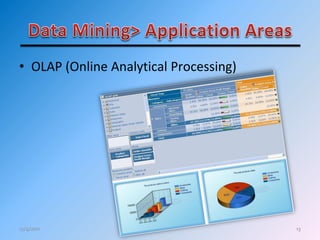
The document discusses the importance of data mining for businesses in Afghanistan, highlighting the growing need to analyze large amounts of stored data to derive beneficial insights. It emphasizes the lack of awareness and usage of data mining tools in the region and proposes that implementing computerized databases and data mining can significantly improve business decisions and operations. Additionally, it outlines potential costs and the development of tailored data mining software for Afghan businesses.