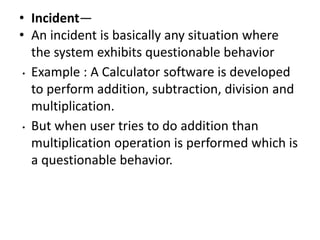
- "Testing is the process of executing a program with the intent of finding faults."
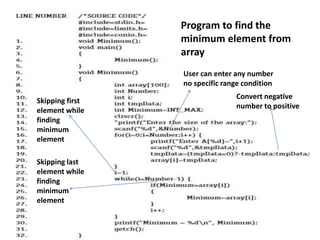
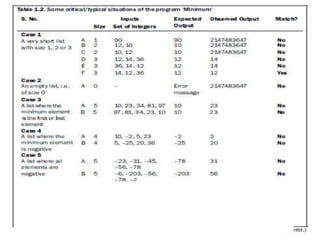
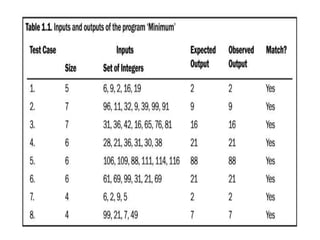
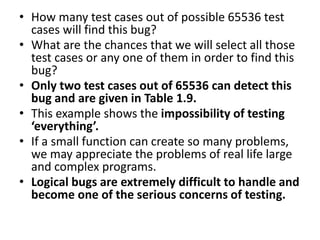
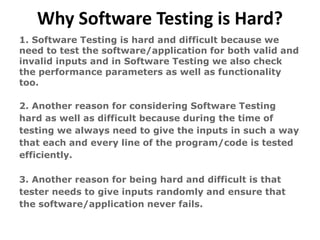
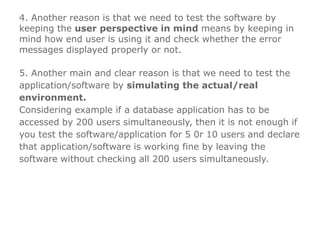
- Good testing involves more than just executing a program a few times, including testing all possible paths and inputs. However, exhaustive testing of everything is impossible due to constraints.
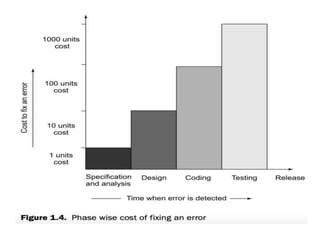
- The costs of fixing errors increases drastically from early phases like specification to later phases like testing and maintenance. Early testing helps find errors at lower cost.