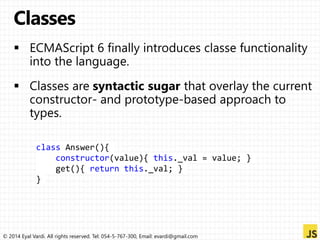
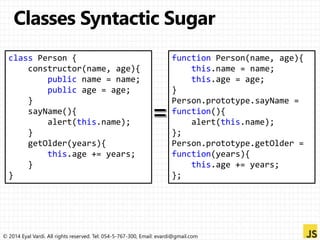
The document contains code snippets demonstrating various JavaScript language features, including: loops, closures, const, let, arrow functions, classes, modules, maps, sets, structs, and more. It is a reference guide for Eyal Vardi covering JavaScript syntax and semantics from ES5 through ES6/ES2015 standards. Each code block is preceded and followed by copyright and contact information for Eyal Vardi.
![var es = [];
for (var i = 0; i < 10; i++) {
es[i] = function () {
console.log("i = " + i);
};
}
es[6](); // i = 10
var es = [];
for (var i = 0; i < 10; i++) {
let c = i;
es[i] = function () {
console.log("i = " + c);
};
}
es[6](); // i = 6
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-9-320.jpg)
![var [start, end] = ["earth", "moon"] // initialize
console.log(start + " => " + end); // earth => moon
[start, end] = [end, start] // swapping
console.log(start + " => " + end); // moon => earth
function equinox() { return [20, "March", 2013, 11, 02]; }
var [date, month, , ,] = equinox();
console.log( date +" "+ month); // 20 March
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-14-320.jpg)

![// defining rest parameters with 3 dot syntax
function push(array, ...items) {
items.forEach(function(item) {
array.push(item);
console.log( item );
});
}
// 1 fixed + 3 variable parameters
var planets = [];
push(planets, "Mercury", "Venus", "Earth");
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-18-320.jpg)
![// Spread operator "...weblink"
function createURL (comment, path, protocol, subdomain, domain, tld)
{
// ...
}
var weblink = ["ht/w/abc.html", "http", "info", "cern", "ch"],
comment = "World's first Website";
createURL( comment, ...weblink );
Spread
operator
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-19-320.jpg)
![Array = [ value for each ( variable in values ) condition ];
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-40-320.jpg)
![//original array
var numbers = [0,1,2,3,4,5,6,7,8,9,10];
//just copy all items into a new array
var duplicate = [i for each (i in numbers)];
//get just the even numbers
var evens = [i for each (i in numbers) if (i % 2 == 0)];
//multiply every value by 2
var doubled = [i*2 for each (i in numbers)];
//multiply every odd number by 3
var tripledOdds =
[ i*3 for each (i in numbers) if ( i % 2 > 0 ) ];
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-41-320.jpg)
![let arr = [ "blue", "green" ];
arr.notAnIndex = 123;
Array.prototype.protoProp = 456;
for (k in arr) console.log(k);
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com
Print:
> 0
> 1
> notAnIndex
> protoProp](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-45-320.jpg)
![var colors = new Set(['rojo', 'amarillo', 'azul']);
colors.language = 'es'; // add an expando property
for (let name in colors)
alert(name); // "language" (the property name)
for (let word of colors)
alert(word); // "rojo", "amarillo", "azul" (the data)
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-46-320.jpg)
![import items from "@iter";
let obj = { first: "Jane", last: "Doe" };
for ( let [k,v] of items(obj) ) {
console.log( k + " = " + v );
}
Output:
first = Jane
last = Doe
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-48-320.jpg)
![Operation Intercepted as
proxy[name] handler.get(proxy, name)
proxy[name] = val handler.set(proxy, name, val)
name in proxy handler.has(name)
delete proxy[name] handler.delete(name)
for (var name in proxy) {...} handler.iterate()
Object.keys(proxy) handler.keys()
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-62-320.jpg)
![getOwnPropertyDescriptor:
function(name) -> PropertyDescriptor | undefined
getPropertyDescriptor:
function(name) -> PropertyDescriptor | undefined
getOwnPropertyNames: function() -> [ string ]
getPropertyNames: function() -> [ string ]
defineProperty: function(name, propertyDescriptor) -> any
delete: function(name) -> boolean
fix: function() -> { string: PropertyDescriptor } | undefined
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-63-320.jpg)
![has: function(name) -> boolean
hasOwn: function(name) -> boolean
get: function(receiver, name) -> any
set: function(receiver, name, val) -> boolean
enumerate: function() -> [string]
keys: function() -> [string]
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-65-320.jpg)
![function makeSimpleProfiler(target) {
var count = Object.create(null);
return Proxy.create( target, {
get: function ( receiver , name) {
count[name] = (count[name] || 0) + 1;
return target[name];
},
stats: function () { return count; }
});
}
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-66-320.jpg)
![var Stack = (function() {
var stack = [],
allowed = ["push", "pop", "length"];
return Proxy.create({
get: function(receiver, name) {
if (allowed.indexOf(name) > -1) {
if (typeof stack[name] == "function") {
return stack[name].bind(stack);
} else {
return stack[name];
}
} else {
return undefined;
}
}
});
});
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-67-320.jpg)
![Proxy.createFunction( handler, callTrap, constructTrap );
// proxy() -> callTrap
// new proxy() -> constructTrap | callTrap
var fp = Proxy.createFunction({}, callTrap);
var o = { name: fp };
o.name(x); // reified as callTrap.apply(o,[x])
© 2014 Eyal Vardi. All rights reserved. Tel: 054-5-767-300, Email: evardi@gmail.com](https://image.slidesharecdn.com/es6-130915015644-phpapp02/85/What-s-new-in-ECMAScript-6-0-68-320.jpg)