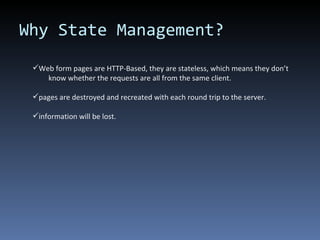
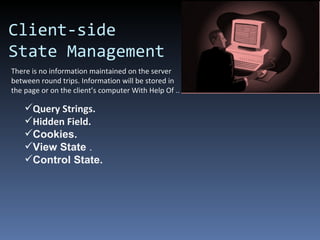
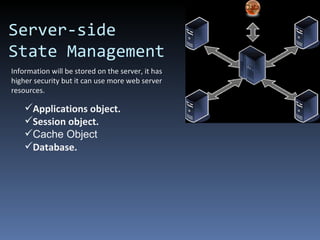
The document discusses different techniques for managing state in web applications, including client-side and server-side approaches. Client-side state management stores information locally in the browser using methods like query strings, hidden fields, cookies, and view state. Server-side state management stores information on the server using objects like application, session, and cache. Each approach has advantages and limitations regarding security, performance, and capacity.



![Query String Limitations You can use query string technique when passing Only String Type Data. Risk When you pass non secure data. Increase Network traffic. There are a few browser limitation when using query strings that impose a length limitation on the query string( 2083-character followed by Length Limit of URL ) . Query String Advantage Query strings provide a simple way to maintain state information. Does not required server side resources. How To Use Query Strings When you need to use a query string data you do it in the following way: string queryStringData = Request.QueryString["data"]; Query Strings Client-side State Management](https://image.slidesharecdn.com/statemanagement-110826021013-phpapp02/85/State-management-10-320.jpg)


![write the cookie to the response Response.Cookies["cookie"].Value = "value“; In the HttpCookie class there is a Expires property. If you don't use it (like in the example) the cookie is saved in memory and discarded if the user closes the browser. If you use the property you must define the amount of time the cookie is saved. In order to delete a saved cookie you need to use the Expires property and pass a past expiration date. There is no way to delete a cookie otherwise. In the previous example the cookie saves a single value. The cookie can save multiple values like in the next example. Response.Cookies["cookie"]["key1"].Value = "value1"; Response.Cookies["cookie"]["key2"].Value = "value2"; Response.Cookies["cookie"]["key3"].Value = "value3";](https://image.slidesharecdn.com/statemanagement-110826021013-phpapp02/85/State-management-14-320.jpg)
![How To Use Cookies? Cookies are sent in the HTTP header of the response. To create a cookie you need to use the Response.Cookies property. To read a cookie value from the cookie use the Request.Cookies property. The following example shows how to read a cookie named " cookie " and how to write the cookie : // it can be different from null only is // a request was made before if (Request.Cookies["cookie"] != null) { // get the cookie HttpCookie cookie = Request.Cookies["cookie"]; // get the cookie value string value = Server.HtmlEncode(cookie.Value); }](https://image.slidesharecdn.com/statemanagement-110826021013-phpapp02/85/State-management-15-320.jpg)