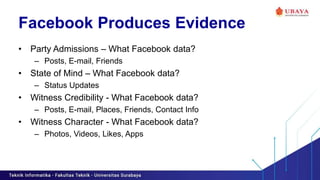
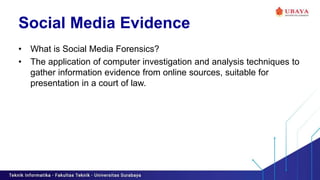
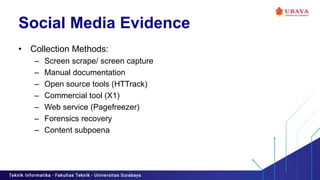
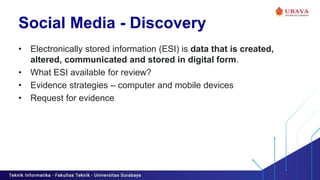
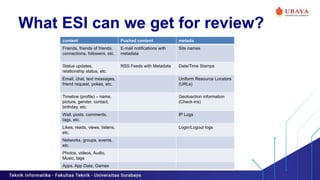
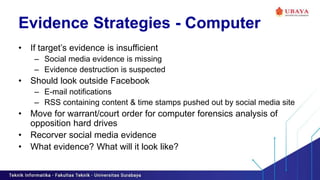
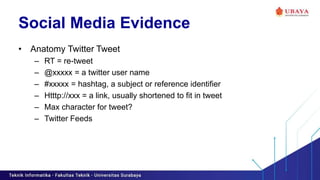
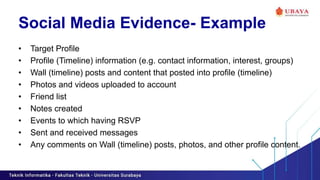
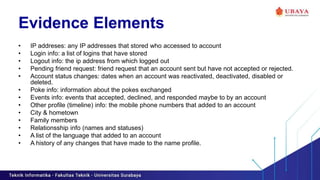
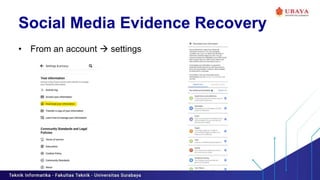
This document discusses social media forensics and the use of social media evidence. It explains that social media evidence, such as posts, messages, photos and location data from platforms like Facebook, Twitter and LinkedIn, can be collected and analyzed for use in investigations and legal cases. The document outlines methods for collecting, preserving and requesting social media evidence and provides examples of the types of information that can be obtained, such as IP addresses, login/logout times, and location history. It also discusses how automatic sharing settings and graph search tools can produce unintended evidence from a user's online activities and presence.