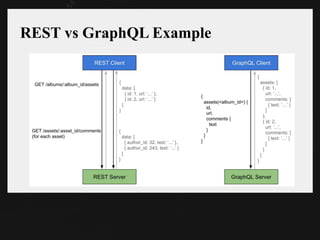
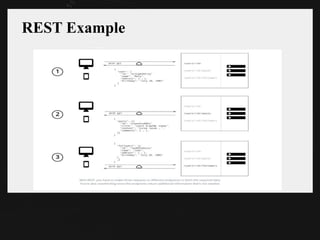
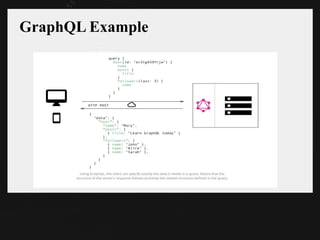
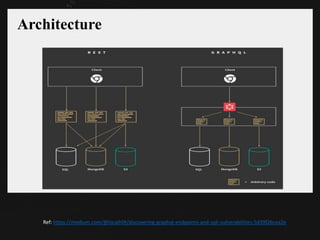
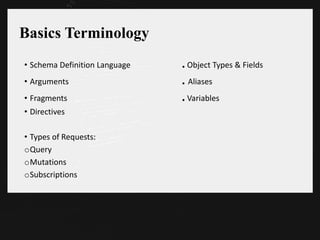
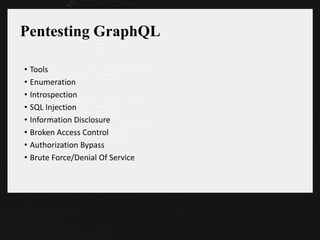
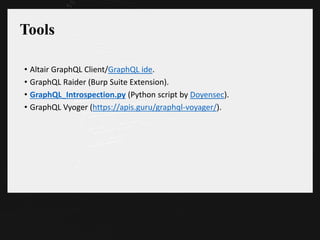
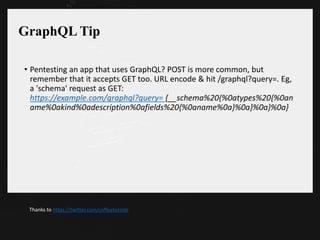
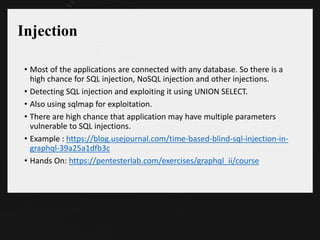
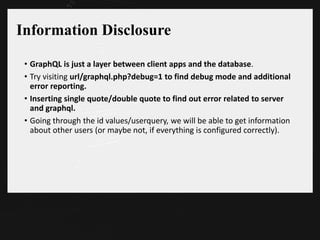
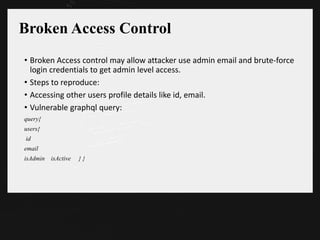
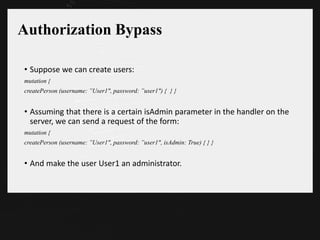
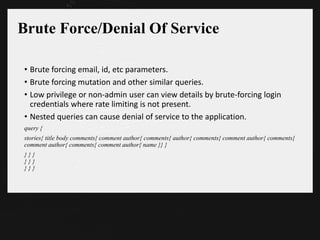
The document discusses the pentesting of applications using GraphQL, outlining its advantages over REST, such as reduced data fetching issues and rapid frontend development. It covers key concepts, such as schema, queries, and typical vulnerabilities, including SQL injection, information disclosure, and authorization bypass. Additionally, it provides useful tools and techniques for testing GraphQL applications and highlights various references for further learning.