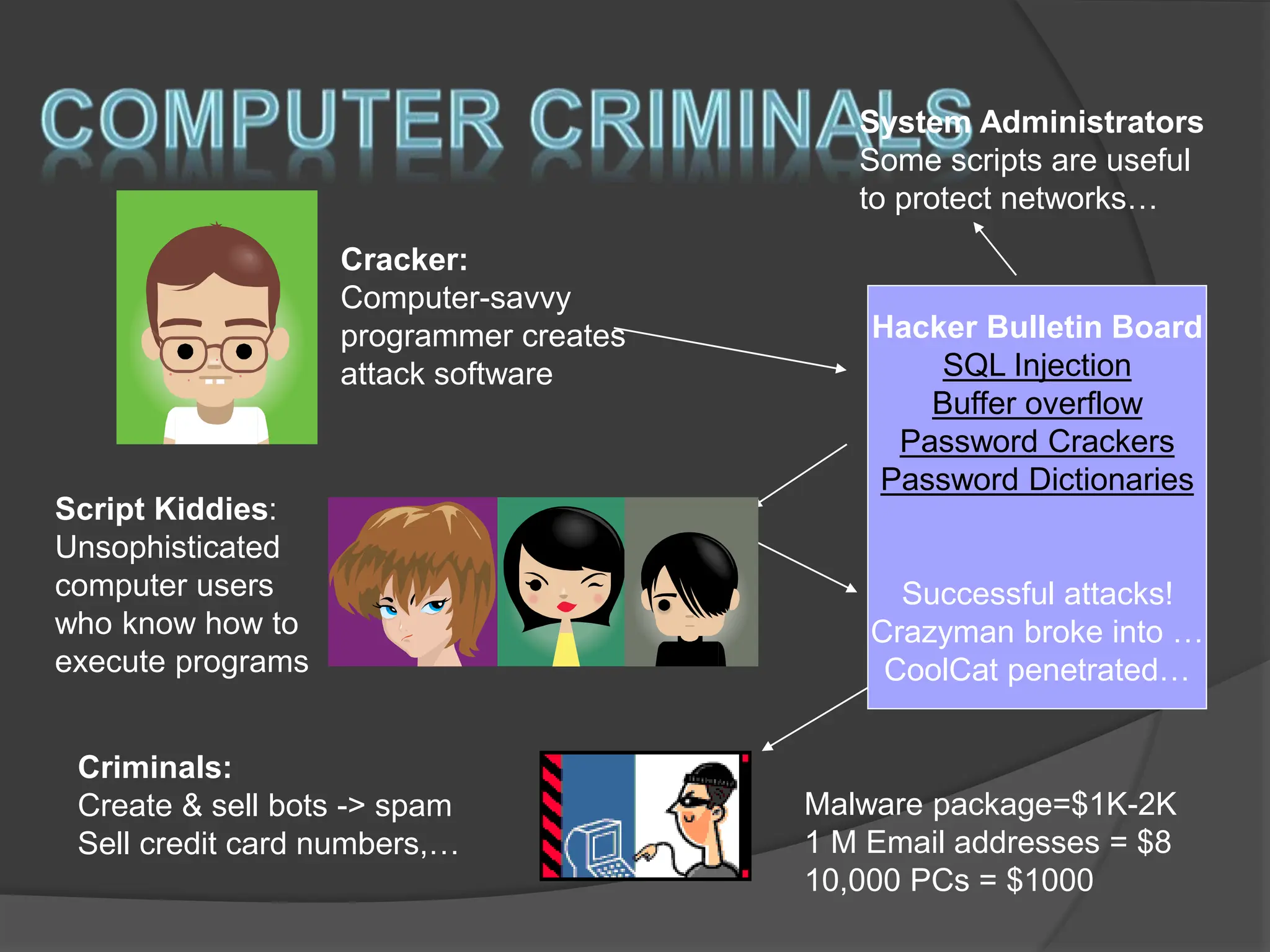
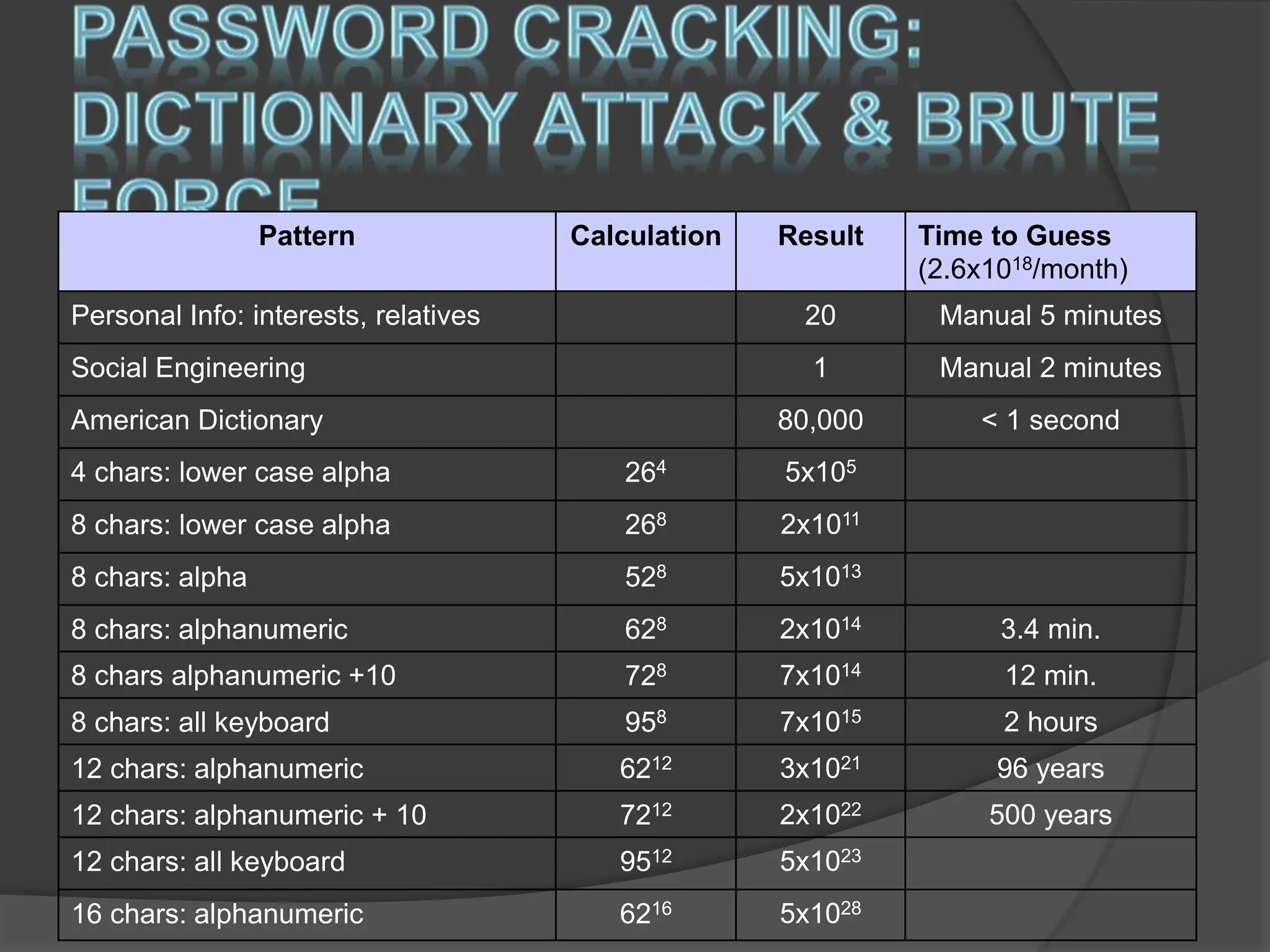
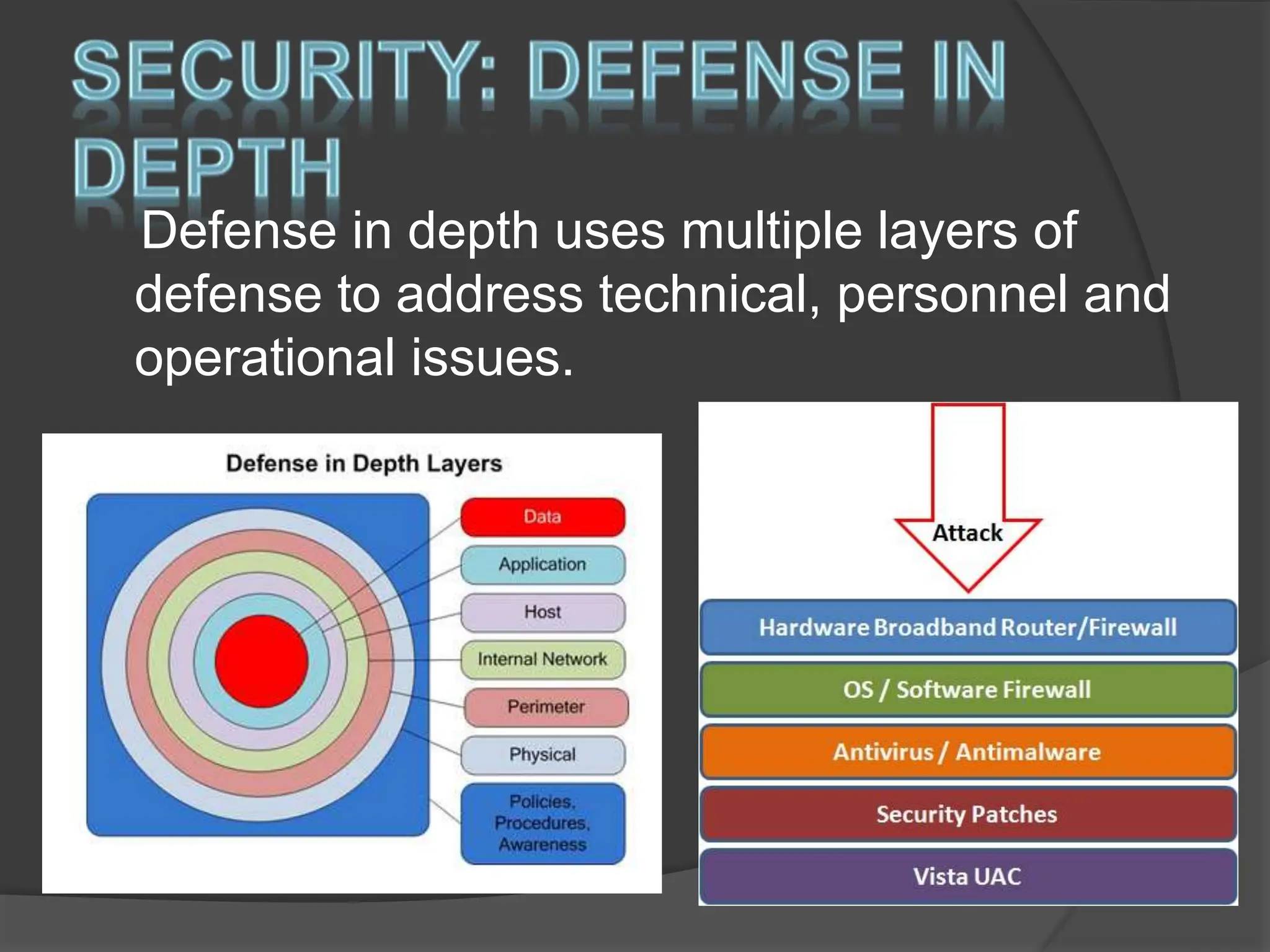
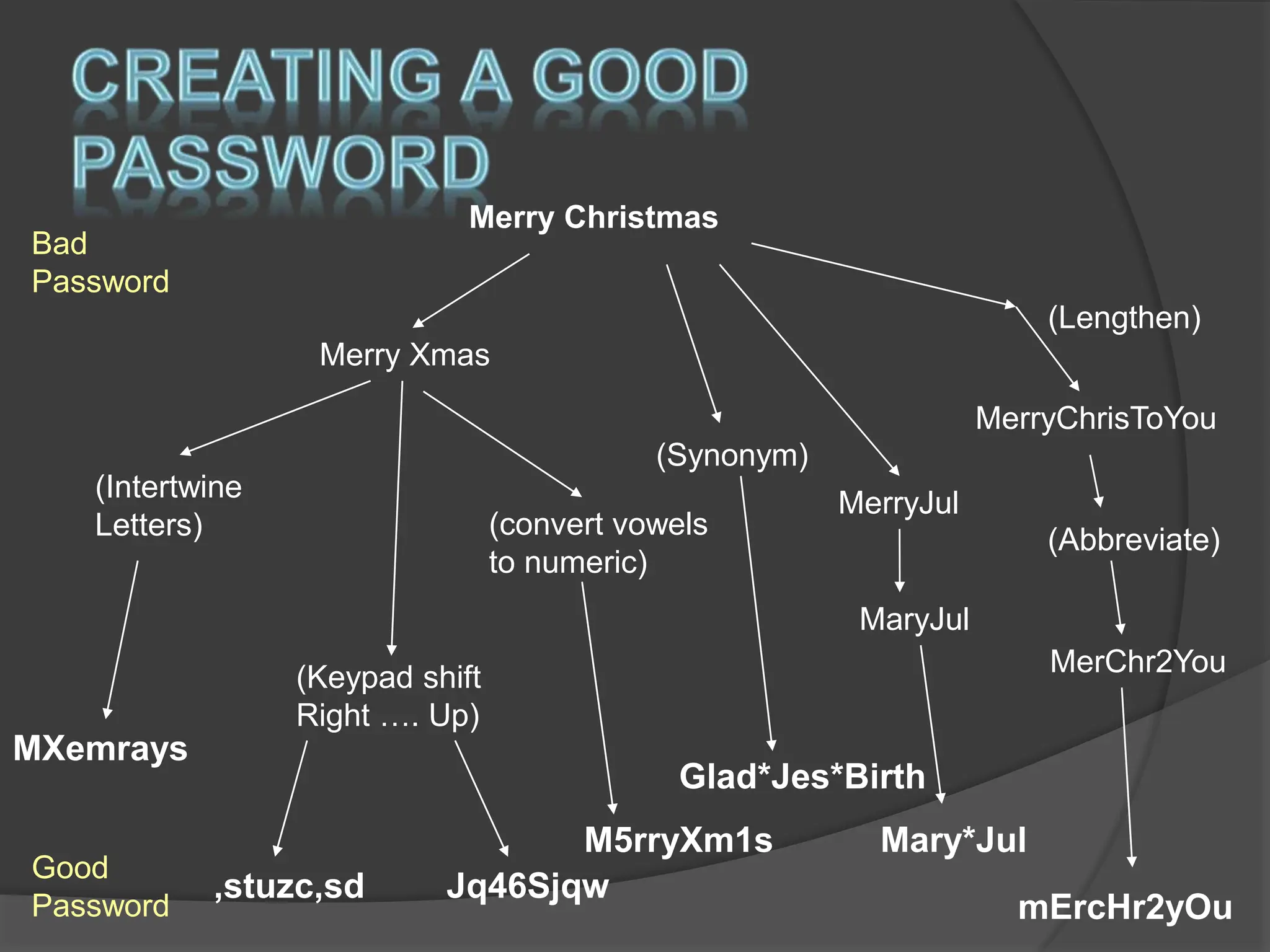
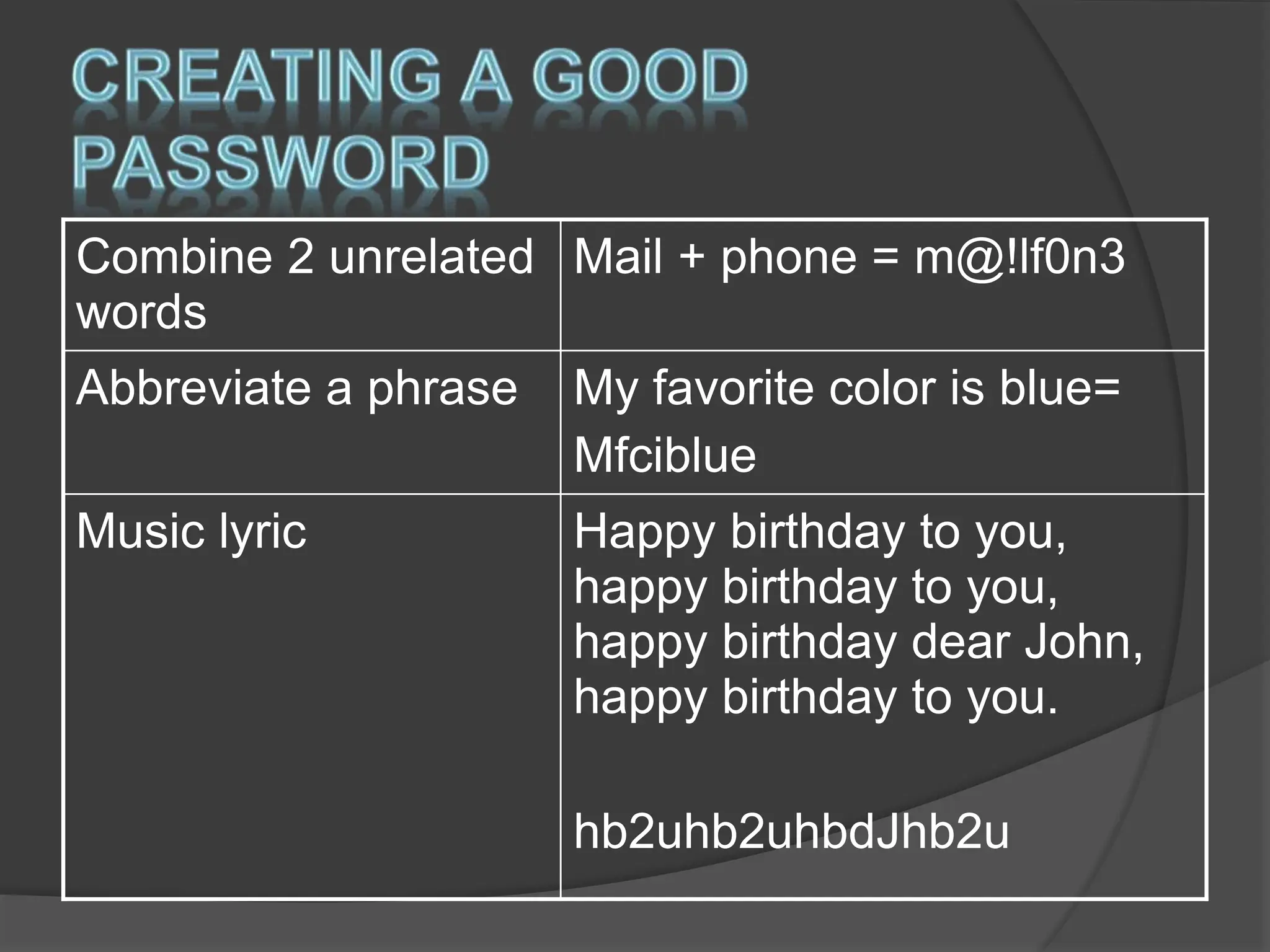
User awareness and security practices are important due to the risks posed by poor security knowledge and attacks from anywhere in the world via the internet. The top vulnerabilities exploited by cyber criminals include web browsers, IM clients, web applications, and excessive user rights. Maintaining updated anti-virus software, using strong and unique passwords, avoiding suspicious emails and attachments, and practicing good cyber hygiene can help protect users from common security risks. Organizations should implement defense in depth with multiple layers of security to address technical, personnel, and operational issues.