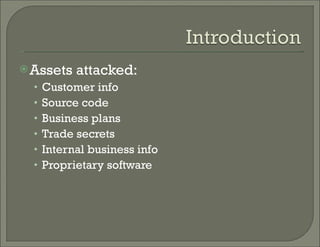
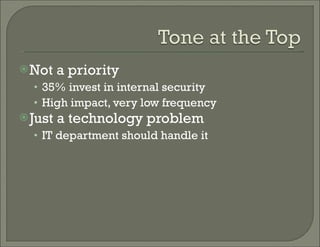
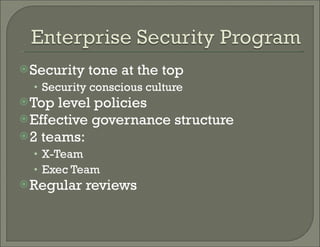
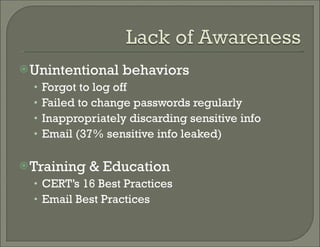
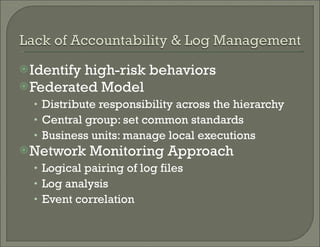
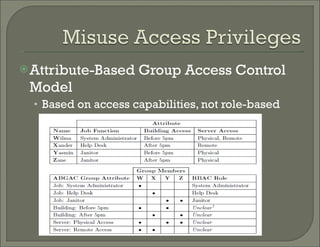
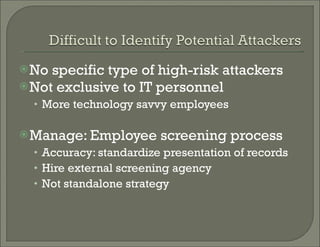
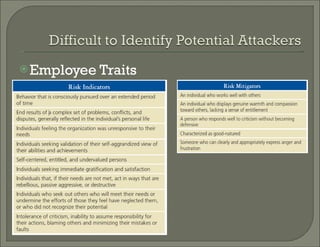
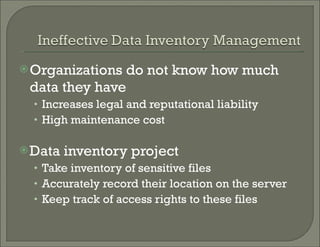
Managing insider threats is a priority for organizations. Key aspects include establishing a strong security culture from the top-down through policies and regular reviews, identifying and monitoring high-risk employee behaviors, and implementing technical controls like access monitoring and honeypot approaches. Data-centric policies and identifying where sensitive data is located and who can access it are also important strategies for mitigating insider risks.