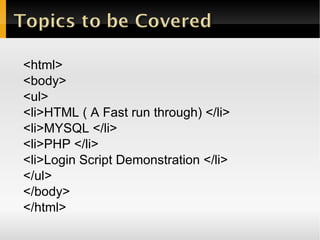
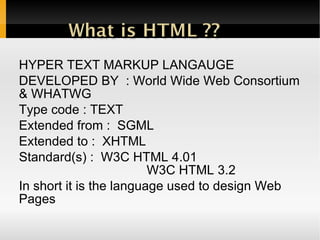
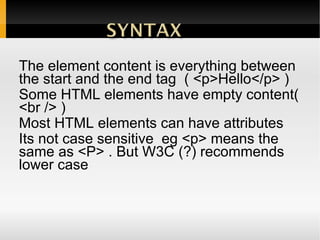
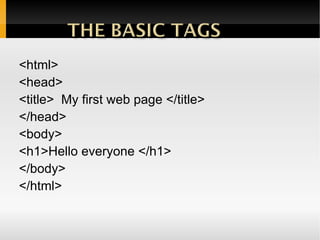
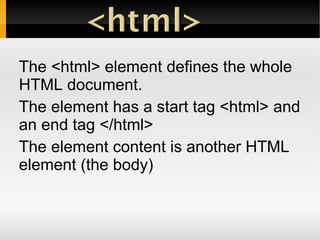
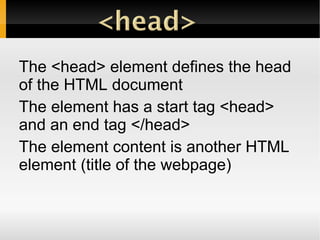
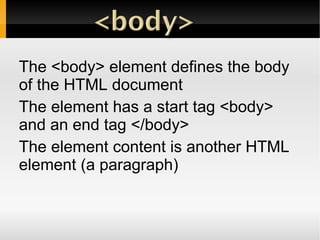
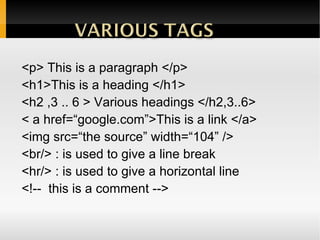
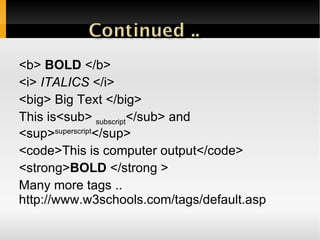
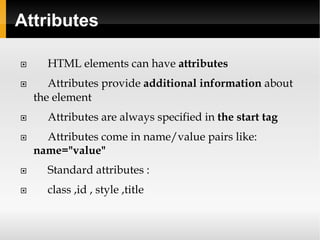
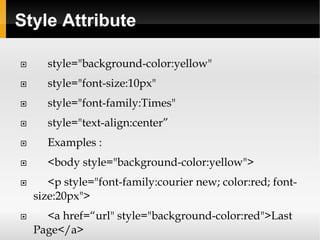
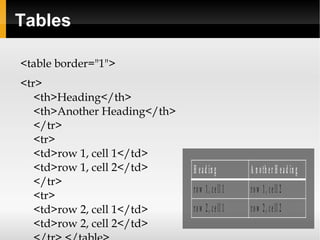
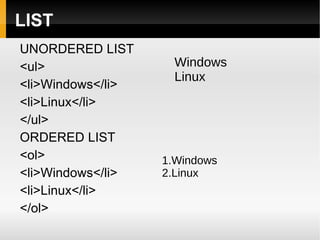
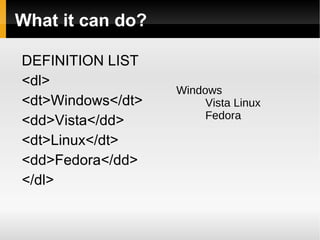
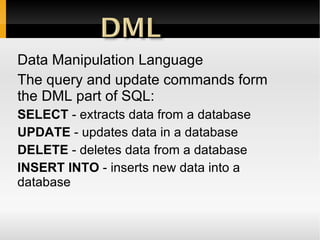
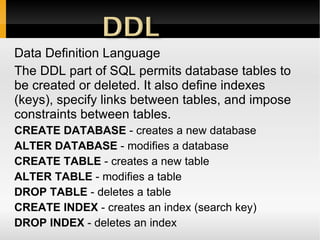
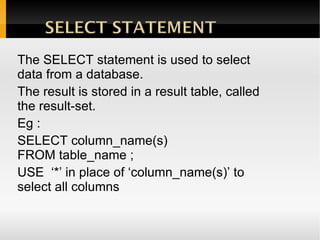
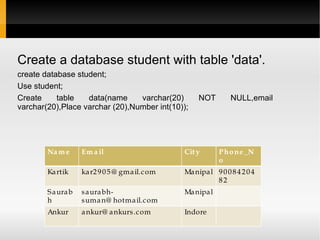
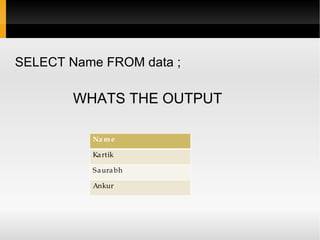
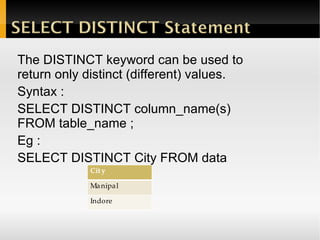
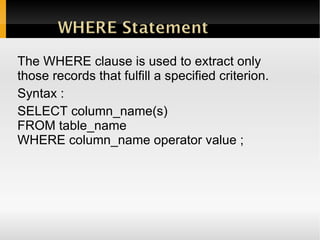
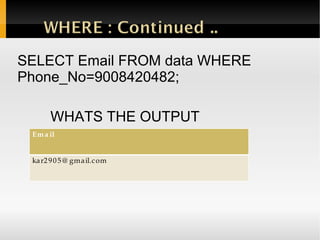
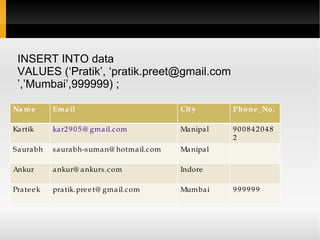
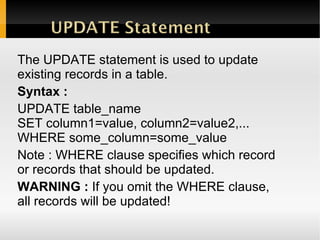
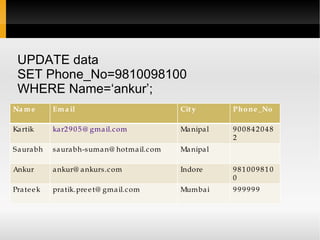
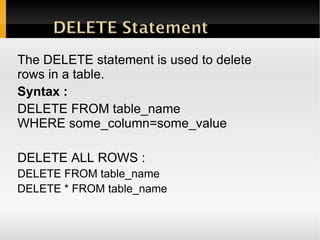
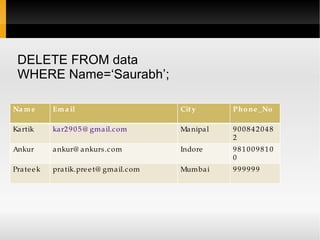
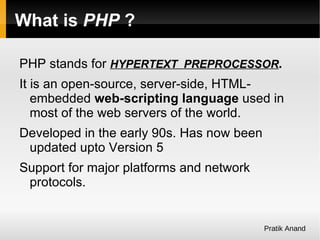
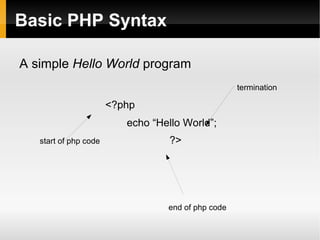
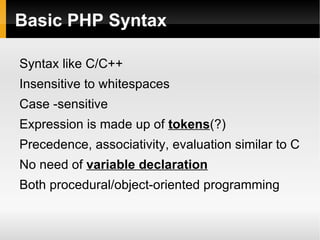
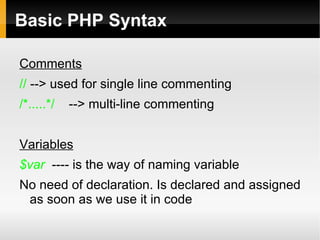
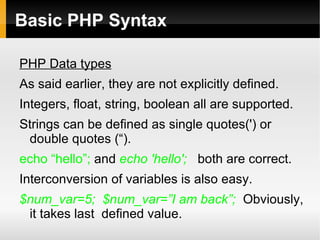
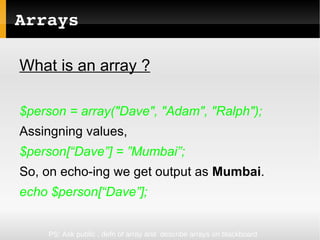
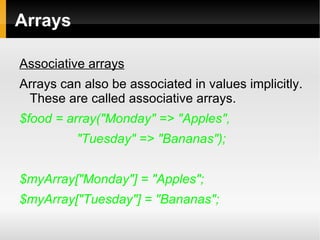
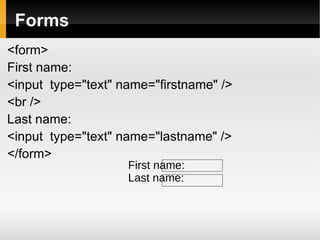
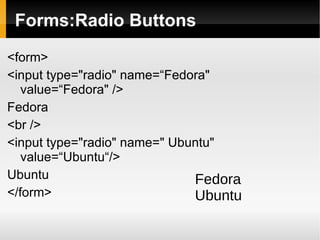
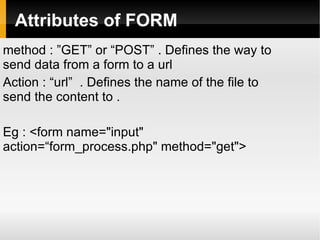
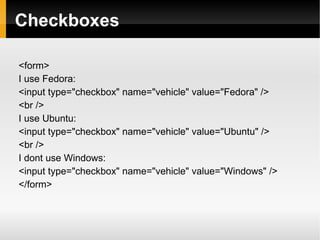
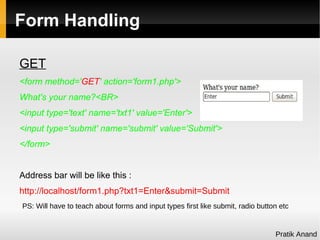
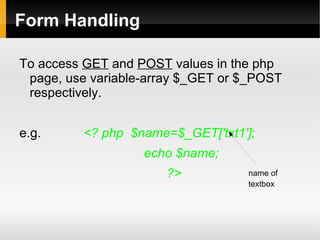
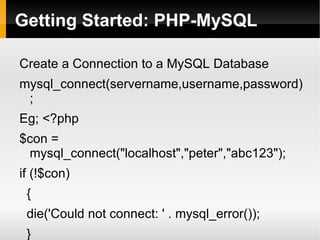
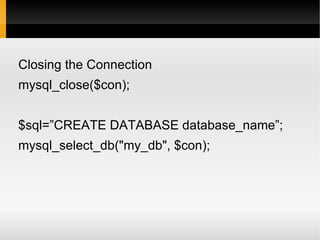
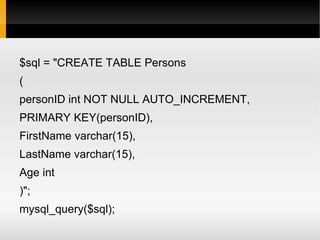
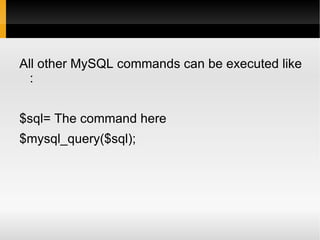
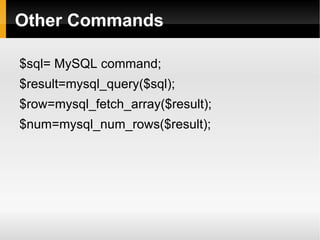
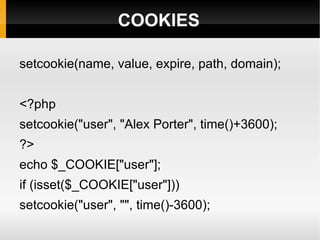
This document provides an overview of web development technologies including HTML, CSS, PHP, MySQL, and forms. It includes brief introductions and code snippets for each topic. Key points covered are basic HTML tags and structure, CSS styling, SQL commands for managing a MySQL database, PHP syntax and functions, and using forms to pass data between pages. Contact information is also provided for three web developers.