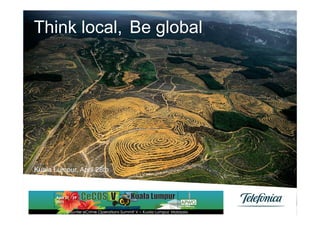
Think Local, Be Global
- 1. Think local, Be global Kuala Lumpur, April 28th Telefónica S.A Global Security
- 2. Contents 01 The project 02 The trip 03 Our Approach 04 Extrapolating it to Global Anti-fraud working group Global Security 1 Telefónica S.A
- 3. 01 The Project Global Security 2 Telefónica S.A
- 4. 3 Security Operation Centers § Haga clic para modificar el estilo de texto del patrón • Segundo nivel Madrid › Tercer nivel Lima Sao Paulo To give service to all our customers in up to 20 local Operators Global Security 3 Telefónica S.A
- 5. 02 The trip Global Security 4 Telefónica S.A
- 6. Global Security 5 Telefónica S.A
- 7. Language Global Security 6 Telefónica S.A
- 8. Cultural Global Security 7 Telefónica S.A
- 9. Legal Global Security 8 Telefónica S.A
- 10. Taxes Global Security 9 Telefónica S.A
- 11. A few obstacles in our journey Diapositiva Muro § Haga clic para modificar el estilo de texto del patrón • Segundo nivel › Tercer nivel Global Security 10 Telefónica S.A
- 12. Just an example Global Security 11 Telefónica S.A
- 13. Mobile Security Global Security 12 Telefónica S.A
- 14. What do you understand for Mobile Security? Global Security 13 Telefónica S.A
- 15. How many of you think about…? § Malware on the mobile § Loss of important data: • Photos • e-mails § Being tracked Global Security 14 Telefónica S.A
- 16. How many of you was thinking about…? § Mobile as a security guard • As a device helping you in case on an emergency › SOS › I’m safe • Locale you or your family member if needed. Global Security 15 Telefónica S.A
- 17. 03 Our Approach Global Security 16 Telefónica S.A
- 18. Building a common framework People Platforms Process Global Security 17 Telefónica S.A
- 19. Operation model scheme n Spain, Perú, and Brazil have been selected to be provider OBs due to expertise (Spain, Perú) and market potential (Brazil). n In the resulting model the commercialising OBs must interface with the Global SOCs through a set of Business Support Systems Security Operation Centers (SOCs) GLOBAL MSS GLOBAL ESPAÑA ** SOC 3 (BRASIL) SOC 2 (PERÚ) (Lead Provider (Povider BSS (Povider & & & Commercializing) Commercializing) Commercializing) Managed Security Services (MSS) Ordering Billing CMDB Trouble ticketing Cost Commercializing OBs Commercializing Commercializing Commercializing Commercializing Commercializing OB1 (LATAM) OB2 (LATAM) OB3 (EUROPA) OB4 (EUROPA) MNCs Global Security 18 Telefónica S.A
- 20. Local and Global Process n In order to allow SOCs to communicate with each other, balance workloads, receive work orders from commercializing OBs, and provide trouble ticketing for complex issues (L2, L3) we will need to implement a central tool for Managed Security Services Business Support Systems Receiving Activity Source Unit unit System Only two areas in Presales OB OB Local commercializing OBs need to Sales OB OB Local interface with the MSS BSS: Provisioning OB SOC Global n Sales back office Service delivery SOC OB Global n Service desk Ticketing OB SOC Global No integration necessary with Reports SOC OB Global local tools SOC->OB billing SOC OB Global Customer billing OB OB Local Global Security 19 Telefónica S.A
- 21. Advantage of global services Telefónica Global SOC Strategy: Enables an efficient operation of the SOCs n Through common tools and procedures set by the Security Vertical n Supported on a virtualized architecture that allows all SOCs to operate on the same platform and enables workload distribution Madrid across centres n With specialised reports for customers and internal use Allows operators to focus on commercial activity and basic support Lima n Providing clear costs and simple ordering and provisioning for the Sao services commercialized to facilitate creation of customer offers Paulo n Facilitating access to knowledge sharing tools to provide 1st level support and unified trouble ticketing for more complex issues + A Global SOC network provides efficiency + A Global SOC network enables superior service n Workload distribution n Homogeneous service portfolio at the same time – Mitigate effect of peak demand hours to serve across footprint (Key for MNC customers) more customers n Add to credibility (analysts and opinion leaders): – Enable follow the sun strategy or absorb more Top service providers’ SOCs are interconnected activity in lower-cost locations n Security threats are inter-related so servicing n Increased leverage in partner negotiations more clients n Sharing virtualized tools and processes: build – Facilitates early detection of threats once exploit n times across footprint – Enables a coordinated response n Expensive expert resources shared across n Truly redundant operations in case of local geographies contingencies Global Security 20 Telefónica S.A
- 22. Much work already done and much to do… Global Security Telefónica S.A 21
- 23. 04 Just extrapolate our small project to Global Antifraud working- group Global Security 22 Telefónica S.A
- 24. Standardize, Standardize, Standardize… § Remember the old days in Phishing fight: • When phishing was “fishing, pishing, piching and who know what else” › Phishing complains was using the terms “Copyright misuse, abuse” › So at the beginning in Europe was poorly attended because was associated to Copyright and Privacy is a value with major protection so every answer was to forward to “justice tutelage” § Phishing now is well covered but what happens with new problems. § Why not impulse standard efforts? § ARF, IODEF • Please remember time zone stamp – How many complains reaches dev- null due to fault of time accuracy. Global Security 23 Telefónica S.A
- 25. Standardize, Standardize, Standardize… § Alliances and Collaboration • Our target is common, avoid fraud. Global Security 24 Telefónica S.A
- 26. Terima kasih banyak Thank you Gracias Kuala Lumpur, April 28th Telefónica S.A Global Security Global Security 25 Telefónica S.A
- 27. Global Security 26 Telefónica S.A
