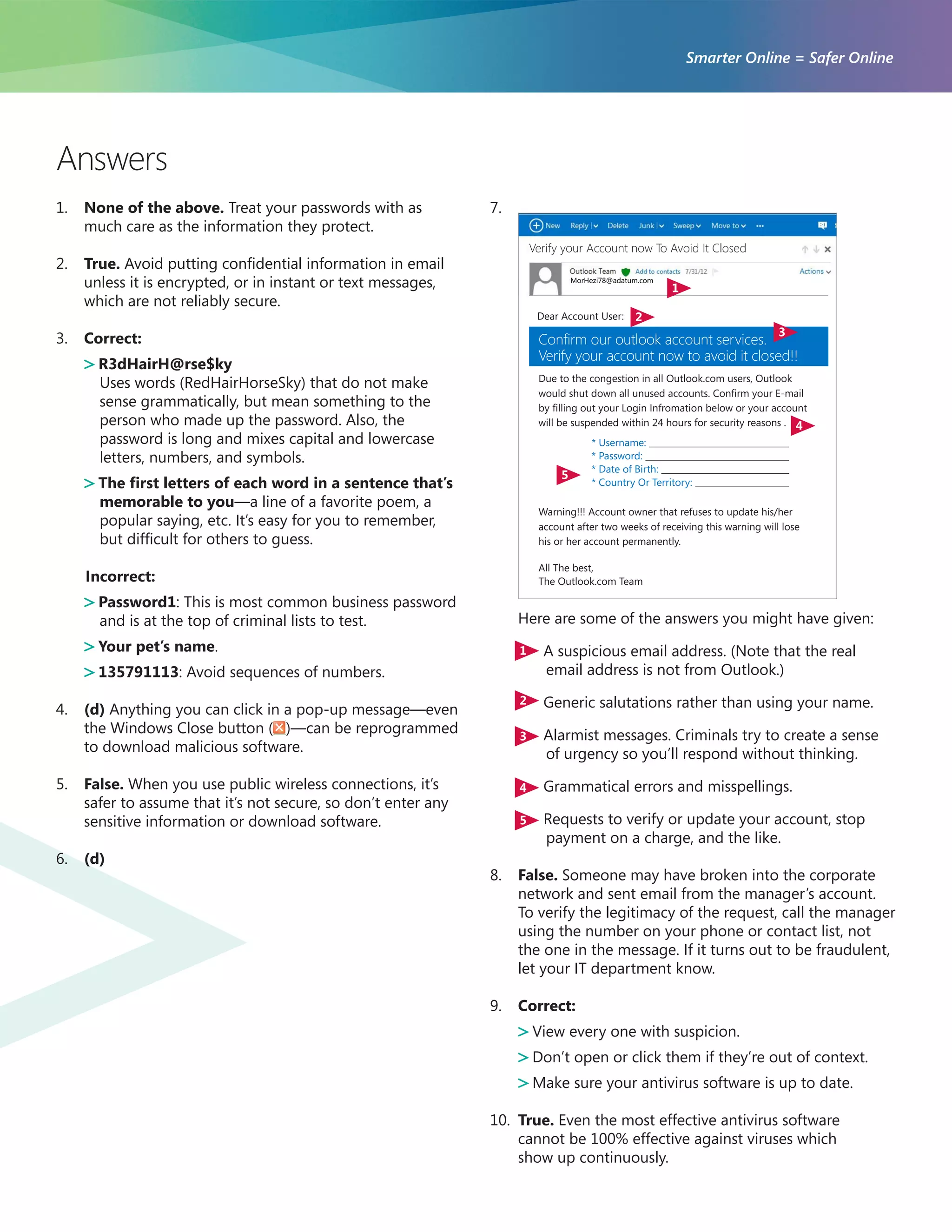
The document is a quiz designed to test knowledge of internet security practices, covering topics like password sharing, safe email communication, and identifying phishing attempts. It provides true/false and multiple-choice questions aimed at educating users on the importance of safeguarding confidential information online. Ultimately, it emphasizes the significance of being cautious and vigilant with personal and sensitive data.