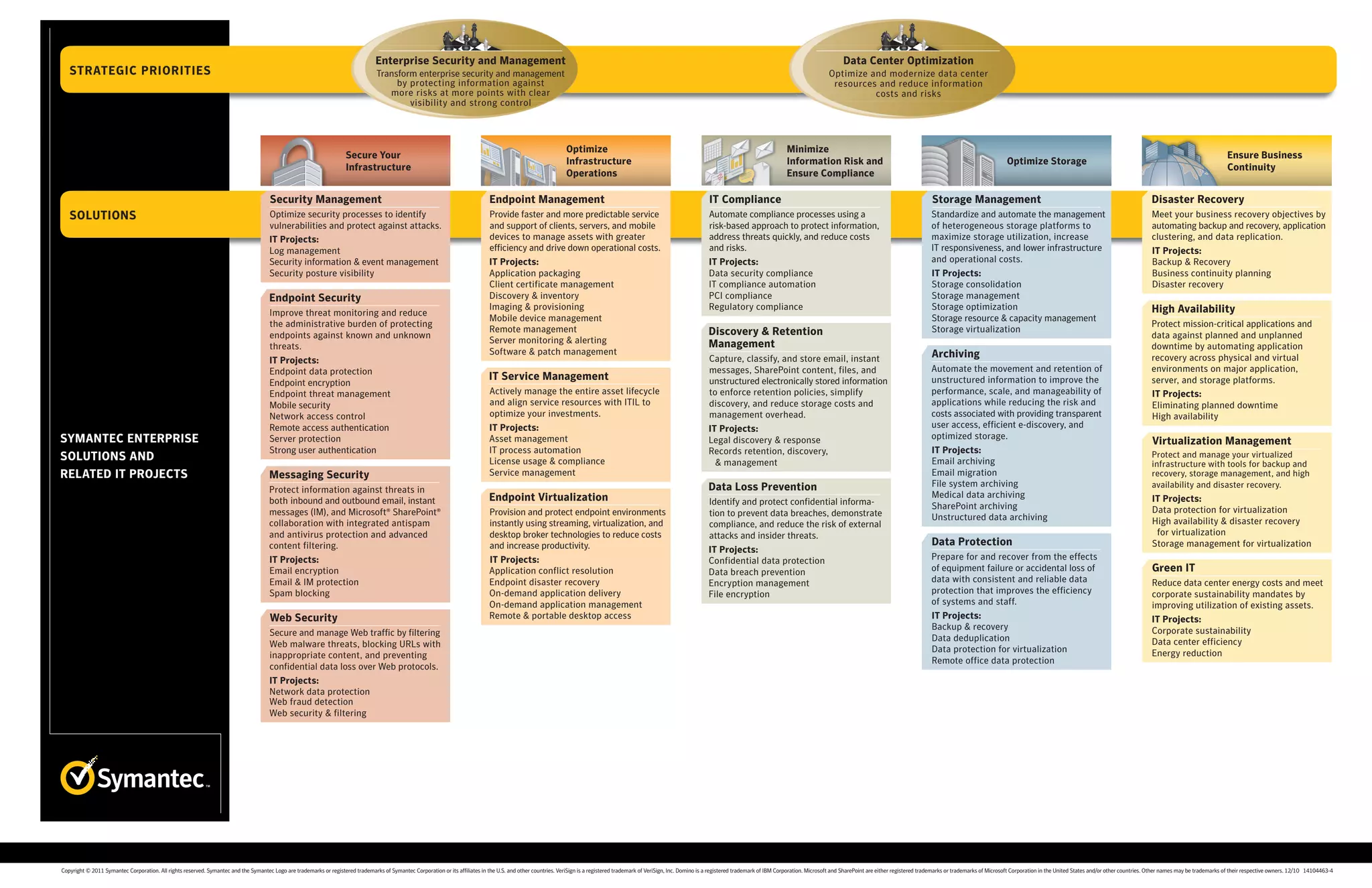
The document discusses strategic priorities and solutions for enterprise security, data center optimization, and ensuring business continuity. Some key areas covered include protecting information from risks through security management and endpoint security, optimizing infrastructure operations through mobile device and remote management, automating compliance processes to address threats and reduce costs and risks, standardizing storage management to maximize utilization and lower costs, and meeting recovery objectives through backup/recovery, application clustering, and data replication.