Mooney Patent Summary
•Download as DOC, PDF•
0 likes•110 views
Report
Share
Report
Share
Recommended
Recommended
More Related Content
Similar to Mooney Patent Summary
Similar to Mooney Patent Summary (20)
Secure Code Generation for Multi-level Mutual Authentication

Secure Code Generation for Multi-level Mutual Authentication
An efficient implementation for key management technique using smart card and...

An efficient implementation for key management technique using smart card and...
E-Passport: Deploying Hardware Security Modules to Ensure Data Authenticity a...

E-Passport: Deploying Hardware Security Modules to Ensure Data Authenticity a...
Design of a gsm based biometric access control system

Design of a gsm based biometric access control system
Internet of Things (IoT) Security Measures Insights from Patents

Internet of Things (IoT) Security Measures Insights from Patents
06 Computer Image Verification and Authentication - Notes

06 Computer Image Verification and Authentication - Notes
A Review Study on Secure Authentication in Mobile System

A Review Study on Secure Authentication in Mobile System
Information security proposal for electronic door lock

Information security proposal for electronic door lock
AN ENHANCED SECURITY FOR GOVERNMENT BASE ON MULTIFACTOR BIOMETRIC AUTHENTICATION

AN ENHANCED SECURITY FOR GOVERNMENT BASE ON MULTIFACTOR BIOMETRIC AUTHENTICATION
AN ENHANCED SECURITY FOR GOVERNMENT BASE ON MULTIFACTOR BIOMETRIC AUTHENTICATION

AN ENHANCED SECURITY FOR GOVERNMENT BASE ON MULTIFACTOR BIOMETRIC AUTHENTICATION
An Internet Based Interactive Data Acquisition System 

An Internet Based Interactive Data Acquisition System
Smartphone Mobile Payment Process Insights from Patents

Smartphone Mobile Payment Process Insights from Patents
Recently uploaded
Recently uploaded (20)
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Emergent Methods: Multi-lingual narrative tracking in the news - real-time ex...

Emergent Methods: Multi-lingual narrative tracking in the news - real-time ex...
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...

Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...
Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...

Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
CNIC Information System with Pakdata Cf In Pakistan

CNIC Information System with Pakdata Cf In Pakistan
Mooney Patent Summary
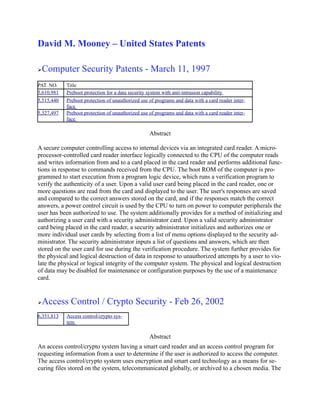
- 1. David M. Mooney – United States Patents Computer Security Patents - March 11, 1997 PAT. NO. Title 5,610,981 Preboot protection for a data security system with anti-intrusion capability 5,515,440 Preboot protection of unauthorized use of programs and data with a card reader inter- face 5,327,497 Preboot protection of unauthorized use of programs and data with a card reader inter- face Abstract A secure computer controlling access to internal devices via an integrated card reader. A micro- processor-controlled card reader interface logically connected to the CPU of the computer reads and writes information from and to a card placed in the card reader and performs additional func- tions in response to commands received from the CPU. The boot ROM of the computer is pro- grammed to start execution from a program logic device, which runs a verification program to verify the authenticity of a user. Upon a valid user card being placed in the card reader, one or more questions are read from the card and displayed to the user. The user's responses are saved and compared to the correct answers stored on the card, and if the responses match the correct answers, a power control circuit is used by the CPU to turn on power to computer peripherals the user has been authorized to use. The system additionally provides for a method of initializing and authorizing a user card with a security administrator card. Upon a valid security administrator card being placed in the card reader, a security administrator initializes and authorizes one or more individual user cards by selecting from a list of menu options displayed to the security ad- ministrator. The security administrator inputs a list of questions and answers, which are then stored on the user card for use during the verification procedure. The system further provides for the physical and logical destruction of data in response to unauthorized attempts by a user to vio- late the physical or logical integrity of the computer system. The physical and logical destruction of data may be disabled for maintenance or configuration purposes by the use of a maintenance card. Access Control / Crypto Security - Feb 26, 2002 6,351,813 Access control/crypto sys- tem Abstract An access control/crypto system having a smart card reader and an access control program for requesting information from a user to determine if the user is authorized to access the computer. The access control/crypto system uses encryption and smart card technology as a means for se- curing files stored on the system, telecommunicated globally, or archived to a chosen media. The
- 2. system includes an access hierarchy, combined with the issuance of smart cards, to control the various levels of access provided by the system. Further, the present system provides secure file transfer by encrypting sensitive files at a first site, transferring the encrypted version to a second site, providing an authorized user at the second site with a secret password, and decrypting the file at the second site using the secret password under control of the authorized user. Cellular Phone Call Management System – Security - June 2, 1998 5,761,624 Method and apparatus for controlling and recording cellular phone transactions using an integrated circuit card Abstract A cellular phone call management system using a microprocessor-controlled remote card reader interface for a cellular telephone system to record calls onto a card as they are placed or received. A microprocessor reads information from a card placed in the remote card reader and ensures the card is valid. The cellular telephone's transceiver logic bus is monitored to determine the transac- tion information of a call as it is placed or received. After the call is completed, the call transac- tion information is recorded on the card. When all calls are complete, the card is placed in a host card reader attached to a host computer where the call transaction information is read from the card, processed, and written to a host storage device. The call transactions may then be analyzed and reports may be generated and printed by host computer software.