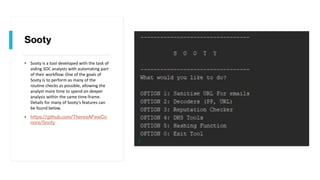
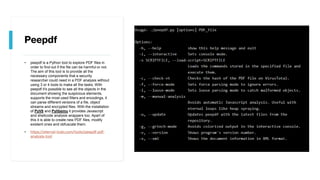
Sooty is a tool that aims to automate parts of a SOC analyst's workflow to allow them to spend more time on deeper analysis. Peepdf is a Python tool to explore PDF files and detect any potentially harmful elements. PyREBox is a Python scriptable reverse engineering sandbox based on QEMU to aid reverse engineering through dynamic analysis and debugging. Fail2Ban scans log files to detect and ban malicious IPs showing signs like too many password failures or exploits.