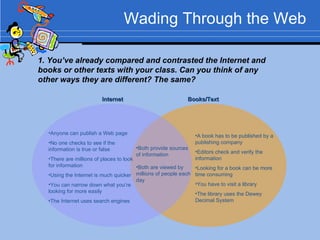
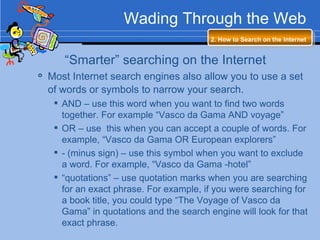
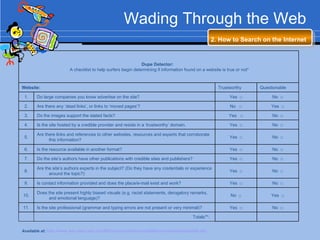
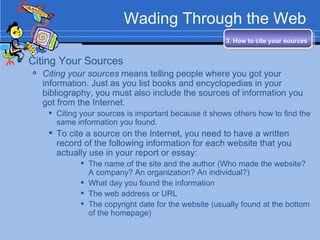
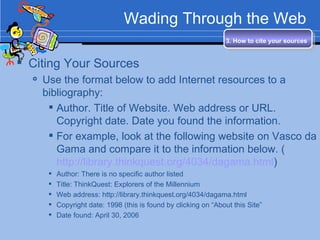
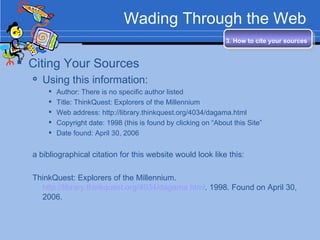
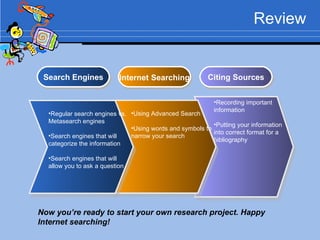
This document provides an overview of how to effectively conduct research on the internet. It discusses different types of search engines such as regular search engines, metasearch engines, and specialized search engines. It also covers how to perform advanced searches using Boolean operators and search syntax. Finally, it explains the importance of properly citing internet sources and provides the correct format for citing sources in a bibliography. The overall goal is to teach students how to efficiently find reliable information online and give proper attribution to sources.