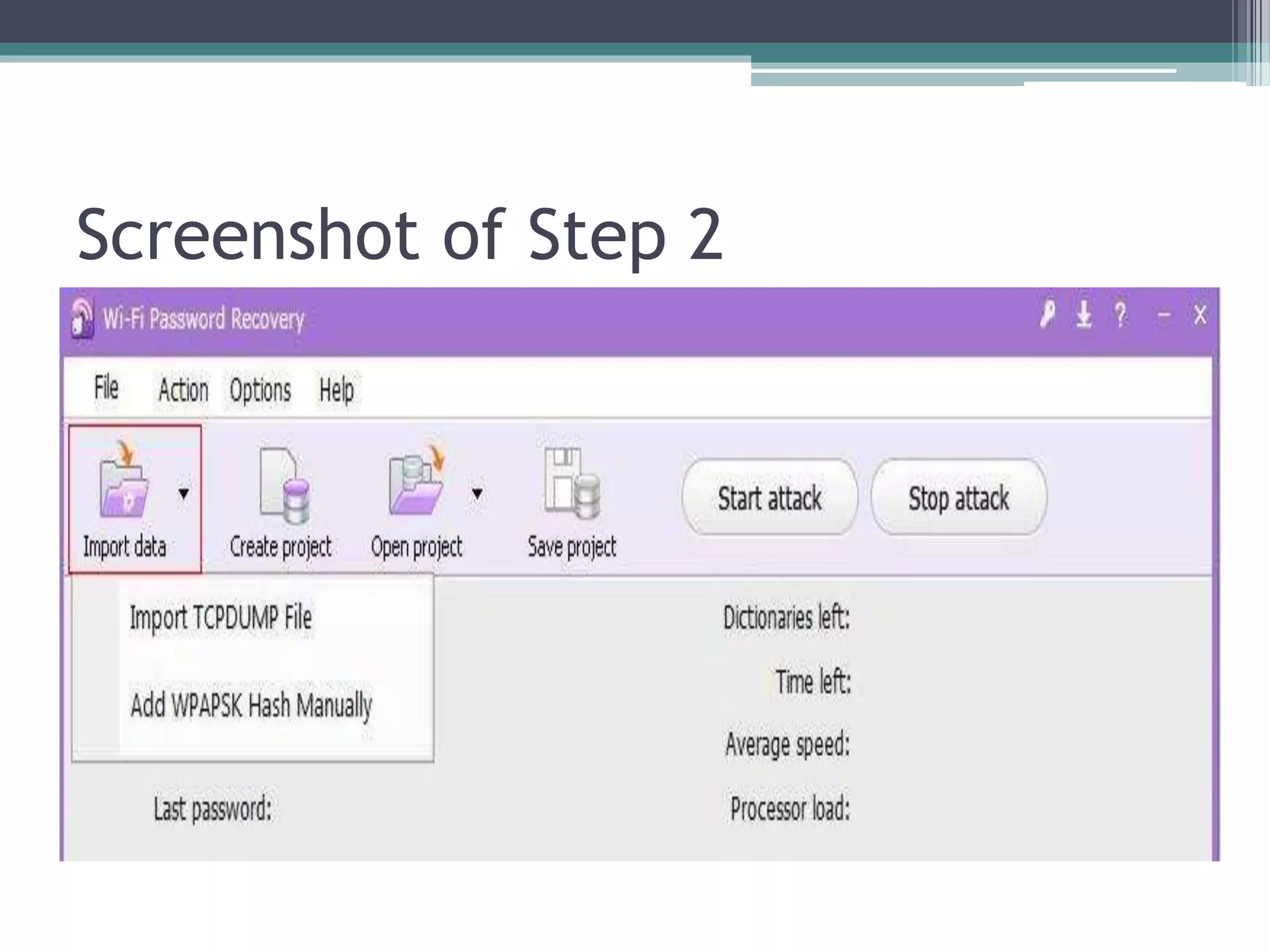
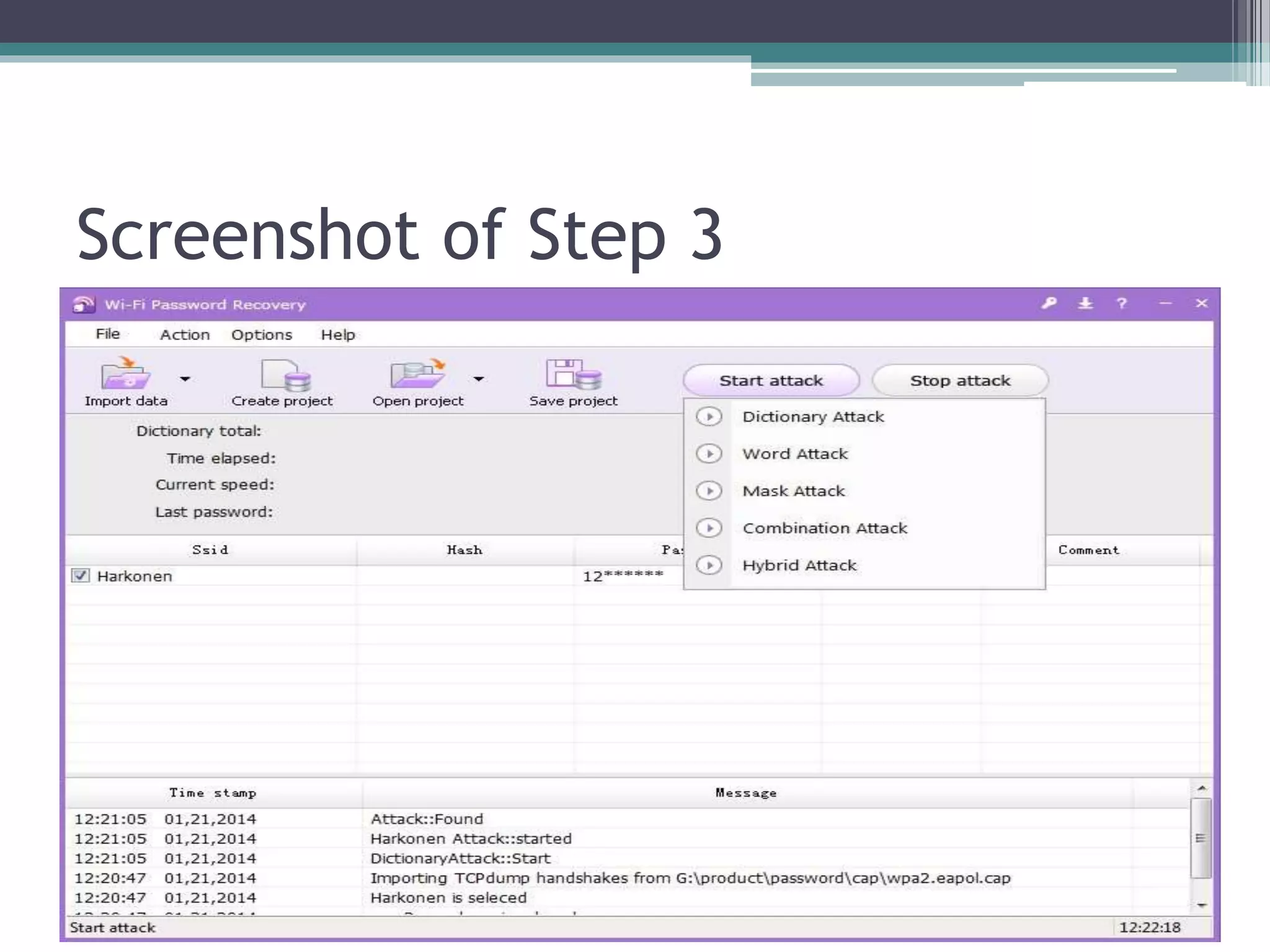
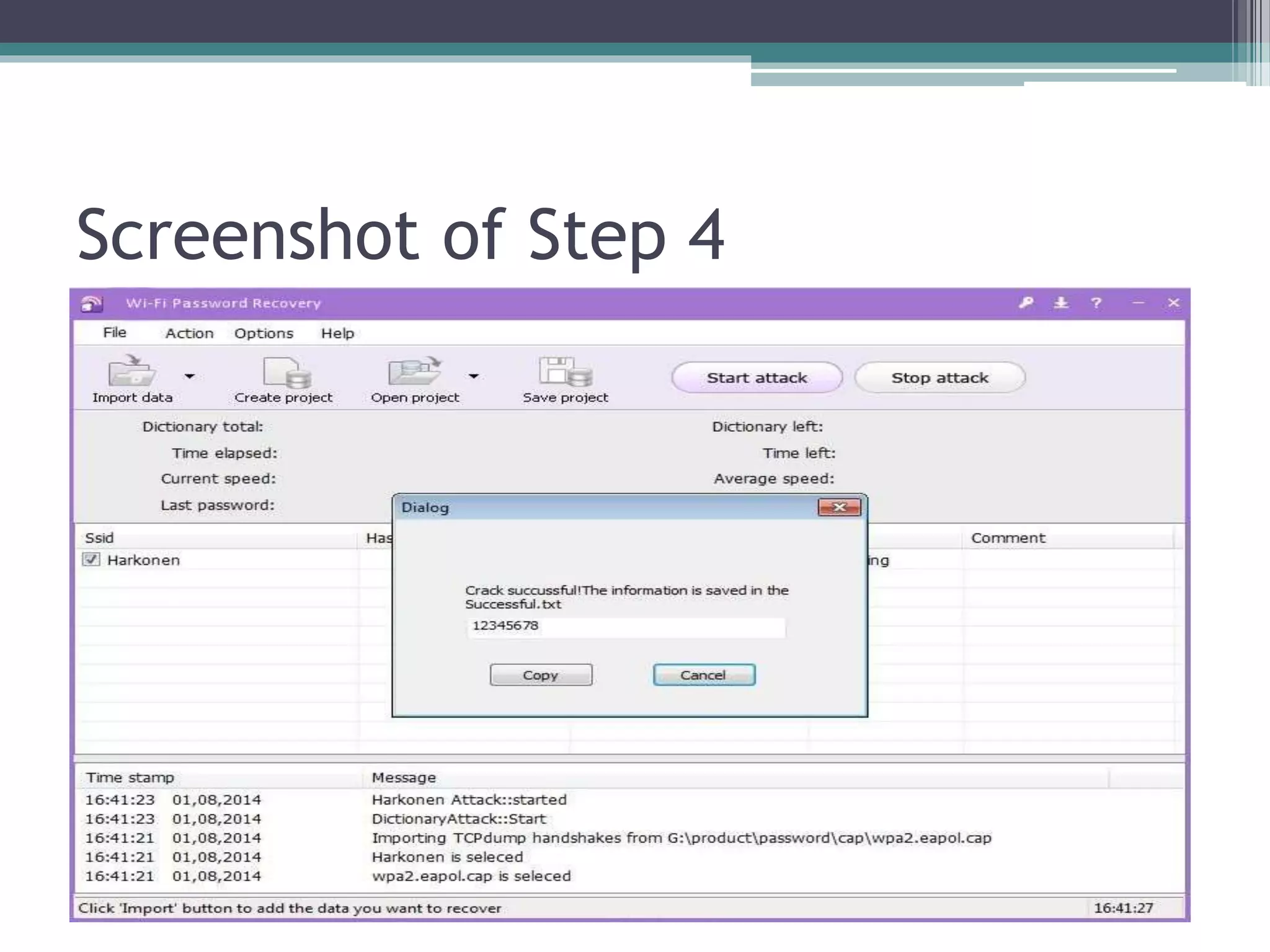
Wi-Fi password recovery is a method for regaining access to forgotten Wi-Fi passwords using various tools, such as SmartKey Wi-Fi Password Recovery, which offers multiple recovery methods without data loss. The document outlines the installation and usage steps of SmartKey, including how to load network data and initiate different attack types to retrieve the lost password. It emphasizes that the recovered password is saved in a text file for easy access.