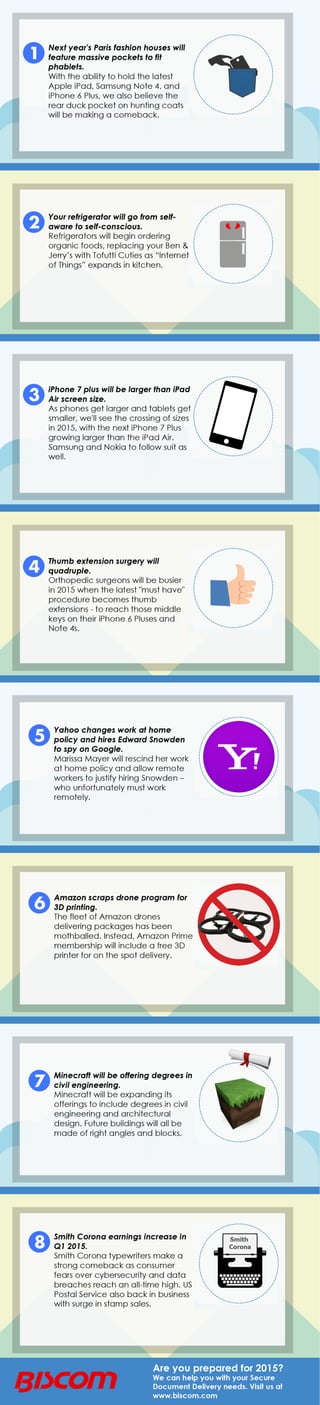
2015 technology-predictions-infographic-biscom
•
0 likes•179 views
Some fun technology predictions for 2015 from Biscom.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (14)
Recently uploaded
Recently uploaded (20)
Hyatt driving innovation and exceptional customer experiences with FIDO passw...

Hyatt driving innovation and exceptional customer experiences with FIDO passw...
Navigating the Large Language Model choices_Ravi Daparthi

Navigating the Large Language Model choices_Ravi Daparthi
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Introduction to FIDO Authentication and Passkeys.pptx

Introduction to FIDO Authentication and Passkeys.pptx
Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)

Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)
WebRTC and SIP not just audio and video @ OpenSIPS 2024

WebRTC and SIP not just audio and video @ OpenSIPS 2024
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
State of the Smart Building Startup Landscape 2024!

State of the Smart Building Startup Landscape 2024!
The Ultimate Prompt Engineering Guide for Generative AI: Get the Most Out of ...

The Ultimate Prompt Engineering Guide for Generative AI: Get the Most Out of ...
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
