Untitled document.pdf
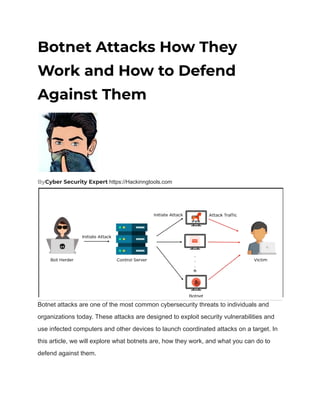
- 1. Botnet Attacks How They Work and How to Defend Against Them ByCyber Security Expert https://Hackinngtools.com Botnet attacks are one of the most common cybersecurity threats to individuals and organizations today. These attacks are designed to exploit security vulnerabilities and use infected computers and other devices to launch coordinated attacks on a target. In this article, we will explore what botnets are, how they work, and what you can do to defend against them.
- 2. Table of Contents 1. Introduction 2. What is a Botnet? 3. How Botnets Work 4. Types of Botnets 1. IRC Botnets 2. HTTP-Based Botnets 3. P2P Botnets 4. Zombie Botnets 5. Common Uses of Botnets 6. How to Detect a Botnet 7. How to Defend Against Botnets 1. Keep Your Software Up-to-Date 2. Install Antivirus and Anti-Malware Software 3. Use Strong Passwords and Two-Factor Authentication 4. Educate Yourself and Your Staff 5. Use Network Segmentation and Firewall Rules 6. Monitor Your Network for Unusual Activity 8. Conclusion 9. FAQs Introduction Botnets are networks of infected computers, servers, and other devices that are controlled by cybercriminals to carry out a variety of malicious activities. These activities can range from sending spam emails and launching DDoS attacks to stealing sensitive data and spreading malware. Botnets are highly organized and can consist of hundreds or even thousands of infected devices. They are often used to launch attacks on large organizations, but individuals can also be targeted. In this article, we will look at how botnets work, the different types of botnets, and what you can do to defend against them.
- 3. What is a Botnet? A botnet is a network of computers, servers, and other internet-connected devices that have been infected with malware. Once infected, these devices can be controlled by the botnet operator, who can use them to carry out a variety of malicious activities. Botnets are created using a variety of techniques, including exploiting security vulnerabilities in software and tricking users into downloading malware. How Botnets Work Botnets are controlled by a command and control (C&C) server, which is used by the botnet operator to send instructions to the infected devices. These instructions can range from sending spam emails to launching DDoS attacks on a target. The infected devices in a botnet are known as bots, zombies, or drones. These devices are typically compromised without the knowledge of the owner and can be controlled remotely by the botnet operator. Botnets can also use a peer-to-peer (P2P) architecture, where infected devices communicate with each other instead of relying on a central C&C server. This makes it more difficult to shut down the botnet, as there is no central point of control. Types of Botnets There are several types of botnets, including: 1. IRC Botnets IRC botnets use internet relay chat (IRC) channels to communicate with the infected devices. The botnet operator can issue commands through the IRC channel, which are then carried out by the infected devices.
- 4. 2. HTTP-Based Botnets HTTP-based botnets use HTTP requests to communicate with the infected devices. The botnet operator can issue commands through a website or web application, which are then carried out by the infected devices. 3. P2P Botnets P2P botnets use a peer-to-peer architecture to communicate with the infected devices. The infected devices communicate with each other to share information and carry out instructions from the botnet operator. 4. Zombie Botnets Zombie botnets are a type of botnet that can be created by exploiting security vulnerabilities in internet-connected devices, such as routers and IoT devices. Once infected, these devices can be used to carry out a variety of malicious activities, including DDoS attacks, spam campaigns, and data theft. Common Uses of Botnets ● Launching DDoS attacks: Botnets can be used to launch distributed denial-of-service (DDoS) attacks, which overwhelm a target server or network with traffic and cause it to crash. ● Sending spam emails: Botnets can be used to send large volumes of spam emails, which can be used to spread malware or phishing attacks. ● Stealing sensitive data: Botnets can be used to steal sensitive data, such as login credentials, credit card numbers, and personal information. ● Spreading malware: Botnets can be used to spread malware, such as viruses, worms, and Trojans. How to Detect a Botnet
- 5. Detecting a botnet can be difficult, as the infected devices are often controlled remotely and can appear to be functioning normally. However, there are several signs that may indicate that a device is infected with malware and part of a botnet, including: ● Unusual network activity: If you notice unusual network activity, such as a large amount of traffic coming from a specific device, it may be a sign that the device is part of a botnet. ● Slow performance: If a device is infected with malware, it may slow down or crash frequently. ● Unusual programs or files: If you notice unusual programs or files on a device, it may be a sign that it is infected with malware. How to Defend Against Botnets Defending against botnets requires a multi-layered approach, which includes the following steps 1. Keep Your Software Up-to-Date Keeping your software up-to-date is one of the most effective ways to defend against botnets. 2. Install Antivirus and Anti-Malware Software Installing antivirus and anti-malware software can help detect and remove malware from your devices. Make sure to keep your antivirus software up-to-date and scan your devices regularly. 3. Use Strong Passwords and Two-Factor Authentication
- 6. Using strong passwords and two-factor authentication can help prevent unauthorized access to your devices and accounts. Make sure to use unique passwords for each account and enable two-factor authentication whenever possible. 4. Educate Yourself and Your Staff Educating yourself and your staff on how to identify and avoid phishing attacks and other forms of malware can help prevent infections and reduce the risk of becoming part of a botnet. 5. Use Network Segmentation and Firewall Rules Using network segmentation and firewall rules can help prevent botnets from spreading to other devices on your network. Make sure to segment your network and set up firewall rules to restrict access to certain devices and services. 6. Monitor Your Network for Unusual Activity Monitoring your network for unusual activity can help you detect botnets and other forms of malware early. Make sure to use network monitoring tools to track traffic and look for signs of unusual activity. Conclusion Botnet attacks are a serious threat to individuals and organizations around the world. These attacks are designed to exploit security vulnerabilities and use infected devices to launch coordinated attacks on a target. By following the steps outlined in this article, you can help defend against botnets and reduce the risk of becoming a victim.
- 7. FAQs 1. What is a botnet attack? A botnet attack is a coordinated attack carried out by a network of infected devices, such as computers, routers, and IoT devices, that are controlled by a central command and control server. 2. How do botnets spread? Botnets can spread through a variety of methods, including exploiting security vulnerabilities, phishing attacks, and social engineering. 3. What are some common signs of a botnet infection? Some common signs of a botnet infection include slow performance, unusual network activity, and the presence of unusual files or programs on a device. 4. How can I defend against botnets? Defending against botnets requires a multi-layered approach that includes keeping your software up-to-date, using antivirus and anti-malware software, using strong passwords and two-factor authentication, educating yourself and your staff, using network segmentation and firewall rules, and monitoring your network for unusual activity. 5. Can botnets be completely eradicated? While it is difficult to completely eradicate botnets, taking proactive steps to defend against them can help reduce the risk of becoming a victim. It is important to stay vigilant and continue to update your defenses as new threats emerge.