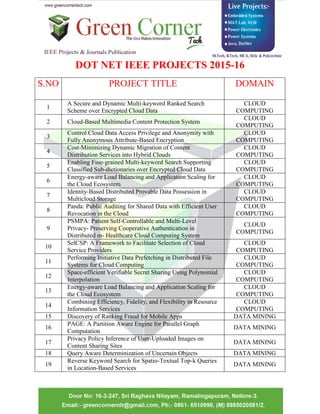
cse projects,Dot net ieee projects 2015,green corner tech,nellore
- 1. DOT NET IEEE PROJECTS 2015-16 S.NO PROJECT TITLE DOMAIN 1 A Secure and Dynamic Multi-keyword Ranked Search Scheme over Encrypted Cloud Data CLOUD COMPUTING 2 Cloud-Based Multimedia Content Protection System CLOUD COMPUTING 3 Control Cloud Data Access Privilege and Anonymity with Fully Anonymous Attribute-Based Encryption CLOUD COMPUTING 4 Cost-Minimizing Dynamic Migration of Content Distribution Services into Hybrid Clouds CLOUD COMPUTING 5 Enabling Fine-grained Multi-keyword Search Supporting Classified Sub-dictionaries over Encrypted Cloud Data CLOUD COMPUTING 6 Energy-aware Load Balancing and Application Scaling for the Cloud Ecosystem CLOUD COMPUTING 7 Identity-Based Distributed Provable Data Possession in Multicloud Storage CLOUD COMPUTING 8 Panda: Public Auditing for Shared Data with Efficient User Revocation in the Cloud CLOUD COMPUTING 9 PSMPA: Patient Self-Controllable and Multi-Level Privacy- Preserving Cooperative Authentication in Distributed m- Healthcare Cloud Computing System CLOUD COMPUTING 10 SelCSP: A Framework to Facilitate Selection of Cloud Service Providers CLOUD COMPUTING 11 Performing Initiative Data Prefetching in Distributed File Systems for Cloud Computing CLOUD COMPUTING 12 Space-efficient Verifiable Secret Sharing Using Polynomial Interpolation CLOUD COMPUTING 13 Energy-aware Load Balancing and Application Scaling for the Cloud Ecosystem CLOUD COMPUTING 14 Combining Efficiency, Fidelity, and Flexibility in Resource Information Services CLOUD COMPUTING 15 Discovery of Ranking Fraud for Mobile Apps DATA MINING 16 PAGE: A Partition Aware Engine for Parallel Graph Computation DATA MINING 17 Privacy Policy Inference of User-Uploaded Images on Content Sharing Sites DATA MINING 18 Query Aware Determinization of Uncertain Objects DATA MINING 19 Reverse Keyword Search for Spatio-Textual Top-k Queries in Location-Based Services DATA MINING
- 2. 20 Tweet Segmentation and Its Application to Named Entity Recognition DATA MINING 21 EMR: A Scalable Graph-based Ranking Model for Content- based Image Retrieval DATA MINING 22 Automatic Group Happiness Intensity Analysis DATA MINING 23 RRW - A Robust and Reversible Watermarking Technique for Relational Data DATA MINING 24 Collision Tolerant and Collision Free Packet Scheduling for Underwater Acoustic Localization NETWORKING 25 Defeating Jamming With the Power of Silence: A Game- Theoretic Analysis NETWORKING 26 Universal Network Coding-Based Opportunistic Routing for Unicast NETWORKING 27 Congestion Aware Load Balancing for Multiradio Wireless Mesh Network NETWORKING 28 A Distributed Three-hop Routing Protocol to Increase the Capacity of Hybrid Wireless Networks MOBILE COMPUTING 29 Mobile Data Gathering with Load Balanced Clustering and Dual Data Uploading in Wireless Sensor Networks MOBILE COMPUTING 30 Optimal Configuration of Network Coding in Ad Hoc Networks MOBILE COMPUTING 31 Privacy-Preserving and Truthful Detection of Packet Dropping Attacks in Wireless Ad Hoc Networks MOBILE COMPUTING 32 Optimum Power Allocation in Sensor Networks for Active Radar Applications MOBILE COMPUTING 33 Authenticated Key Exchange Protocols for Parallel Network File Systems PARALLEL & DISTRIBUTED SYSTEMS 34 Dominating Set and Network Coding-based Routing in Wireless Mesh Networks PARALLEL & DISTRIBUTED SYSTEMS 35 A Time Efficient Approach for Detecting Errors in Big Sensor Data on Cloud PARALLEL & DISTRIBUTED SYSTEMS 36 Data Collection in Multi-Application Sharing Wireless Sensor Networks PARALLEL & DISTRIBUTED SYSTEMS 37 Enabling Fine-grained Multi-keyword Search Supporting Classified Sub-dictionaries over Encrypted Cloud Data PARALLEL & DISTRIBUTED SYSTEMS 38 A Secure and Dynamic Multi-keyword Ranked Search Scheme over Encrypted Cloud Data PARALLEL & DISTRIBUTED SYSTEMS
- 3. 39 Cost-Minimizing Dynamic Migration of Content Distribution Services into Hybrid Clouds PARALLEL & DISTRIBUTED SYSTEMS 40 Behavior Rule Specification-Based Intrusion Detection for Safety Critical Medical Cyber Physical Systems SECURE COMPUTING 41 Generating Searchable Public-Key Ciphertexts with Hidden Structures for Fast Keyword Search SECURE COMPUTING 42 Improved Privacy-Preserving P2P Multimedia Distribution Based on Recombined Fingerprints SECURE COMPUTING 43 Key-Recovery Attacks on KIDS, a Keyed Anomaly Detection System SECURE COMPUTING 44 Hacking is not random: a case-control study of webser ver- compromise risk SECURE COMPUTING 45 VoteTrust: Leveraging Friend Invitation Graph to Defend against Social Network Sybils SECURE COMPUTING 46 Public Integrity Auditing for Dynamic Data Sharing with Multi-User Modification SECURE COMPUTING 47 My Privacy My Decision: Control of Photo Sharing on Online Social Networks SECURE COMPUTING 48 Knowledge Sharing in the Online Social Network of Yahoo! Answers and Its Implications SECURE COMPUTING 49 Generating Searchable Public-Key Ciphertexts with Hidden Structures for Fast Keyword Search SECURE COMPUTING 50 Automatic Face Naming by Learning Discriminative Affinity Matrices from Weakly Labeled Images SECURE COMPUTING 51 Revealing the Trace of High-Quality JPEG Compression Through Quantization Noise Analysis SECURE COMPUTING 52 An Attribute-Assisted Reranking Model for Web Image Search IMAGE PROCESSING 53 Steganography Using Reversible Texture Synthesis IMAGE PROCESSING 54 Detection and Rectification of Distorted Fingerprints IMAGE PROCESSING 55 Eye Gaze Tracking With a Web Camera in a Desktop Environment IMAGE PROCESSING 56 Learning Fingerprint Reconstruction: From Minutiae to Image IMAGE PROCESSING 57 Multi view Alignment Hashing for Efficient Image Searc IMAGE PROCESSING 58 Single Image Super resolution Based on Gradient Profile Sharpness IMAGE PROCESSING 59 Steganography Using Reversible Texture Synthesis IMAGE PROCESSING
- 4. 60 A Regularization Approach to Blind Deblurring and Denoising of QR Barcodes IMAGE PROCESSING 61 Vector Sparse Representation of Color Image Using Quaternion Matrix Analysis IMAGE PROCESSING 62 Saliency-based color accessibility IMAGE PROCESSING 63 Contextual Online Learning for Multimedia Content Aggregation IMAGE PROCESSING 64 A Probabilistic Approach for Color Correction in Image Mosaicking Applications IMAGE PROCESSING 65 A Methodology for Visually Lossless JPEG2000 Compression of Monochrome Stereo Images IMAGE PROCESSING 66 Single Image Super-Resolution Based on Gradient Profile Sharpness IMAGE PROCESSING 67 RRW - A Robust and Reversible Watermarking IMAGE PROCESSING 68 A Highly Accurate Prediction Algorithm for Unknown Web Service QoS Values IMAGE PROCESSING 69 Location-Aware and Personalized Collaborative Filtering for Web Service Recommendation SERVICE COMPUTING (WEB SERVICE) 70 Trustworthy Parking Communities: Helping Your Neighbor to Find a Space SERVICE COMPUTING 71 On the Security of Data Access Control for Multiauthority Cloud Storage Systems SERVICE COMPUTING 72 Guest Editorial: Recommendation Techniques for Services Computing and Cloud Computing SERVICE COMPUTING 73 Diversifying Web Service Recommendation Results via Exploring Service Usage History SERVICE COMPUTING
