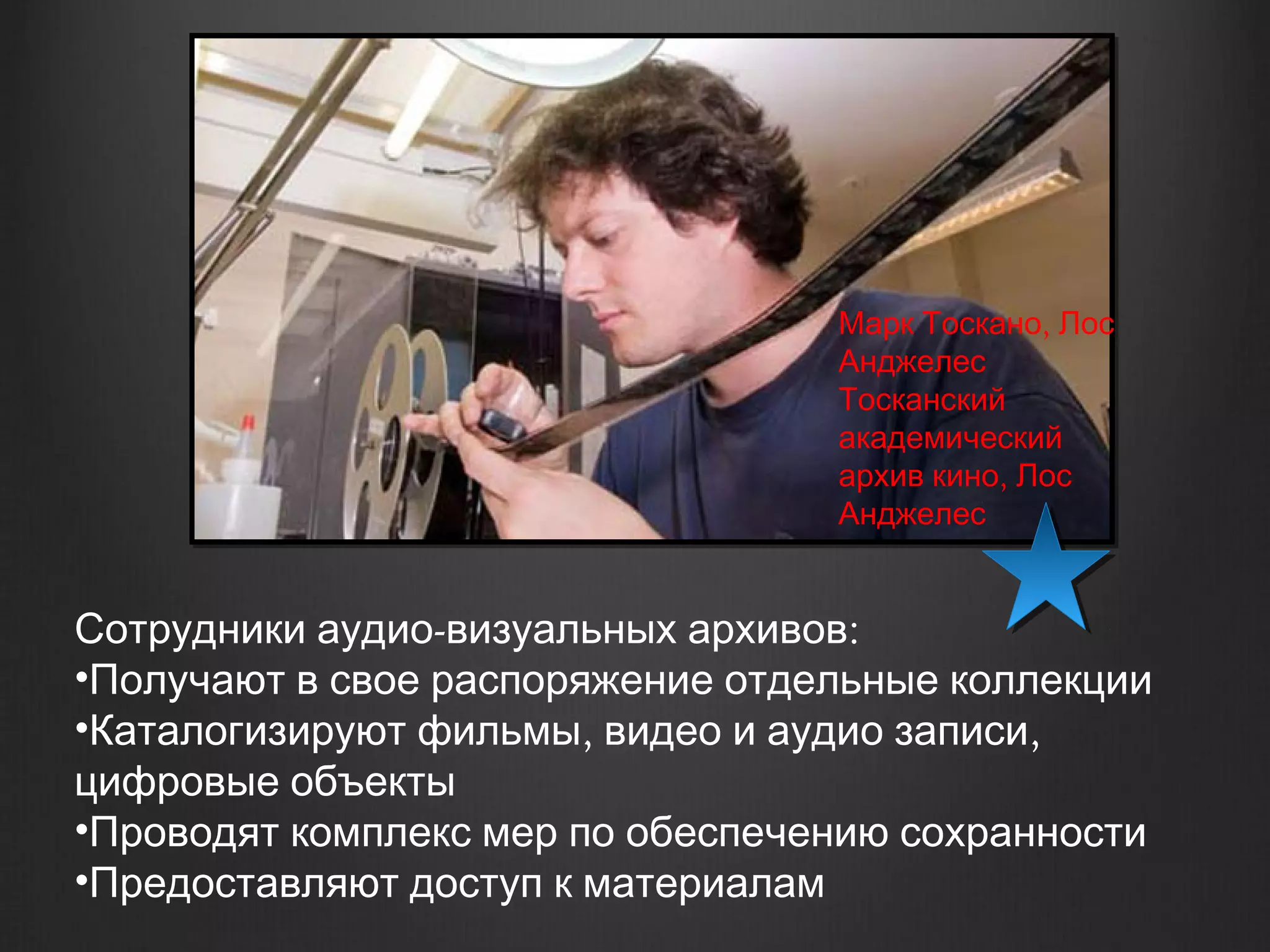
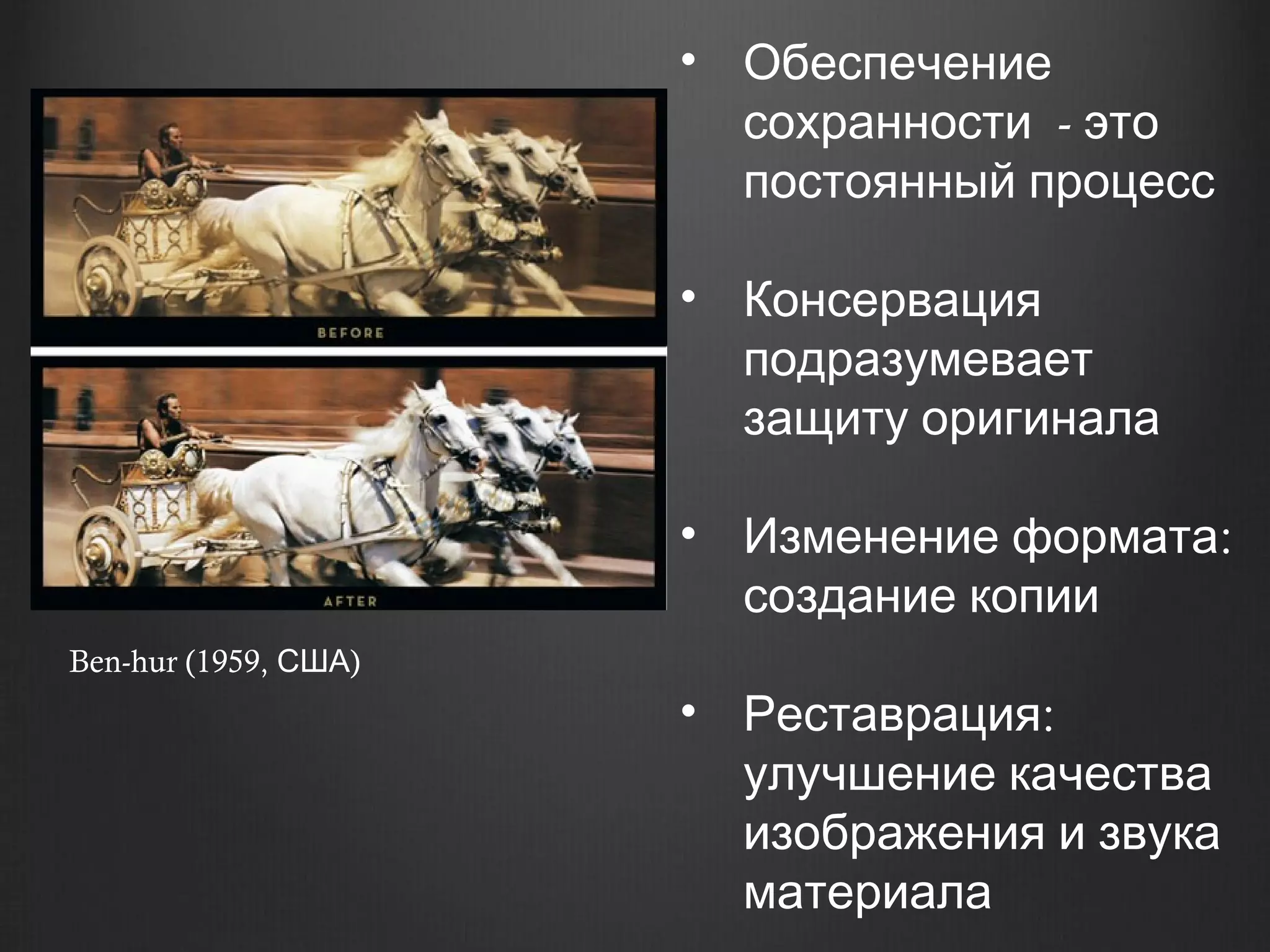
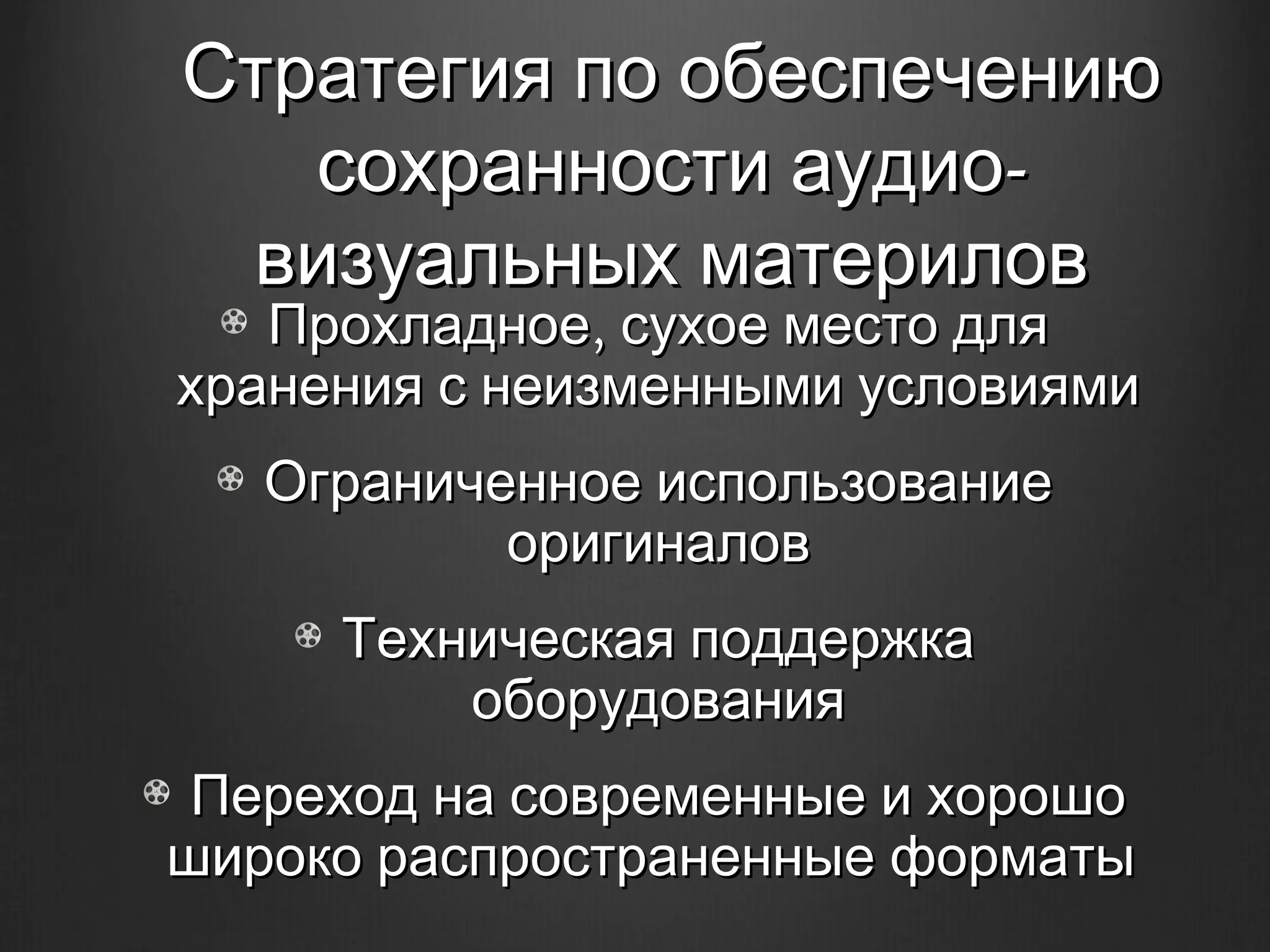
Документ исследует сохранение аудио-визуального наследия, подчеркивая важность архивирования и доступа к историческим материалам. Описаны различные типы архивных материалов, их консервация и изменение форматов, а также проблемы, связанные с морально устаревшей информацией. Подробно рассматриваются условия хранения, техническое оснащение и стратегии обеспечения сохранности архивных коллекций.