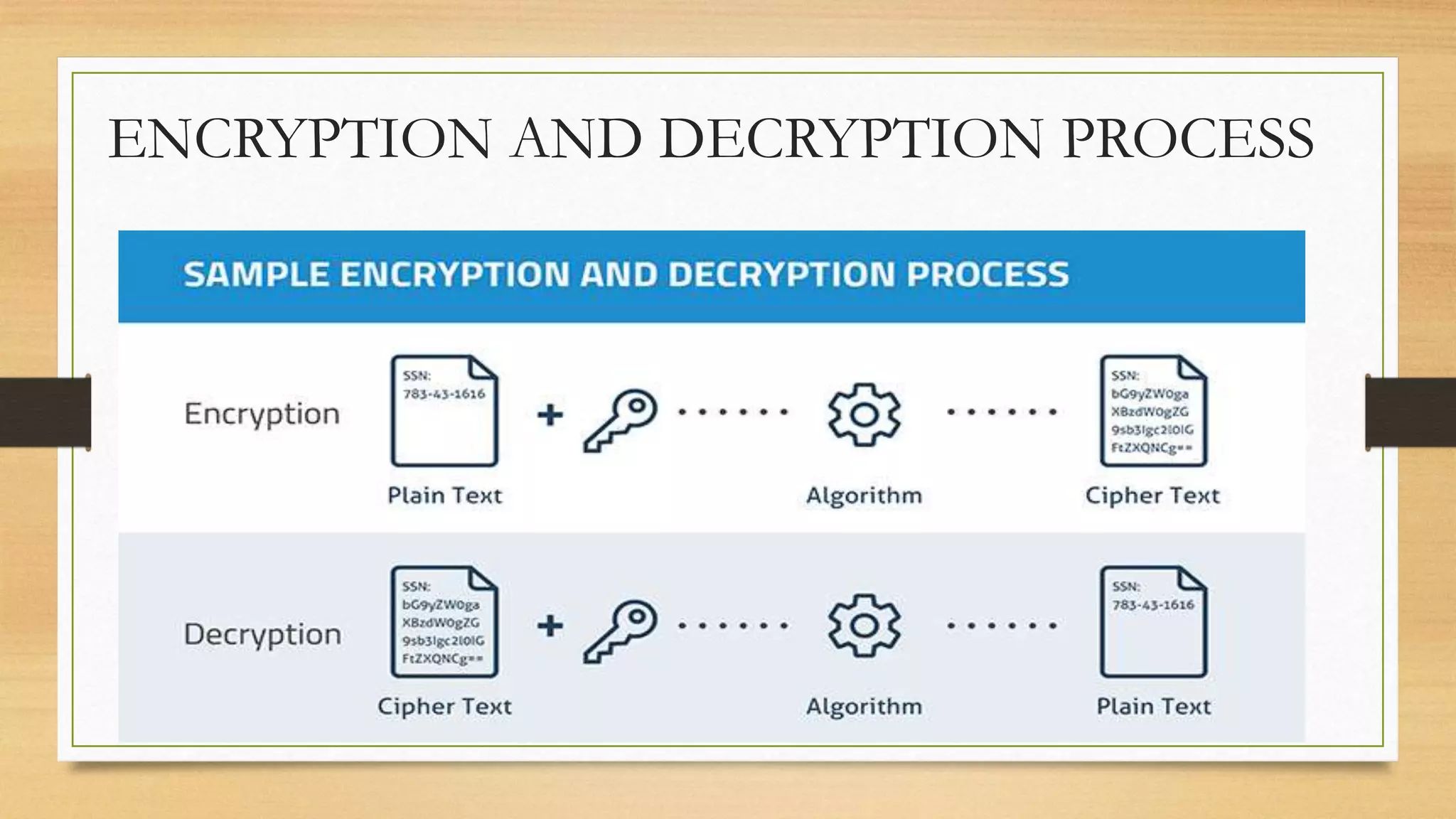
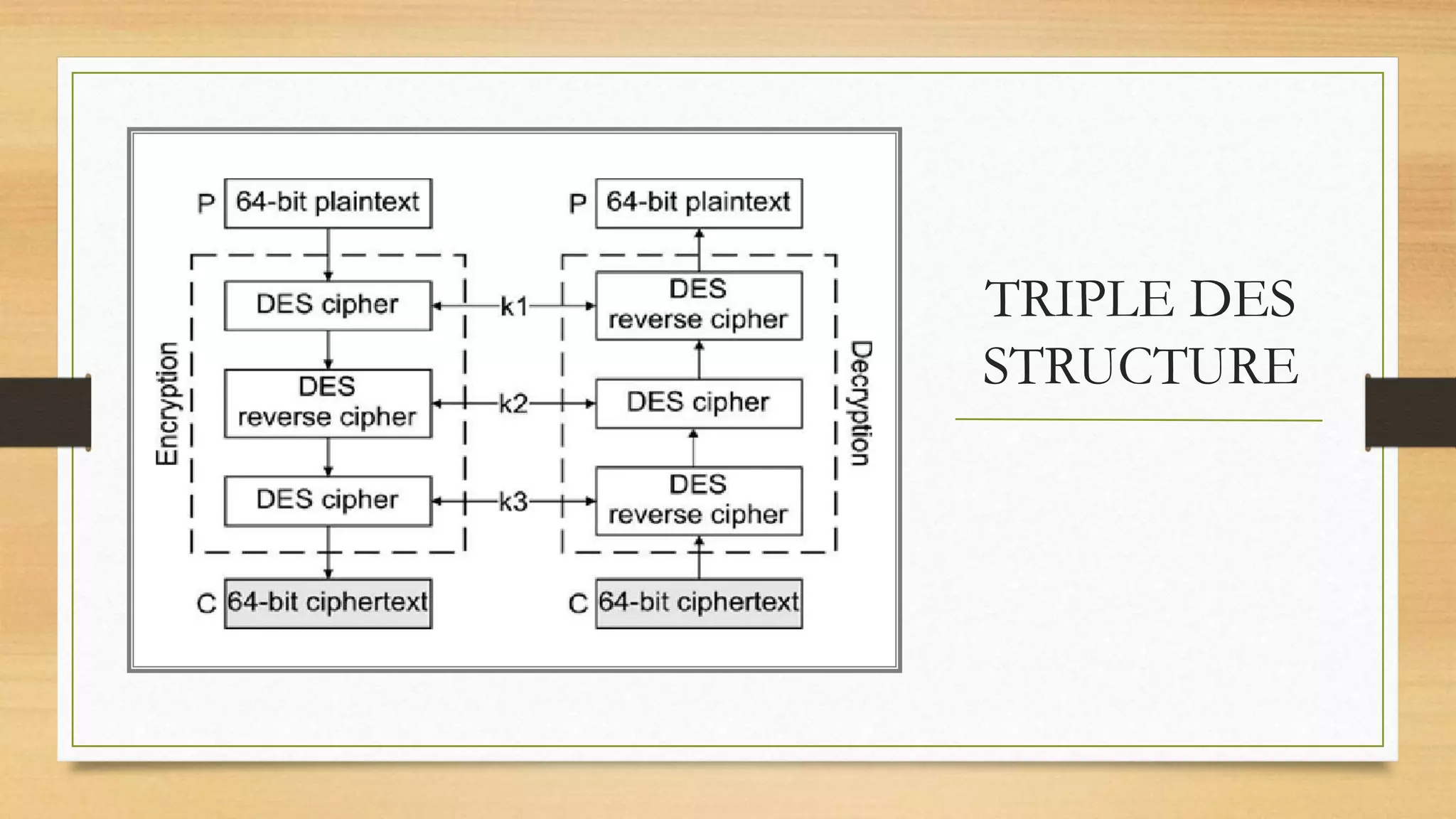
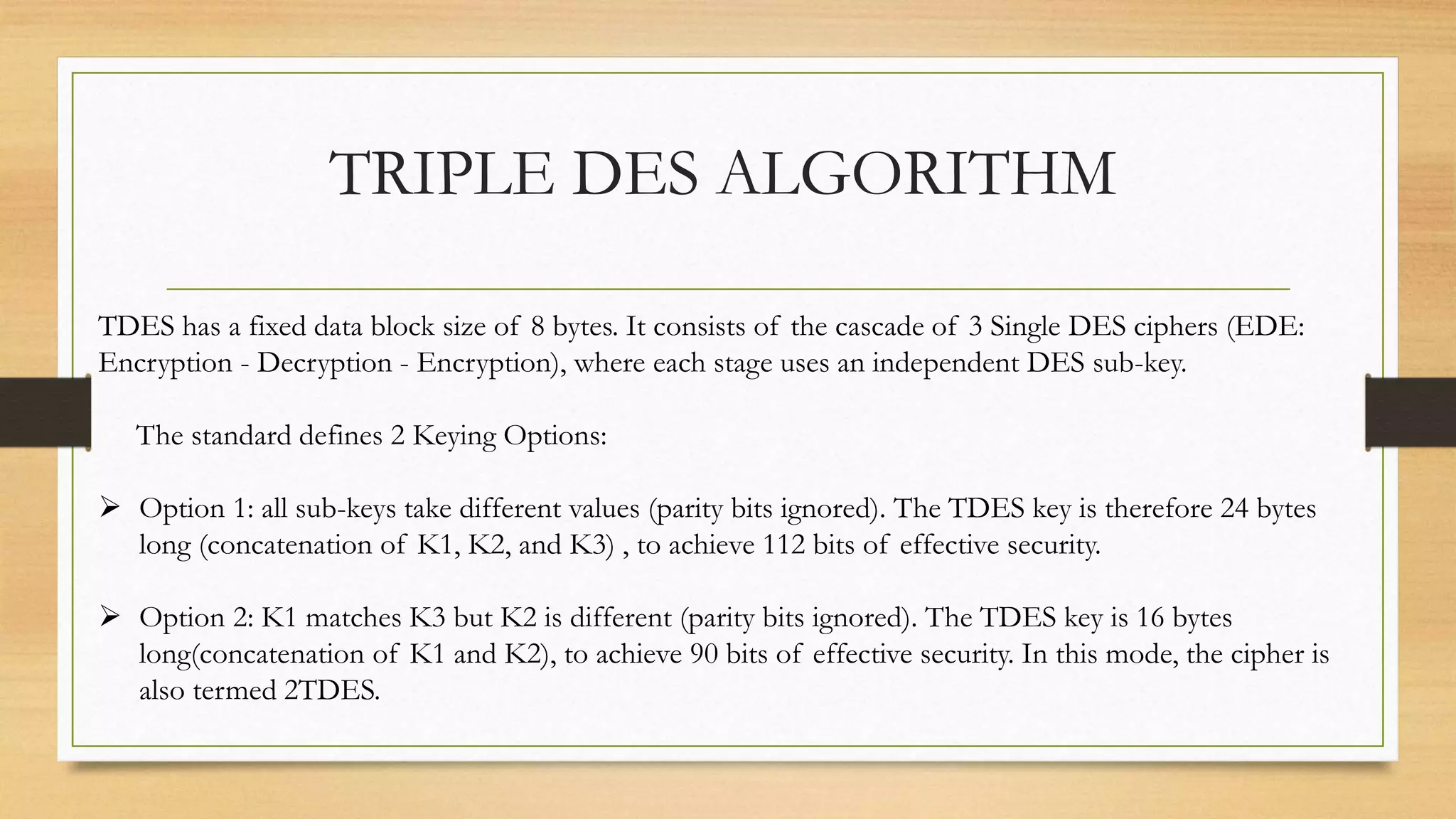
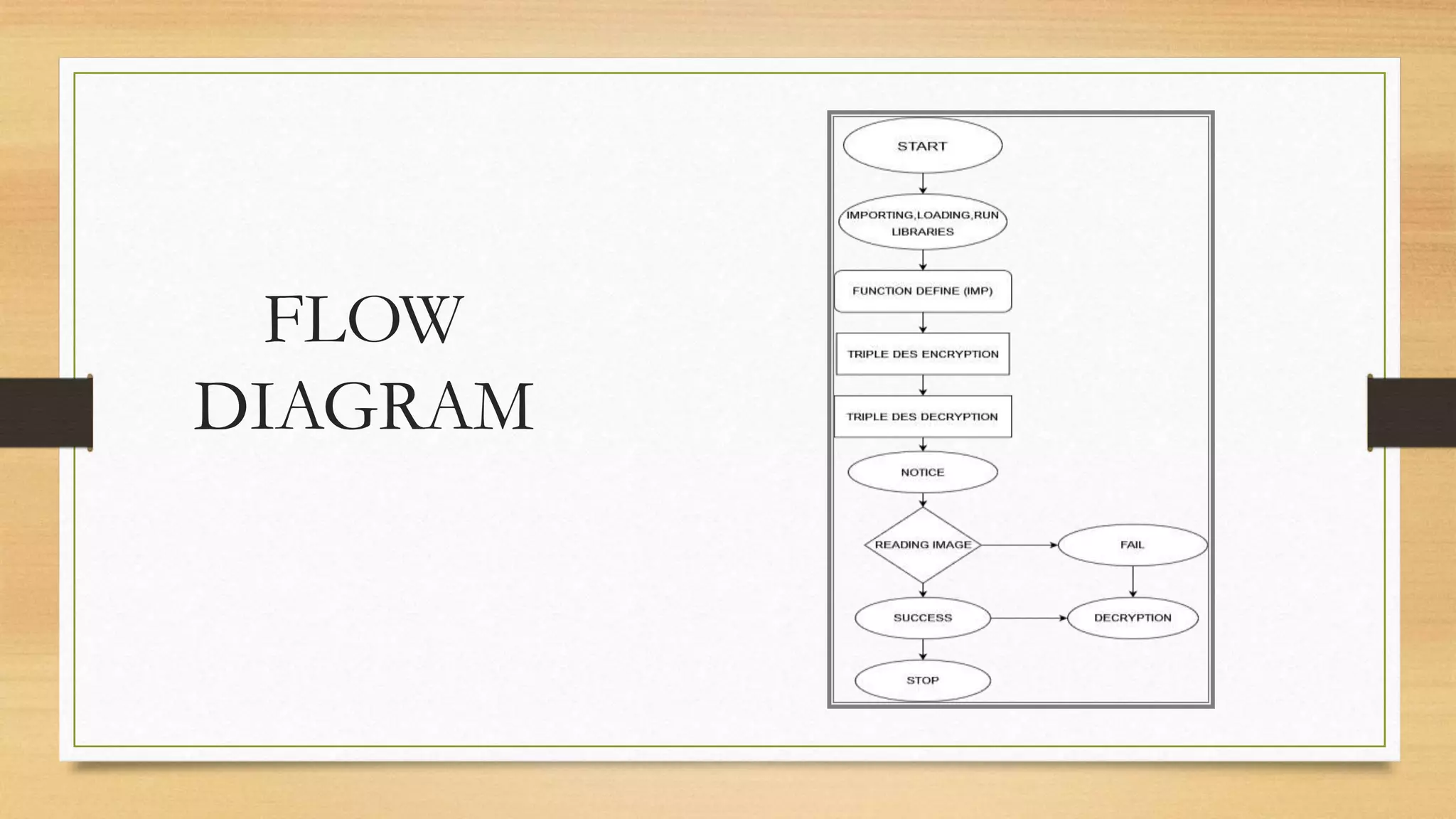
The document describes Triple DES encryption, which applies the Data Encryption Standard (DES) cipher algorithm three times to each data block. Triple DES is used to encrypt digital images containing critical information. It has a block size of 64 bits and uses 168-bit, 112-bit, or 56-bit keys depending on the keying option. The encryption process involves three instances of DES encryption with different or same keys, providing stronger security than single DES. Pseudocode and flow diagrams illustrate the Triple DES algorithm and encryption/decryption process.