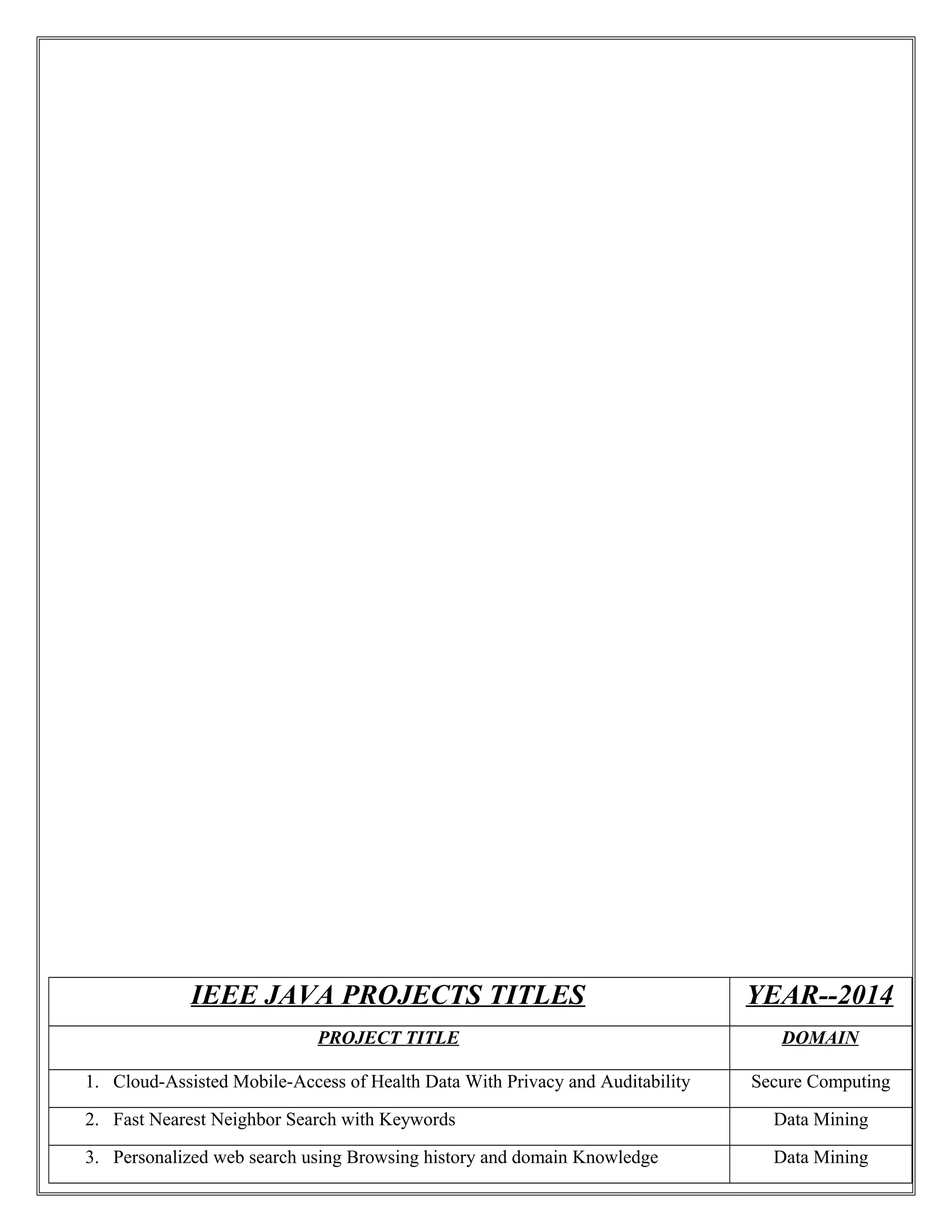
The document lists project titles from IEEE in 2014 across various domains, primarily focusing on secure computing, data mining, mobile computing, and parallel and distributed systems. Each project title addresses specific challenges and innovations in areas like cloud computing, security, and data privacy. The diverse range of topics reflects ongoing research and development efforts in enhancing technology and safeguarding data.