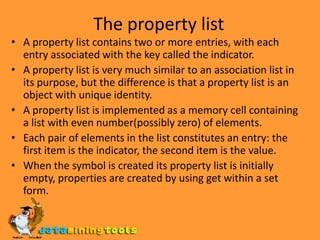
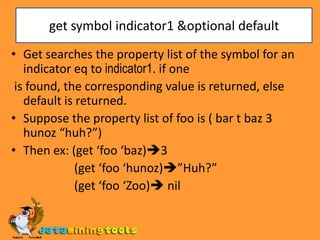
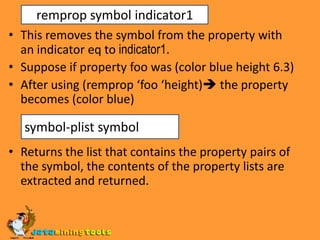
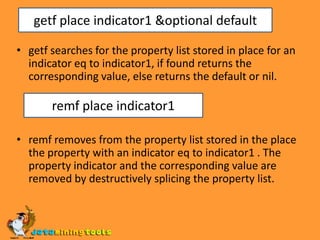
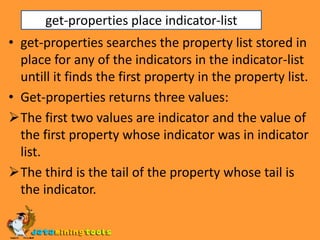
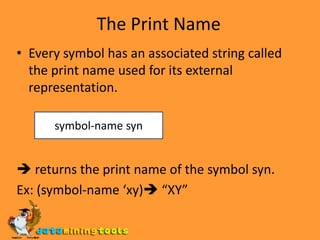
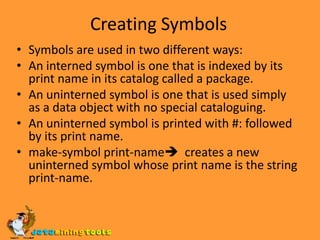
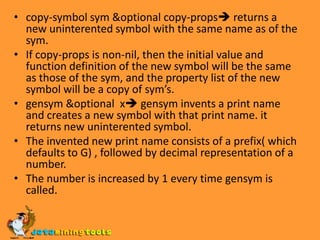
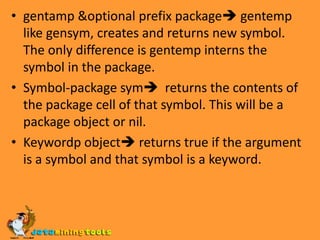
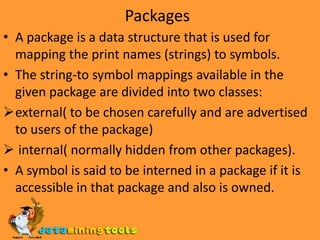
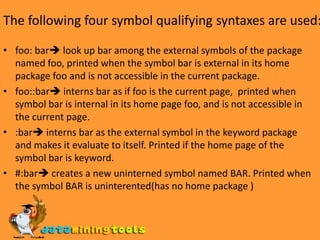
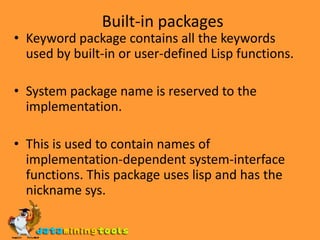
Lisp symbols have three components - a property list, print name, and package cell. A symbol is uniquely identified by its print name within a package. Packages map print names to symbols and determine symbol visibility. Functions like intern, find-package, package-name, and import/export control symbol packages and namespaces. Built-in Lisp packages include common-lisp, lisp, keyword, and system packages for core functions and keywords. Symbol properties, packages, and namespaces allow Lisp symbols to serve as named objects that can be organized and shared across code.