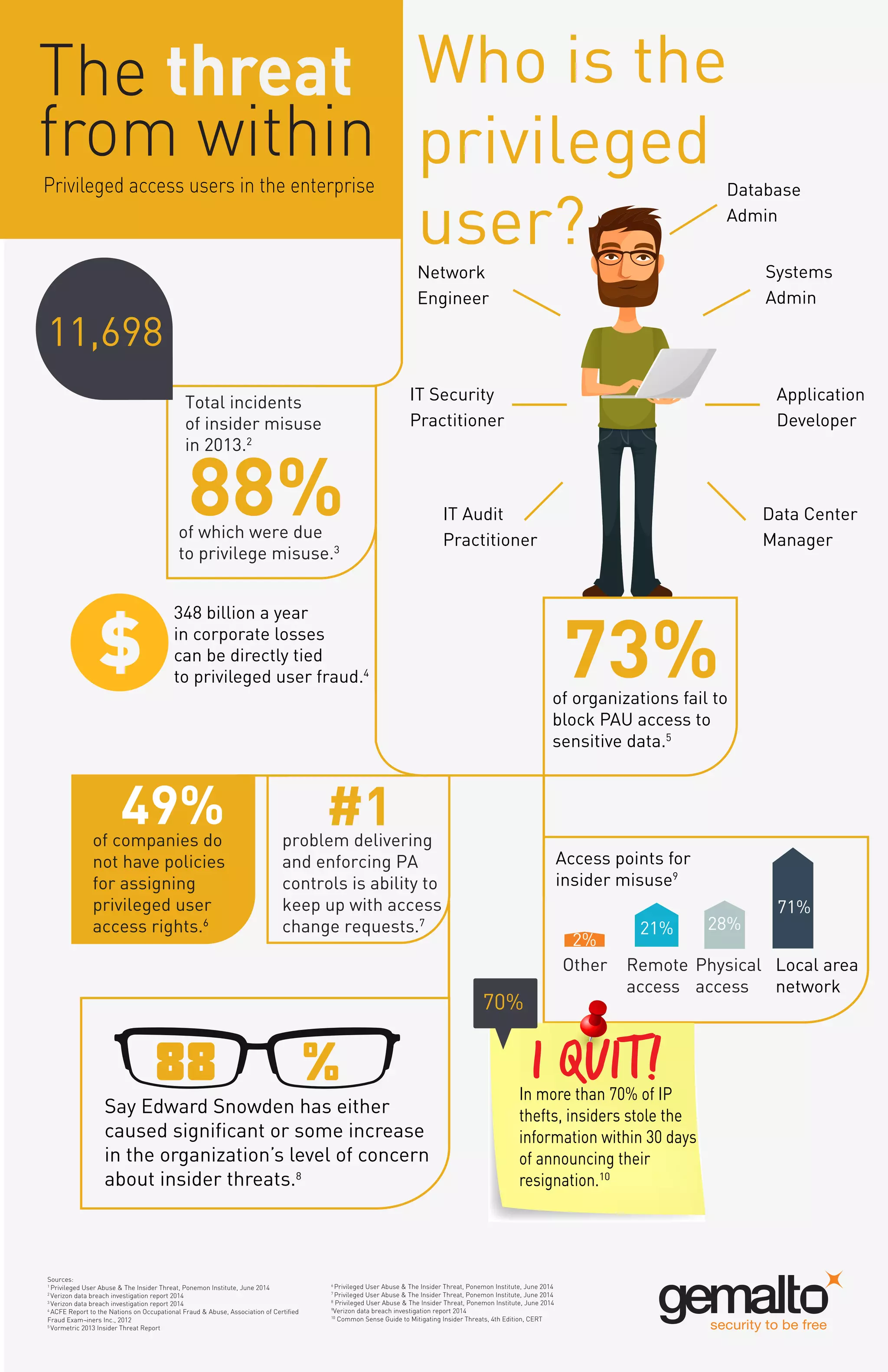
The document outlines the significant threat posed by privileged access users in enterprises, noting that 73% of organizations struggle to restrict their access to sensitive data. Insider misuse leads to an estimated $348 billion in annual losses, with a substantial percentage of organizations reporting heightened concerns post-Edward Snowden's revelations. Additionally, over 70% of intellectual property thefts occur within 30 days of an insider's resignation, highlighting the urgency for effective access controls and policies.