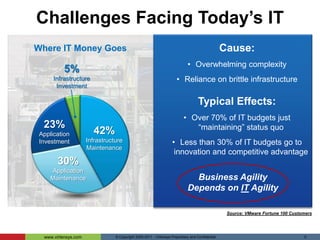
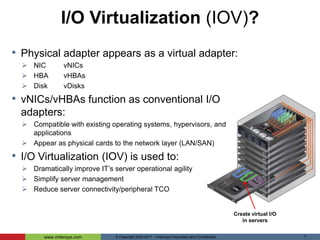
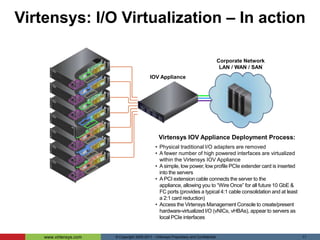
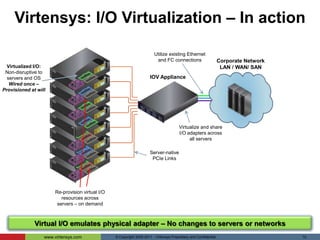
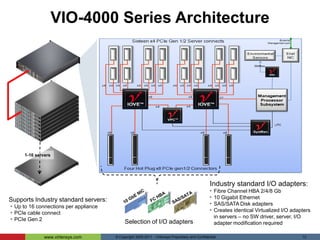
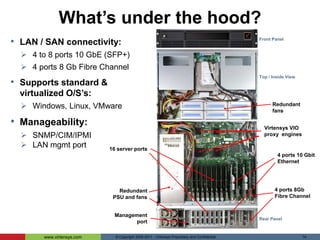
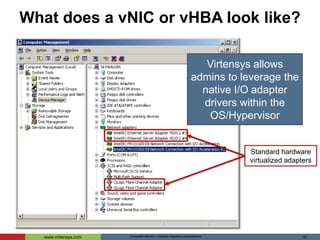
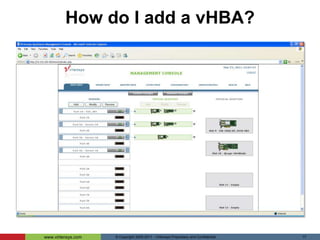
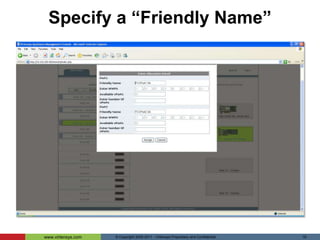
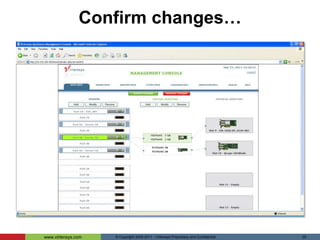
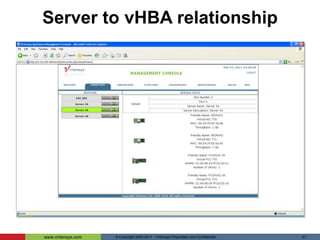
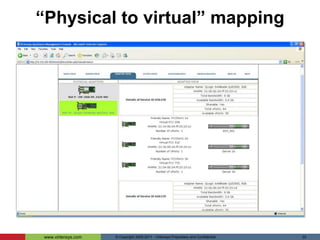
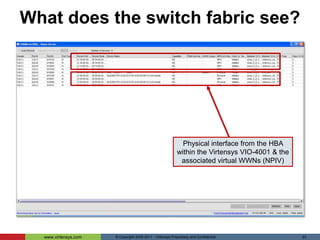
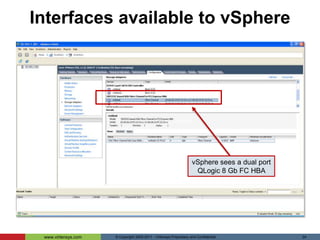
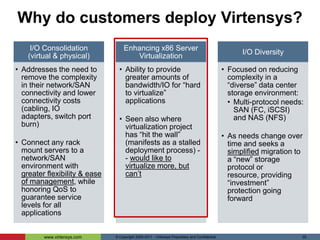
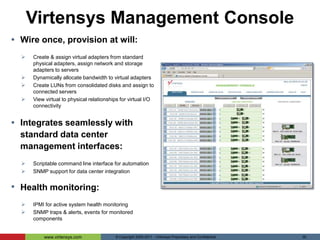
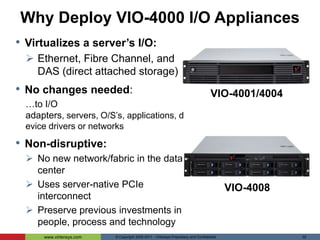
Virtensys provides I/O virtualization appliances that simplify server connectivity and management. Their appliances consolidate physical networking and storage adapters into shared pools of virtual I/O resources. This allows datacenter administrators to easily provision and reallocate virtual network interface cards and host bus adapters across multiple servers from a centralized management console. Customers benefit from reduced complexity, costs, and time spent on routine I/O provisioning and management tasks.