The document discusses memory segmentation and registers in the 8086 processor. Memory is divided into 64K segments identified by a 16-bit number, and locations within segments are specified with a 16-bit offset. There are 14 registers for data, addresses, segments, pointers, indexes, status flags, and instructions. The registers are used for arithmetic, logic, and flow control operations. Instructions include data transfer, arithmetic, logic, shifts, and flow control. Memory addressing uses segment and offset addresses, and the stack uses push and pop instructions.
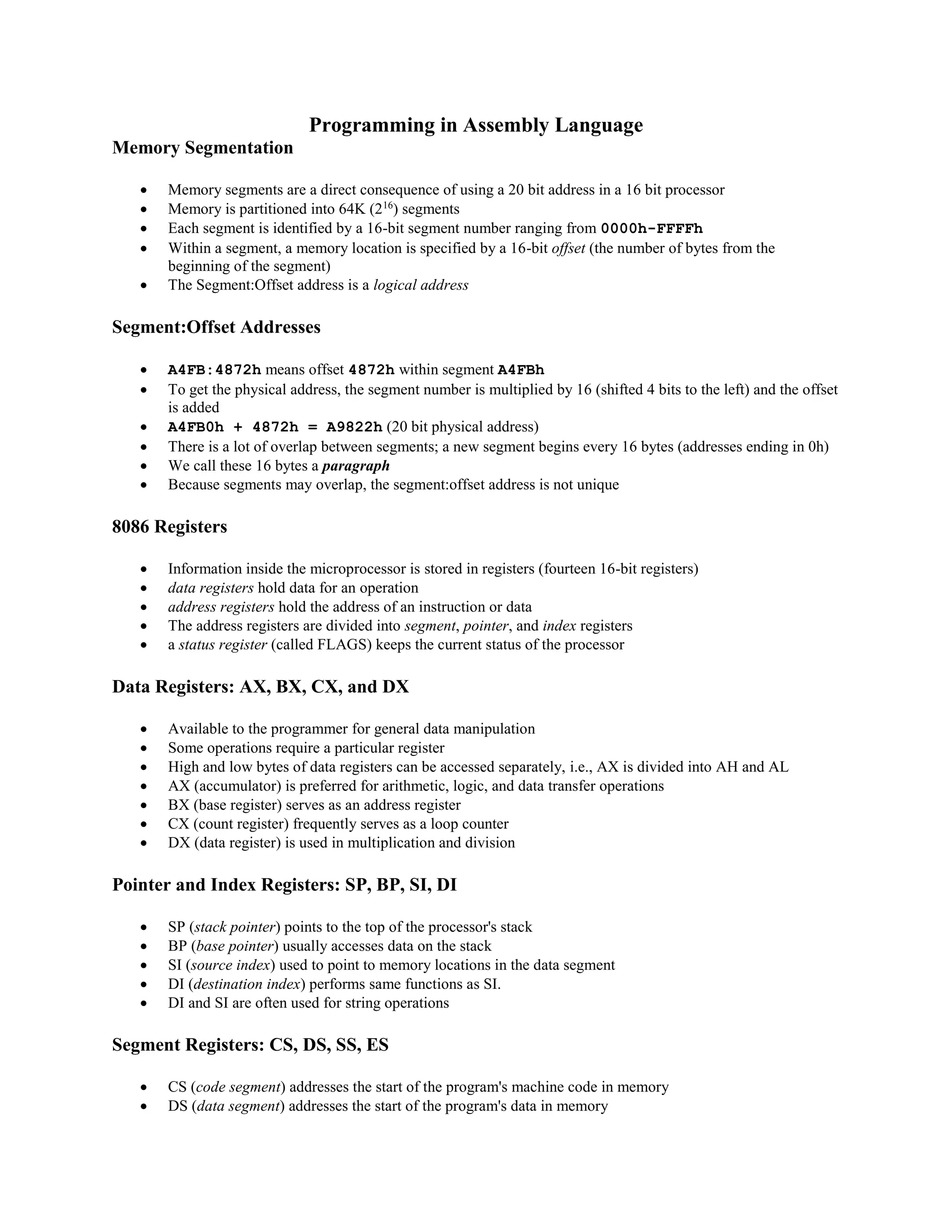
![ mov ax, [word1]
o "Move word1 to ax"
o Contents of register ax are replaced by the contents of the memory location word1
o The brackets specify that the contents of word1 are stored -- word1==address,
[word1]==contents
xchg ah, bl
o Swaps the contents of ahand bl
Illegal: mov [word1], [word2]
o can't have both operands be memory locations
The Stack
A data structure in which items are added and removed only from one end (the "top")
A program must set aside a block of memory to hold the stack by declaring a stack segment
stack 256
SS will contain the segment number of the stack segment -- SP will be initialized to 256 (100h)
The stack grows from higher memory addresses to lower ones
PUSH and POP
New words are added with push
push source
o SP is decreased by 2
o a copy of the source contents is moved to SS:SP
Items are removed with pop
pop destination
o Content of SS:SP is moved to the destination
o SP is increased by 2
Stack example
push ax ;Save ax and bx
push bx ; on the stack
mov ax, -1 ;Assign test values
mov bx, -2
mov cx, 0
mov dx, 0
push ax ;Push ax onto stack
push bx ;Push bx onto stack
pop cx ;Pop cx from stack
pop dx ;Pop dx from stack
pop bx ;Restore saved ax and bx
pop ax ; values from stack
Arithmetic Instructions
Addition instructions
o aaa, adc, add, daa, inc
Subtraction instructions
o aas, cmp, das, dec, neg, sbb, sub
Multiplication instructions
o aam, imul, mul](https://image.slidesharecdn.com/topic6-programminginassemblylanguage230517115118-230622142852-51dde8e6/75/Topic-6-Programming-in-Assembly-Language_230517_115118-pdf-3-2048.jpg)
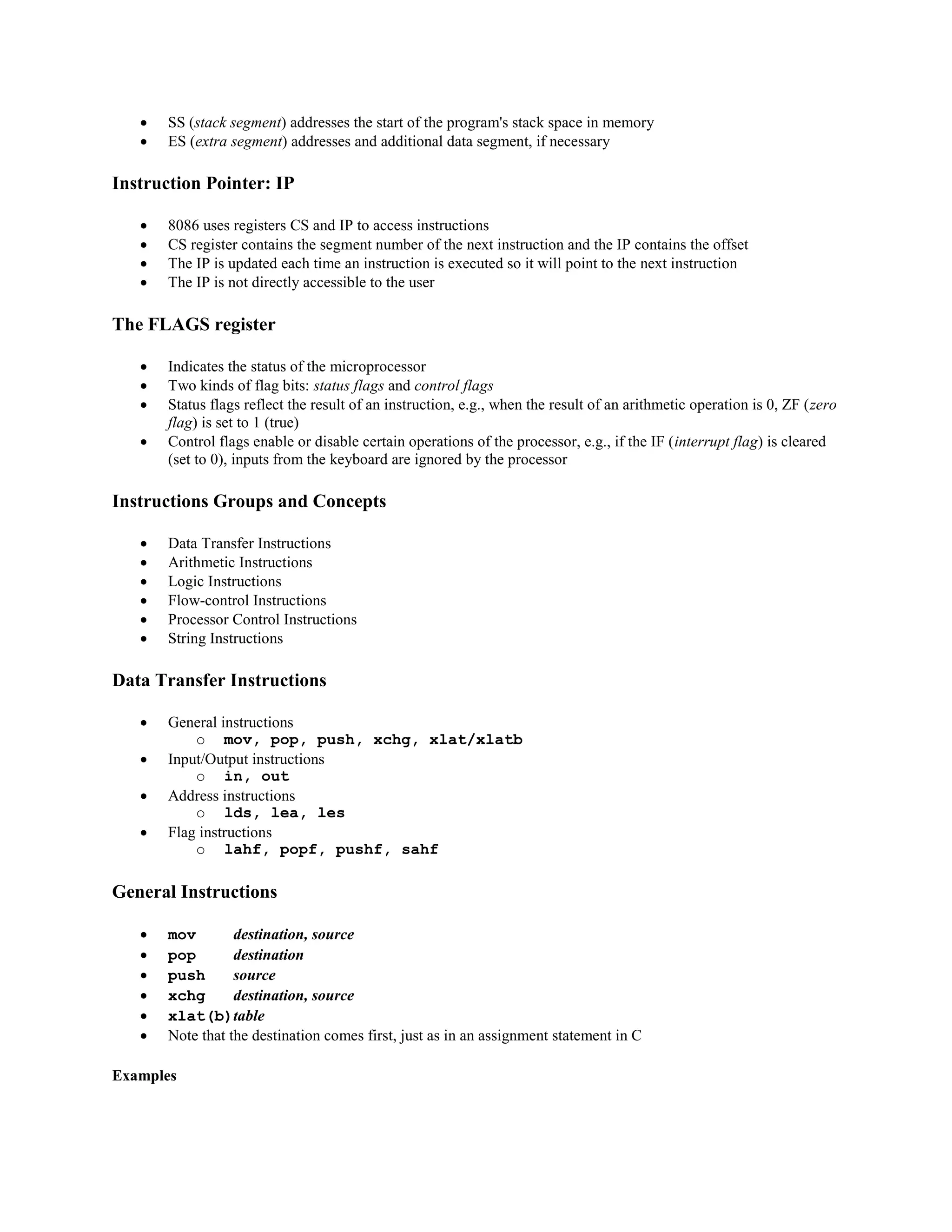
![ Division instructions
o aad, cbw, cwd, div, idiv
Addition Instructions
aaa
o ASCII adjust for addition
adc destination, source
o Add with carry
add destination, source
o Add bytes or words
daa
o Decimal adjust for addition
inc destination
o Increment
ADD and INC
ADD is used to add the contents of
o two registers
o a register and a memory location
o a register and a constant
INC is used to add 1 to the contents of a register or memory location
Examples
add ax, [word1]
o "Add word1to ax"
o Contents of register ax and memory location word1 are added, and the sum is stored in ax
inc ah
o Adds one to the contents of ah
Illegal: add [word1], [word2]
o can't have both operands be memory locations
Subtraction instructions
aas
o ASCII adjust for subtraction
cmp destination, source
o Compare
das
o Decimal adjust for subtraction
dec destination
o Decrement byte or word
neg destination
o Negate (two's complement)
sbb destination, source
o Subtract with borrow
sub destination, source
o Subtract
Examples](https://image.slidesharecdn.com/topic6-programminginassemblylanguage230517115118-230622142852-51dde8e6/75/Topic-6-Programming-in-Assembly-Language_230517_115118-pdf-4-2048.jpg)
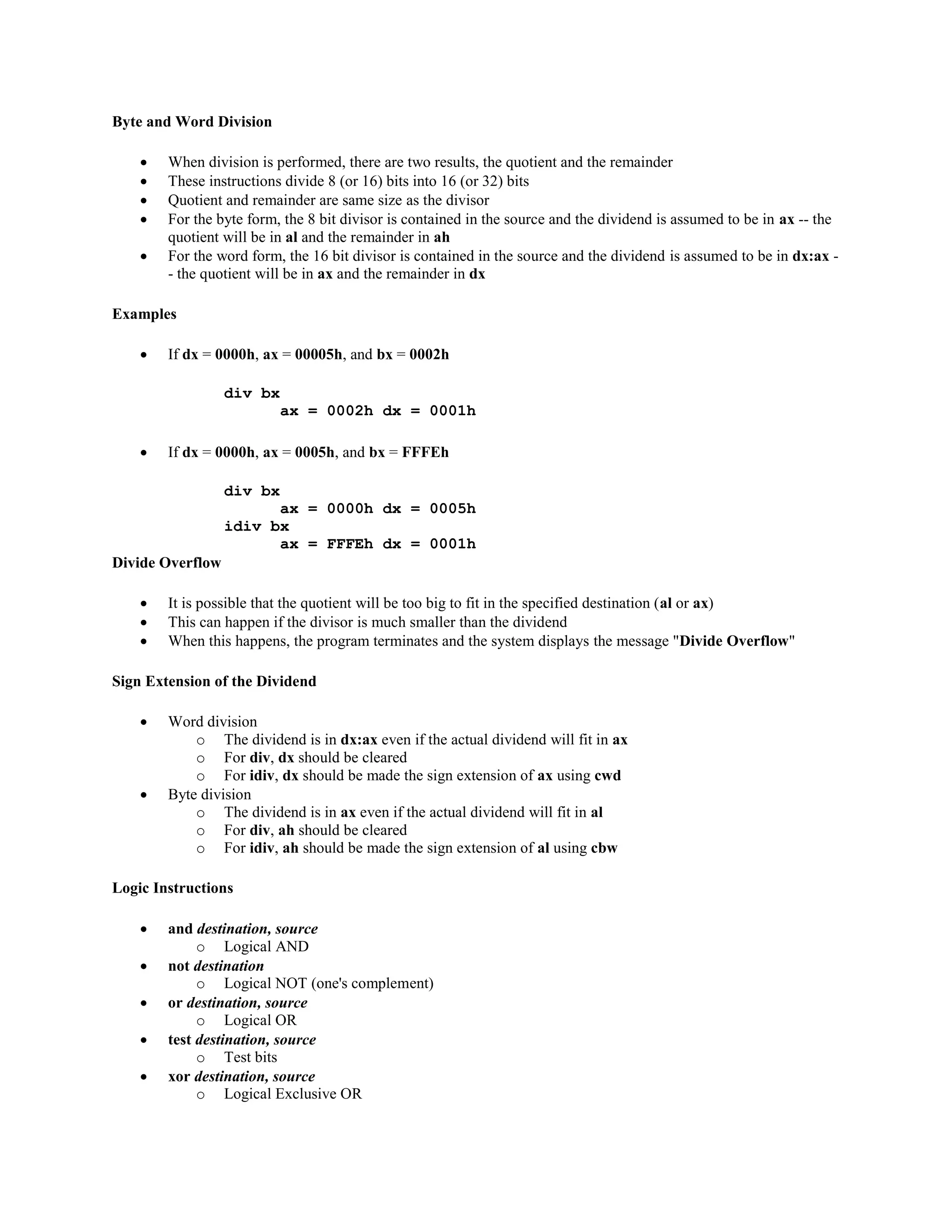
![ sub ax, [word1]
o "Subtract word1 from ax"
o Contents of memory location word1 is subtracted from the contents of register ax, and the sum is
stored in ax
dec bx
o Subtracts one from the contents of bx
Illegal: sub [byte1], [byte2]
o can't have both operands be memory locations
Multiplication instructions
aam
o ASCII adjust for multiply
imul source
o Integer (signed) multiply
mul source
o Unsigned multiply
Byte and Word Multiplication
If two bytes are multiplied, the result is a 16-bit word
If two words are multiplied, the result is a 32-bit doubleword
For the byte form, one number is contained in the source and the other is assumed to be in al -- the product
will be in ax
For the word form, one number is contained in the source and the other is assumed to be in ax -- the most
significant 16 bits of the product will be in dx and the least significant 16 bits will be in ax
Examples
If ax contains 0002h and bx contains 01FFh
mul bx
dx = 0000h ax = 03FEh
If ax contains 0001h and bx contains FFFFh
mul bx
dx = 0000h ax = FFFFh
imul bx
dx = FFFFh ax = FFFFh
Division instructions
aad
o ASCII adjust for divide
cbw
o convert byte to word
cwd
o convert word to doubleword
div source
o unsigned divide
idiv source
o integer (signed) divide](https://image.slidesharecdn.com/topic6-programminginassemblylanguage230517115118-230622142852-51dde8e6/75/Topic-6-Programming-in-Assembly-Language_230517_115118-pdf-5-2048.jpg)
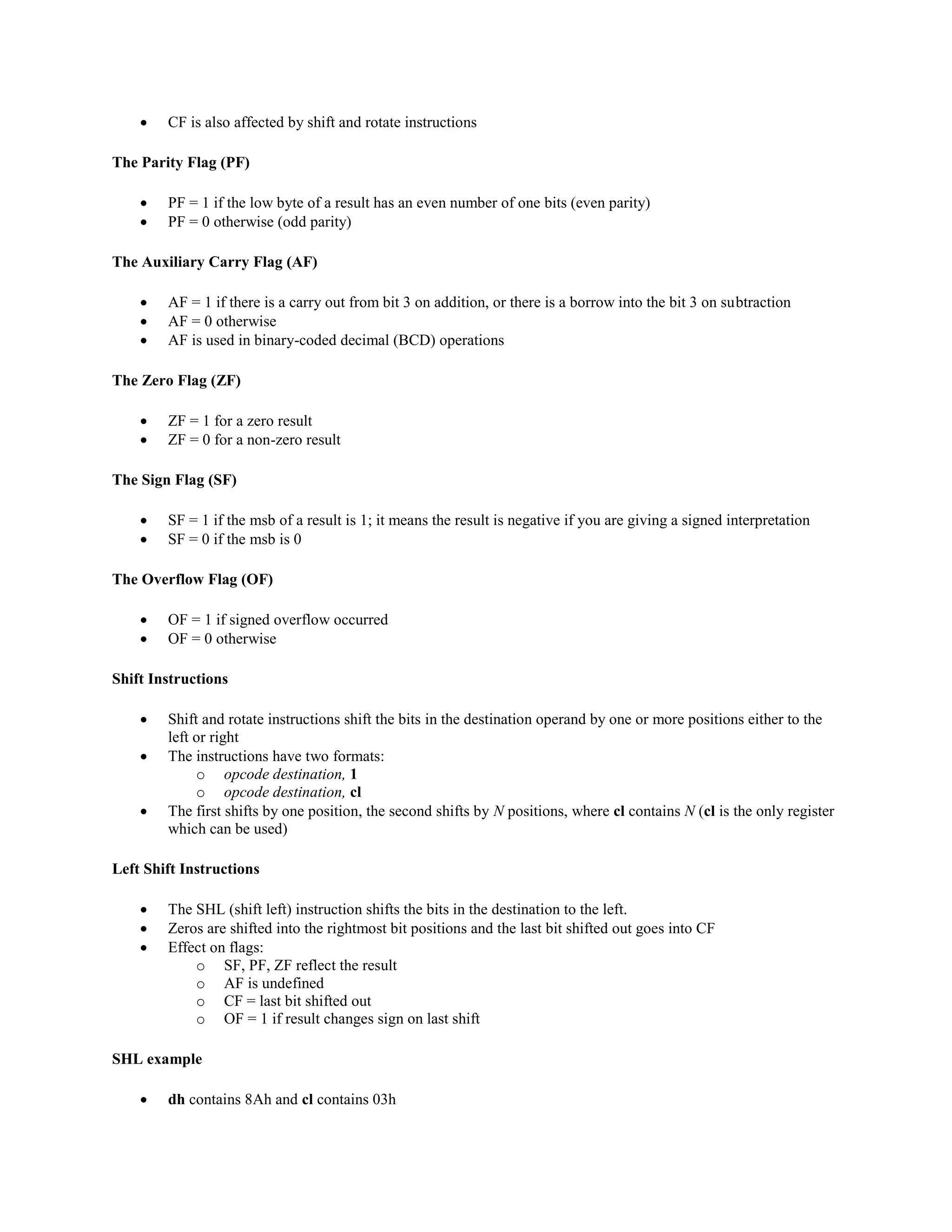
![ The ability to manipulate bits is one of the advantages of assembly language
One use of and, or, and xor is to selectively modify the bits in the destination using a bit pattern (mask)
The and instruction can be used to clear specific destination bits
The or instruction can be used to set specific destination bits
The xor instruction can be used to complement specific destination bits
Examples
To clear the sign bit of al while leaving the other bits unchanged, use the and instruction with 01111111b
=7Fh as the mask
and al,7Fh
To set the most significant and least significant bits of al while preserving the other bits, use the or
instruction with 10000001b = 81h as the mask
or al,81h
To change the sign bit of dx, use the xor instruction with a mask of 8000h
xor dx,8000h
The NOT instruction
The not instruction performs the one's complement operation on the destination
The format is
o not destination
To complement the bits in ax:
o not ax
To complement the bits in WORD1
o not [WORD1]
The TEST instruction
The test instruction performs an and operation of the destination with the source but does not change the
destination contents
The purpose of the test instruction is to set the status flags (discussed later)
Status Flags
Bit Name Symbol
0 Carry flag cf
2 Parity flag pf
4 Auxiliary carry flag af
6 Zero flag zf
7 Sign flag sf
11 Overflow flag of
The Carry Flag (CF)
CF = 1 if there is a carry out from the msb (most significant bit) on addition, or there is a borrow into the
msb on subtraction
CF = 0 otherwise](https://image.slidesharecdn.com/topic6-programminginassemblylanguage230517115118-230622142852-51dde8e6/75/Topic-6-Programming-in-Assembly-Language_230517_115118-pdf-7-2048.jpg)
![mov ax,@data ;Initialize DS to address
mov ds,ax ; of data segment
lea dx,[msg] ;get message
mov ah,09h ;display string function
int 21h ;display message
Exit:
mov ah,4Ch ;DOS function: Exit program
mov al,0 ;Return exit code value
int 21h ;Call DOS. Terminate program
END Start ;End of program / entry point](https://image.slidesharecdn.com/topic6-programminginassemblylanguage230517115118-230622142852-51dde8e6/75/Topic-6-Programming-in-Assembly-Language_230517_115118-pdf-17-2048.jpg)
