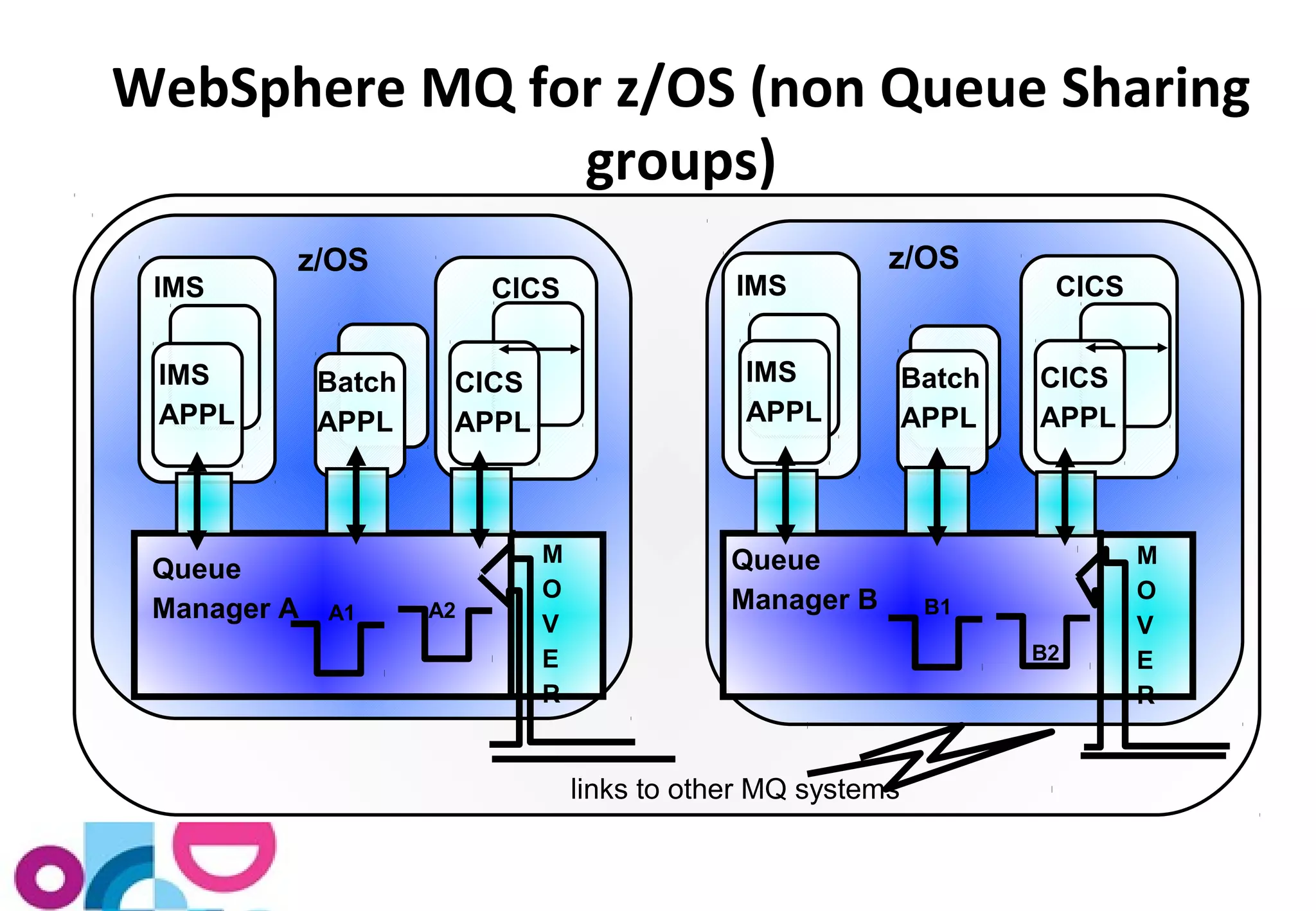
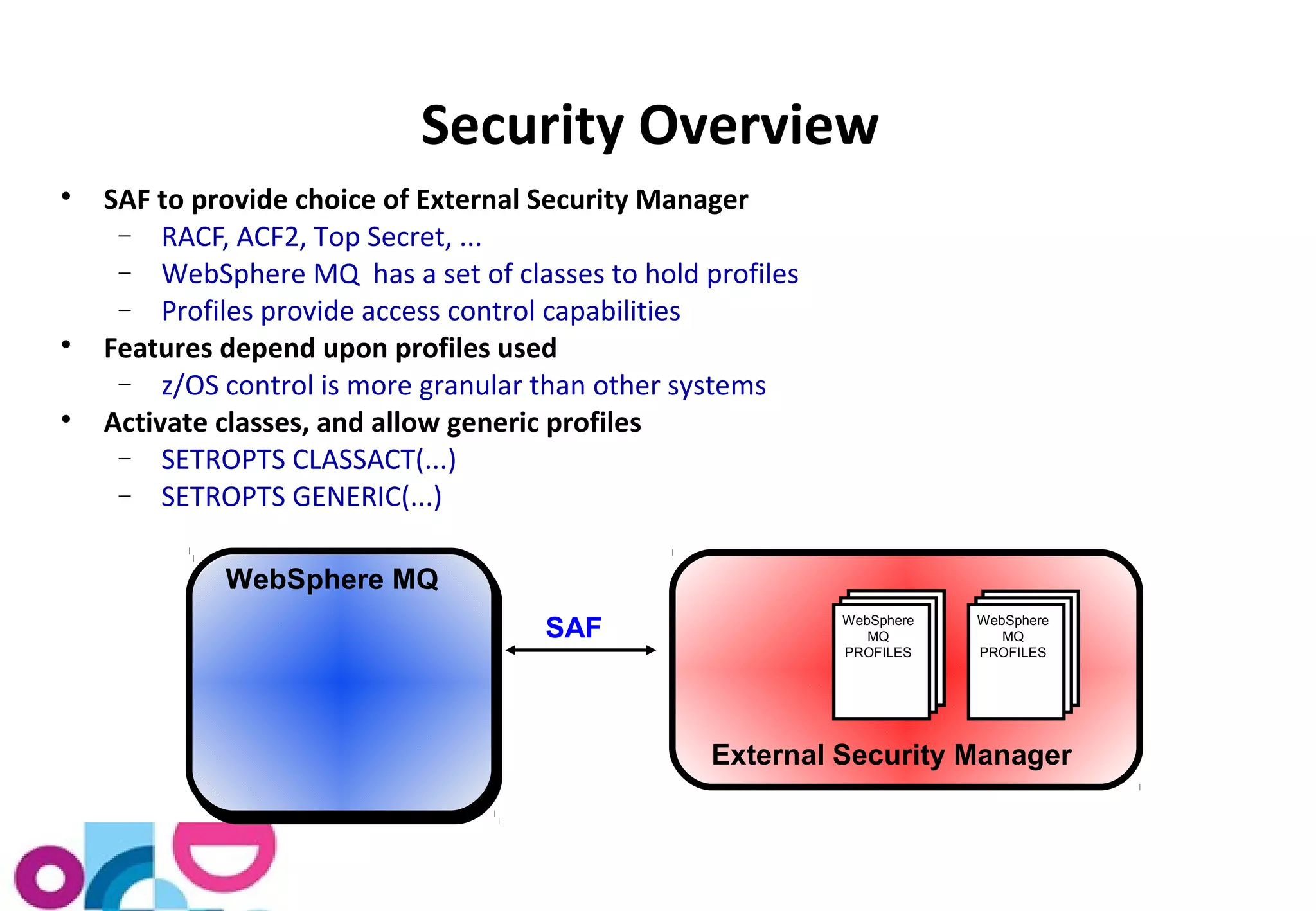
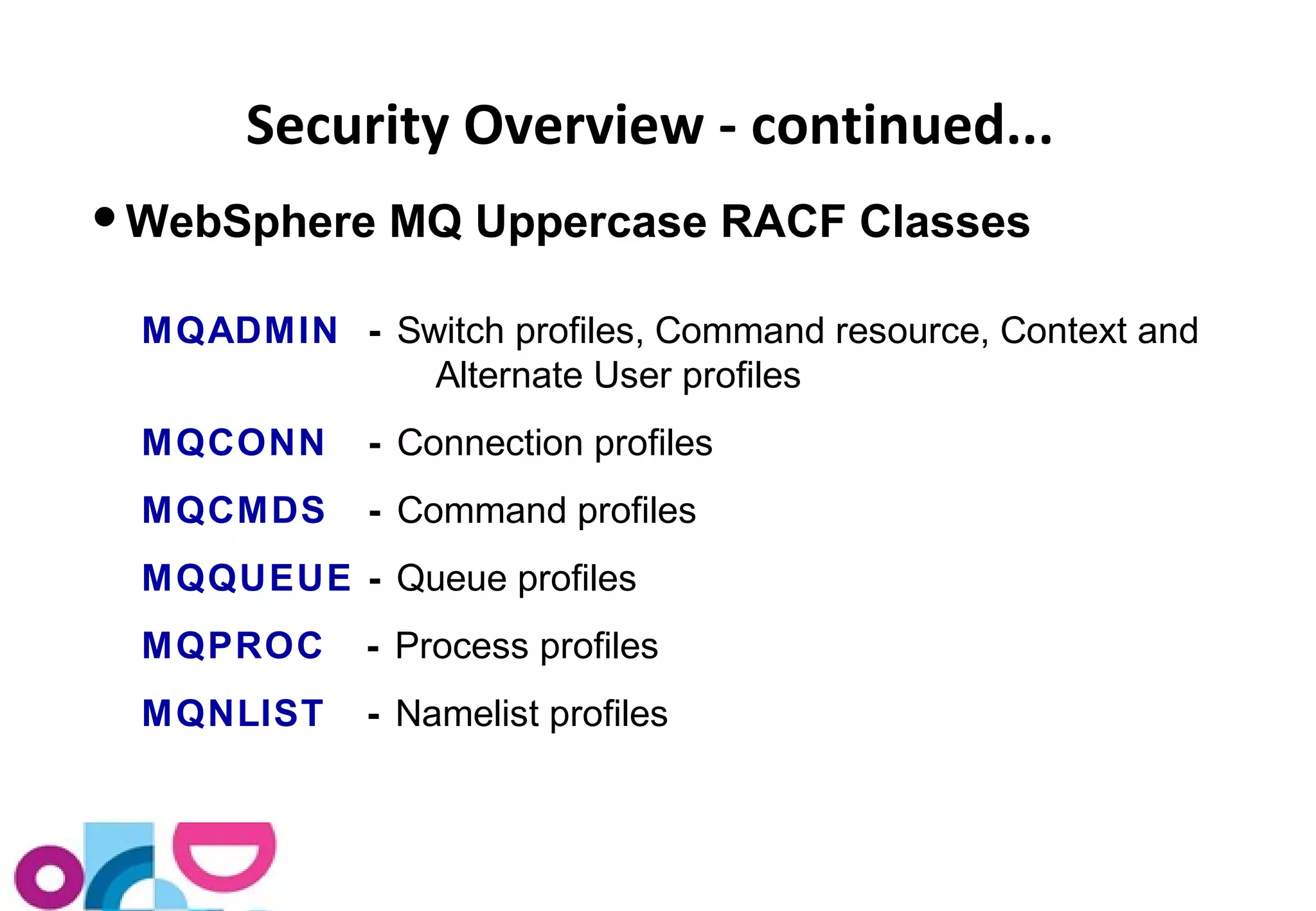
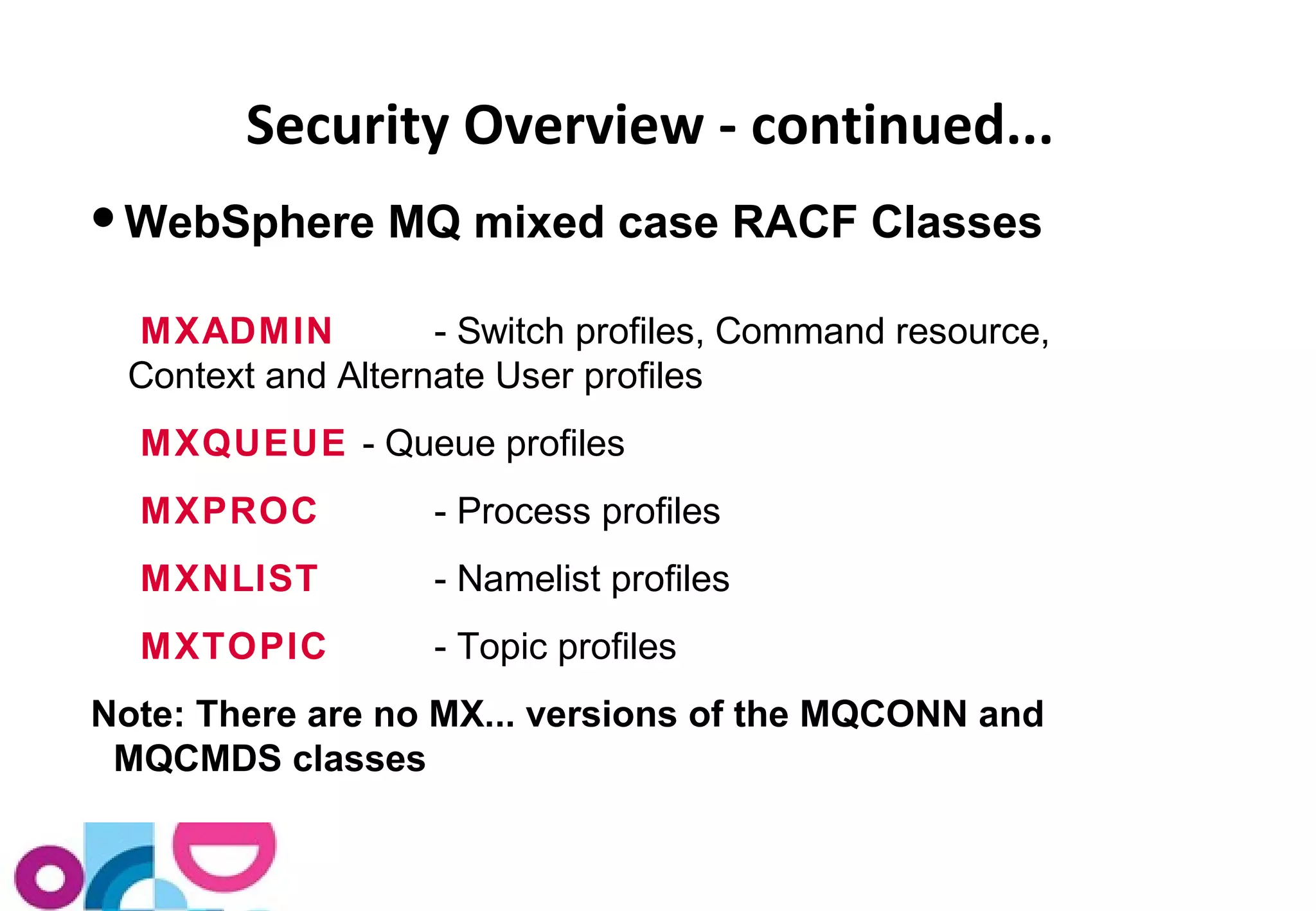
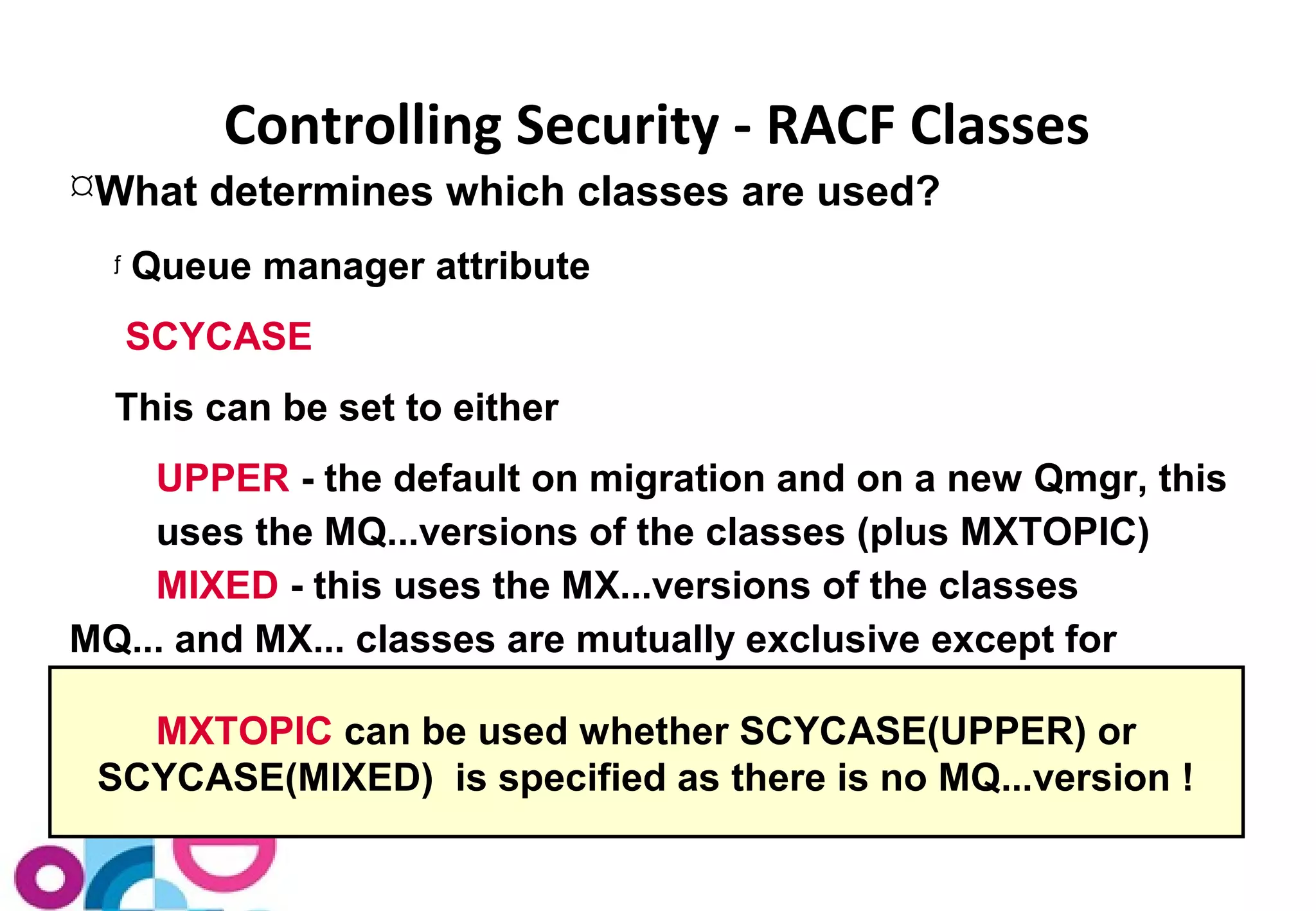
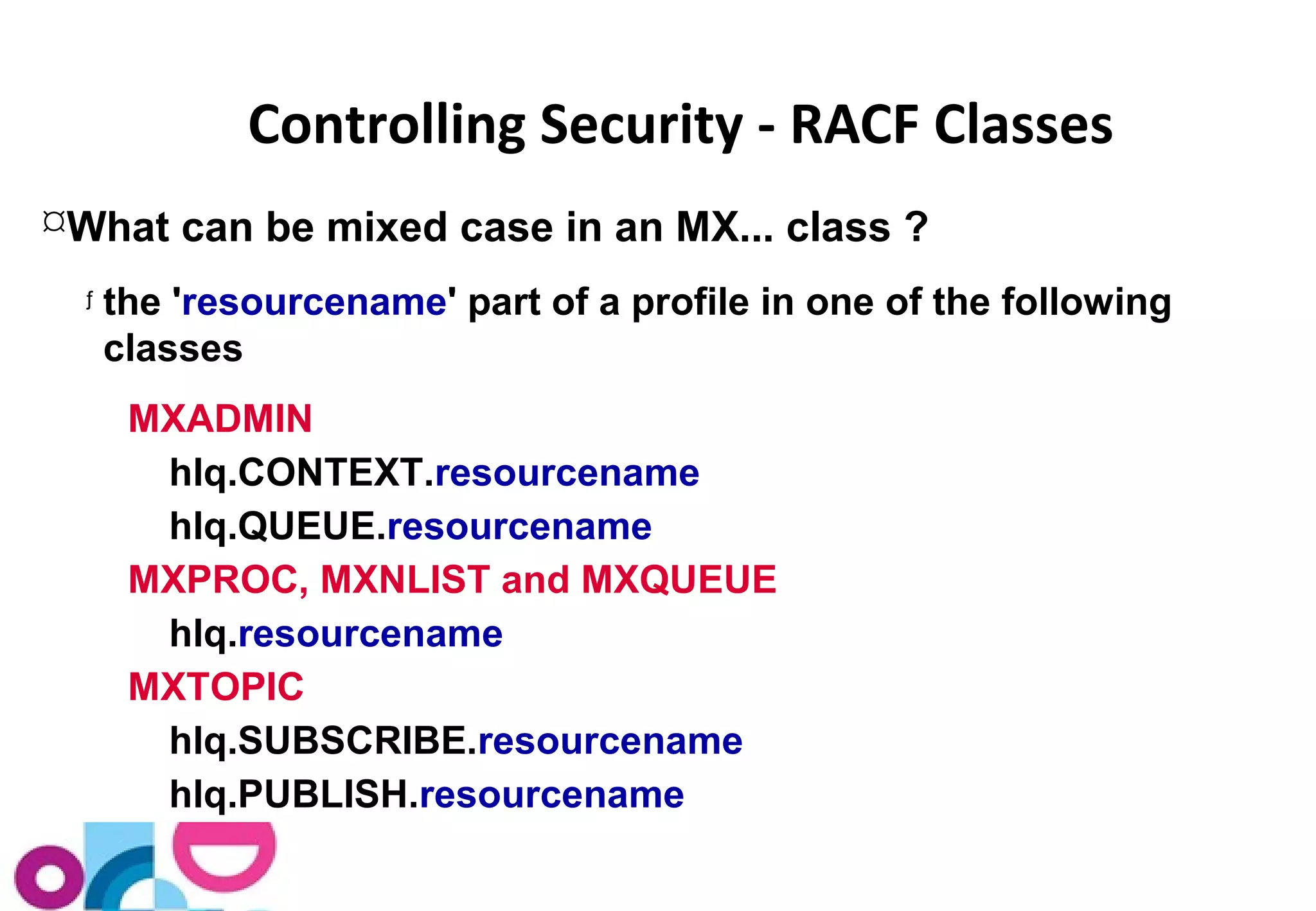
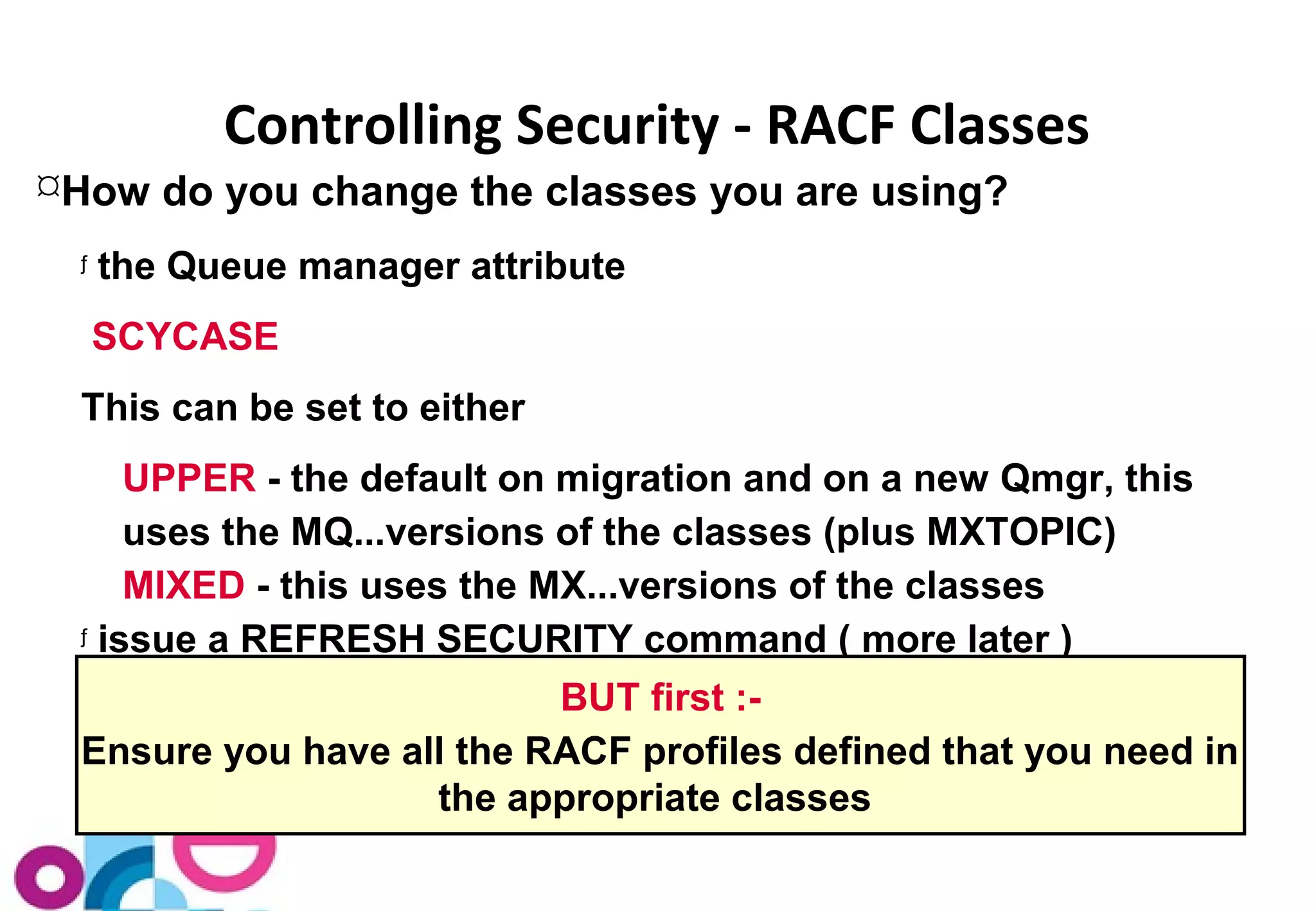
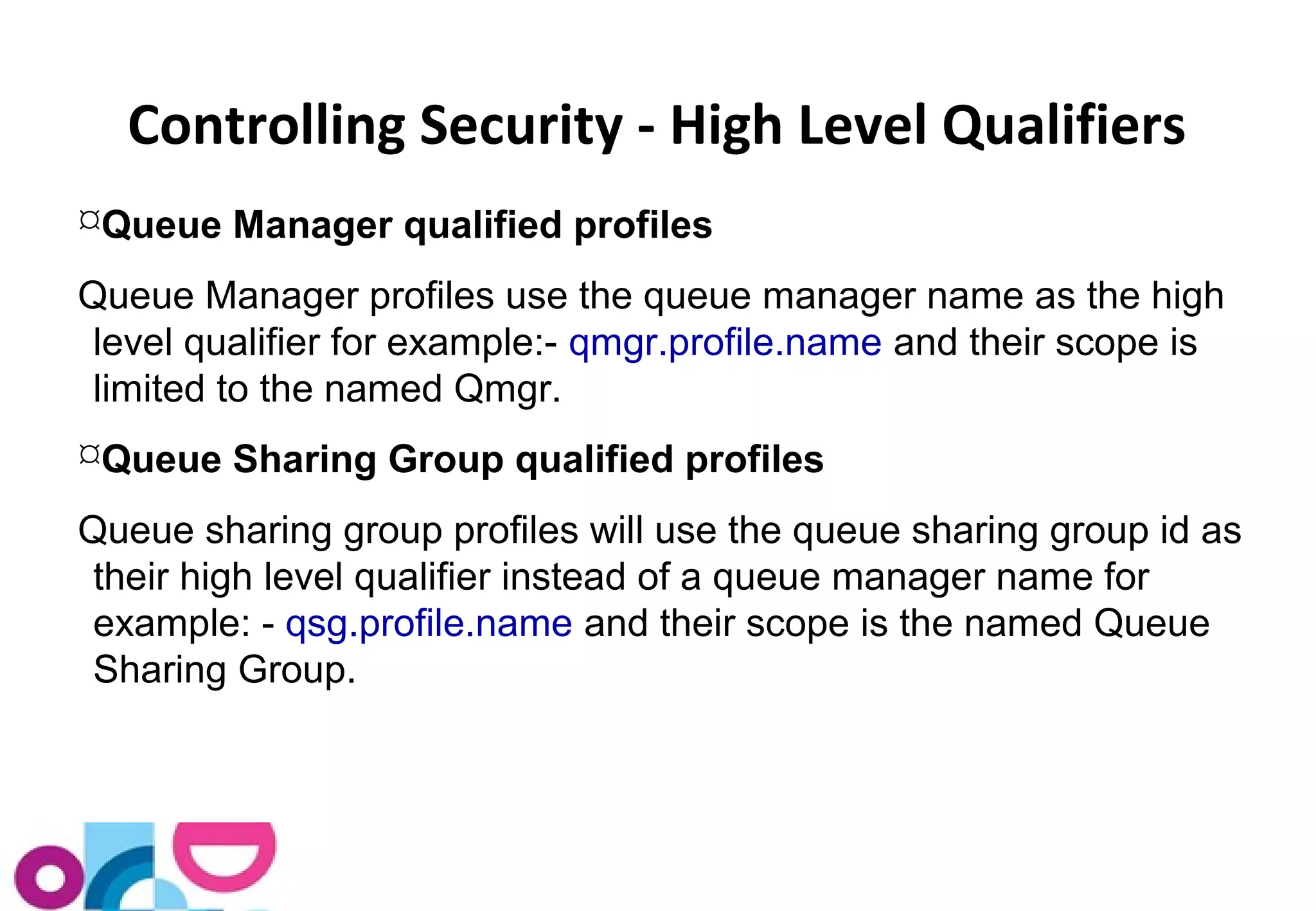
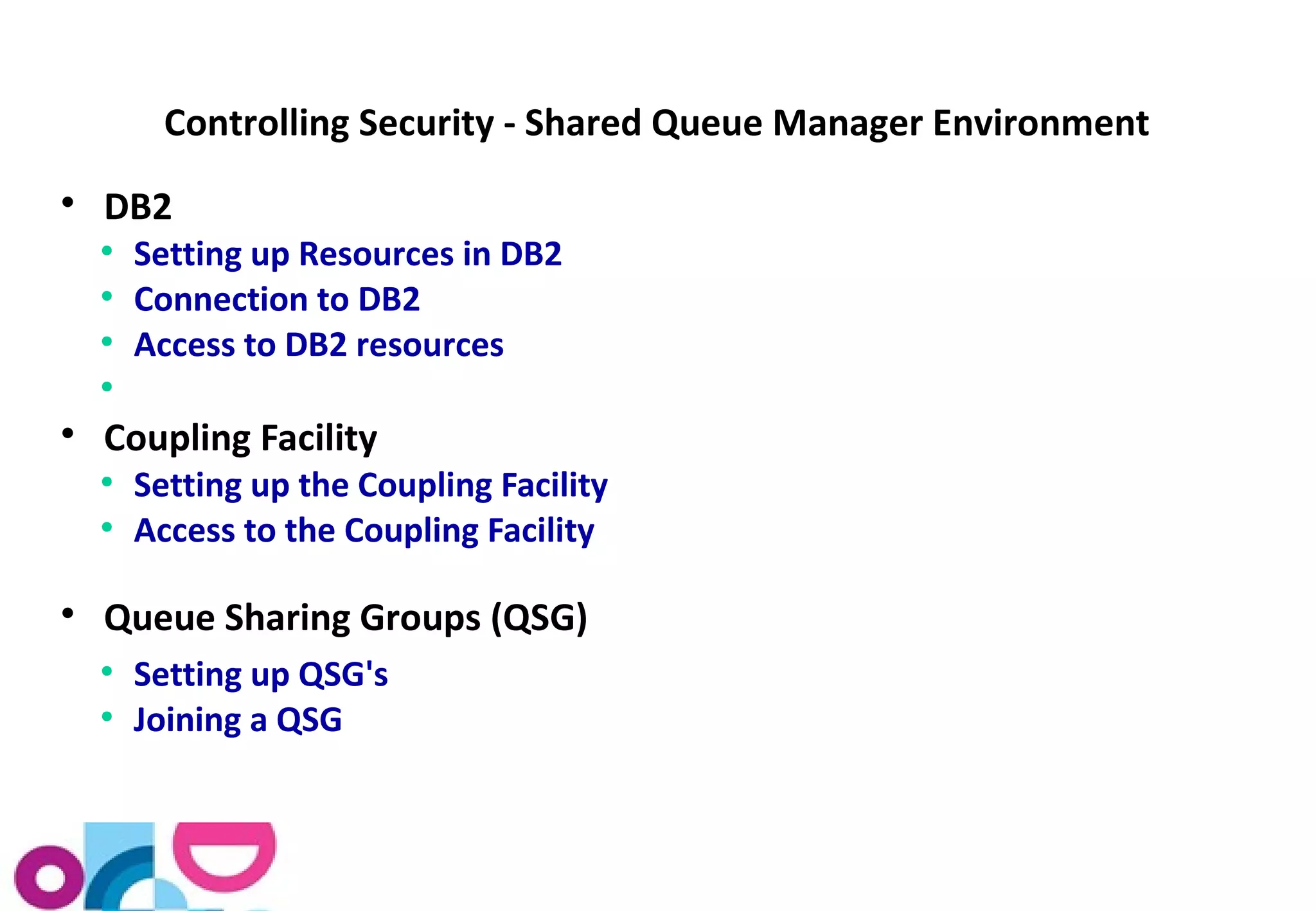
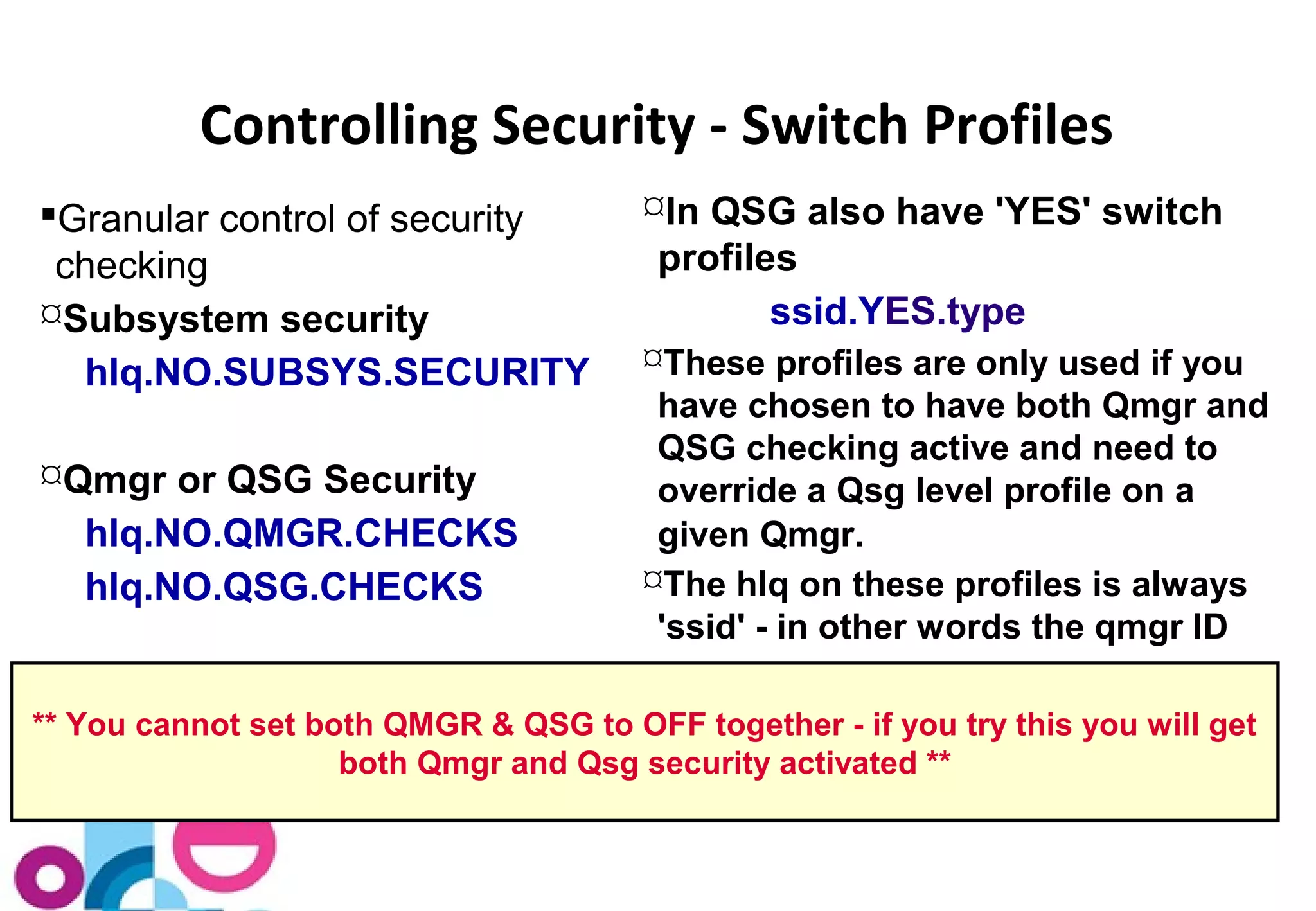
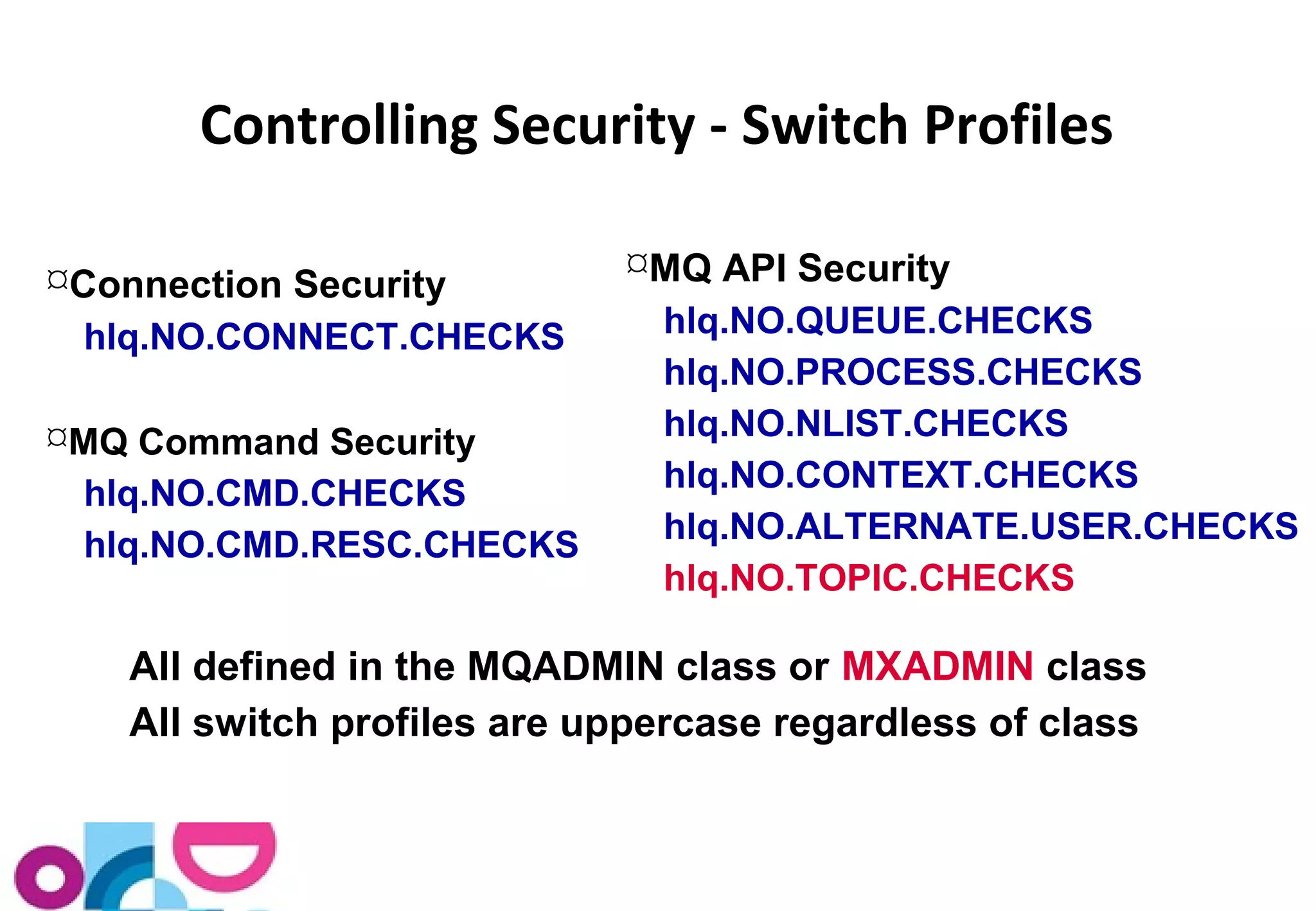
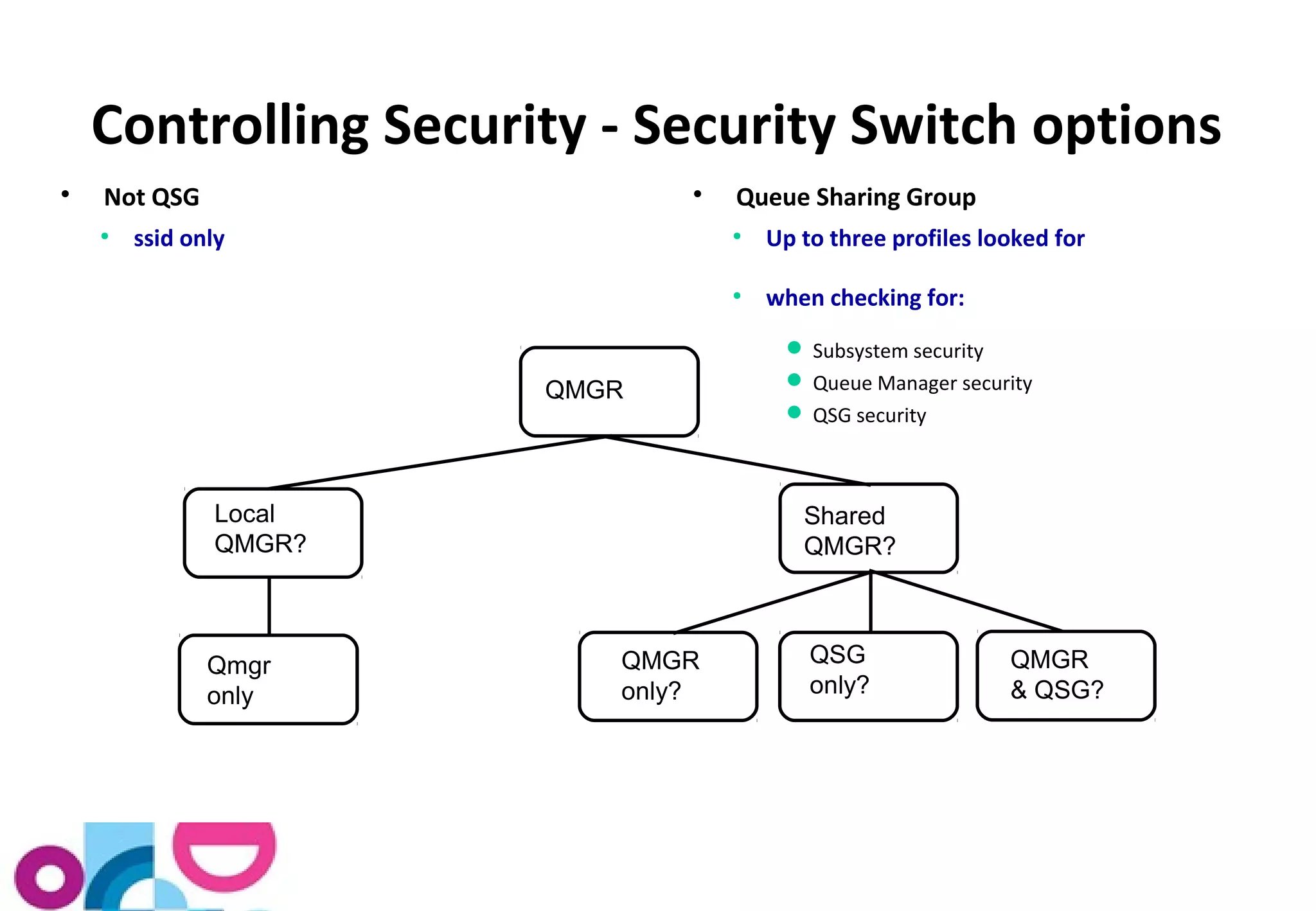
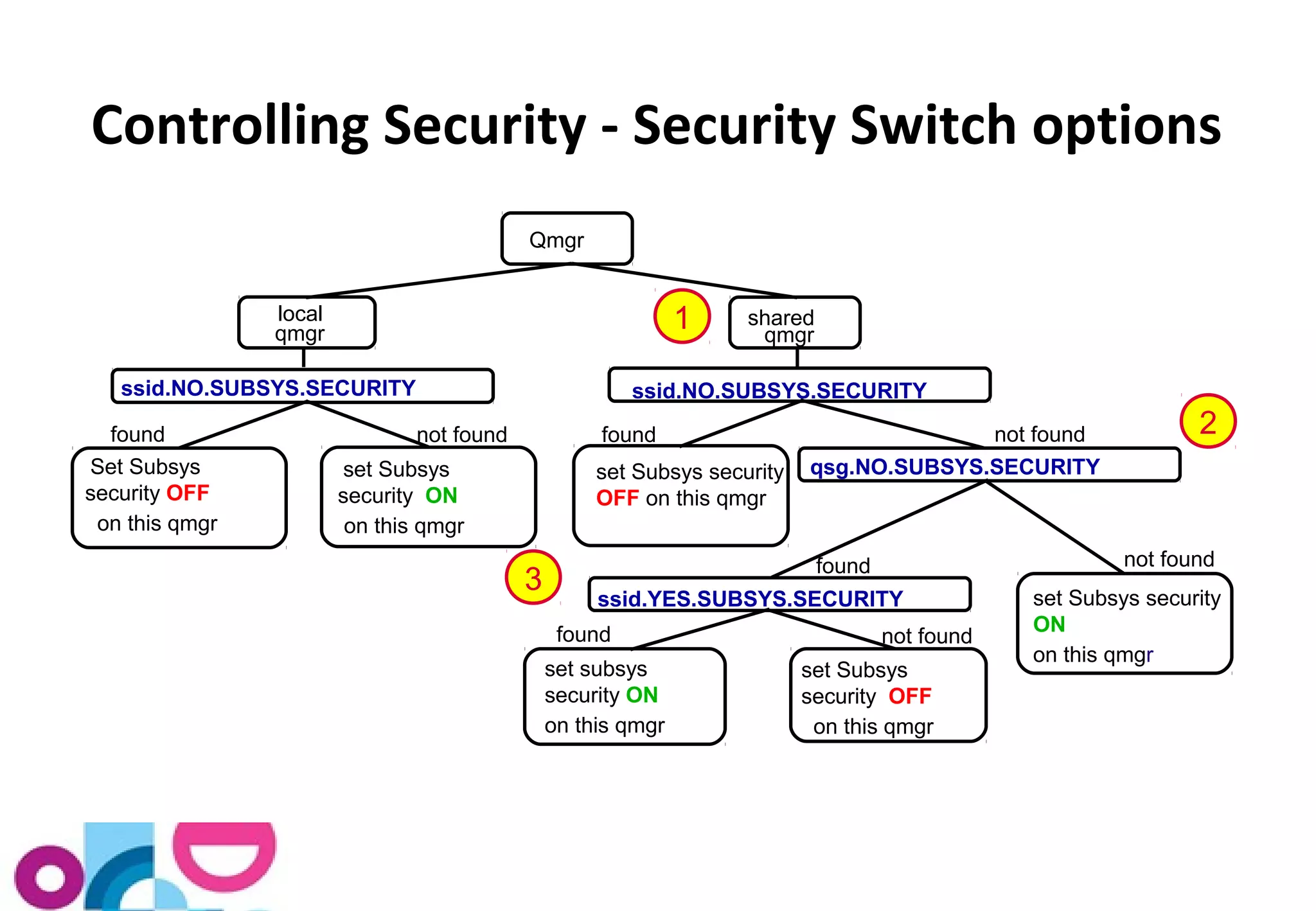
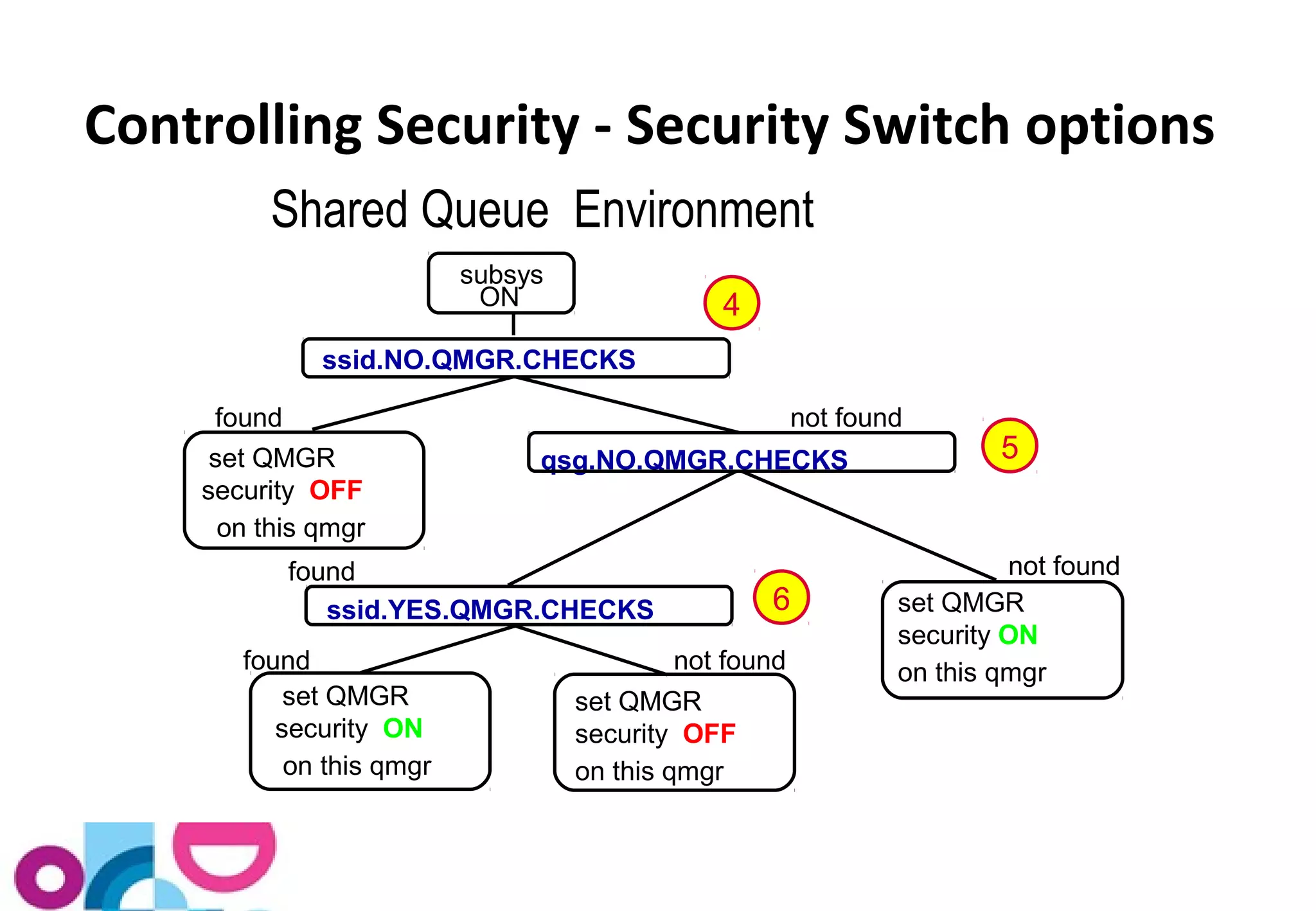
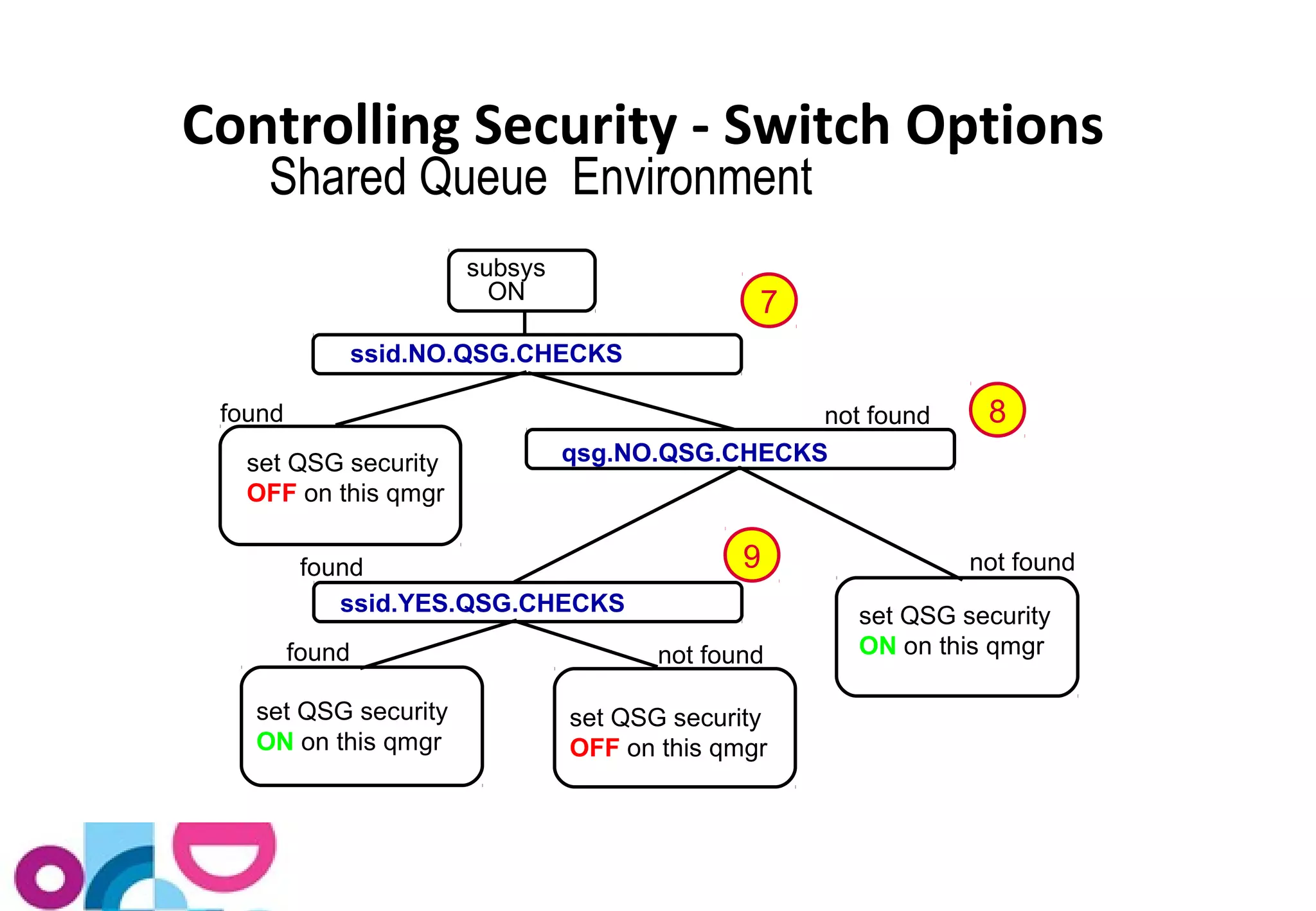
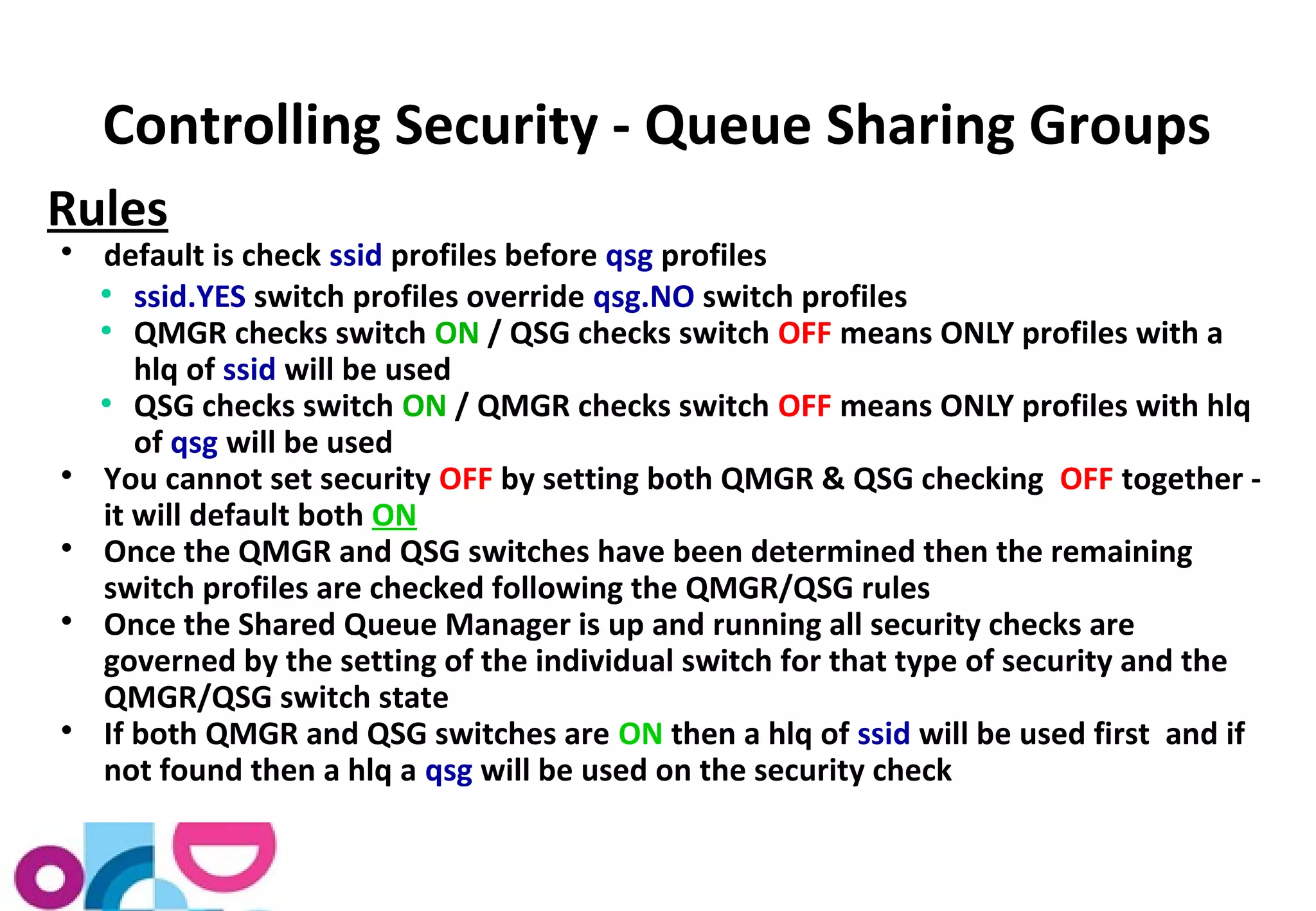
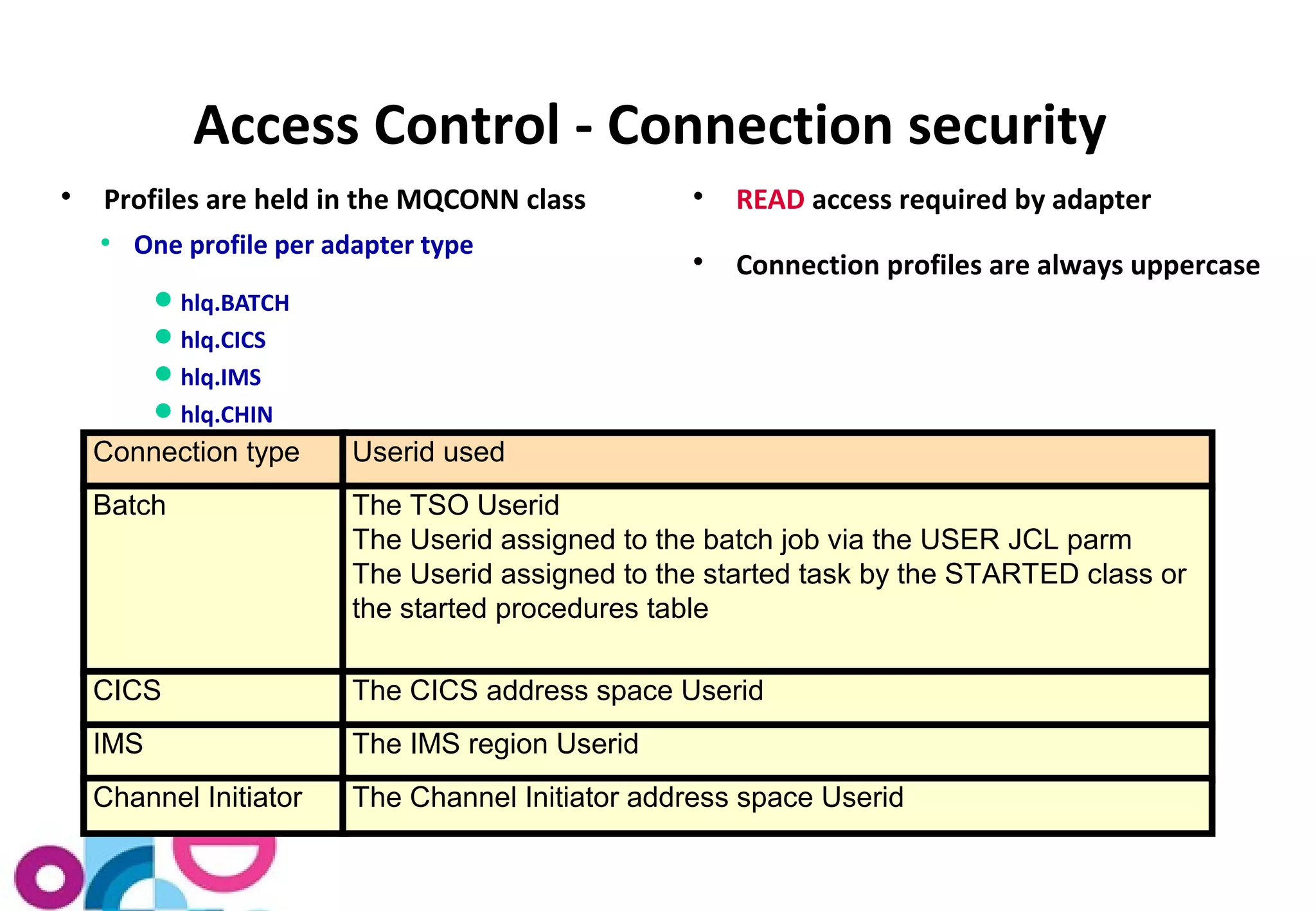
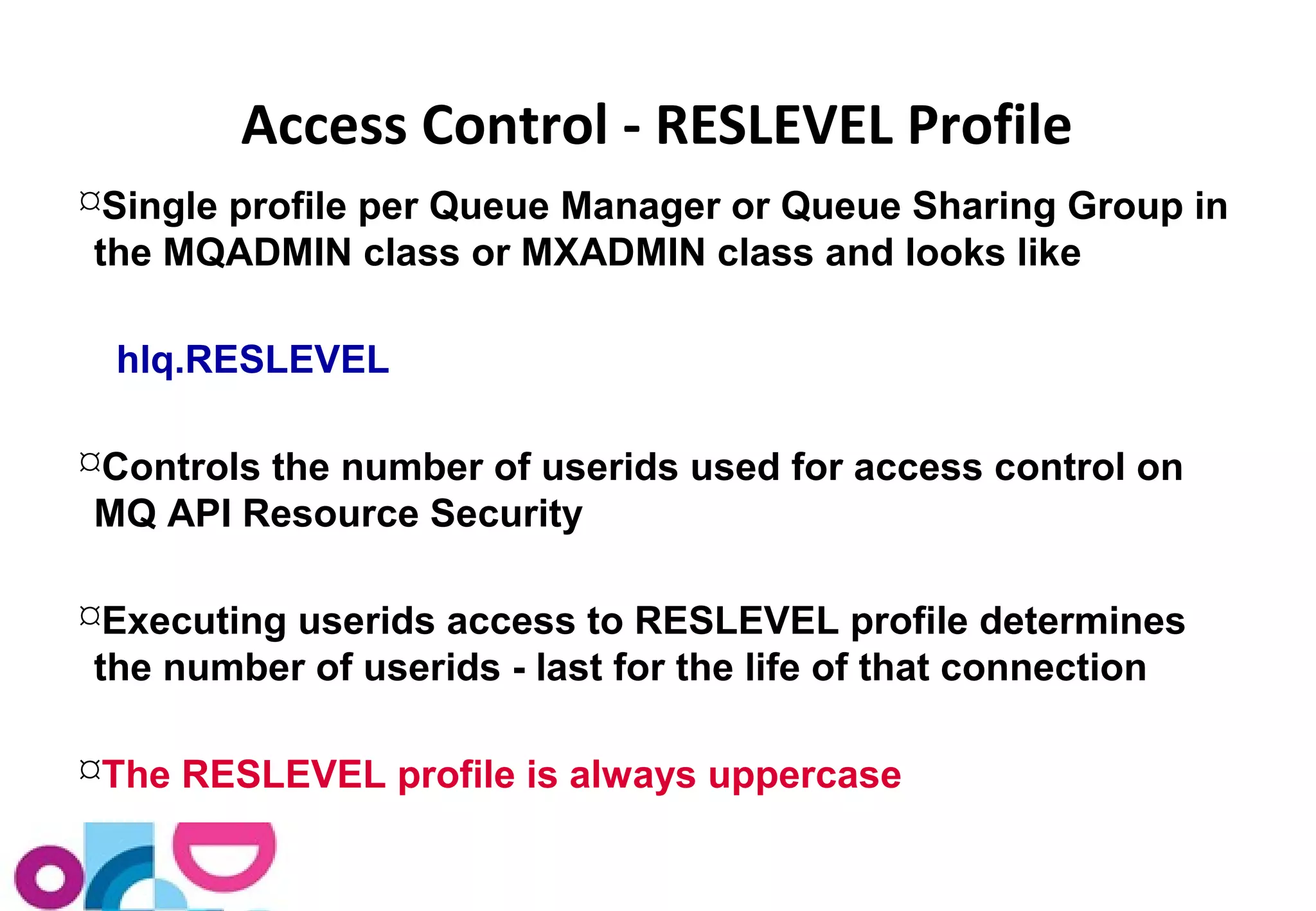
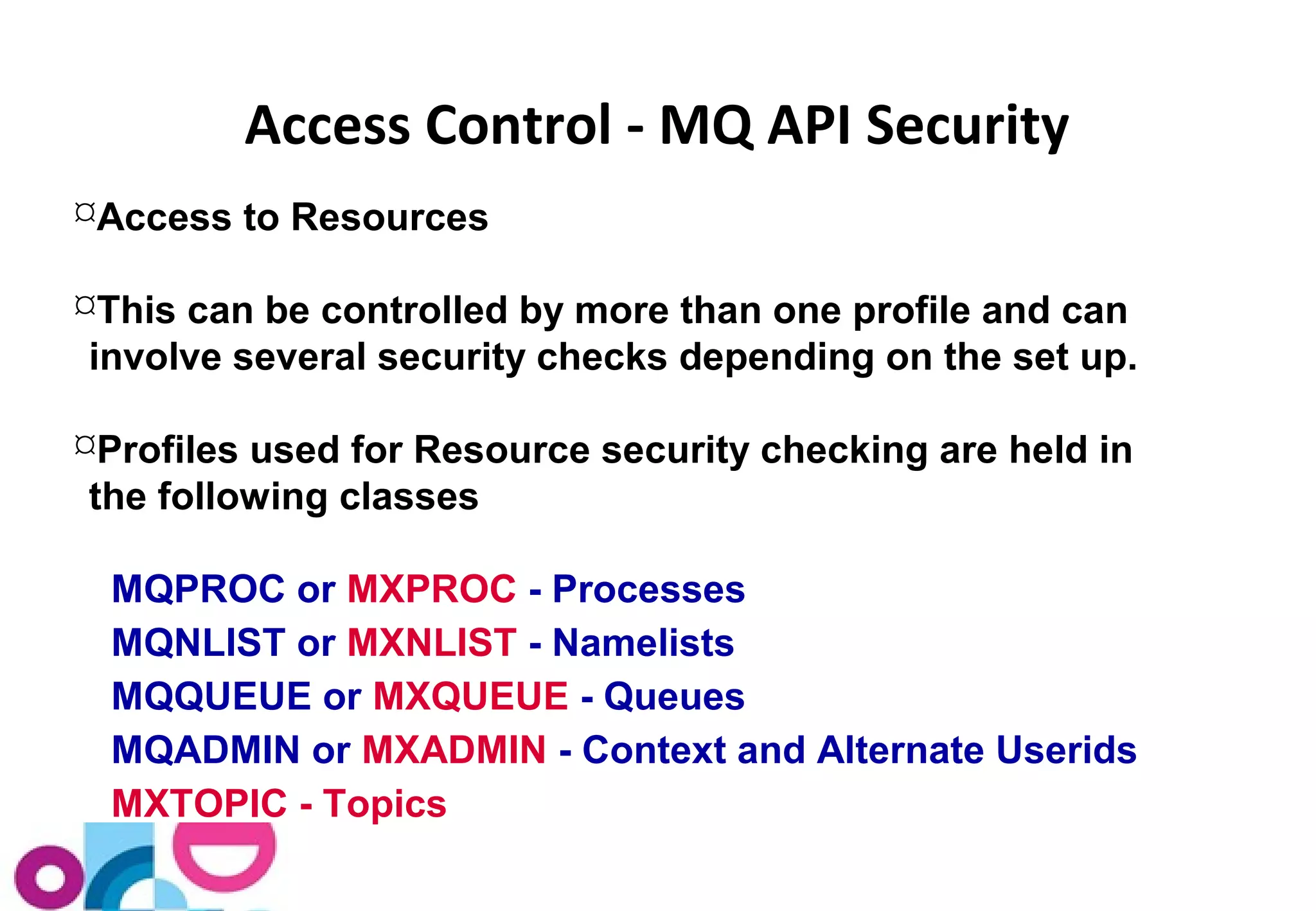
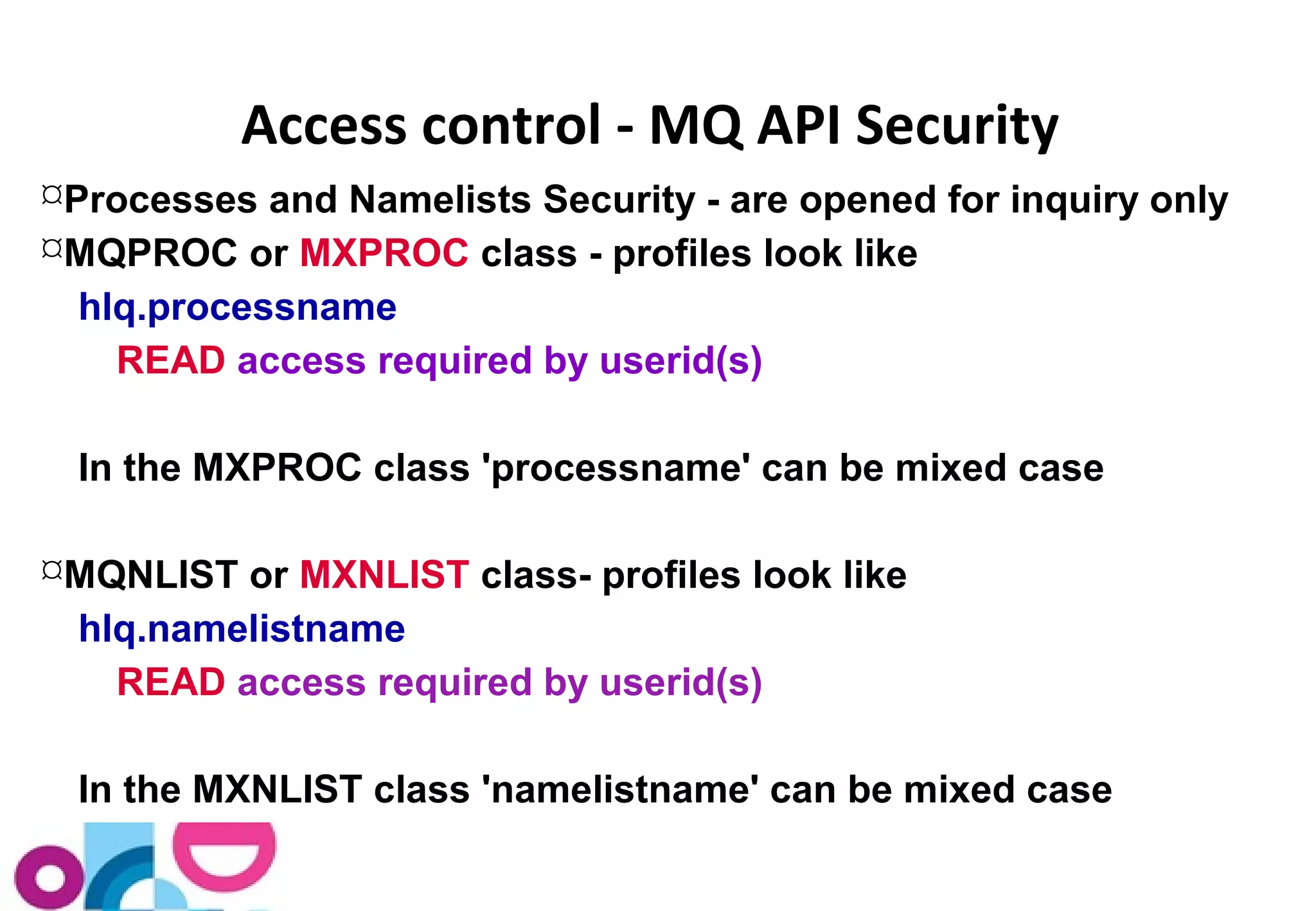
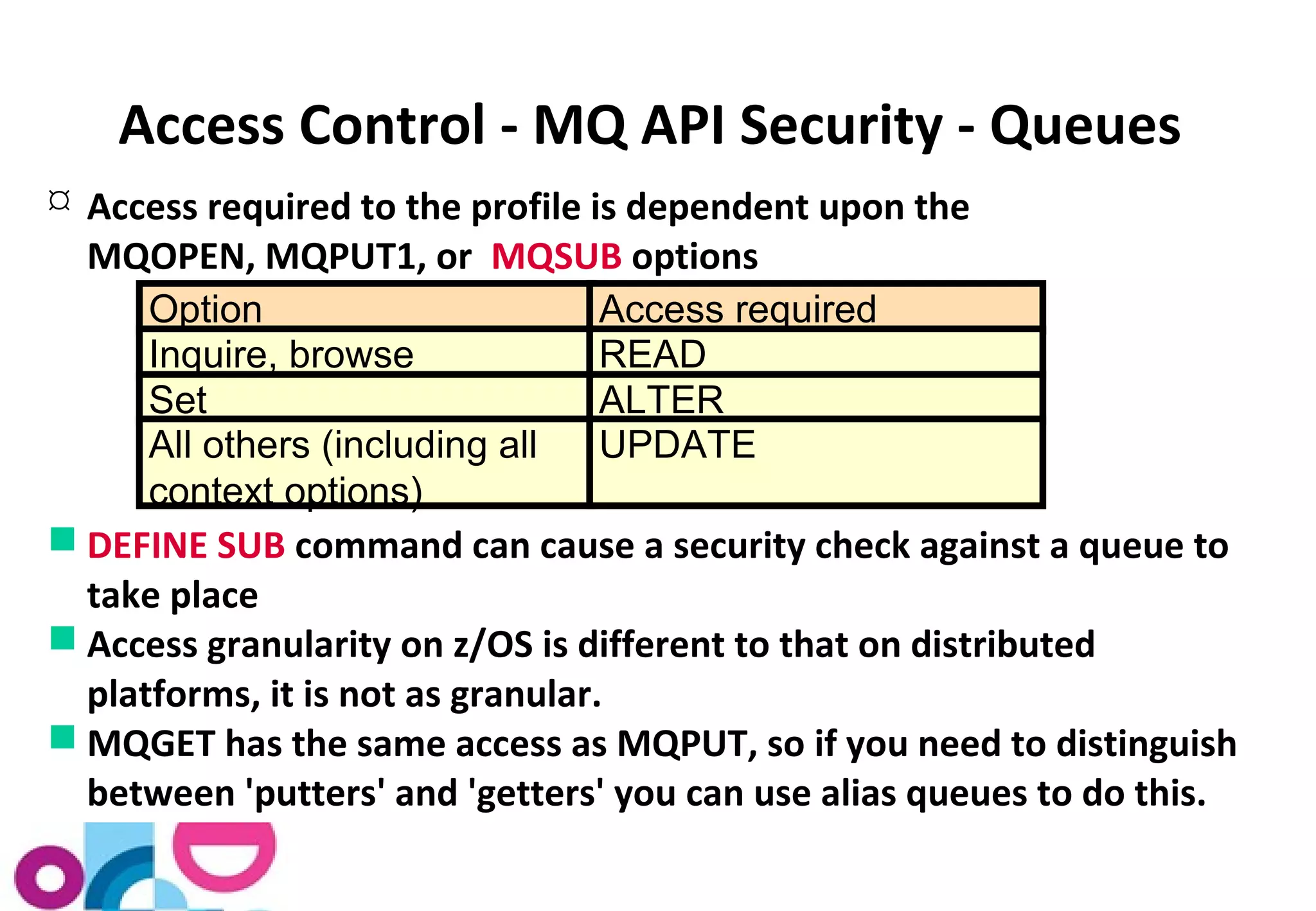
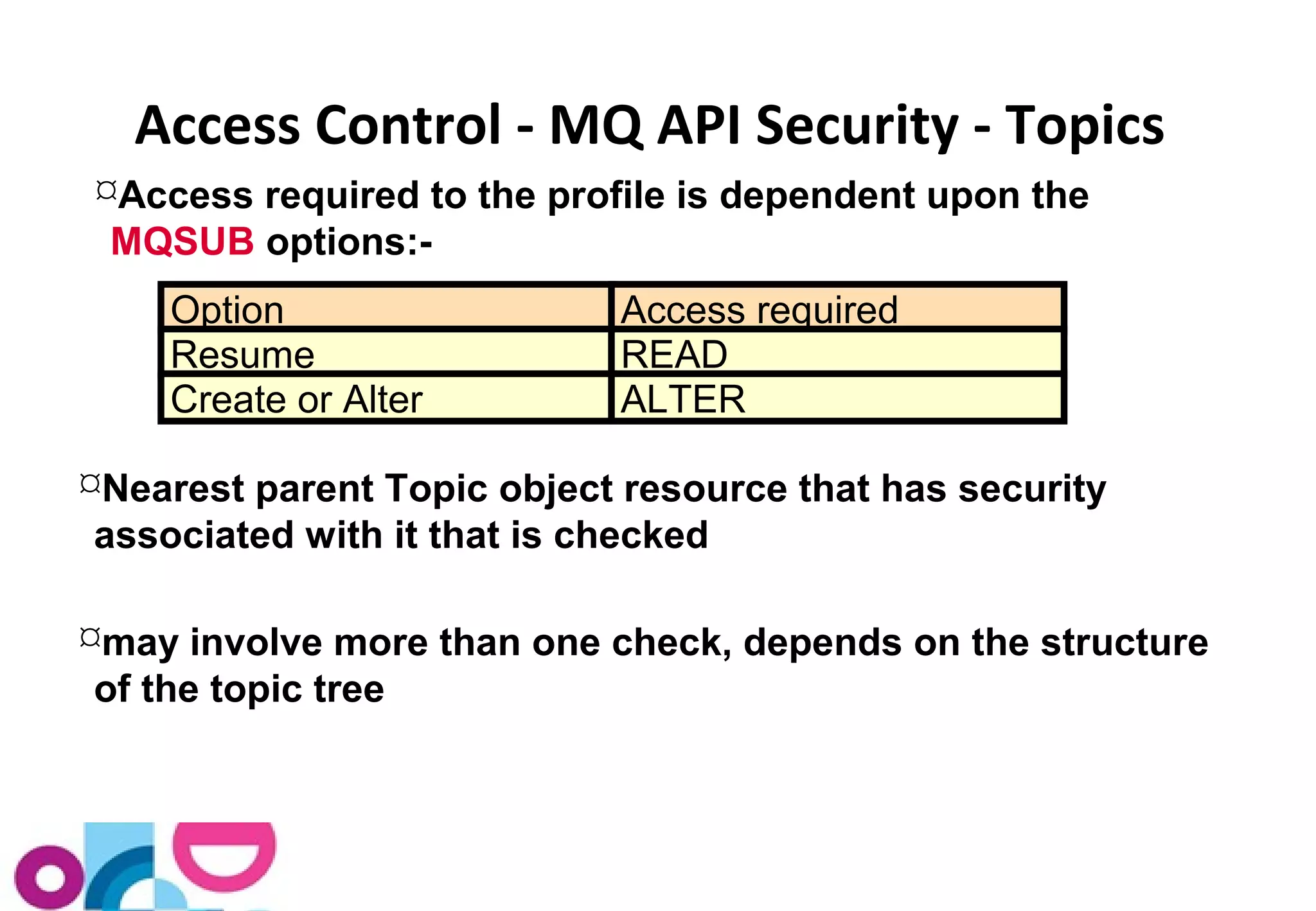
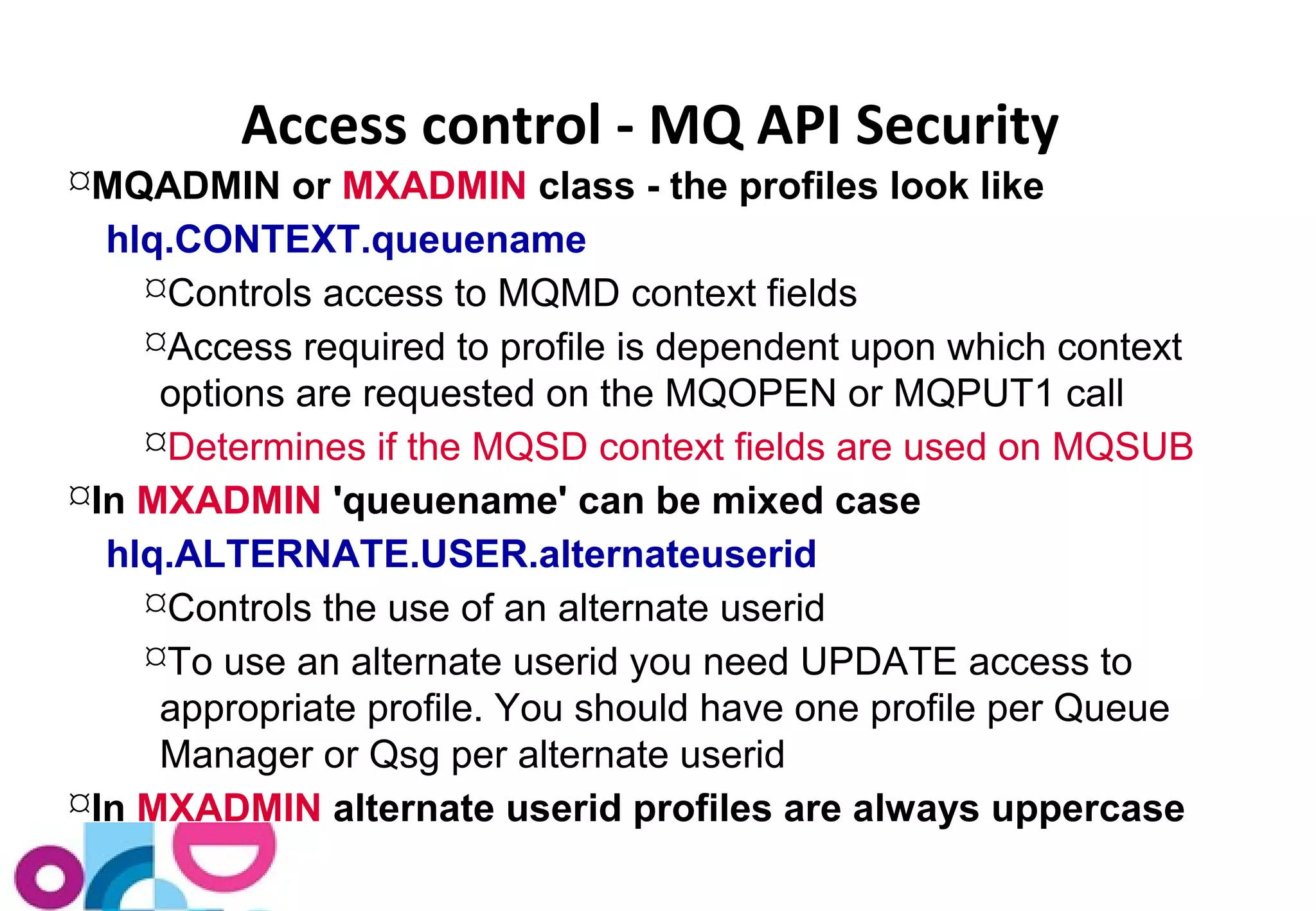
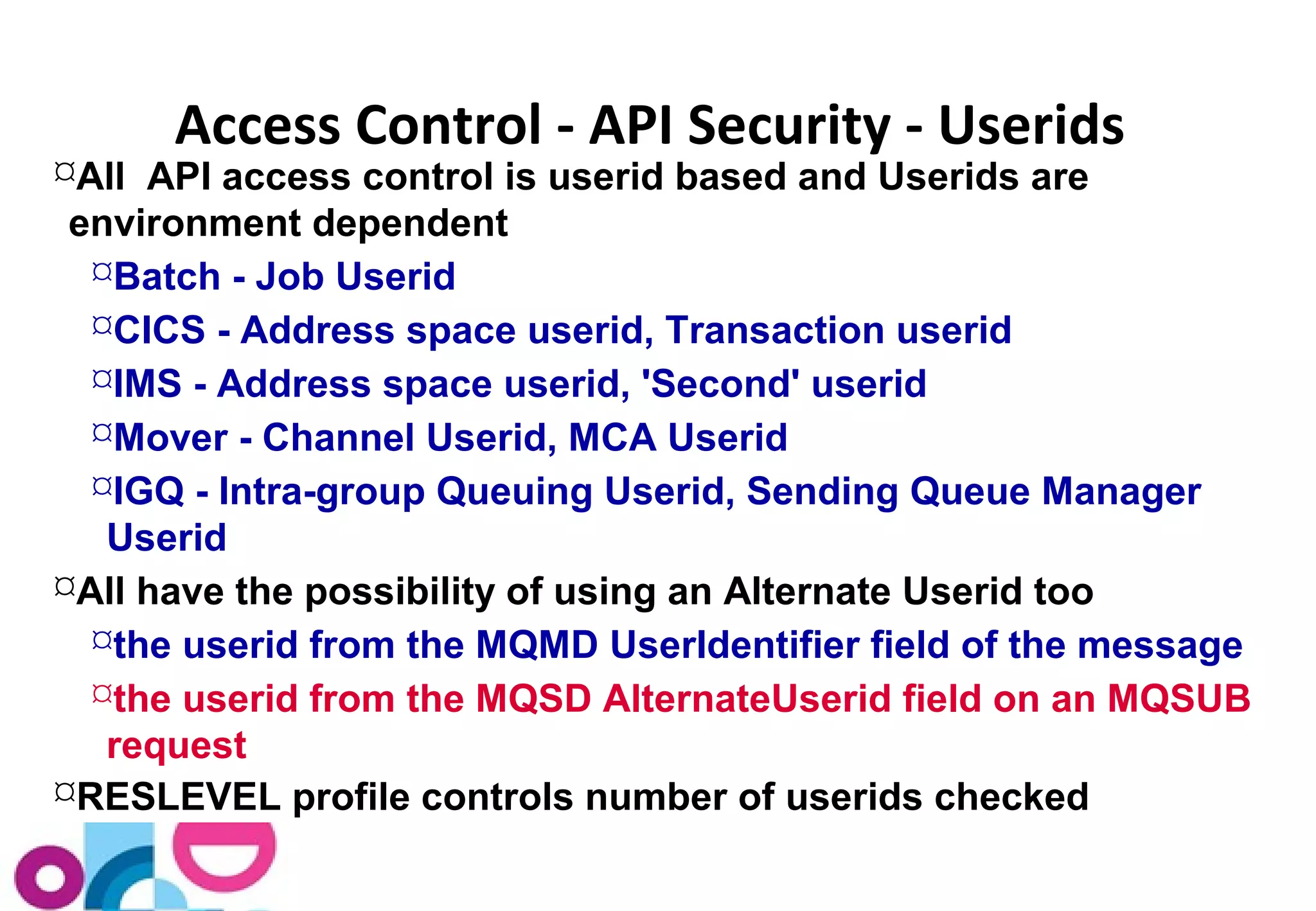
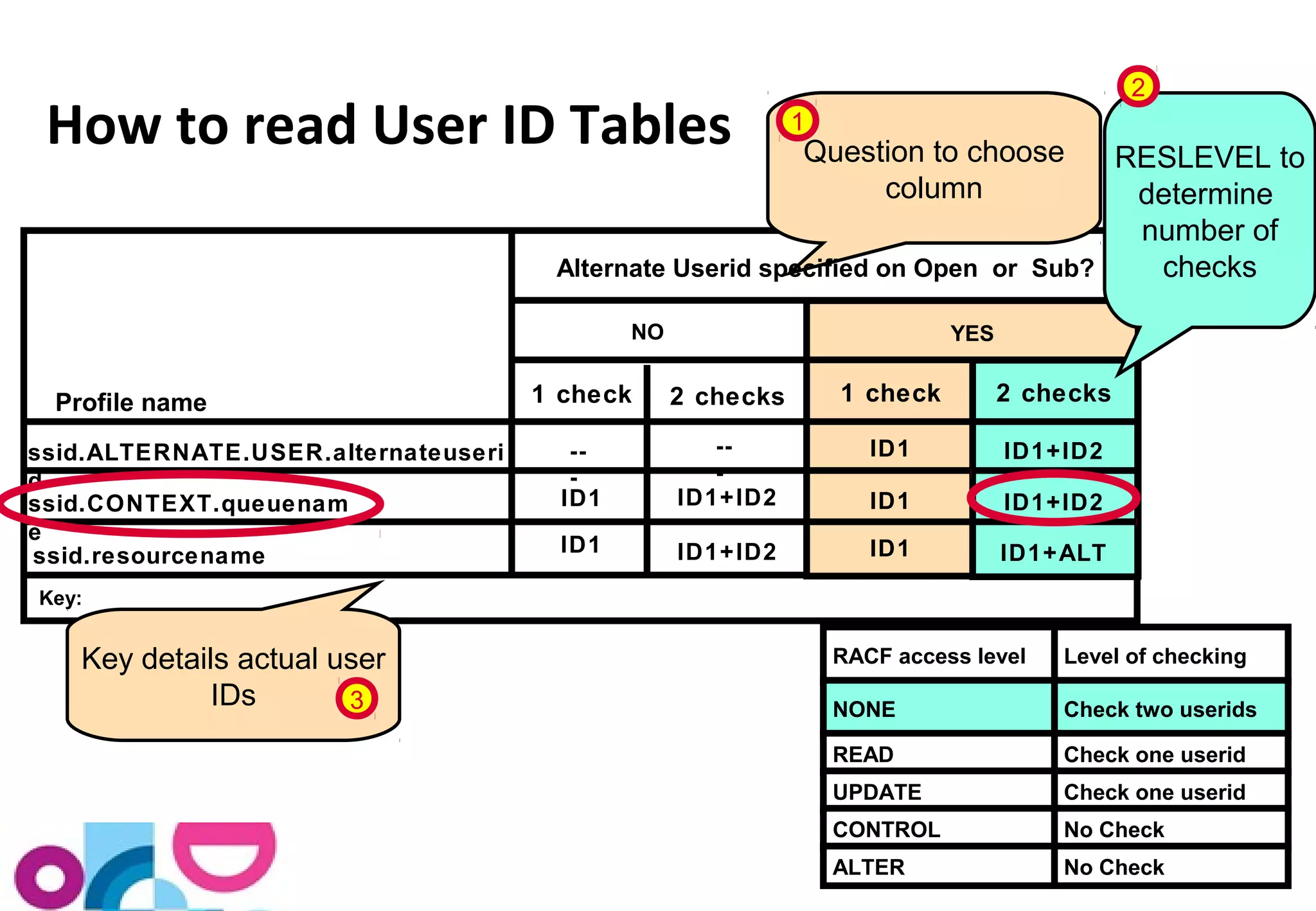
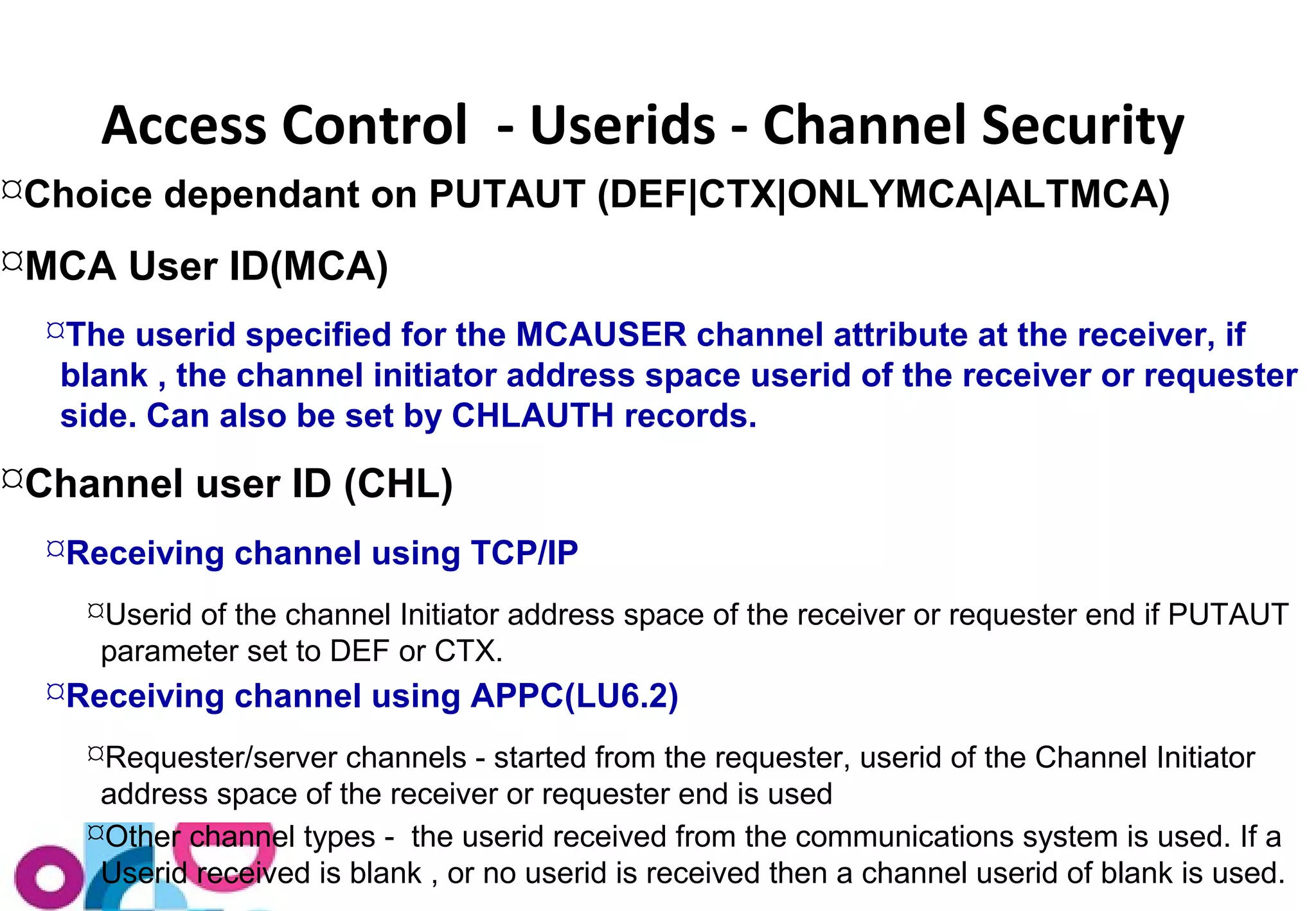
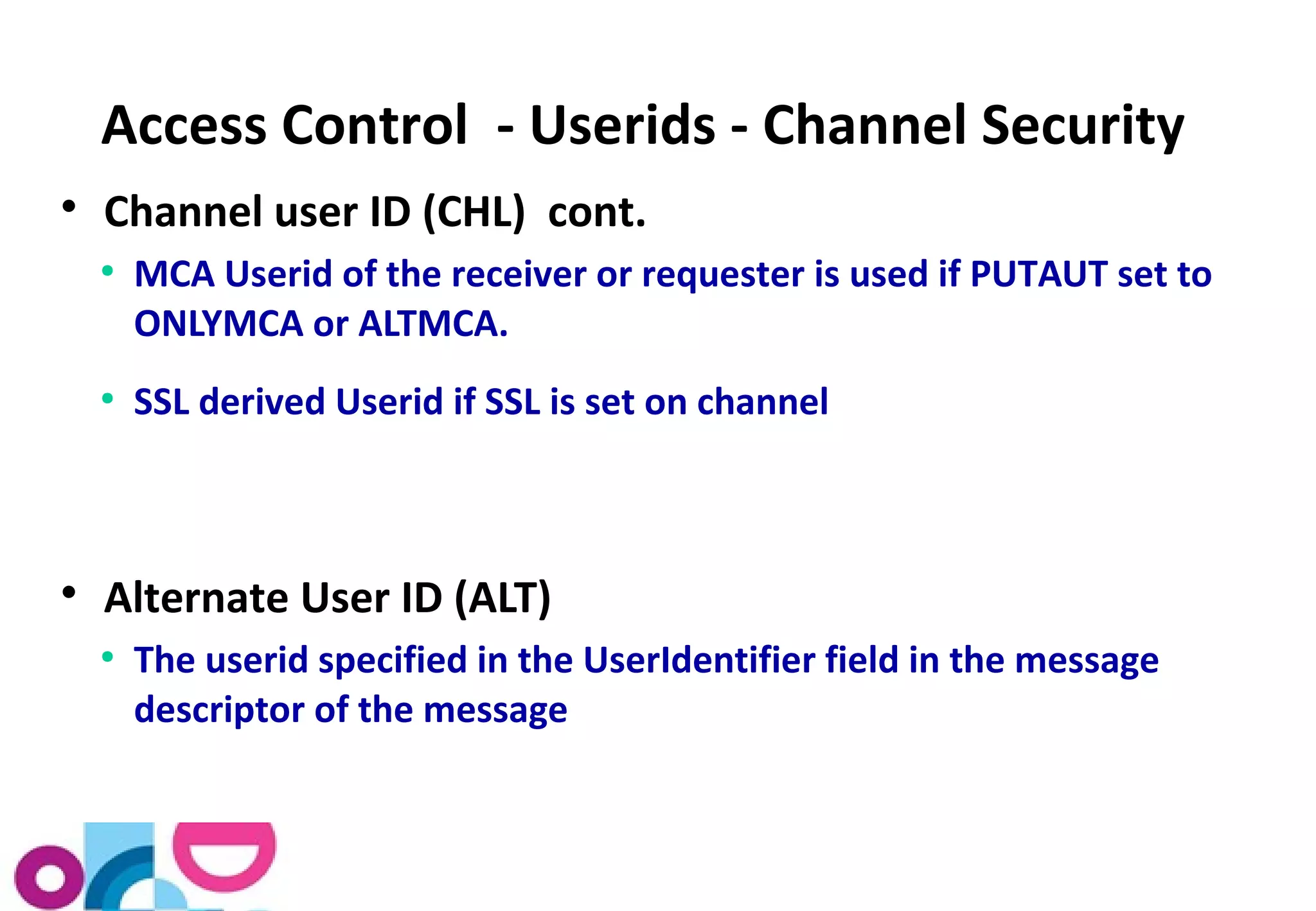
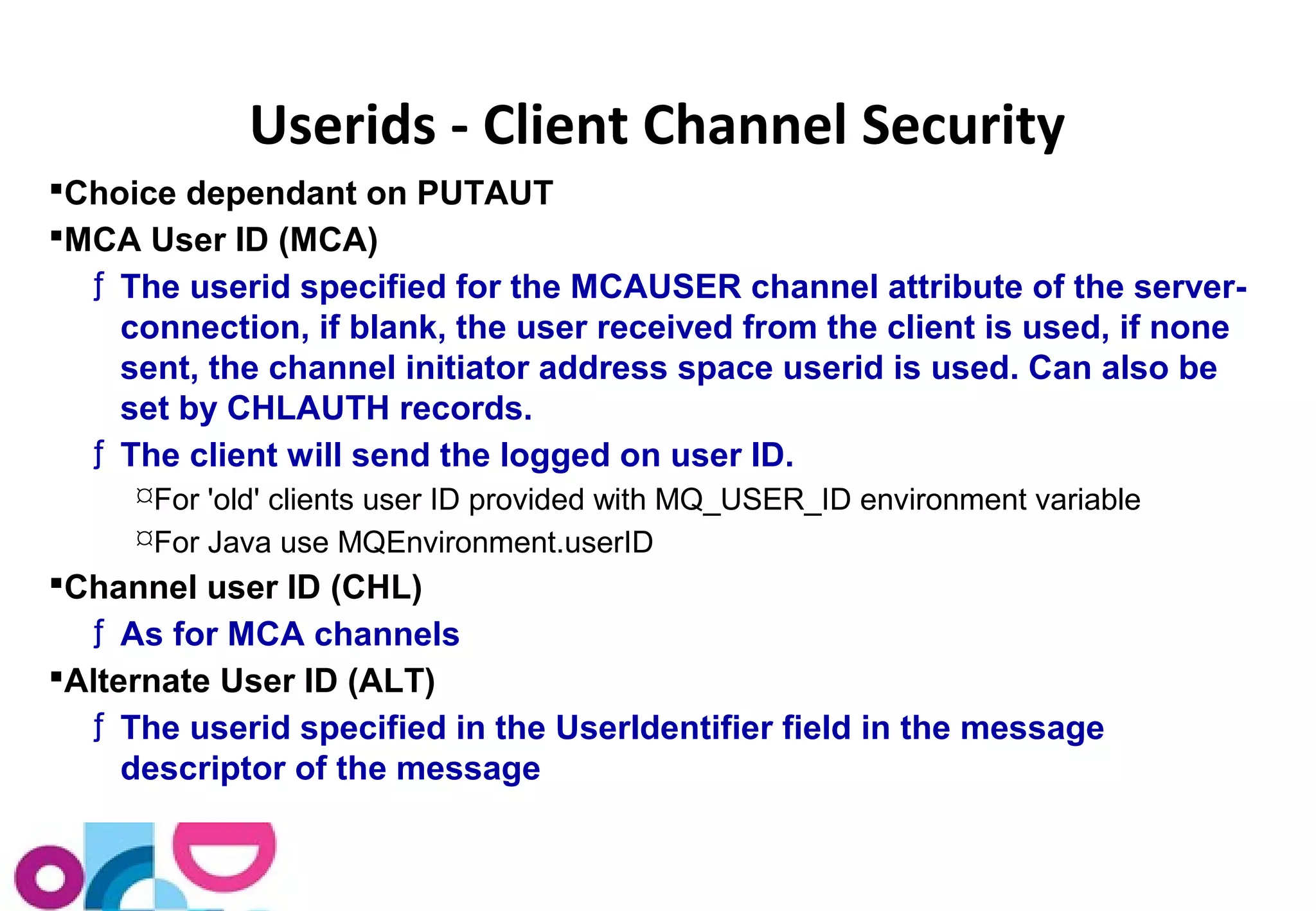
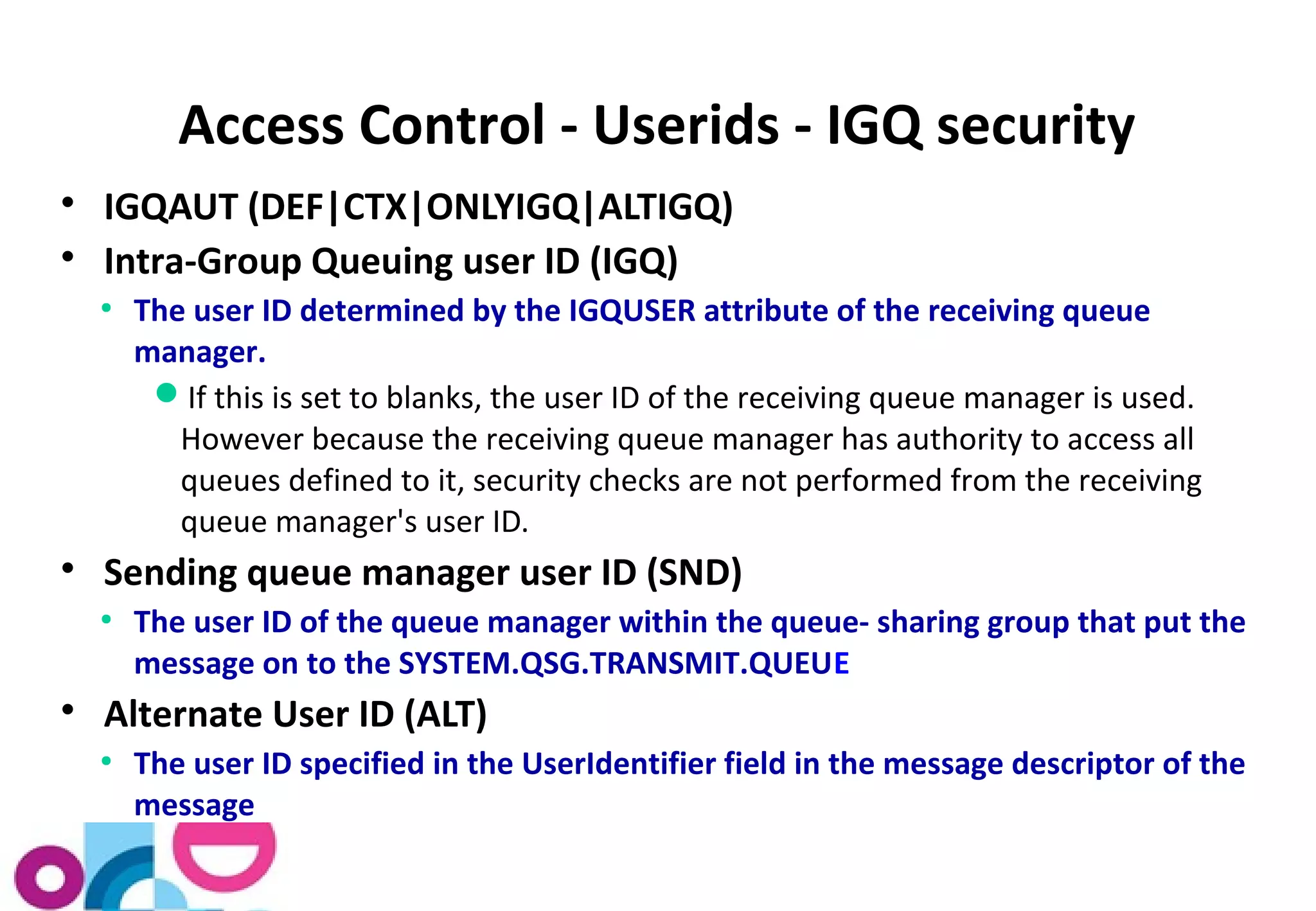
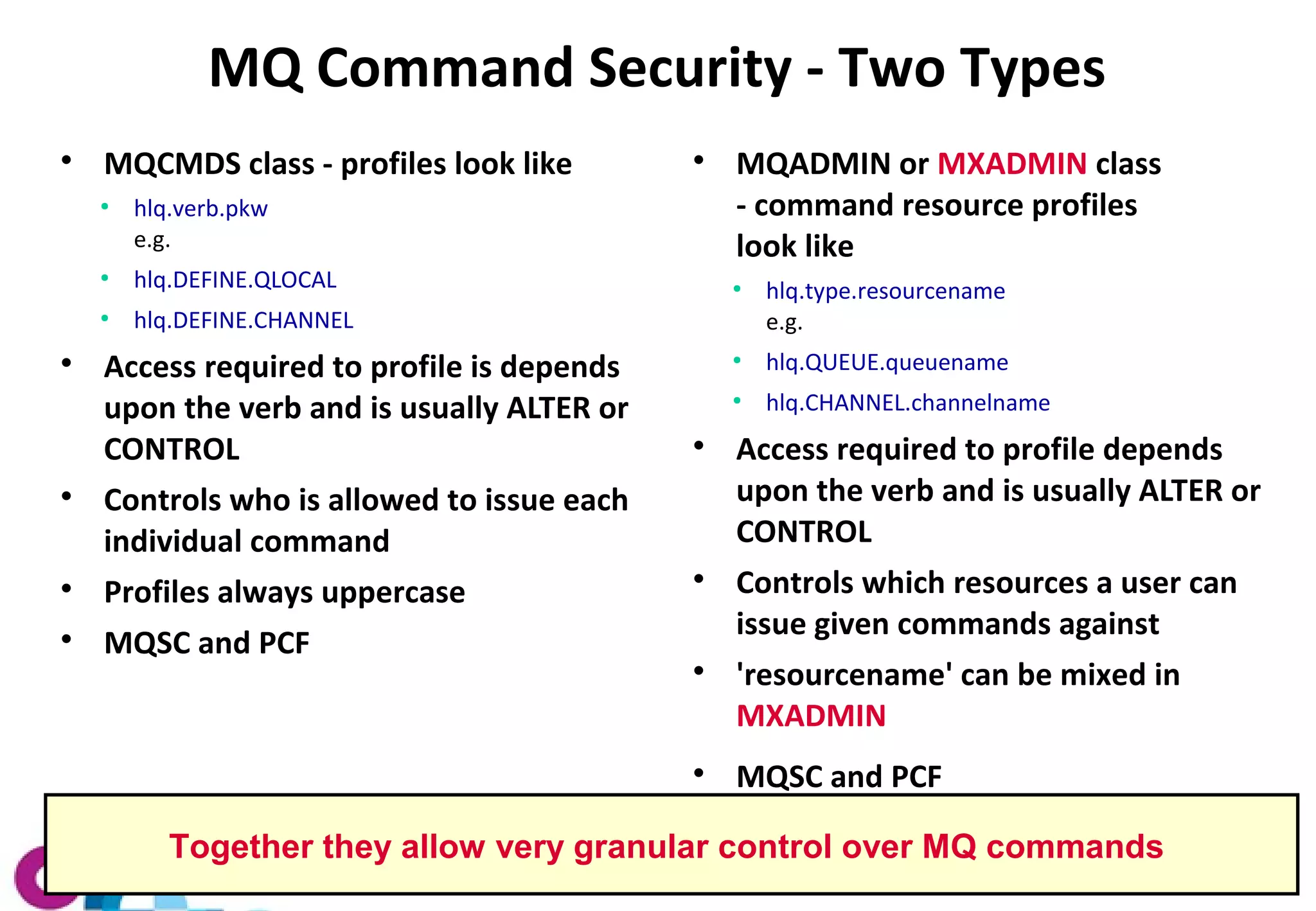
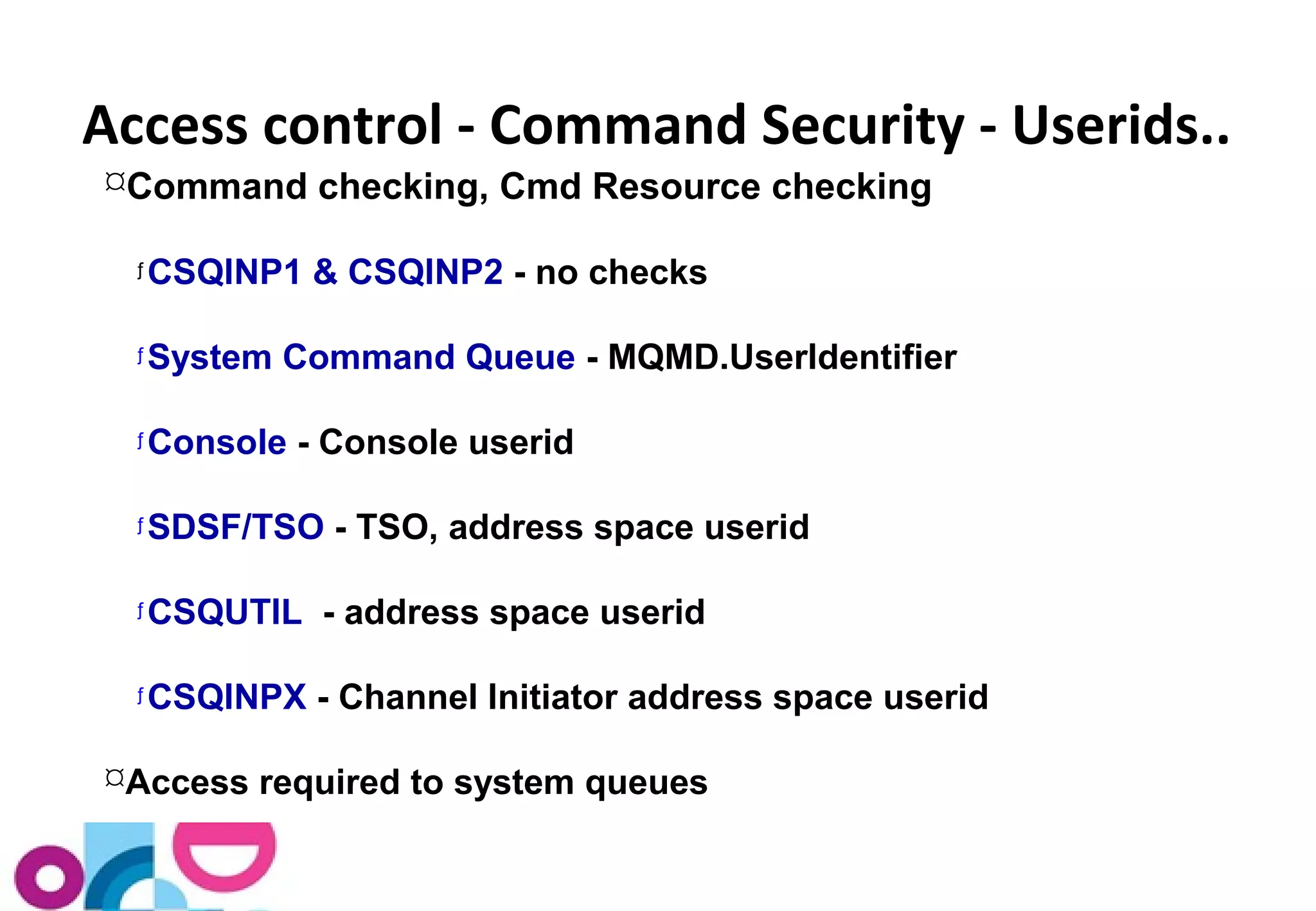
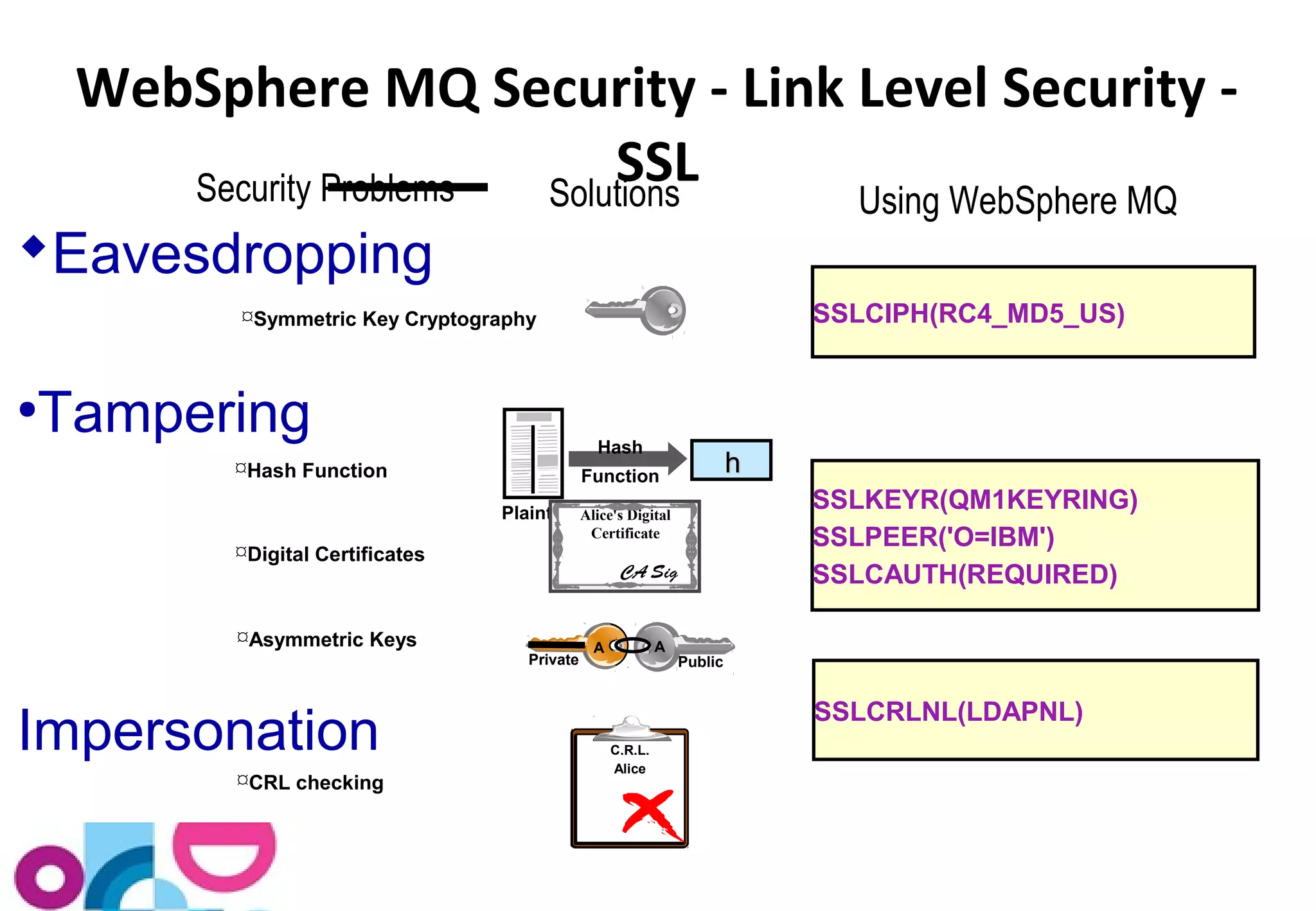
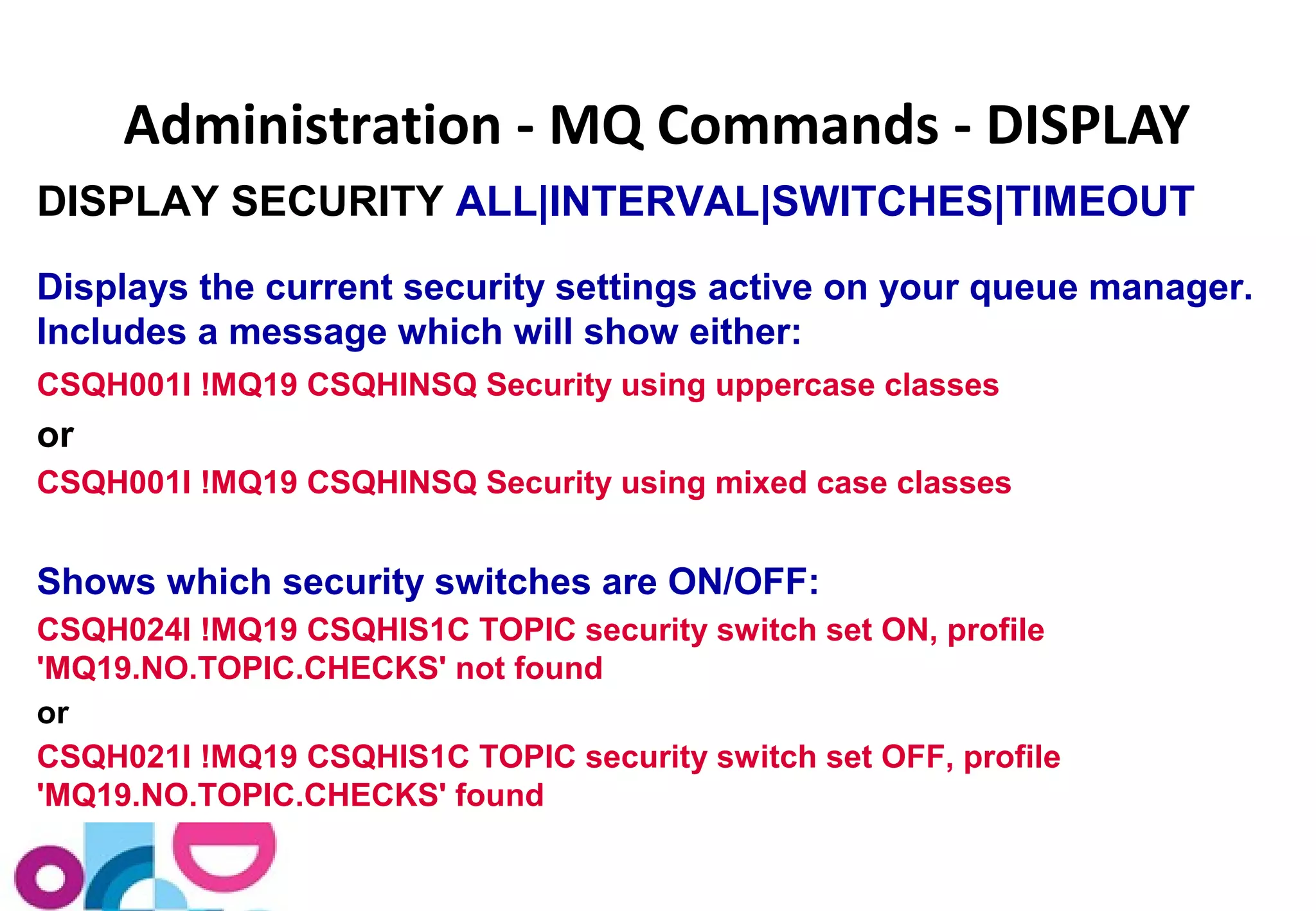
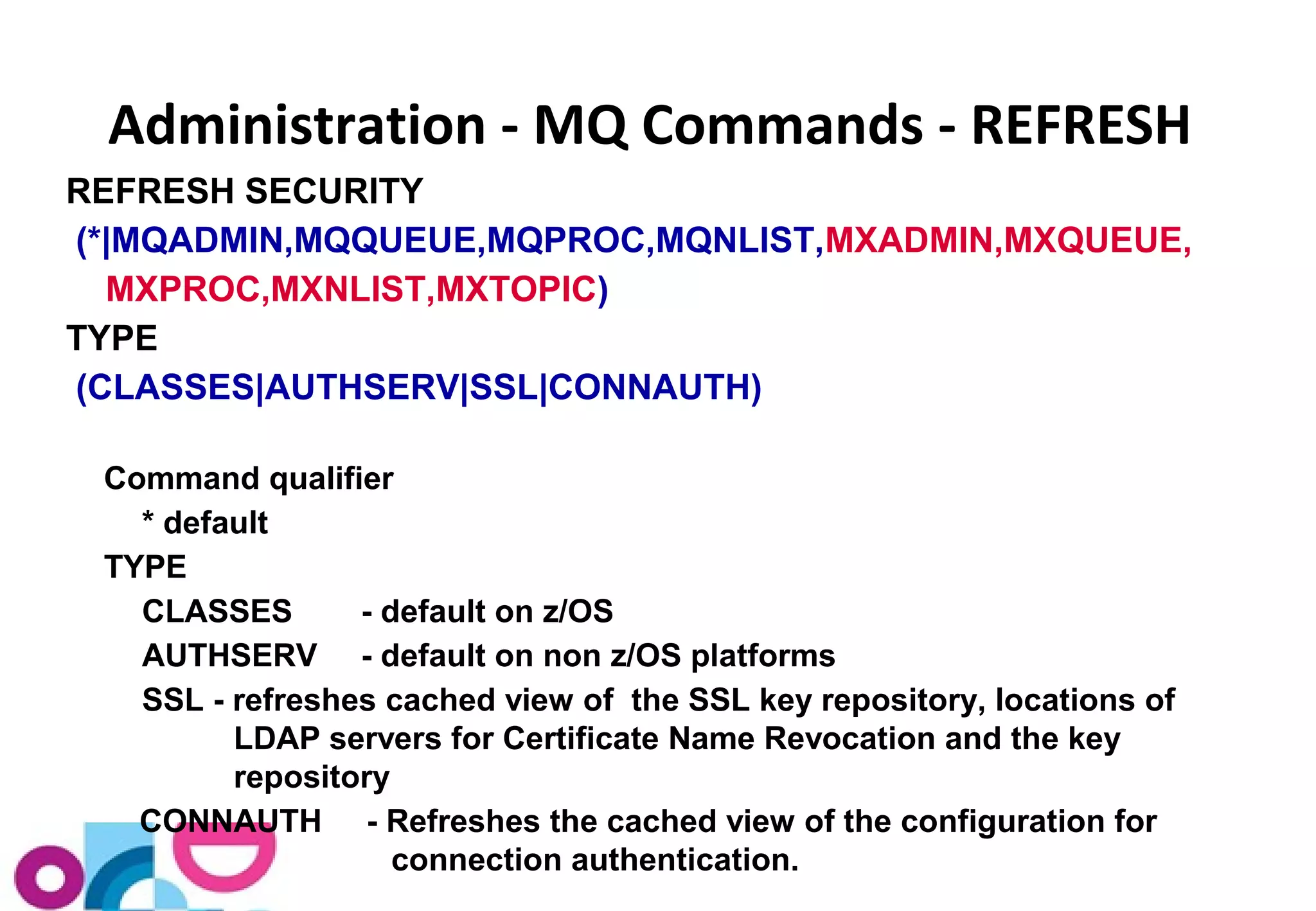
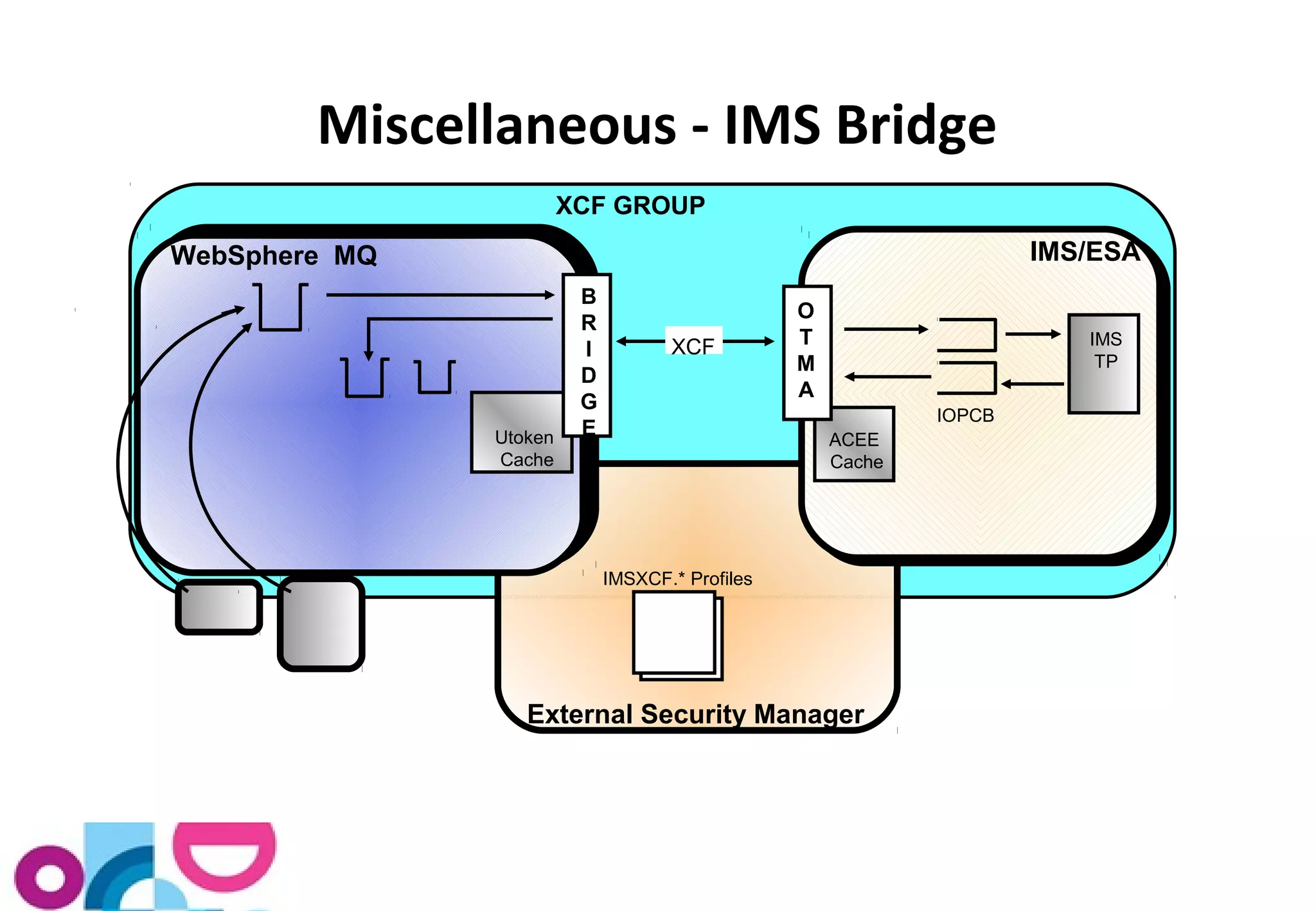
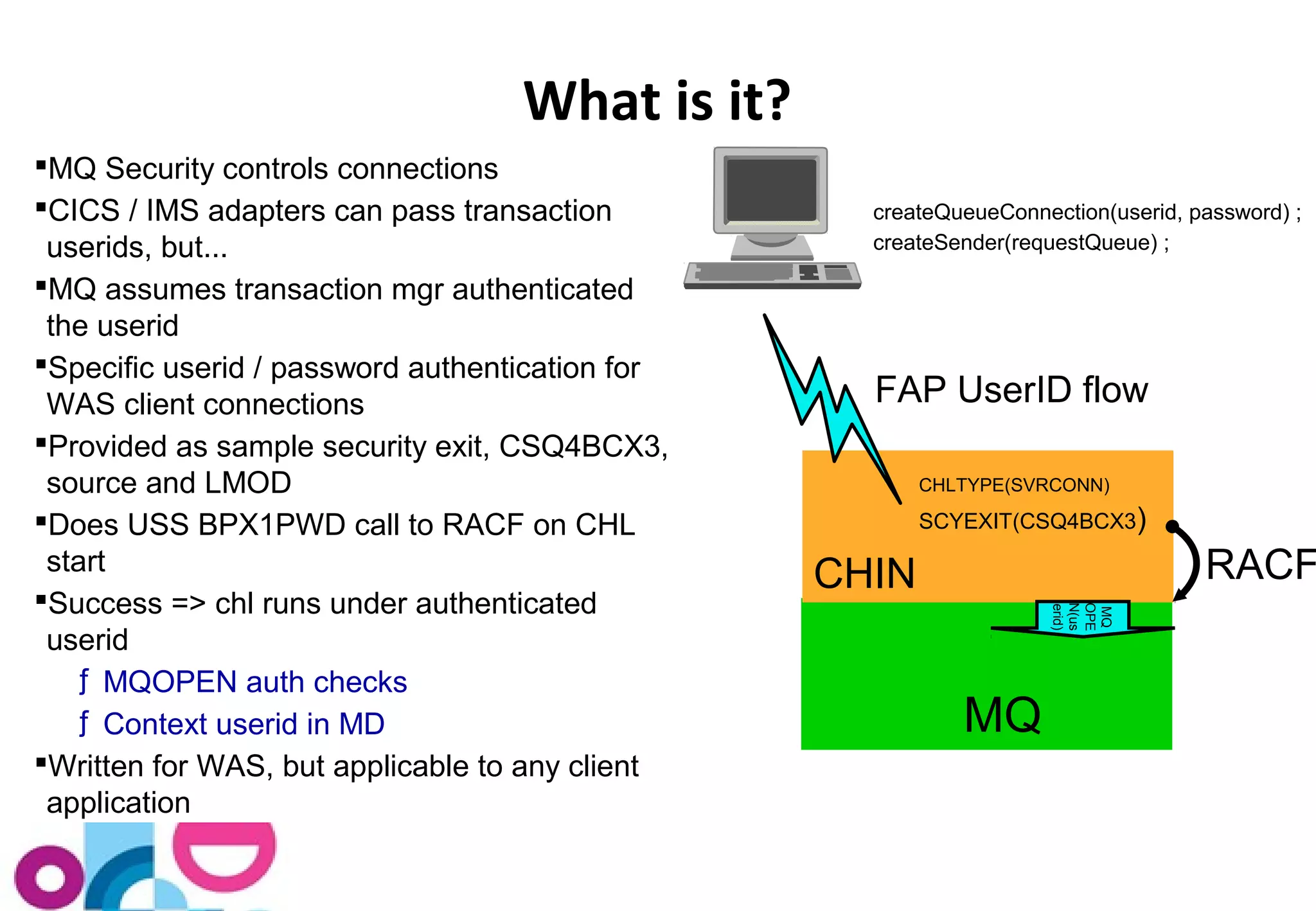
The document provides an overview of security features for WebSphere MQ on z/OS, focusing on user identification, authentication, access control, auditing, and protecting resources. It discusses the use of external security managers, detailed classes for profiles, and granular control for access management. Additionally, it outlines the characteristics of connection, API, and resource-level security, emphasizing the importance of auditing and managing security check configurations.