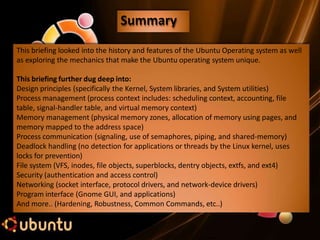
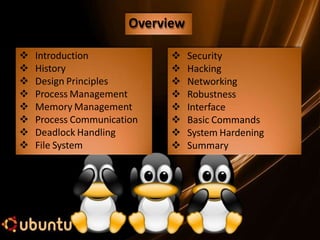
This document provides an overview and summary of the Ubuntu operating system. It discusses Ubuntu's history beginning with the creation of Linux by Linus Torvalds in 1991. It then covers key aspects of Ubuntu including its design principles, process and memory management, security features, networking capabilities, and graphical user interface. The document also provides examples of basic commands and important directories in Ubuntu. It concludes with recommendations for securing the boot loader to help harden the Ubuntu system.

![•1991, Linus Torvalds (a Finnish student) writes a open
source small, self-contained kernel (Linux) for the 80386
processor.
•Version 0.01 - no network support, basic VM subsystem,
support for Minix fs and limited device-driver support.
[1]
•1994, Version 1.0 - networking (TCP/IP protocols, new file
system, SCSI, floppy disks, CD-ROM devices, sound cards,
mice, keyboards, floating point emulation, UNIX- style IPC
and extended VM subsystem. [1]
•1996, Version 2.0 - PCI support, 80386 CPU virtual 8086
mode , memory management improvements, ISDN,
internal kernel threading, automatic module loading and
multiprocessor support. [1]
•1999, Version 2.2 - firewalling, routing and traffic
management, improved symmetric multiprocessor (SMP)
performance and (Acorn, Apple, and NT) disk support. [1]
http://en.wikipedia.org/wiki/Linux_kernel
History](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-4-320.jpg)
![Ubuntu’s Linux kernel (2.6):
Multiuser, multitasking system w/ complete set of UNIX-
compatible tools.
Linux supports the Portable Operating System Interface
[for Unix] (POSIX) threading extensions (Pthreads and a
subset of the POSIX extensions for real time process
control. [1]
The Linux system three bodies of code:
Kernel – Maintains OS abstractions, virtual memory and
process management. [1]
System Libraries – Standard set of functions for
applications to interact with the kernel. [1]
System utilities – Programs that perform individual,
specialized management tasks. [1]
Design Principles](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-7-320.jpg)
![Kernel
•Ability to load/unload sections of code on demand.
Three components to the module support :
• Module management (allows loading modules in mem)
•Driver registration (allows modules to tell kernel when new
drivers are available)
• Conflict-resolution.
Driver Registration tables include the following:
•Device Drivers – Character devices (printers, terminals,
mice), block devices (disk drives), and network interface
devices. [1]
•File Systems – Anything that implements Linux’s virtual- file-
system call routines. [1]
• Network protocols – IPX, firewall packet filtering rules, etc.
[1]
•Binary format – specifies way for recognizing/loading an
executable file. [1]
Design Principles](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-8-320.jpg)
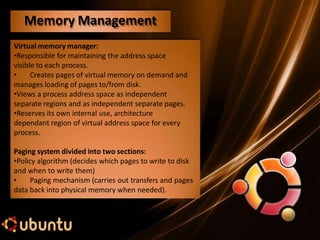
![Linux avoids segmentation and separates physical
memory into three zones:
ZONE_DMA (lower 16MB of physical memory),
ZONE_NORMAL (normally used 16-896 MB),
ZONE_HIGHMEM (Not mapped into kernel address
space > 896MB). [1]
Page tables keep track of the physical pages of memory
that are used by a process, and they map the virtual
pages to the physical pages.
Linux kernel 2.6 uses reverse page mapping
Memory Management](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-11-320.jpg)

![Deadlock - a condition where one or more executing threads and one or more resources,
such that each thread is waiting for one of the resources, but all the resources are already
held. [1]
In essence the threads are all waiting for each other, but they will never make any
progress toward releasing the resources that they already hold.
Unlike some Operating Systems:
“There is no deadlock detection for applications or threads by the Linux kernel”.
Linux requires the use of semaphores (sleeping locks), spin locks (a lock that can be held
by at most one thread of execution), and the Big Kernel Lock (BKL) to attempt deadlock
prevention.
Deadlock Handling](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-16-320.jpg)

![Linux 2.6 retains UNIX’s standard file-system module.
•Allows Linux files to be anything capable of handling the input or output of a
stream of data.
• Device drivers, interprocess communication channels and network connections
all look like files on Linux.
•The Linux kernel hides the implementation details of any single file type behind a
layer of software called the virtual file system (VFS). [1]
The VFS defines four major types of objects:
• inode object – represents an individual file.
• file object – represents an open file.
• superblock object – represents the entire file system.
• dentry object – represents an individual directory entry.
File System](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-18-320.jpg)
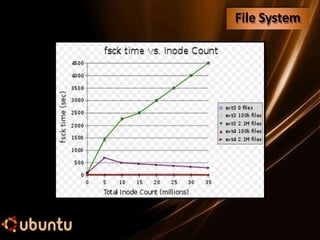
![XFS was a file system:
Developed by Silicon Graphics and designed to handle files as large as a million terabytes,
in 32 bit Linux systems it can handle files up to 16 terabytes.
Ext4 is currently the default choice of Ubuntu 10.10 and performs much better than ext2,
ext3, and XFS. A new file system btrfs is also supported in Ubuntu version 10.10 but is not
yet stable [9]
Ext4 (forth extended file system) - journaling (keeps track of changes in a journal before
changing in main file) Linux file system that became stable in 2008.
Ext4 :
•Supports volumes up to 1 Exabyte (1018) and files with sizes up to 16 terabytes
(16x1012). Uses extents (range of contiguous physical blocks) to replace the traditional
block mapping used by ext2/3, performs pre-allocation of on-disk space, delayed
allocation (using an allocate-on-flush technique), breaks the ext3 32,000 subdirectory
limit (now 64,000), performs journal check-summing (improved reliability), faster file
system checking, multi-block allocation, and improved timestamps.
File System](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-19-320.jpg)
![The Linux security module is closely tied to UNIX security mechanisms.
Security concerns can be classified into two groups:
Authentication (Ensuring that only authorized individuals have access to files that they
are authorized.)
Access control (mechanism for validating whether a user has the right to access a
particular object and preventing unauthorized access as necessary). [1]
Historically Linux suffered from the same security vulnerabilities (such as eight character
passwords) as UNIX. However, a newer security mechanism known as the Pluggable
authentication Module (PAM) system based on shared libraries is now available to Linux
users. [1]
Security](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-21-320.jpg)

![Brute-force (password guessing) attacks are the most common form of attack on any
operating system. In Linux, the most common types of services that can be brute-force
attacked are: [4]
• Telnet
• File Transfer Protocol (FTP)
• The “r” commands (rlogin, rsh, and so on)
• Secure Shell (ssh)
• SNMP community names
• Post Office Protocol (POP) and Internet Message Access Protocol (IMAP)
• Hypertext Transport Protocol (HTTP/HTTPS)
• Concurrent Version System (CVS) and Subversion (SVN)
Hacking](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-23-320.jpg)
![Hydra is one of the most popular and versatile brute force utilities available. However
pop.c and SNMPbrute are also popular and can be downloaded at the following
locations: [4]
http://freeworld.thc.org/thc-hydra/
http://packetstormsecurity.org/groups/ADM/ADM-pop.c
http://packetstormsecurity.org/Crackers/snmpbrute-
THC – Hydra
pop.c
SNMPbrute
fixedup.c
Hacking](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-24-320.jpg)
![Hacking
Secure Remote Password
OpenSSH
pam_passwdqc
pam_lockout
According to Hacking Exposed 6: Network Secrets & Solutions [4] there are some
freeware tools that can help prevent brute force attacks. For brevity I will not list the
download locations (use Google search). These tools listed in the book follow:
cracklib Password composition tool.
npasswd A replacement for the passwd command.
A new mechanism for performing secure password
based authentication and key exchange over any type
of network.
A telnet/ftp/rsh/login communication replacement
with encryption and RSA authentication.
PAM module for password strength checking.
PAM module for account lockout.](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-25-320.jpg)
![A comparison of operating system robustness was
completed for the 19th International Symposium on
Software Reliability Engineering by Shanghai Jiao Tong
University [8].
They observe that Windows XP achieves better
robustness performance than Ubuntu in their
experiment.
Ubuntu had higher restart and abort rates than
Windows OSs in general robustness test.
In particular, the robustness of Ubuntu rose drastically
from 85.70% to 97.24% in CINT (surpassing Windows
Vista in this generic compute intensive operational
profile) and 97.37% in CFP.” [8]
Robustness](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-28-320.jpg)


![Most Linux systems use two boot loaders, the Linux Loader (LILO) or Grand Unified Boot
Loader (GRUB). Ubuntu uses GRUB. The boot loader controls your boot image and
determines what kernel is booted when the system is started or rebooted. [3]
Both boot loaders are insecure if a hacker has physical system access and
Turnbull recommends that users only keep the current and previous versions of the
kernel.
Both boot loaders can easily be secured with passwords. To accomplish this
Ubuntu’s GRUB do the following: *3+
superman# grub
grub> md5crypt
Password: ********
Encrypted: $1$2FXKzQ0$I6k7iy22wB27CrkzdVPe70
grub> quit
Now copy the encrypted output and add the password to your grub.conf configuration
file. You can also add the --md5 option prior to the password in grub.conf to ensure
interaction with GRUB can only occur when you type p and enter the required password.
System Hardening](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-33-320.jpg)
![Most Linux systems use two boot loaders, the Linux Loader (LILO) or Grand Unified Boot
Loader (GRUB). Ubuntu uses GRUB. The boot loader controls your boot image and
determines what kernel is booted when the system is started or rebooted. [3]
Both boot loaders are insecure if a hacker has physical system access and
Turnbull recommends that users only keep the current and previous versions of the
kernel.
Both boot loaders can easily be secured with passwords. To accomplish this
Ubuntu’s GRUB do the following: *3+
superman# grub
grub> md5crypt
Password: ********
Encrypted: $1$2FXKzQ0$I6k7iy22wB27CrkzdVPe70
grub> quit
Now copy the encrypted output and add the password to your grub.conf configuration
file. You can also add the --md5 option prior to the password in grub.conf to ensure
interaction with GRUB can only occur when you type p and enter the required password.
System Hardening](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-34-320.jpg)
![There are also several services that may start at boot, of which many can pose as security
risks. Turnbull [3] recommends disabling the following:
anacron, apmd, atd, autofs, cups, gpm, irda (unless used), isdn (unless used), kudzu, lpd,
netfs, nfs, nfslock, pcmcia, portmap, rawdevices, rhnsd, snmpd, snmtptrap,winbind, xfs,
ypbind.
Delete the following user accounts:
adm, desktop, ftp, games, gdm, gnats, gopher, identd, irc, list (if not using
mailman), lp & lpd (if no printing) mailnull (if no Sendmail), news, nfsnobody, nscd,
operator, postgres (if no Postgres), proxy, rpc, rpcuser, sync, telnetd, uucp, www-data (if
not Web server).
Delete the following group accounts:
lp, news, uucp, proxy, postgres, www-data, backup, operator, list, irc, src, gnats,
staff, games, users, telnetd, gdm, telnetd, gopher, ftp, nscd, rpc, rpcuser, nfsnobody, xfs,
desktop
System Hardening](https://image.slidesharecdn.com/ubantuppt-230207170837-35b08cbb/85/ubantu-ppt-pptx-35-320.jpg)