflows scientific work flows are usually restricted to certain criterion pairs and require the user to define his preferences either as weights assigned each criterion or as fixed constraints defined for one criterion. The first approach has the drawback that combining multiple criteria into a single objective function is not always intuitive to the end-user, while the second requires a priori knowledge about the result of the first criteria scheduling result 8 ISJGC08 A Distributed Protocol to Serve We propose a distributed overlay 2010 Dynamic Groups For Peer-to-Peer framework for dynamic groups where users Streaming may frequently hop from one group to another while the total pool of users remain stable. SMesh first builds a relatively stable mesh consisting of all hosts for control messaging. The mesh supports dynamic host joining and leaving, and will guide the construction of delivery trees J2EE TECHNOLOGY: J2EE 16 DOMAIN : IEEE TRANSACTIONS ON J2EE Page SNO P.CODE TITLES DESCRIPTION YEAR #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 17. Iris Solutions 1 ISJ2EE1 Integrating Visual Saliency and Visual saliency. From visual aspect, it is 2011 Consistency for Re-ranking Image obvious that salient images would be easier Search Results to catch users eyes and it is observed that these visually salient images in the front pages are often relevant to the users query. 2 ISJ2EE2 Information Security: End User Information security is to protect valuable 2011 Behavior and Corporate Culture assets. The majority of information security (Employee Information specialists believe that promoting good end Management System) user behavior and constraining bad end user behavior is an important component of an effective ISMS. Implementing effective information security involves understanding security-related risk, then developing and implementing appropriate controls. 3 ISJ2EE3 Matching Estimates of the Effect We compare the use of OLS regression and 2011 of College Attendance on propensity score matching methods, and Individual Income incorporate the role of ldquo common support .rdquo Using data from the CHFLS Survey, we estimate career outcomes. 4 ISJ2EE4 Attention modeling for video Overall quality of a distorted video is a 2011 quality assessment: balancing weighted average between the global quality global quality and local quality and the local quality. The proposed video quality modeling algorithm can improve the performance of image quality metrics on video quality assessment compared to the normal averaged spatiotemporal pooling. 5 ISJ2EE5 Movie summarization based on Visual saliency is measured by means of a 2011 audiovisual saliency detection spatiotemporal attention model driven by various feature cues (intensity, color, motion). Audio and video curves are integrated in a single attention curve, where events may be enhanced. The presence of salient events is signified on this audiovisual curve by geometrical features such as local extreme, sharp transition points & level sets. 6 ISJ2EE6 Research on B2B E-Business The model to B2B E-Business System of 2010 System of Bookshop Based on Bookshop, which includes the management Web Service subsystem of order, book information, bookshop information, bill information, and customer relations. 17 Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 18. Iris Solutions DOTNET TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON NETWORKING SNO P.CODE TITLES DESCRIPTION YEAR 1 ISDNW01 Towards Realizable, Low-Cost In this project, popular broadcast scheduling 2011 Broadcast Systems for Dynamic approaches are tested from an Environments implementation cost aspect, and the results render them only conditionally realizable. 2 ISDNW02 Research on cloud computing A traditional method of using load balancing 2011 application in the peer-to-peer and multiple buffer servers we found that based video–on-demand systems the performance of Hadoop framework was improved significantly in feasibility and efficiency when dealing with large data. 3 ISDNW03 A Secure Communication Game A four terminal network with a source, a 2011 with a Relay Helping the destination, an eavesdropper and a jammer Eavesdropper relay is investigated. The source and the jammer relay have conflicting interests. This problem is formulated as a non-cooperative two-player zero sum continuous game. Two cases are studied: 1) the jammer relay does not hear the source, and 2) the jammer relay is given the source signal causally. 4 ISDNW04 Optical Layer Security in Fiber- Our goal is the security threats in an optical 2011 Optic Networks network as well as present several existing optical techniques to improve the security. In the first part of this paper, we discuss various types of security threats that could appear in the optical layer of an optical network, including jamming, physical infrastructure attacks, eavesdropping and interception. 5 ISDNW05 Model-Based Identification of A novel model-based approach for dominant 2011 Dominant Congested Links congested link identification that is based on 18 interpreting probe loss as an unobserved (virtual) delay. We develop parameter Page inference algorithms for hidden Markov #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 19. Iris Solutions model (HMM) and Markov model with a hidden dimension (MMHD) to infer this virtual delay. 6 ISDNW06 Live Streaming With Receiver- Packet traces are collected from a single or a 2011 Based Peer-Division limited number of measurement points, to Multiplexing infer various properties of traffic on the control and data planes. Although such studies are useful to compare different systems from the end-user's perspective, it is difficult to intuitively understand the observed properties without fully reverse- engineering the underlying systems. 7 ISDNW07 Adjacent Link Failure Being reported as the most general 2011 Localization With Monitoring monitoring structure for out-of-band failure Trails in All-Optical Mesh localization approach, the monitoring trail Networks (m-trail) framework has been witnessed with great efficiency and promises to serve in the future Internet backbone with all-optical mesh wavelength division multiplex (WDM) networks. 8 ISDNW08 Predictive Resource Management The monitoring system preserves a high 2011 of Multiple Monitoring degree of flexibility, increasing the range of Applications applications and network scenarios where it can be used. We implemented our load- shedding-based resource management scheme in an existing network monitoring system and deployed it in a large research and educational network. 9 ISDNW09 Active Monitoring and Alarm It focuses the error locations (Localization) 2010 Management for Fault which is occurring on the Optical Networks Localization in Transparent All- and when we monitoring the fault Optical Networks localization, we arrange the alarm to make active the users. 10 ISDNW10 Logoot-Undo: Distributed This project presents the Logoot-Undo 2010 Collaborative Editing System on Commutative Replicated Data Type P2P Networks algorithm, which integrates the ―undo anywhere, anytime‖ feature on the replicated data‘s in peer to peer network for reducing the cost of undo feature. 11 ISDNW11 Multiuser Diversity Gain in An large cognitive networks granted 2010 Cognitive Networks concurrent spectrum access with license- 19 holding users and Dynamic allocation of Page resources to the best link in multiuser n/w. #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 20. Iris Solutions 12 ISDNW12 Correlation-Based Traffic This paper proposes attacks that exploit the 2010 Analysis Attacks on Anonymity timing behavior and applications in low- Networks latency Anonymity networks. 13 ISDNW13 Optimal Resource Placement in This Paper proposes an optimal resource 2010 Structured Peer-to-Peer Networks (replica or link) placement strategy, which can optimally trade off the performance gain and paid cost in Peer-to-Peer Networks 14 ISDNW14 SocioNet: A Social-Based This paper proposes SocioNet, based on the 2010 Multimedia Access System for relationship form social network and share Unstructured P2P Networks contents by preference. Sharing takes place in 3 ways such as regular, small world, random. 15 ISDNW15 Load Balancing for Parallel A communication-aware load- balancing 2010 Applications on Group Of technique that is capable of improving the Systems performance of communication-intensive applications by increasing the effective utilization of networks in cluster environments. We introduce a behavior model for parallel applications with large requirements of network, CPU, memory, and disk I/O resources. 16 ISDNW16 Cache Maintenance over Wireless The efficiency of data access in caching 2010 Ad Hoc Networks systems largely depends on the cost for maintaining cache consistency, which can be high in wireless ad hoc networks due to network dynamism. In this paper, we propose a general consistency model called Probabilistic Delta Consistency (PDC), which integrates the flexibility granted by existing consistency models, covering them as special cases. 17 ISDNW17 Any Cast Based Packet We are interested in minimizing the delay 2010 Forwarding Scheme For MDML and maximizing the lifetime of event-driven wireless sensor networks for which events occur infrequently. Sleep–wake scheduling could result in substantial delays because a transmitting node needs to wait for its next- hop relay node to wake up. To reduce delays we use ―any cast‖-based packet forwarding schemes. 18 ISDNW18 Sharing Memory between This system protecting shared memory from 2009 20 Byzantine Processes Using the unauthorized node in Network by fine- Policy-Enforced Tulle Spaces grained access policies and it will Transfer Page the data‘s in a network using byzantine #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 21. Iris Solutions process. TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON NETWORK SECURITY SNO P.CODE TITLES DESCRIPTION YEAR 1 ISDNS01 A Generic Framework for Three- A well designed three-factor authentication 2011 Factor Authentication: Preserving protocol can greatly improve the Security and Privacy in information assurance in distributed Distributed Systems systems. Three-factor authentication is introduced to incorporate the advantages of the authentication based on password, smart-card and biometrics. 2 ISDNS02 Deadlock-Free Adaptive Routing A new deadlock-free adaptive routing 2011 in Meshes with Fault-Tolerance algorithm for meshes was proposed for 3D Ability Based on Channel meshes based on a new virtual network Overlapping partitioning scheme called channel overlapping. The proposed deadlock-free adaptive routing algorithm was extended to a deadlock-free adaptive fault tolerant routing algorithm in 3D meshes with the same deadlock avoidance technique which can outperform other previous methods. 3 ISDNS03 RITAS: Services for Randomized A stack of randomized intrusion-tolerant 2011 Intrusion Tolerance protocols is described and its performance evaluated under several settings in both LAN and wide-area-network environments. The stack provides a set of relevant services ranging from basic communication primitives up to atomic broadcast. 4 ISDNS04 Online Intrusion Alert Alert aggregation is an important subtask of 2011 Aggregation with Generative intrusion detection. The goal is to identify Data Stream Modeling and to cluster different alerts—produced by low-level intrusion detection systems, firewalls, etc.—belonging to a specific attack instance which has been initiated by an attacker at a certain point in time. 5 ISDNS05 Replica Placement for Route Distributed hash tables share storage and 2011 Diversity in Tree-Based Routing routing responsibility among all nodes in a 21 Distributed Hash Tables peer-to-peer network. These networks have bounded path length unlike unstructured Page networks. The impact of Max Disjoint on #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 22. Iris Solutions routing robustness compared to other placements when nodes are compromised at random or in a contiguous run. 6 ISDNS06 Prime: Byzantine Replication This project demonstrates the extent of 2011 under Attack performance degradation possible in some existing protocols that do satisfy liveness and that do perform well absent Byzantine faults. We propose a new performance oriented Correctness criterion that requires a consistent level of performance, even with Byzantine faults. 7 ISDNS07 Nymble: Blocking Misbehaving Anonymizing networks such as Tor allow 2011 Users in Anonymzing Networks users to access Internet services privately by using a series of routers to hide the client's IP address from the server. Nymble, a system in which servers can ―blacklist‖ misbehaving users, there by blocking users without compromising their anonymity. 8 ISDNS08 Dynamics of Malware Spread in We formulate an analytical model to 2011 Decentralized Peer-to-Peer characterize the spread of malware in Networks decentralized, Gnutella type peer-to-peer (P2P) networks and study the dynamics associated with the spread of malware. Using a compartmental model, we derive the system parameters or network conditions under which the P2P network may reach a malware free equilibrium. 9 ISDNS09 Improving Security and We propose a novel Cipher text policy 2011 Efficiency in Attribute-Based attribute-based encryption (CP-ABE) Data Sharing scheme for a data sharing system by exploiting the characteristic of the system architecture. The proposed scheme achievements:1) The key escrow problem could be solved by escrow-free key issuing protocol.2) Fine-grained user revocation per each attribute could be done by proxy encryption which takes advantage of the selective attribute group key distribution on top of the ABE. 10 ISDNS10 Using Web-Referral We systematically design a security-driven 2010 Architectures to Mitigate Denial- scheduling architecture that can dynamically 22 of-Service Threats measure the trust level of each node in the system by using differential equations Page #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 23. Iris Solutions 11 ISDNS11 Against Flooding Attacks Using In recent years, a number of puzzle-based 2010 Game Theory based Puzzle defense mechanisms have been proposed Approach against flooding denial-of-service (DoS) attacks in networks. This paper utilizes game theory to propose a series of optimal puzzle-based strategies for handling increasingly sophisticated flooding attack scenarios TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON DATAMINING SNO P. CODE PROJECT TITLES DESCRIPTION YEAR 1 ISDDM01 Mining Group Movement Encryption and multiplexing technique not 2011 Patterns for Tracking Moving only enhances the security of confidential Objects Efficiently fingerprint information by making the information inaccessible to any intruder having a random code, but also improves the system resource utilization by reducing the storage and/or transmission bandwidth requirement 2 ISDDM02 Mining Iterative Generators and We introduce a novel concept of 2011 Representative Rules for representative rules expressing forward, Software Specification Discovery backward, and in-between temporal constraints. These rules characterize many real-world constraints including those found in software specifications and can be constructed by pairing iterative generators with closed iterative patterns. 3 ISDDM03 On Computing Farthest The concept of Data mining such as NN and 2011 Dominated Locations closest Pair is used. Based on the client‘s query, the database will be giving the nearest datasets and by the using Closest- Pair concept, we can point the object (data) location and neglect spatial location. 4 ISDDM04 Efficient Relevance Feedback for We propose a novel method NPRF to 2011 Content-Based Image Retrieval achieve the high efficiency and effectiveness by Mining User Navigation of CBIR in coping with the large-scale Patterns image data. In terms of efficiency, the 23 iterations of feedback are reduced substantially by using the navigation Page patterns discovered from the user query log. #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 24. Iris Solutions Our proposed search use three kinds of query refinement strategies QPM, QR and QEX to converge the search space toward the user‘s intention effectively. 5 ISDDM05 Authenticated Multistep NN We are using NN concept to provide 2011 Nearest Neighbor Search similarity search results with trustiness to proof the result correctness. A client gives NN queries to a server that maintains a database signed by a trusted authority. 6 ISDDM06 Missing Value Estimation for Missing data imputation aims at providing 2011 Mixed-Attribute Data Sets estimations for missing values by reasoning from observed data. Missing data imputation is a key issue in learning from incomplete data. Various techniques have been developed with great successes on dealing with missing values in data sets with homogeneous attributes. 7 ISDDM07 Extended XML Tree Pattern We research a large set of XML tree pattern, 2011 Matching: Theories and called extended XML tree pattern, which Algorithms may include P-C, A-D relationships, negation functions, wildcards, and order restriction. We establish a theoretical framework about ―matching cross‖ which demonstrates the intrinsic reason in the proof of optimality on holistic algorithms. 8 ISDDM08 Bridging Domains Using World A novel transfer learning approach, called 2010 Wide Knowledge for Transfer BIG (Bridging information Gap), to Learning effectively extract useful knowledge in a worldwide knowledge base. 9 ISDDM09 Closing the Loop in Webpage This project focuses on the concept of 2010 Understanding information extraction is processing from a web page and its content. 10 ISDDM10 Knowledge-Based Interactive This paper proposes a new interactive 2010 Post mining of Association Rules approach to prune and filter discovered Using Ontologies rules.1) Integration of user knowledge in the post processing task. 2) The Rule Schema formalism extending the specification language for user expectations 11 ISDDM11 Filtering Data flow for Query tolerance is expressed as a numerical 2010 Continuous Queries value, which may be difficult to specify. We 24 observe that in many situations, users may not be concerned with the actual value of an Page answer, but rather which object satisfies a #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
- 25. Iris Solutions query. In this paper We develop fraction- based tolerance for two major classes of entity-based queries 12 ISDDM12 Through Linking for Transfer Our approach at automatically adapting the 2010 Learning Using Web information extraction knowledge previously learned from a source Web site to a new unseen site and discovering previously unseen attributes. Two kinds of text-related clues from the source Web site are considered. The first clue is obtained from the extraction pattern contained in the previously learned wrapper. The second clue is derived from the previously extracted or collected items. 13 ISDDM13 A Binary String Approach for To facilitate XML query processing, several 2010 Updates XML Data labeling schemes have been proposed, in which the ancestor-descendant and parent- child relationships in XML queries can be quickly determined without accessing the original XML file. A novel labeling scheme, called IBSL (Improved Binary String Labeling), which supports order sensitive updates without relabeling or recalculation. TECHNOLOGY: DOTNET DOMAIN : IEEE TRANSACTIONS ON MOBILE COMPUTING SNO P. CODE PROJECT TITLES DESCRIPTION YEAR 1 ISDMC01 A Policy Enforcing Mechanism The design and implementation of a policy 2011 for Trusted Ad Hoc Networks enforcing mechanism based on Satem, a kernel-level trusted execution monitor built on top of the Trusted Platform Module. Under this mechanism, each application or protocol has an associated policy. Two instances of an application running on different nodes may engage in communication only if these nodes enforce the same set of policies for both the application and the underlying protocols used by the application. 25 2 ISDMC02 Call Admission Control In efficient CAC scheme for mobile networks 2011 Page Performance Analysis in Mobile that takes into account voice connections, #165, 1st Floor, 5th Street, Gandhipuram, Coimbatore-12 Ph: 0422-4372816 Mail: irisprojects@yahoo.com website: www.irisprojects.com, Our branches: Tanjore: 9943 317 317, Trichy: 9943 314 314, Kovai: 9943 357 357 Chennai, Madurai, Nellai, Erode, Salem
