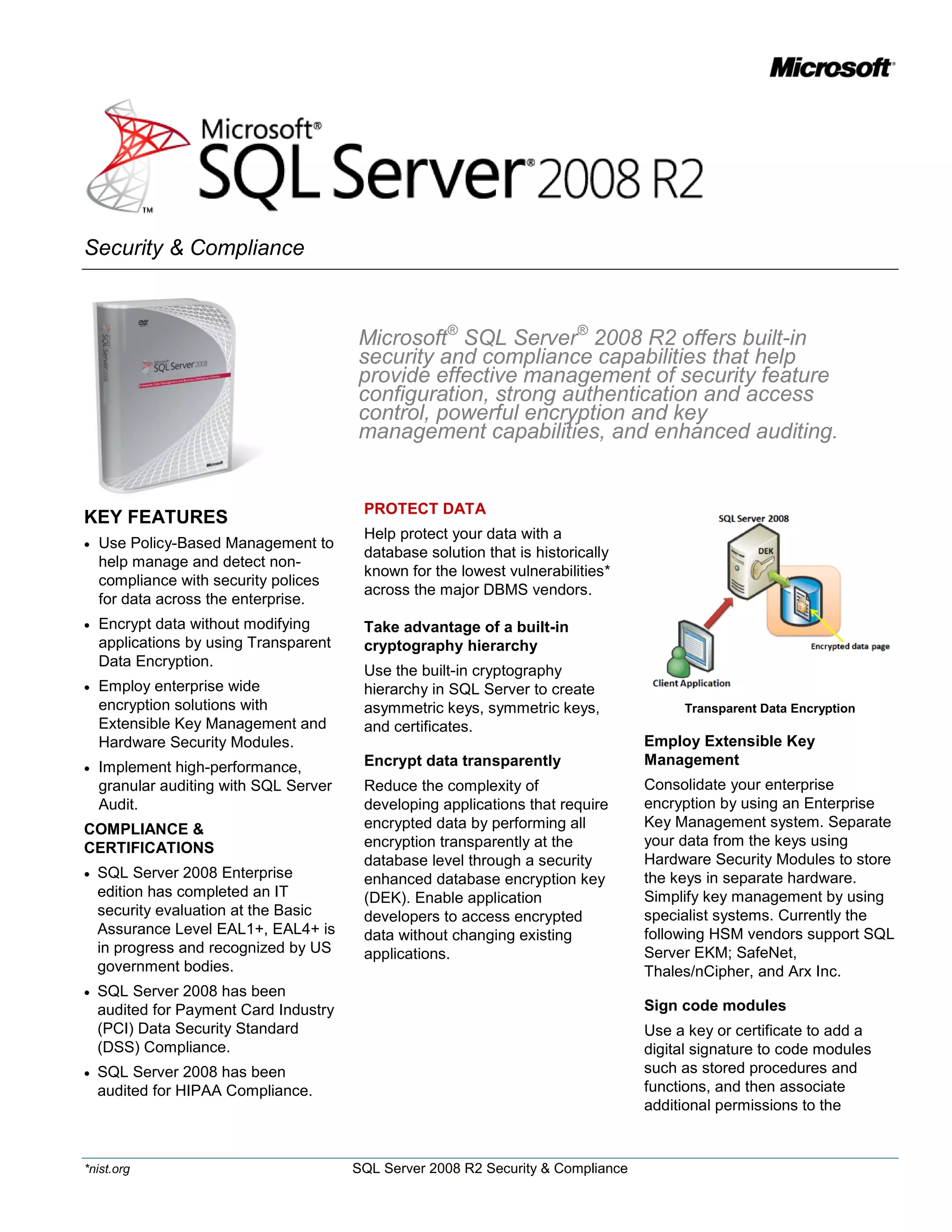
The document summarizes security and compliance capabilities in Microsoft SQL Server 2008 R2. It provides key features such as policy-based management to help manage compliance with security policies, transparent data encryption to encrypt data without modifying applications, and extensible key management with hardware security modules for enterprise-wide encryption solutions. It also discusses controls for access, authentication, authorization and auditing as well as ensuring compliance with policies and regulations.