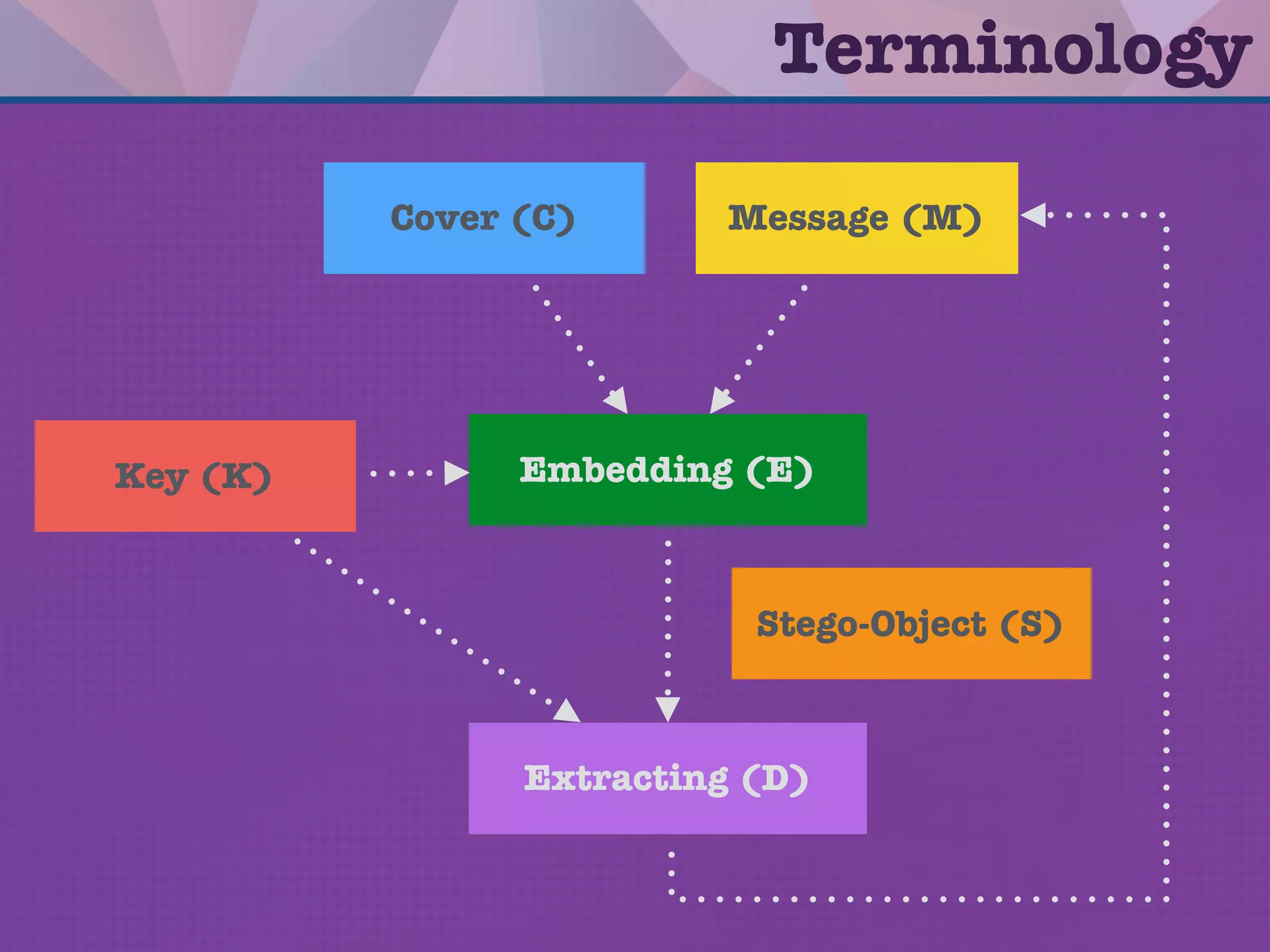
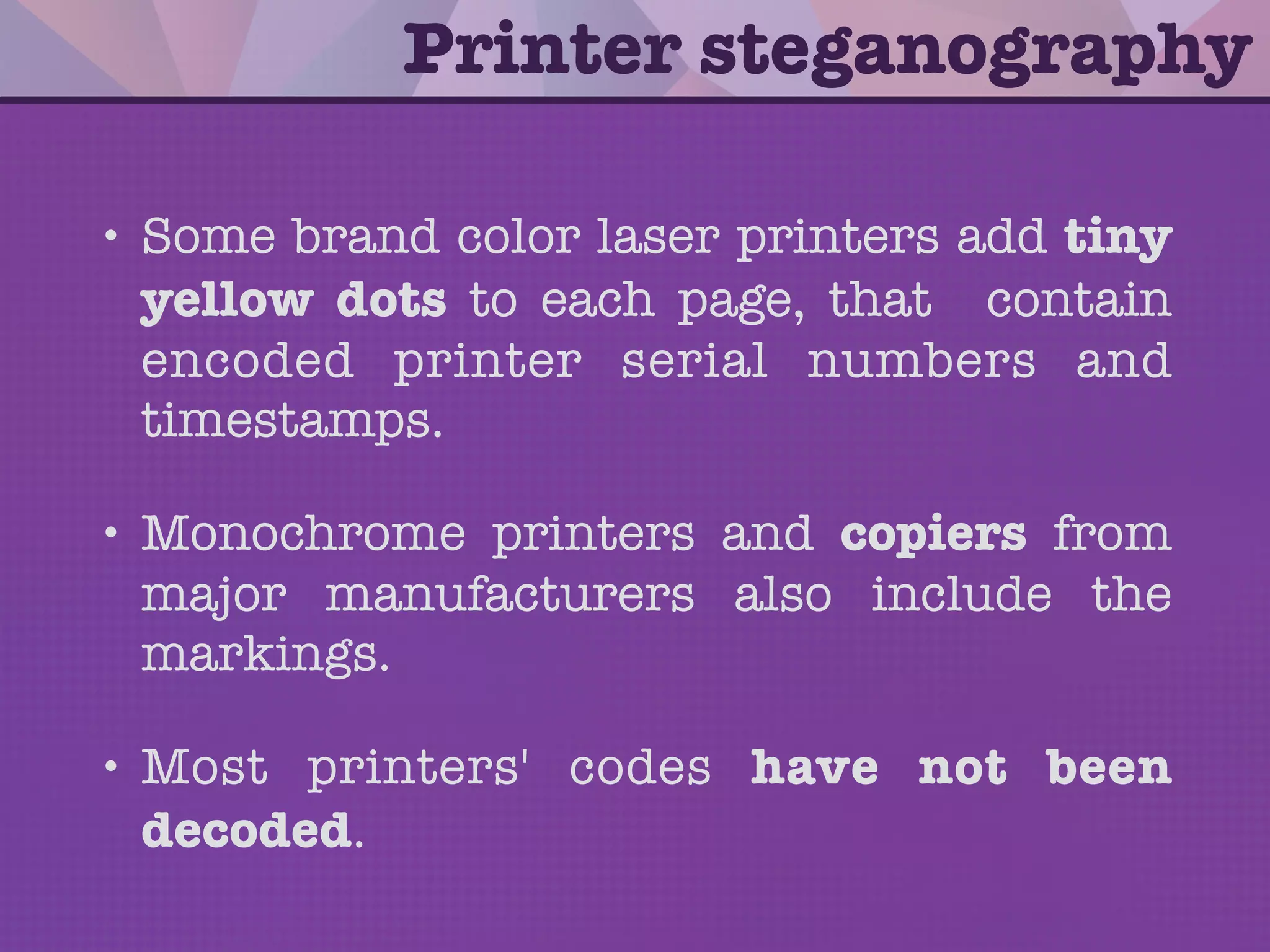
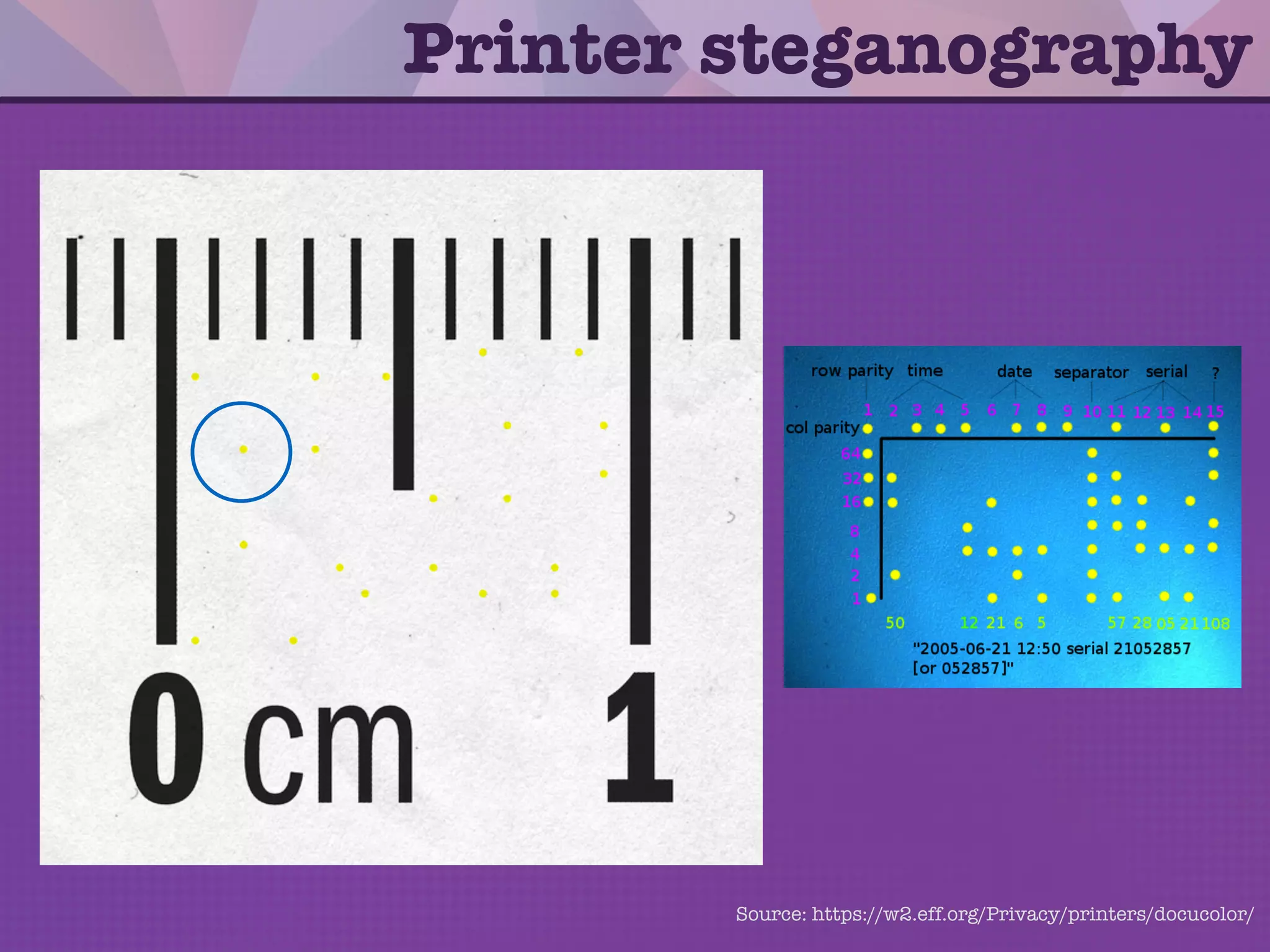
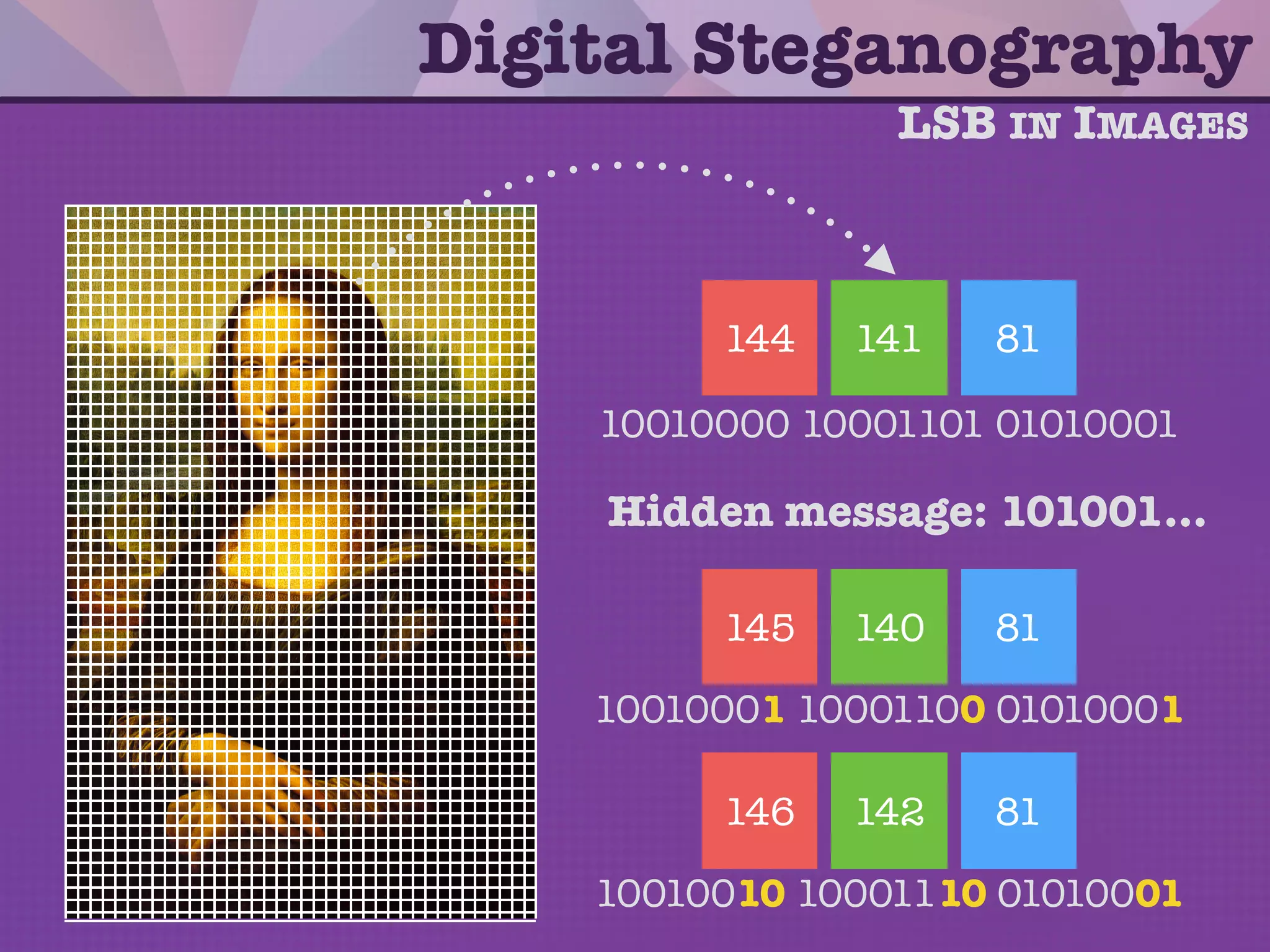
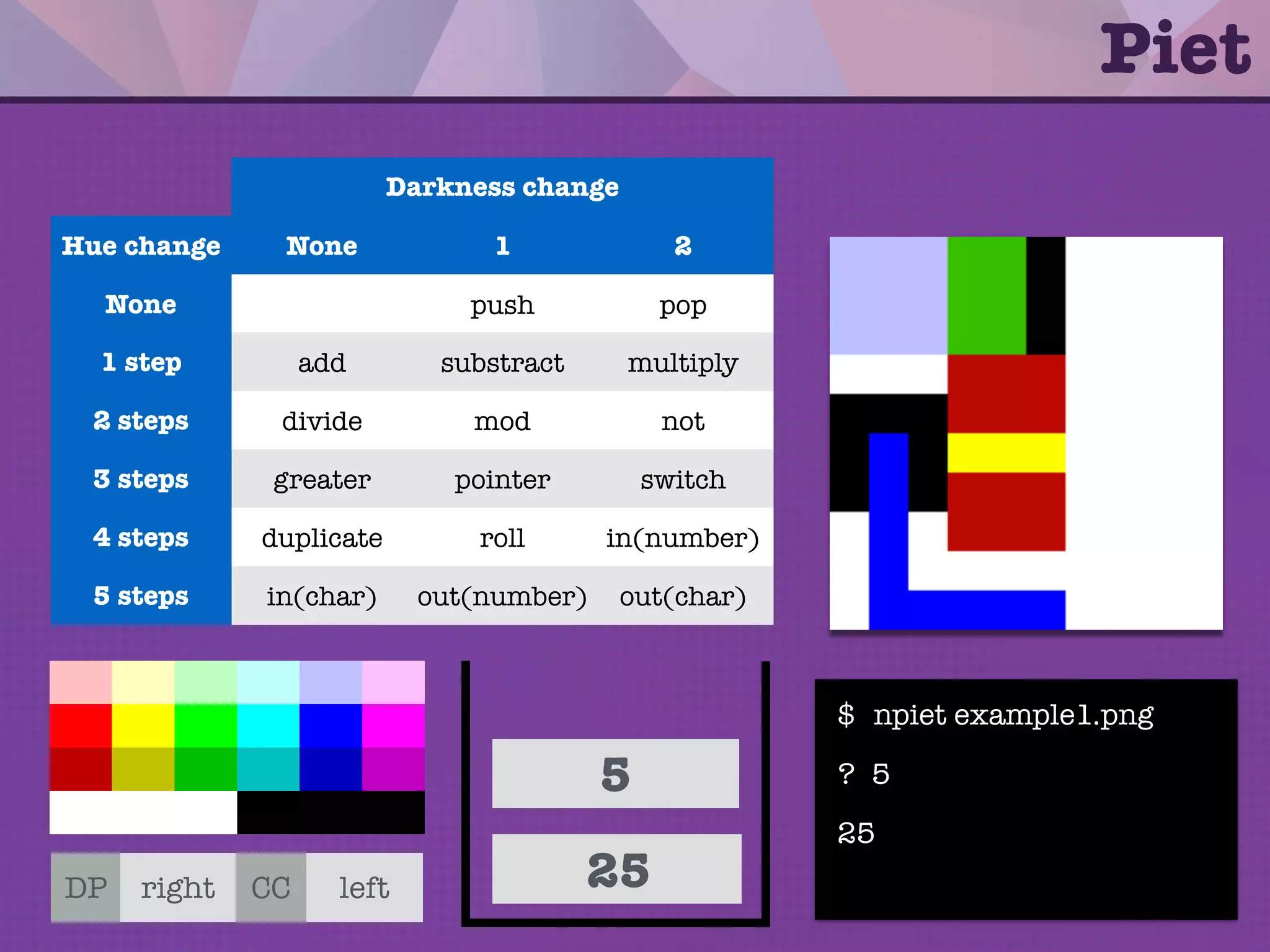
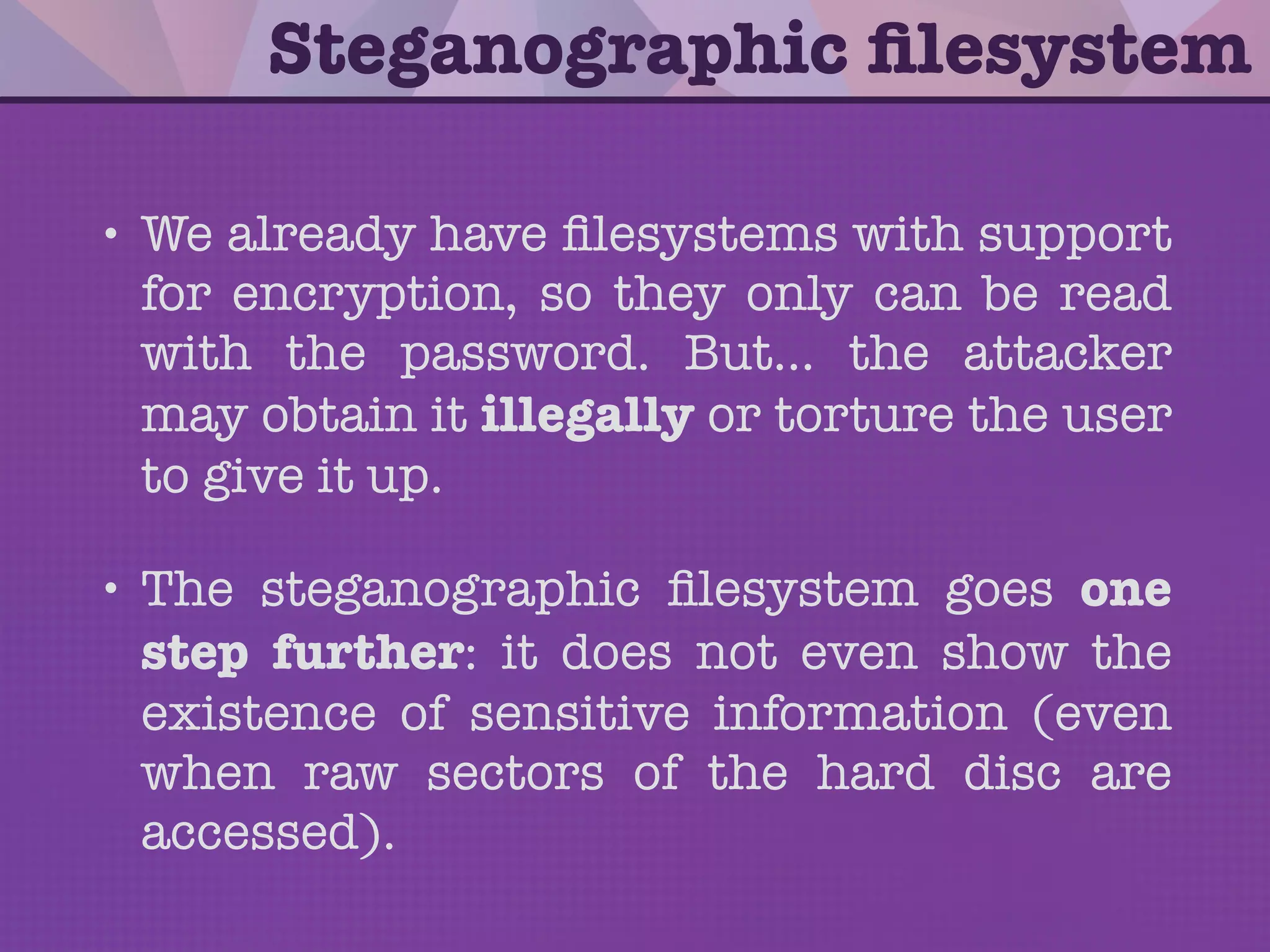
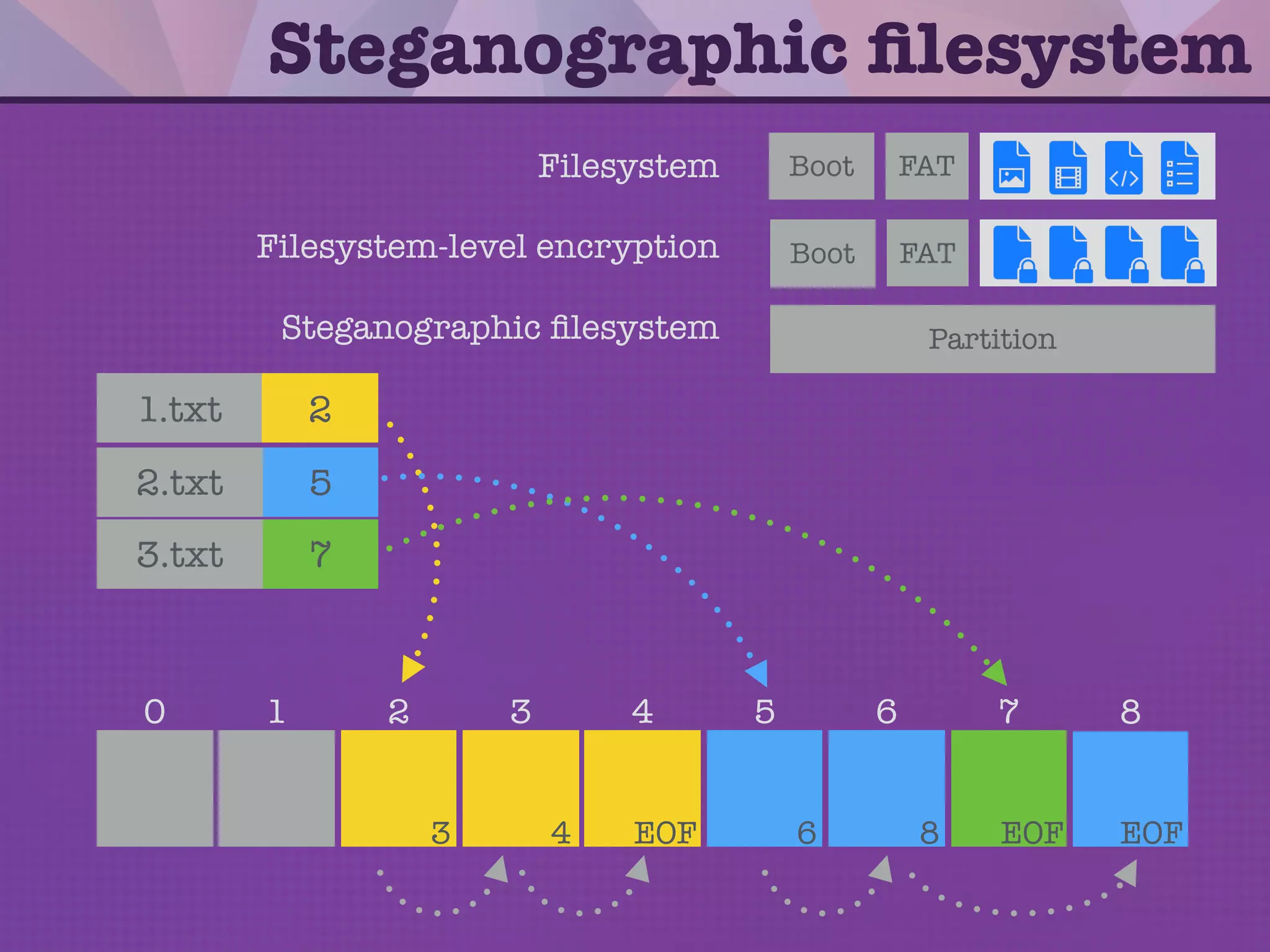
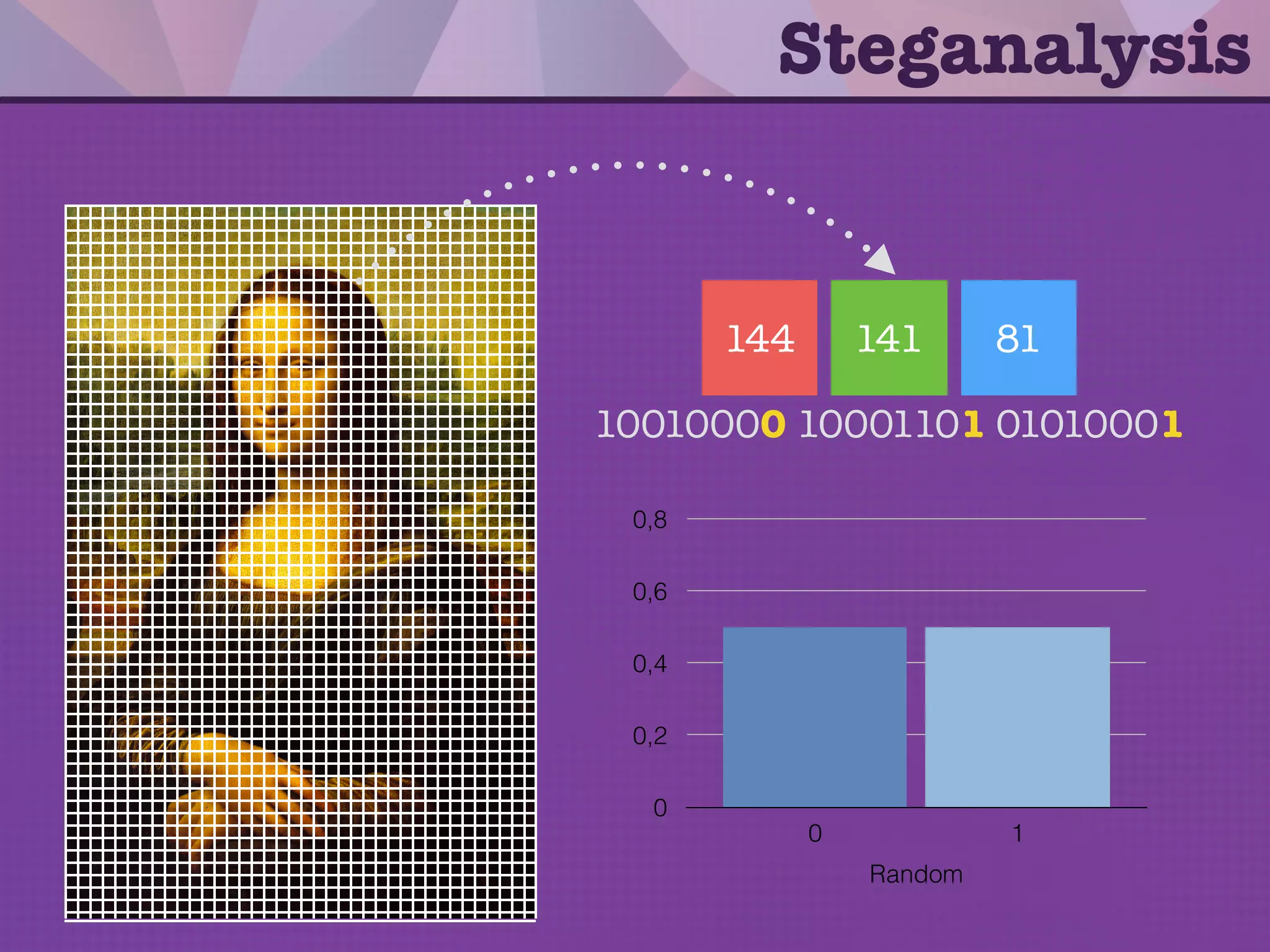
The document discusses steganography, the practice of concealing messages within other messages to avoid detection, alongside cryptography, which makes data unreadable. It covers various techniques, applications, and examples of steganography, including network steganography, printer steganography, and digital steganography using images. Additionally, it touches upon the concept of polyglot programming, where a single program can function in multiple programming languages.



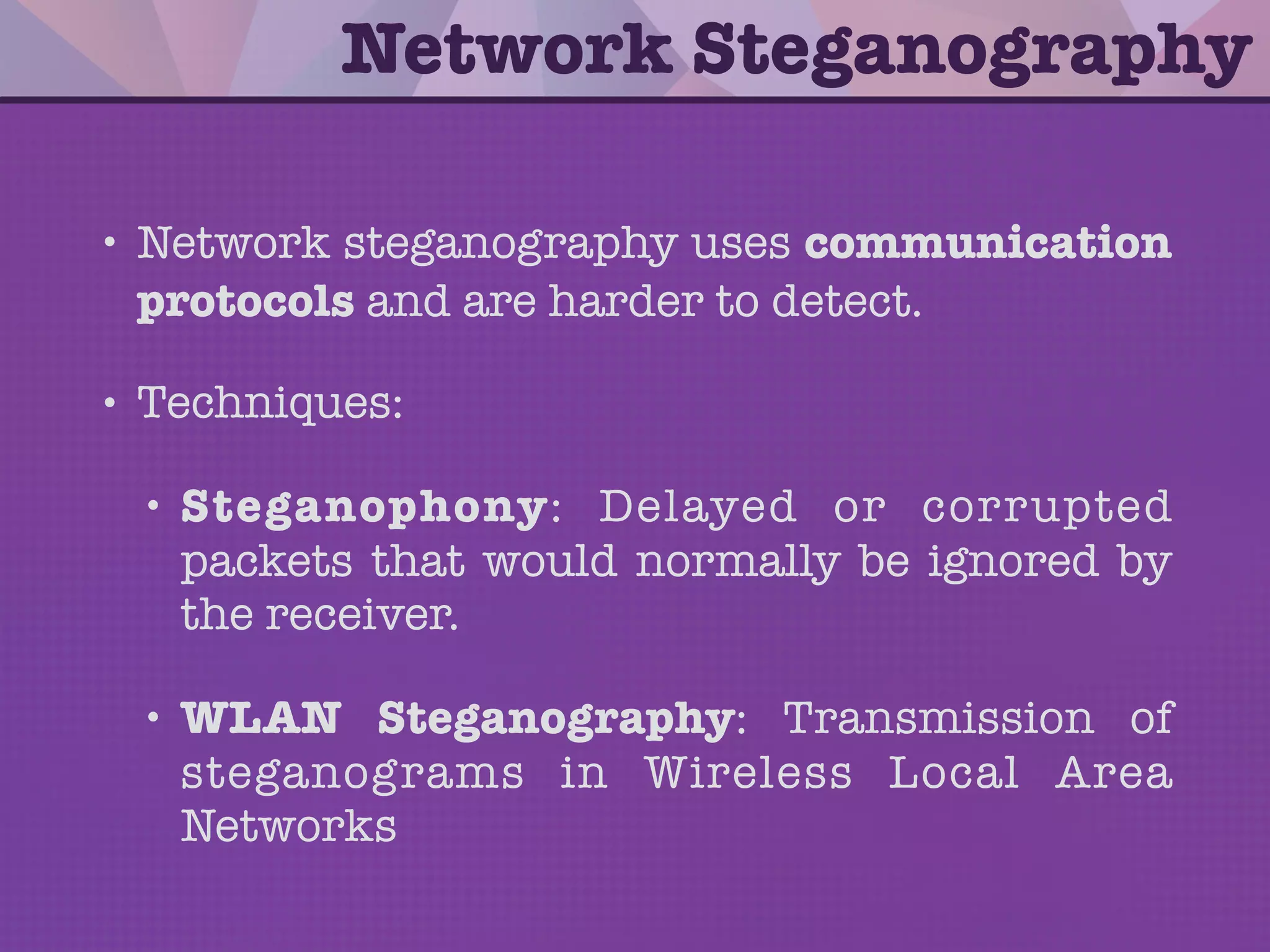


![5
l l oh e*val
len
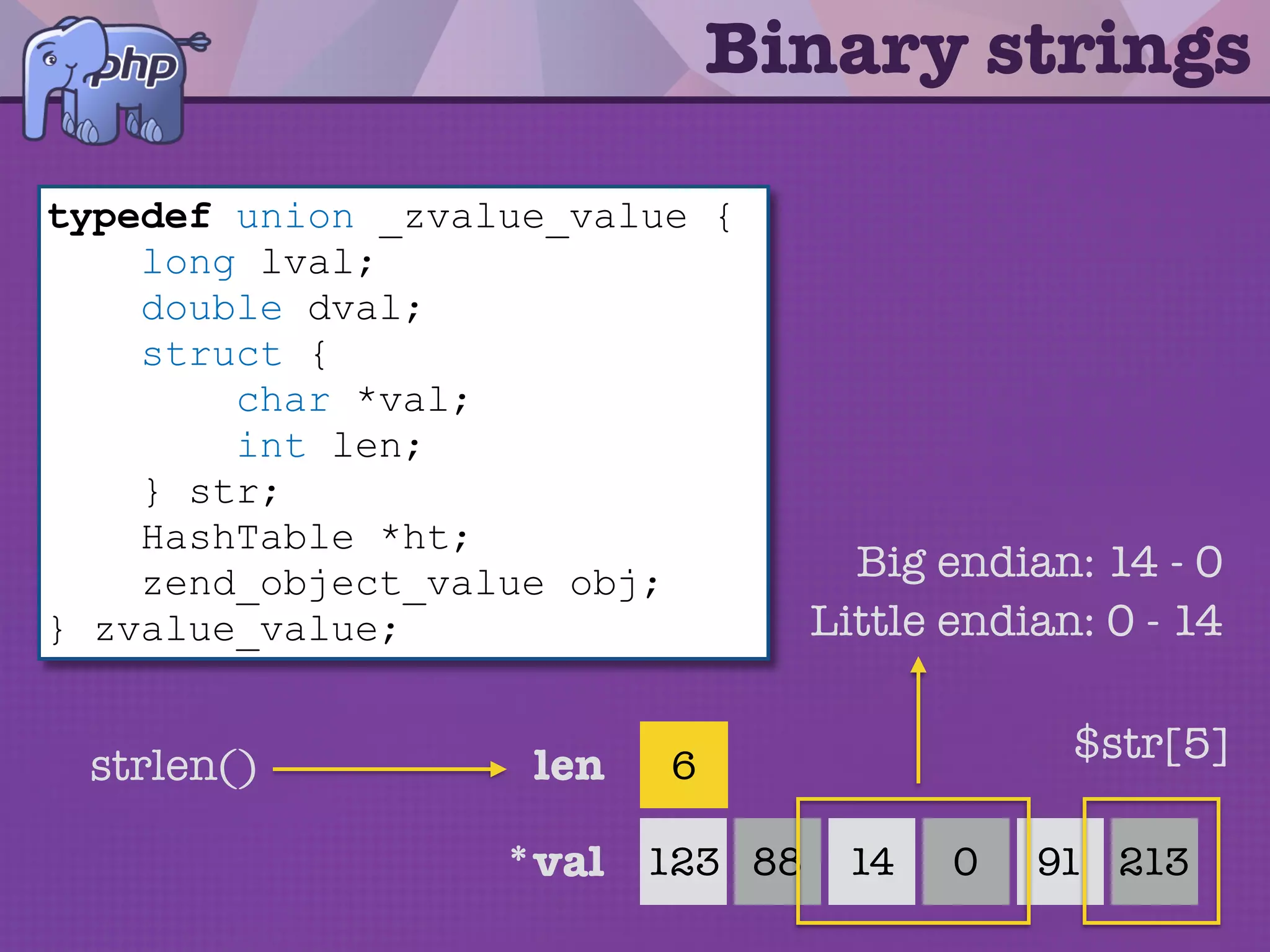
Binary strings
typedef union _zvalue_value {
long lval;
double dval;
struct {
char *val;
int len;
} str;
HashTable *ht;
zend_object_value obj;
} zvalue_value;
6
091 21314 0123 88
$str[5]
Big endian: 14 - 0
Little endian: 0 - 14
strlen()](https://image.slidesharecdn.com/steganography-150131143936-conversion-gate01/75/Steganography-Hiding-your-secrets-with-PHP-41-2048.jpg)
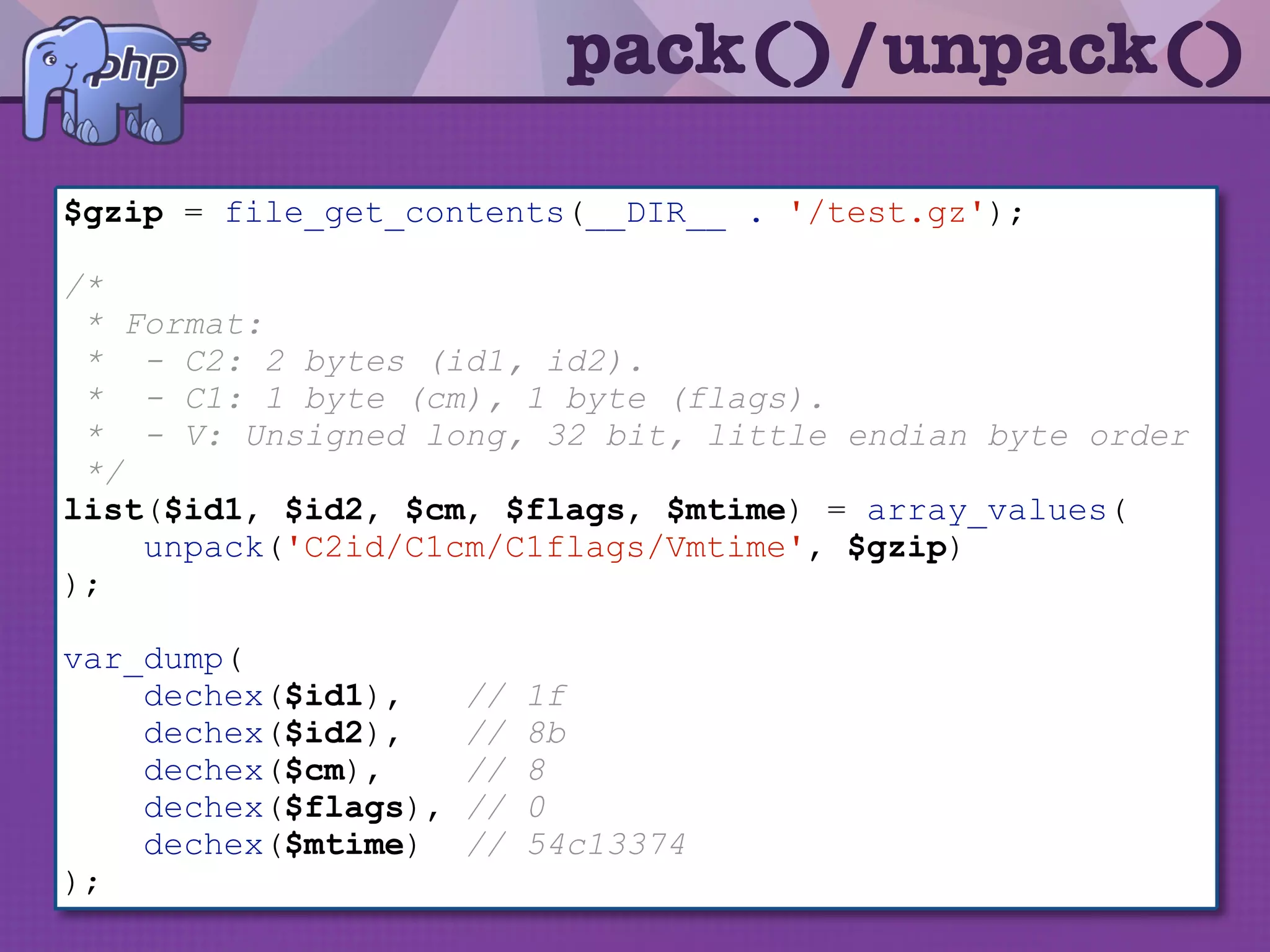


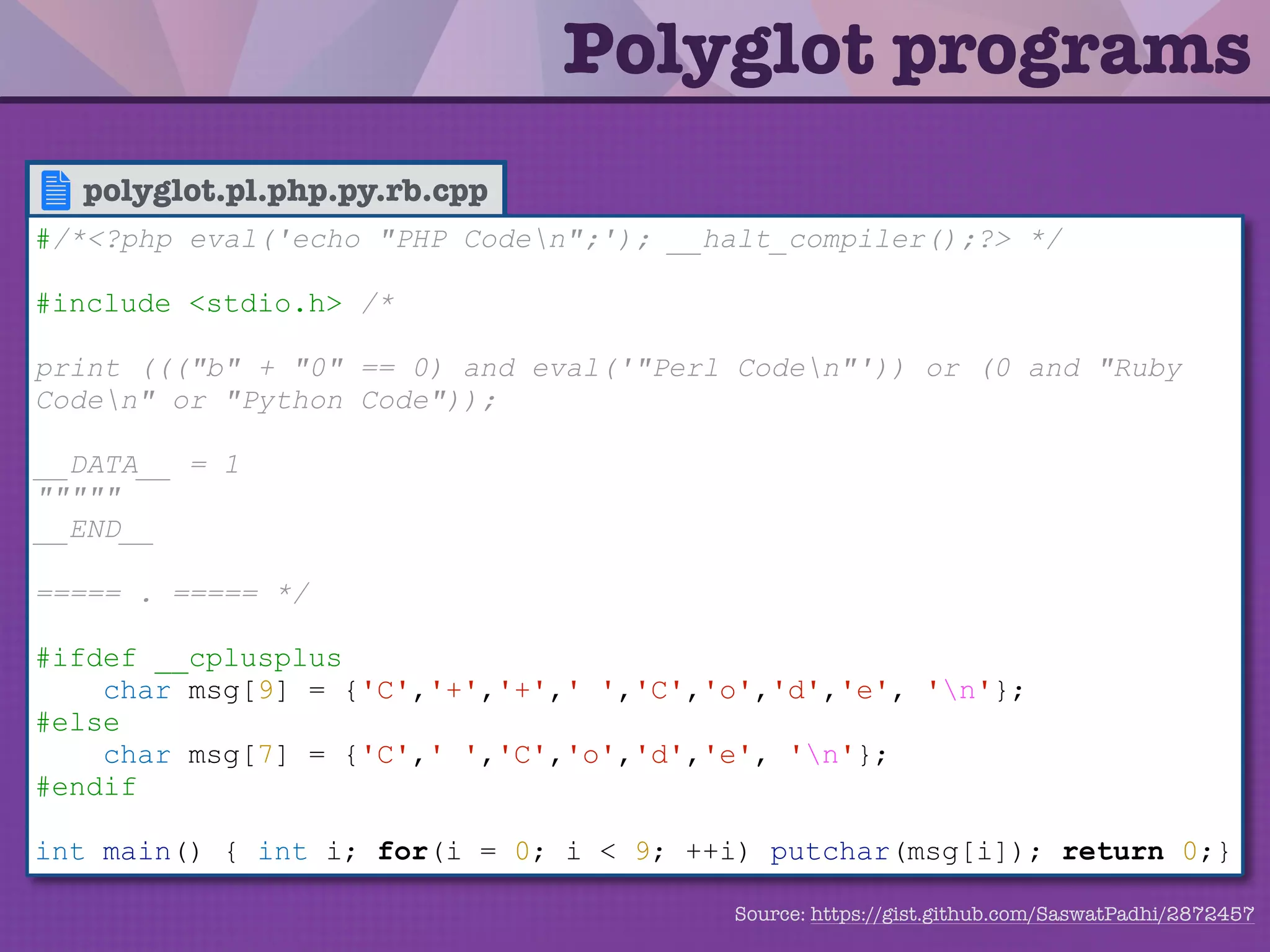
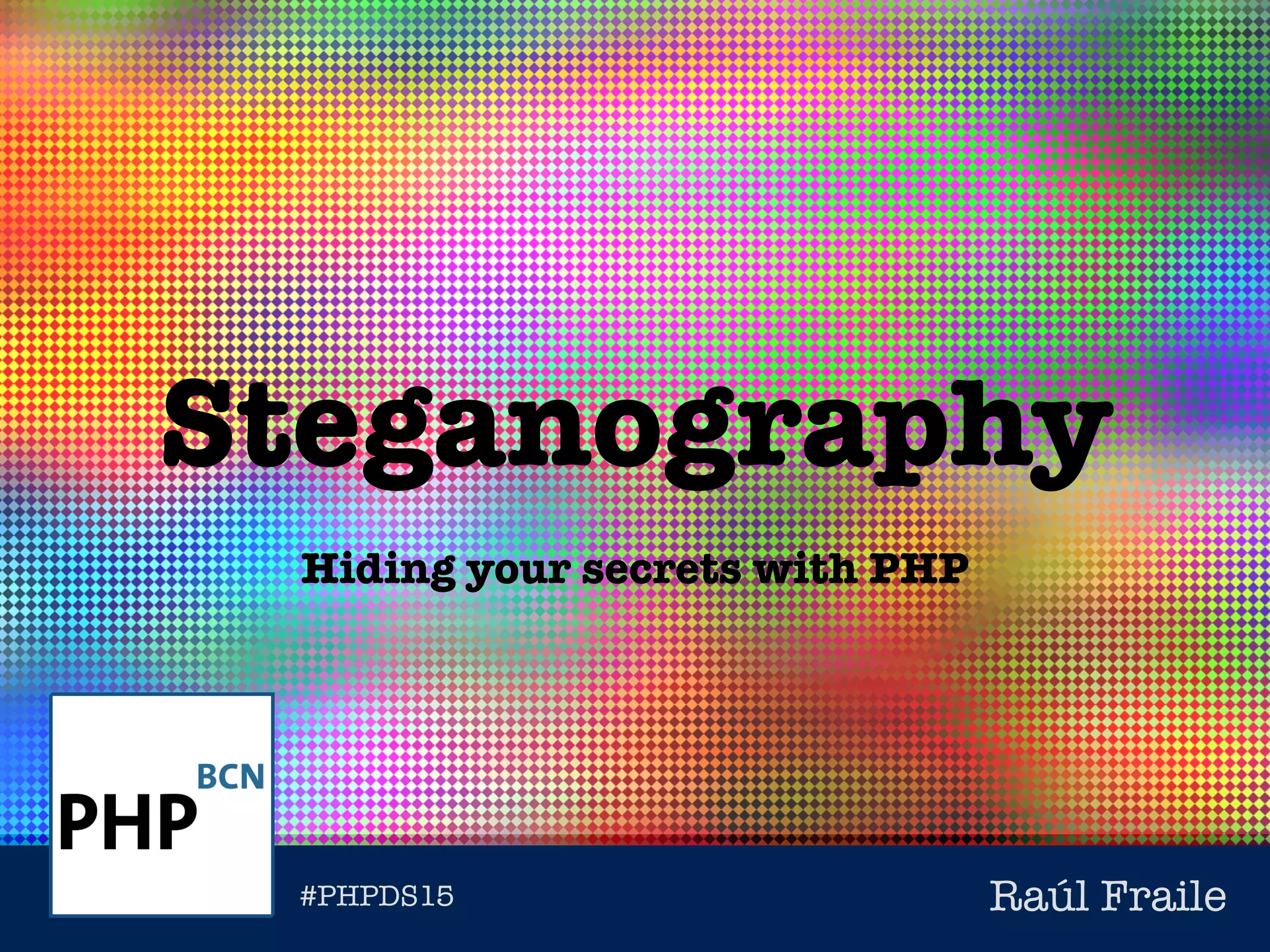
![polyglot.pl.php.py.rb.cpp
Polyglot programs
#/*<?php eval('echo "PHP Coden";'); __halt_compiler();?> */
#include <stdio.h> /*
print ((("b" + "0" == 0) and eval('"Perl Coden"')) or (0 and "Ruby
Coden" or "Python Code"));
__DATA__ = 1
"""""
__END__
===== . ===== */
#ifdef __cplusplus
char msg[9] = {'C','+','+',' ','C','o','d','e', 'n'};
#else
char msg[7] = {'C',' ','C','o','d','e', 'n'};
#endif
int main() { int i; for(i = 0; i < 9; ++i) putchar(msg[i]); return 0;}
Source: https://gist.github.com/SaswatPadhi/2872457](https://image.slidesharecdn.com/steganography-150131143936-conversion-gate01/75/Steganography-Hiding-your-secrets-with-PHP-63-2048.jpg)