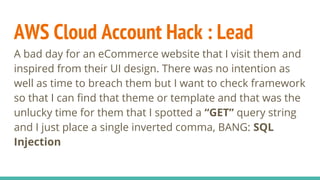
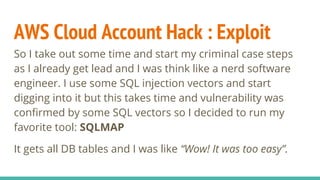
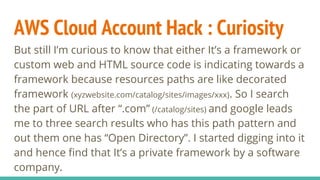
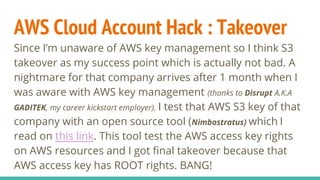
The document discusses a security breach of an AWS cloud account, detailing the author's process of discovering and exploiting vulnerabilities through SQL injection. It outlines lessons learned regarding cybersecurity practices and personal growth, emphasizing the importance of never blindly trusting frameworks and the need for proactive security measures. The author concludes by stressing that security should be viewed as an ongoing process rather than a one-time product.










![Thank You![Every opinion is solely my mindset and can be differ from others - Rational correction is highly
appreciable]
(Sorry for any english grammar or spelling mistakes)](https://image.slidesharecdn.com/awscloudaccounthacked-170409085028/85/AWS-Cloud-Account-Hacked-15-320.jpg)