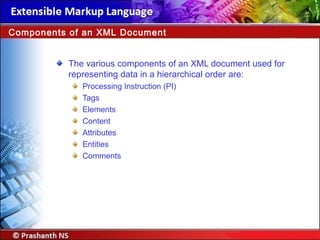
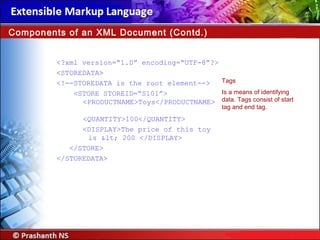
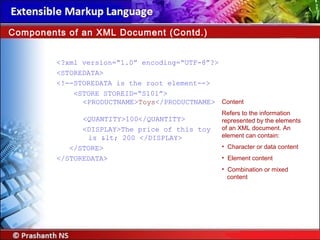
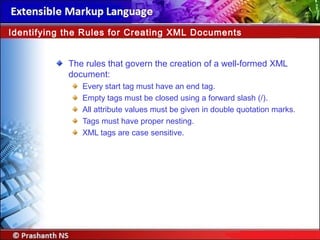
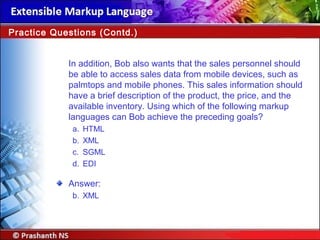
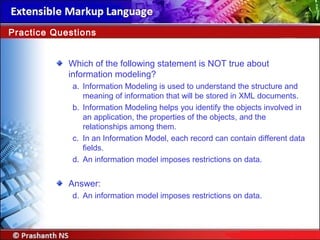
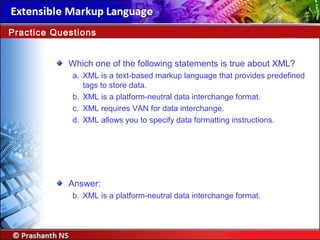
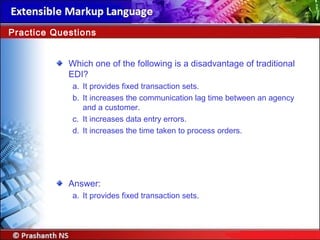
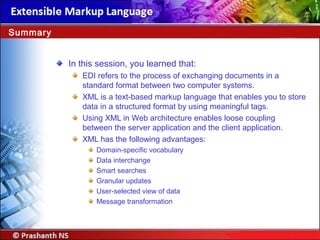
The document discusses the importance of XML as a standard format for data interchange, enabling effective communication across disparate systems and applications. It covers the fundamentals of XML, its advantages over traditional methods like EDI, and provides insights into its future use in e-commerce, B2B services, and mobile applications. Additionally, the document introduces components of XML documents, information modeling, and the process of creating well-formed XML documents.