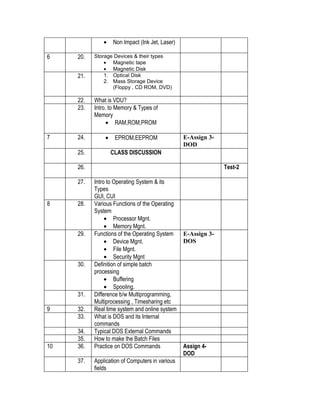
1. The document outlines the course plan for Introduction to IT for the first year BCA class at Punjab College of Technical Education in Ludhiana. It includes 47 total lectures over 11 weeks covering various topics in computer fundamentals, I/O devices, operating systems, and computer applications.
2. Students will have 3 assignments and 3 tests throughout the semester, with evaluations based on marks semester exam, presentations, assignments, and tests.
3. The course will introduce students to basic computer concepts like number systems, computer hardware, operating systems, and applications of computers in various fields to provide foundational knowledge in information technology.