Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Project presentation - Steganographic Application of improved Genetic Shifti...

Project presentation - Steganographic Application of improved Genetic Shifti...
Viewers also liked
Viewers also liked (14)
Similar to Steganography ppt
Similar to Steganography ppt (20)
Feature Selection Algorithm for Supervised and Semisupervised Clustering

Feature Selection Algorithm for Supervised and Semisupervised Clustering
Steganography using Interpolation and LSB with Cryptography on Video Images -...

Steganography using Interpolation and LSB with Cryptography on Video Images -...
Steganography using Interpolation and LSB with Cryptography on Video Images-A...

Steganography using Interpolation and LSB with Cryptography on Video Images-A...
Steganography Technique of Sending Random Passwords on Receiver’s Mobile (A N...

Steganography Technique of Sending Random Passwords on Receiver’s Mobile (A N...
Recently uploaded
Mehran University Newsletter is a Quarterly Publication from Public Relations OfficeMehran University Newsletter Vol-X, Issue-I, 2024

Mehran University Newsletter Vol-X, Issue-I, 2024Mehran University of Engineering & Technology, Jamshoro
Recently uploaded (20)
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
ICT role in 21st century education and it's challenges.

ICT role in 21st century education and it's challenges.
On National Teacher Day, meet the 2024-25 Kenan Fellows

On National Teacher Day, meet the 2024-25 Kenan Fellows
This PowerPoint helps students to consider the concept of infinity.

This PowerPoint helps students to consider the concept of infinity.
Food safety_Challenges food safety laboratories_.pdf

Food safety_Challenges food safety laboratories_.pdf
Seal of Good Local Governance (SGLG) 2024Final.pptx

Seal of Good Local Governance (SGLG) 2024Final.pptx
Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi

Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi
Asian American Pacific Islander Month DDSD 2024.pptx

Asian American Pacific Islander Month DDSD 2024.pptx
Steganography ppt
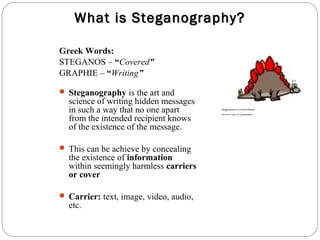
- 1. What is Steganography? Greek Words: STEGANOS – “Covered” GRAPHIE – “Writing” Steganography is the art and science of writing hidden messages in such a way that no one apart Stegosaurus: a covered lizard from the intended recipient knows (but not a type of cryptography) of the existence of the message. This can be achieve by concealing the existence of information within seemingly harmless carriers or cover Carrier: text, image, video, audio, etc.
- 2. Cryptography Cryptography was concerned solely with message confidentiality (i.e., encryption)—conversion of message from a comprehensible form into an incomprehensible one and back again at the other end, rendering it unreadable by interceptors or eavesdroppers without secret knowledge (namely the key needed for decryption of that message) Cryptography is secret writing. Anybody can see the message, but nobody else can read it. Usually, this is because its letters have been re-arranged, or replaced by different letters, according to some scheme that only the sender and receiver know. Only those who possess a secret key can decrypt the message into plain text
- 3. DIFFERENCE B/W CRYPTOGRAPHY AND STEGANOGRAPHY Steganography deals with composing hidden messages so that only the sender and the receiver know that the message even exists. Since, nobody except the sender and the receiver knows the existence of the message, it does not attract unwanted attention. Steganography is hidden writing. The message is there, but nobody notices it. Once the presence of hidden information is revealed or even suspected, the purpose of steganography is defeated. However, once noticed, it can be read. A common form of steganography is the use of JPEG files (a computer image) to hide the message. The obvious advantage of Steganography over cryptography is that messages do not attract any attention
- 4. History of Steganography Steganography ancient origins can be traced back to 440 BC, from the Histories of Herodotus Demeratus sent a warning about a forthcoming attack to Greece by writing it on a wooden panel and covering it in wax. Histiaeus, who shaved the head of his most trusted slave and tattooed a message on it. After his hair had grown the message was hidden. The purpose was to instigate a revolt against the Persians. Hidden messages on messenger's body — also used in ancient Greece. Herodotus tells the story of a message tattooed on the shaved head of a slave of Histiaeus, hidden by the hair that afterwards grew over it, and exposed by shaving the head again. The message allegedly carried a warning to Greece about Persian invasion plans World War II the French Resistance sent some messages written on the backs of couriers using invisible ink.
- 5. Modern Steganography Technique Least Significant Bit Insertion: The most common and popular method of modern day Steganography is to make use of the LSB of a picture’s pixel information. Thus the overall image distortion is kept to a minimum while the message is spaced out over the pixels in the images. This technique works best when the image file is larger then the message file and if the image is grayscale.
- 6. Image of a tree with a steganographically hidden image. The hidden image is revealed by removing all but the two least significant bits of each color component and a subsequent normalization. The hidden image is shown below. Image of a cat extracted from the tree image above.
- 7. Basics of Modern Steganography fE: steganographic function "embedding" fE-1: steganographic function "extracting" cover: cover data in which emb will be hidden emb: message to be hidden key: parameter of fE stego: cover data with the hidden message
- 8. Important Requirement for Steganographic System Security of the hidden communication size of the payload Robustness against malicious and unintentional attacks
- 9. Detection of Steganographic Content/Countermeasures The detection of steganographically encoded packages is called Steganalysis. Visual Analysis tries to reveal the presence of secret communication through inspection, either with the naked eye or with the assistance of a computer. Statistical (Algorithmic) Analysis reveals tiny alterations in an image's statistical behavior caused by steganographic embedding. The nominally universal methods developed to detect embedded stego- data are generally less effective than the steganalytic methods aimed at specific types of embedding.