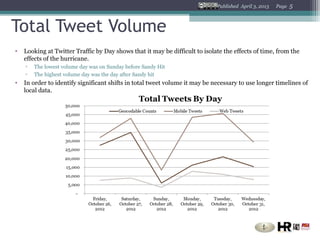
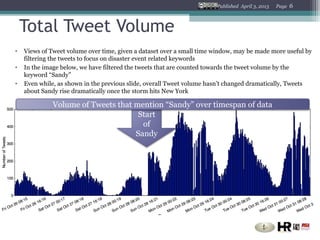
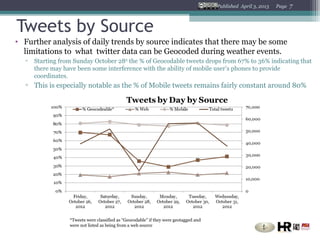
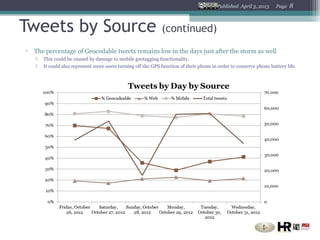
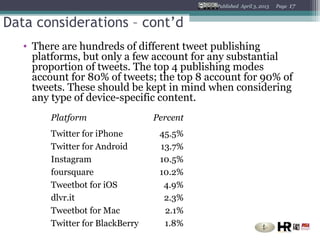
The document analyzes Twitter data during Hurricane Sandy to understand communication flows. It finds that tweet volume increased as the storm hit but geotagging decreased, possibly due to cell network issues. Keyword analysis showed tweets mentioning "Sandy" rose dramatically. Maps showed tweet locations and densities increased in affected areas. Network analysis revealed interactions between general accounts and those mentioning "weather." Proper data handling, geocoding analysis, deduplication and device platform understanding are needed for effective emergency communication analysis.