Mca3050 advanced computer networks
•Download as DOCX, PDF•
0 likes•23 views
Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
Report
Share
Report
Share
Recommended
Combining cryptographic primitives to prevent jamming attacks in wireless networksCombining cryptographic primitives to prevent jamming attacks in wireless net...

Combining cryptographic primitives to prevent jamming attacks in wireless net...JPINFOTECH JAYAPRAKASH
Recommended
Combining cryptographic primitives to prevent jamming attacks in wireless networksCombining cryptographic primitives to prevent jamming attacks in wireless net...

Combining cryptographic primitives to prevent jamming attacks in wireless net...JPINFOTECH JAYAPRAKASH
More Related Content
What's hot
What's hot (18)
A precise termination condition of the probabilistic packet marking algorithm...

A precise termination condition of the probabilistic packet marking algorithm...
A Neighbor Coverage-Based Probabilistic Rebroadcast for Reducing Routing Ove...

A Neighbor Coverage-Based Probabilistic Rebroadcast for Reducing Routing Ove...
Design of Transport Layer Based Hybrid Covert Channel Detection Engine

Design of Transport Layer Based Hybrid Covert Channel Detection Engine
Performance analysis of transport layer basedhybrid covert channel detection ...

Performance analysis of transport layer basedhybrid covert channel detection ...
CLUSTER BASED FIDELITY TO SECURE DSDV PROTOCOL AGAINST BLACK HOLE ATTACKS

CLUSTER BASED FIDELITY TO SECURE DSDV PROTOCOL AGAINST BLACK HOLE ATTACKS
Packet hiding methods for preventing selective jamming attacks

Packet hiding methods for preventing selective jamming attacks
Packet hiding methods for preventing selective jamming attacks

Packet hiding methods for preventing selective jamming attacks
A survey on mitigation methods to black hole attack on aodv routing protocol

A survey on mitigation methods to black hole attack on aodv routing protocol
Hop- by- Hop Message Authentication and Wormhole Detection Mechanism in Wirel...

Hop- by- Hop Message Authentication and Wormhole Detection Mechanism in Wirel...
Similar to Mca3050 advanced computer networks
Similar to Mca3050 advanced computer networks (20)
Question 1The OSI model has seven layers where each layer pe.docx

Question 1The OSI model has seven layers where each layer pe.docx
Client server computing in mobile environments part 2

Client server computing in mobile environments part 2
A study of cryptography for satellite applications

A study of cryptography for satellite applications
THE UNIFIED OPERATION STRUCTURE FOR SYMMETRIC-KEY ALGORITHM

THE UNIFIED OPERATION STRUCTURE FOR SYMMETRIC-KEY ALGORITHM
Recently uploaded
Making communications land - Are they received and understood as intended? webinar
Thursday 2 May 2024
A joint webinar created by the APM Enabling Change and APM People Interest Networks, this is the third of our three part series on Making Communications Land.
presented by
Ian Cribbes, Director, IMC&T Ltd
@cribbesheet
The link to the write up page and resources of this webinar:
https://www.apm.org.uk/news/making-communications-land-are-they-received-and-understood-as-intended-webinar/
Content description:
How do we ensure that what we have communicated was received and understood as we intended and how do we course correct if it has not.Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...Association for Project Management
https://app.box.com/s/7hlvjxjalkrik7fb082xx3jk7xd7liz3TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...

TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...Nguyen Thanh Tu Collection
Mehran University Newsletter is a Quarterly Publication from Public Relations OfficeMehran University Newsletter Vol-X, Issue-I, 2024

Mehran University Newsletter Vol-X, Issue-I, 2024Mehran University of Engineering & Technology, Jamshoro
Recently uploaded (20)
Python Notes for mca i year students osmania university.docx

Python Notes for mca i year students osmania university.docx
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
ICT role in 21st century education and it's challenges.

ICT role in 21st century education and it's challenges.
Food safety_Challenges food safety laboratories_.pdf

Food safety_Challenges food safety laboratories_.pdf
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...
HMCS Max Bernays Pre-Deployment Brief (May 2024).pptx

HMCS Max Bernays Pre-Deployment Brief (May 2024).pptx
Micro-Scholarship, What it is, How can it help me.pdf

Micro-Scholarship, What it is, How can it help me.pdf
TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...

TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...
Jual Obat Aborsi Hongkong ( Asli No.1 ) 085657271886 Obat Penggugur Kandungan...

Jual Obat Aborsi Hongkong ( Asli No.1 ) 085657271886 Obat Penggugur Kandungan...
General Principles of Intellectual Property: Concepts of Intellectual Proper...

General Principles of Intellectual Property: Concepts of Intellectual Proper...
Mca3050 advanced computer networks
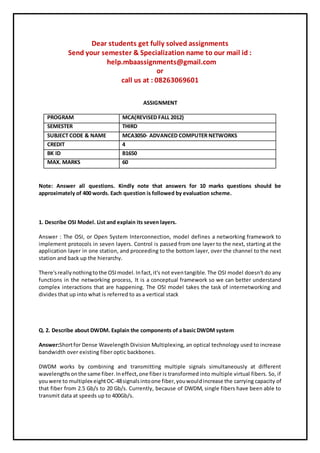
- 1. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601 ASSIGNMENT PROGRAM MCA(REVISED FALL 2012) SEMESTER THIRD SUBJECT CODE & NAME MCA3050- ADVANCED COMPUTER NETWORKS CREDIT 4 BK ID B1650 MAX. MARKS 60 Note: Answer all questions. Kindly note that answers for 10 marks questions should be approximately of 400 words. Each question is followed by evaluation scheme. 1. Describe OSI Model. List and explain its seven layers. Answer : The OSI, or Open System Interconnection, model defines a networking framework to implement protocols in seven layers. Control is passed from one layer to the next, starting at the application layer in one station, and proceeding to the bottom layer, over the channel to the next station and back up the hierarchy. There'sreallynothingtothe OSImodel.Infact,it's not eventangible. The OSI model doesn't do any functions in the networking process, It is a conceptual framework so we can better understand complex interactions that are happening. The OSI model takes the task of internetworking and divides that up into what is referred to as a vertical stack Q. 2. Describe about DWDM. Explain the components of a basic DWDM system Answer:Shortfor Dense Wavelength Division Multiplexing, an optical technology used to increase bandwidth over existing fiber optic backbones. DWDM works by combining and transmitting multiple signals simultaneously at different wavelengthsonthe same fiber.Ineffect,one fiber is transformed into multiple virtual fibers. So, if youwere to multiplex eightOC-48signalsintoone fiber,youwouldincrease the carrying capacity of that fiber from 2.5 Gb/s to 20 Gb/s. Currently, because of DWDM, single fibers have been able to transmit data at speeds up to 400Gb/s.
- 2. Q. 3. Describe about Peak cell rate (PCR) and Sustained cell rate (SCR). Answer: If a service (or application) wishes to use a broadband network (an ATM network in particular) to transport a particular kind of traffic, it must first inform the network about what kind of traffic is to be transported, and the performance requirements of that traffic. The application presents this information to the network in the form a traffic contract. An example of trafficthatrequiresthistype of service categoryare variable rate, compressed video streams.Sourcesthatuse rt-VBR connectionsare expectedtotransmitata rate that varieswithtime (forexample,trafficthatcan be consideredbursty).Real-time VBRconnectionscanbe characterized by a Peak Cell Rate (PCR), Sustained Cell Rate (SCR), and Q. 4. Describe the following: a) Open Shortest Path First (OSPF) protocol Answer:OpenShortestPath First (OSPF) is a routing protocol for Internet Protocol (IP) networks. It uses a link state routing algorithm and falls into the group of interior routing protocols, operating withinasingle autonomoussystem (AS). It is defined as OSPF Version 2 in RFC 2328 (1998) for IPv4. The updates for IPv6 are specified as OSPF Version 3 in RFC 5340 (2008). OSPF is perhaps the most widely used interior b) Broader Gateway Routing Protocol (BGP) Answer: Border Gateway Protocol (BGP) is a standardized exterior gateway protocol designed to exchange routingandreachabilityinformationbetween autonomous systems (AS) on the Internet. The protocol is oftenclassifiedasapath vectorprotocol but is sometimesalsoclassed as a distance- vector routing protocol. The Border Gateway Protocol makes routing decisions based on paths, networkpolicies,orrule-setsconfiguredby a network administrator and is involved in making core routing decisions. Q. 5. Write short notes on: a) Cryptography: Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense. The
- 3. originatorof an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, b) Encryption:In cryptography, encryption is the process of encoding messages or information in such a way that only authorized parties can read it. Encryption does not of itself prevent interception,butdenies the message content to the interceptor.:374 In an encryption scheme, the message or information, referred to as plaintext, is encrypted using an encryption algorithm, generating ciphertext c) Decryption:Decryptionisthe reverse process to Encryption. Frequently, the same Cipher is used for both Encryption and Decryption. While Encryption creates a Ciphertext from a Plaintext, Decryption creates a Plaintext from a Ciphertext. The process of decoding data that has been encrypted into a secret format. Decryption requires a secret key or password. Decryption is the process of converting d) Cryptanalysis:Cryptanalysisreferstothe studyof ciphers,ciphertext,orcryptosystems(thatis,to secret code systems) with a view to finding weaknesses in them that will permit retrieval of the plaintextfromthe ciphertext,withoutnecessarilyknowingthe keyorthe algorithm.Thisisknown as breaking the cipher, ciphertext, or cryptosystem. Cryptanalysis is the study of e) Cryptology:Cryptology is the mathematics, such as number theory, and the application of formulas and algorithms, that underpin cryptography and cryptanalysis. Since the cryptanalysis concepts are highly specialized and complex, we concentrate here only on some of the key mathematical concepts behind Q. 6. Differentiate between Single server queue and Multi-server queue Answer: Queueingtheoryisthe mathematical study of waitinglines, or queues. In queueing theory a model isconstructedsothat queue lengthsandwaitingtime can be predicted.Queueing theory is generally considered a branch of operations research because the results are often used when makingbusinessdecisionsaboutthe resourcesneededtoprovideaservice. Queueing theory has its origins in research by Agner Krarup Erlang when Dear students get fully solved assignments
- 4. Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
