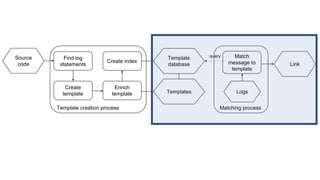
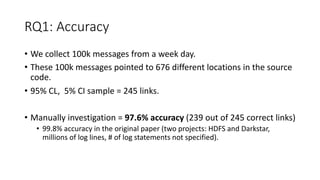
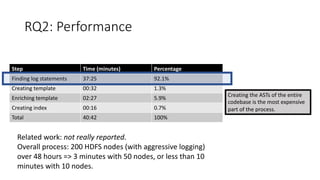
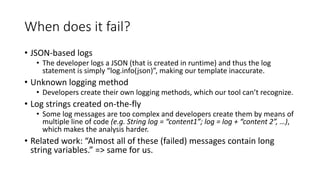
The document discusses techniques for tracing log data back to its originating log statements, evaluating the effectiveness of heuristic methods in an industry dataset. It highlights a high accuracy of approximately 97% in linking log messages to their source code lines, though the process can be resource-intensive due to Abstract Syntax Tree (AST) generation. The paper also notes that complex log statements can complicate the analysis, highlighting challenges such as JSON-based logs and custom logging methods.

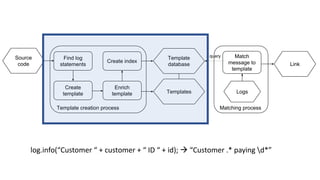
![log.info(”Customer “ + customer +
“ paying ” + paymentValue);
[2019-02-03 15:43:24] [MagicPayment.java][L456] Customer Maurício paying 235.67
Class name Line number](https://image.slidesharecdn.com/msr19-presentation-190527191706/85/Tracing-Back-Log-Data-to-its-Log-Statement-From-Research-to-Practice-3-320.jpg)